Cs-Cr

A proposed architecture for network forensic system in large-scale networks
A Reliable User Authentication and Data Protection Model in Cloud Computing Environments
A Revised Classification of Anonymity
A Secure Database System using Homomorphic Encryption Schemes

A secure service provisioning framework for cyber physical cloud computing systems
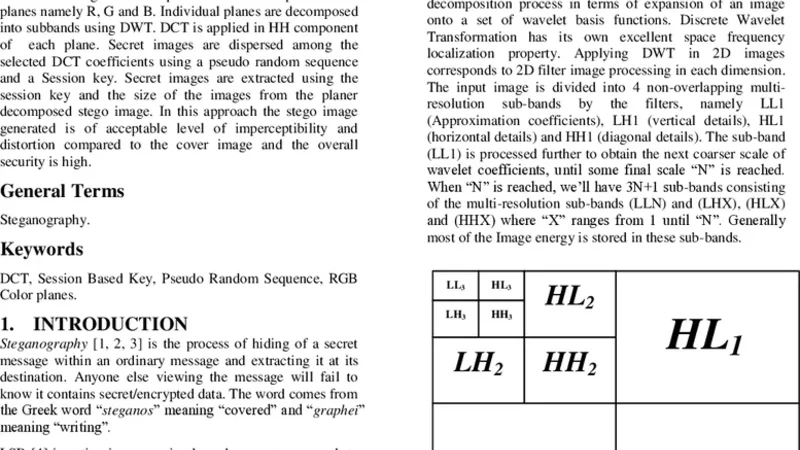
A Session based Multiple Image Hiding Technique using DWT and DCT
A Survey on Cloud Computing Security
A Survey on Various Data Hiding Techniques and their Comparative Analysis
About the Linear Complexity of Ding-Hellesth Generalized Cyclotomic Binary Sequences of Any Period
An Authentication Protocol Based on Combined RFID-Biometric System RFID-Biometric System
An Authentication Technique in Frequency Domain through Wavelet Transform (ATFDWT)

An Efficient Encryption Algorithm for P2P Networks Robust Against Man-in-the-Middle Adversary
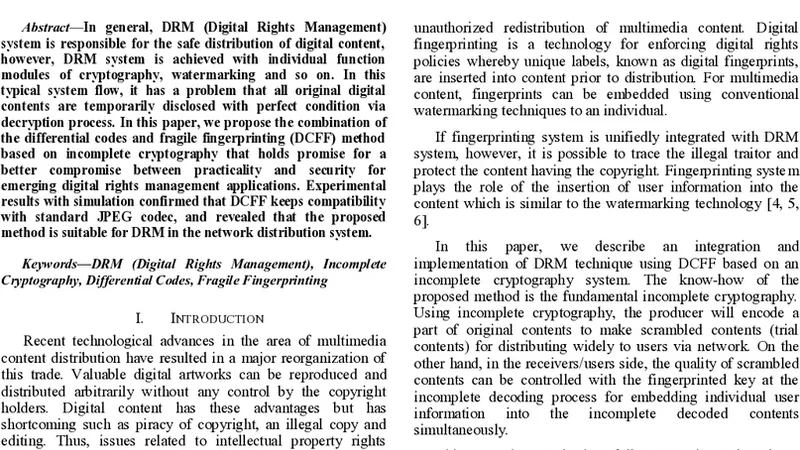
An Incomplete Cryptography based Digital Rights Management with DCFF

An ISP Level Solution to Combat DDoS Attacks using Combined Statistical Based Approach
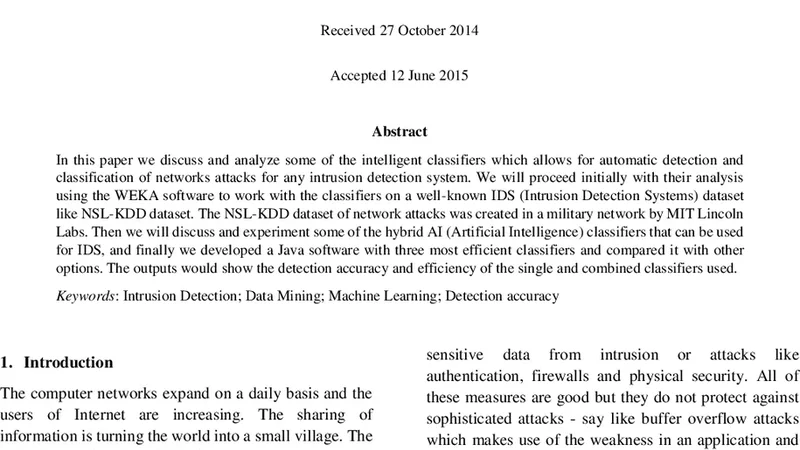
Analysis of Intelligent Classifiers and Enhancing the Detection Accuracy for Intrusion Detection System

Analysis of RSA algorithm using GPU programming
Andlantis: Large-scale Android Dynamic Analysis
Authentication System for Smart Homes Based on ARM7TDMI-S and IRIS-Fingerprint Recognition Technologies
Because we care: Privacy Dashboard on Firefox OS

BitWhisper: Covert Signaling Channel between Air-Gapped Computers using Thermal Manipulations

Cloud-Aware Web Service Security: Information Hiding in Cloud Computing
Context, Content, Process Approach to Align Information Security Investments with Overall Organizational Strategy