Cs-Cr

Lattices for Physical-layer Secrecy: A Computational Perspective
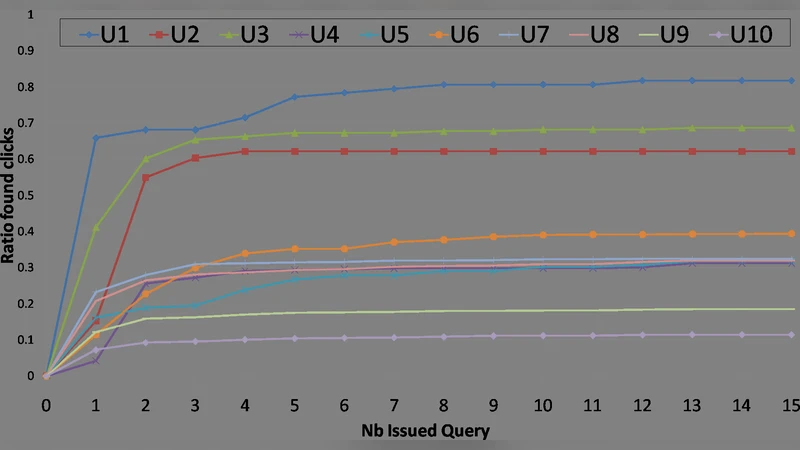
Show Me Your Cookie And I Will Tell You Who You Are

Unconditionally Secure Bit Commitment by Transmitting Measurement Outcomes
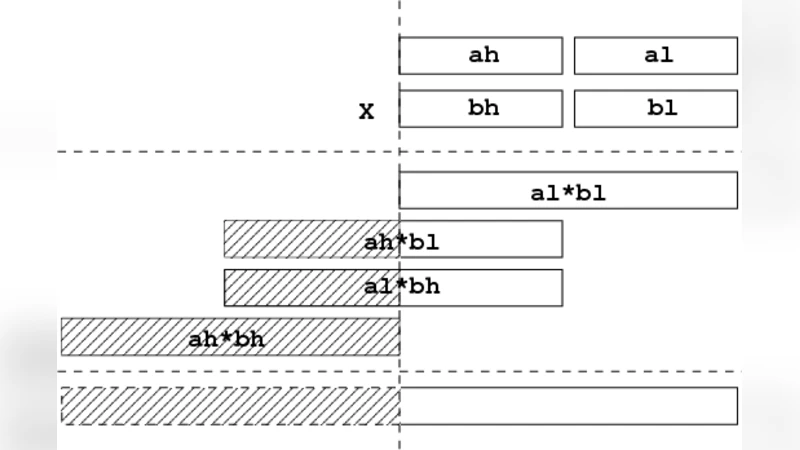
The Rabin cryptosystem revisited
An AI Based Super Nodes Selection Algorithm in BlockChain Networks

PPT: New Low Complexity Deterministic Primality Tests Leveraging Explicit and Implicit Non-Residues. A Set of Three Companion Manuscripts

Superposition Attacks on Cryptographic Protocols
On Detecting Pollution Attacks in Inter-Session Network Coding
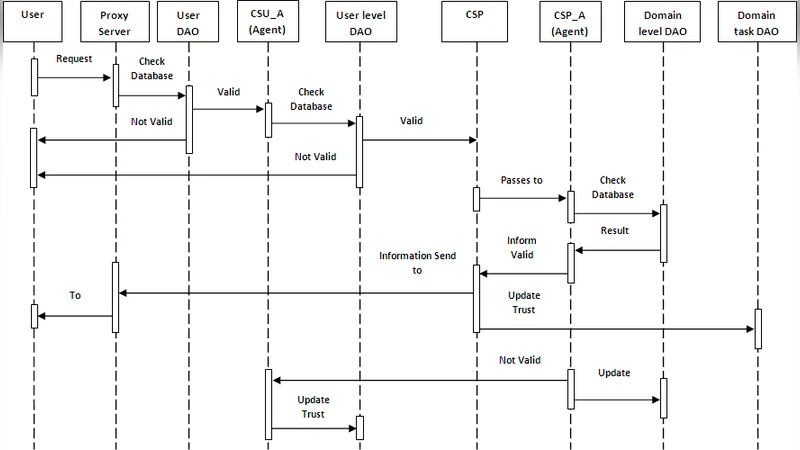
A New Trusted and Collaborative Agent Based Approach for Ensuring Cloud Security

Collision-resistant hash function based on composition of functions
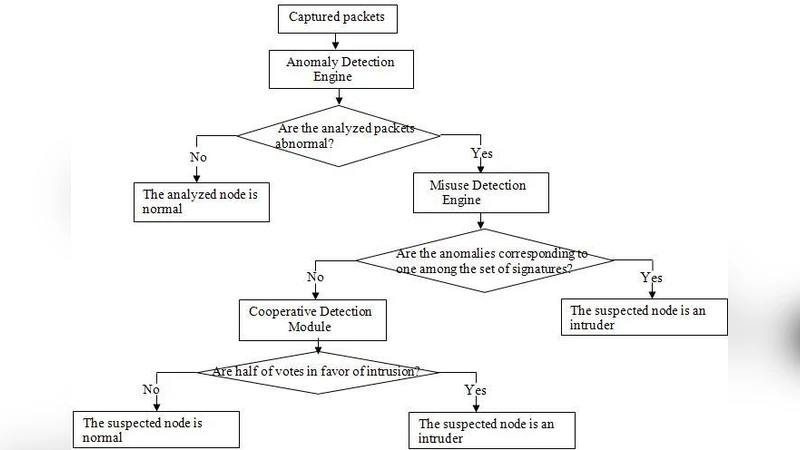
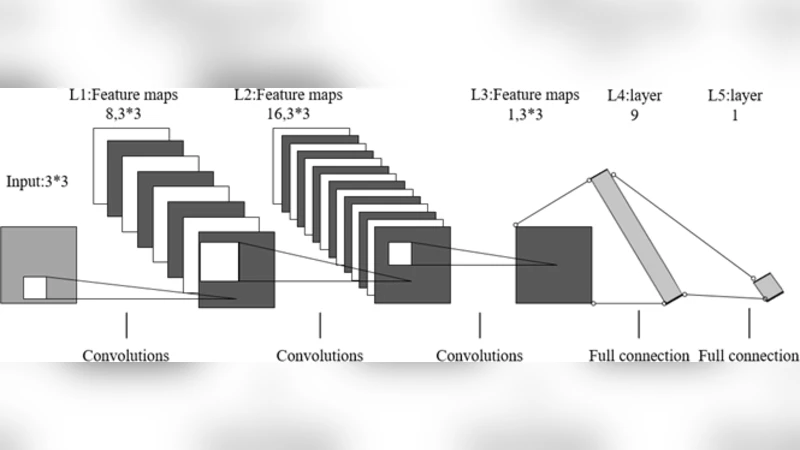
Novel hybrid intrusion detection system for clustered wireless sensor network
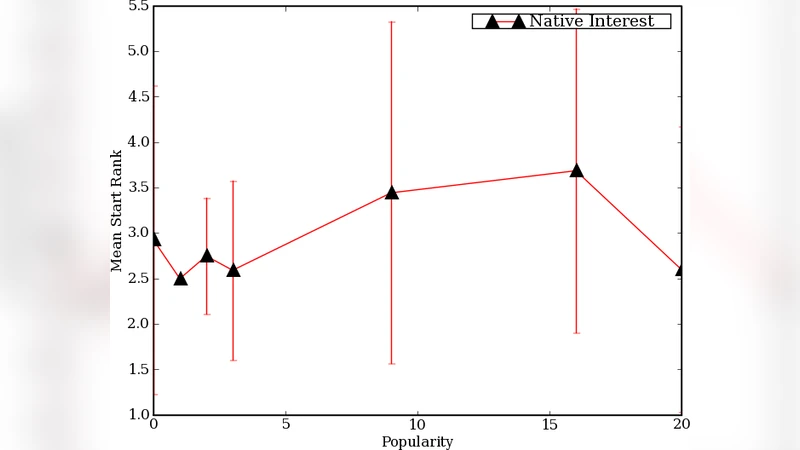
The BitTorrent Anonymity Marketplace
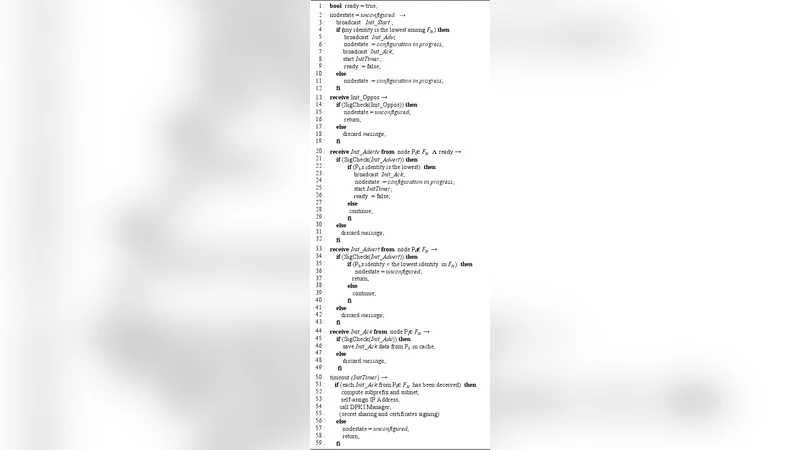
Secure and Robust IPV6 Autoconfiguration Protocol For Mobile Adhoc Networks Under Strong Adversarial Model
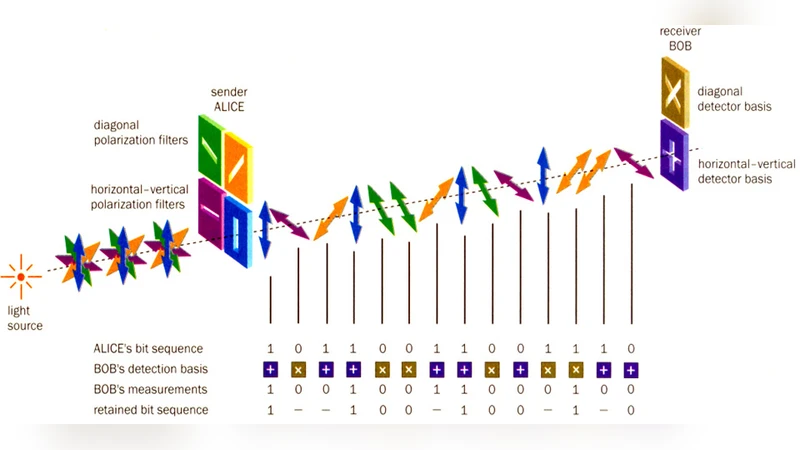
Quantum cryptography

Governing Information Security in Conjunction with COBIT and ISO 27001

User Awareness Measurement Through Social Engineering
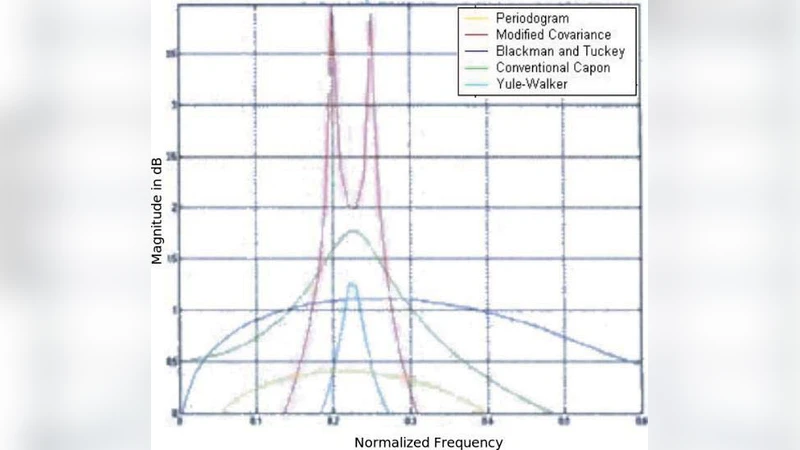
Digital Forensics Analysis of Spectral Estimation Methods

A Novel Header Matching Algorithm for Intrusion Detection Systems
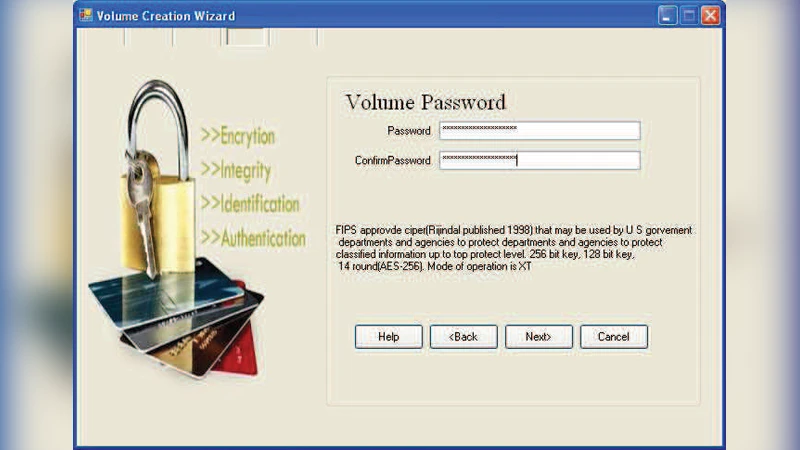
Digitalized Responsive Logical Interface Application
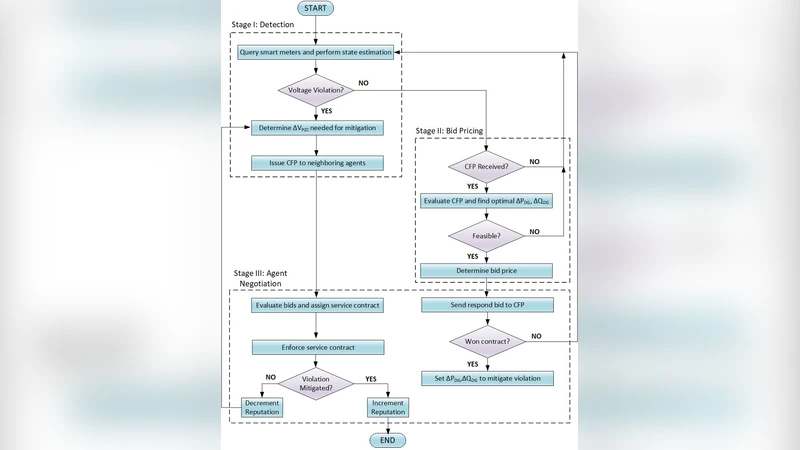
Blockchain Based Transactive Energy Systems for Voltage Regulation
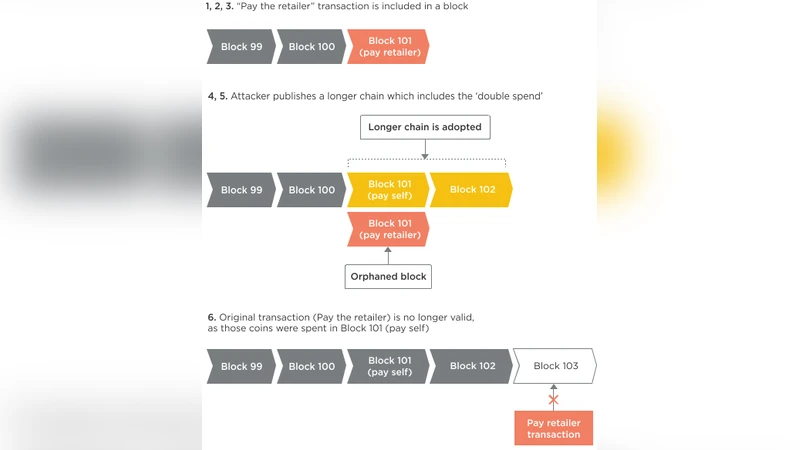
Application of Blockchain in Booking and Registration Systems of Securities Exchanges
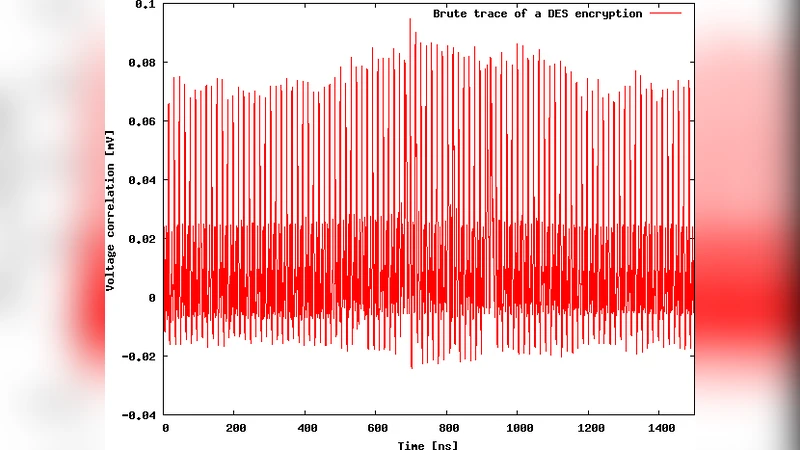
A Secure Asynchronous FPGA Architecture, Experimental Results and Some Debug Feedback