Cs-Cr
Simulation of Collision Resistant Secure Sum Protocol
SODEXO: A System Framework for Deployment and Exploitation of Deceptive Honeybots in Social Networks
StegBlocks: ensuring perfect undetectability of network steganography
Survey of Security and Privacy Issues of Internet of Things
Survey on security issues in file management in cloud computing environment
The Case for a General and Interaction-based Third-party Cookie Policy
The effect of constraints on information loss and risk for clustering and modification based graph anonymization methods
Threshold Voltage-Defined Switches for Programmable Gates
Touchalytics: On the Applicability of Touchscreen Input as a Behavioral Biometric for Continuous Authentication
Towards Approaches to Continuous Assessment of Cyber Risk in Security of Computer Networks
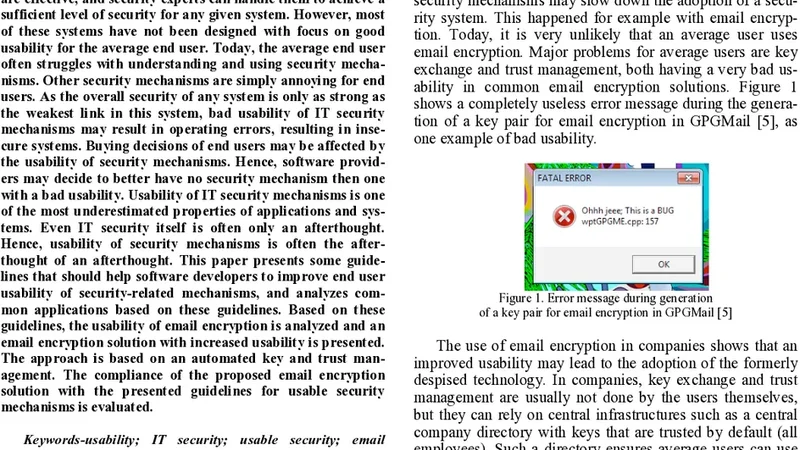
Towards Enhanced Usability of IT Security Mechanisms - How to Design Usable IT Security Mechanisms Using the Example of Email Encryption
Tracking Protection in Firefox For Privacy and Performance

Two Trends in Mobile Security: Financial Motives and Transitioning from Static to Dynamic Analysis
Upper Bounds on the Number of Codewords of Some Separating Codes

Using Facebook for Image Steganography
Variations in Tracking in Relation to Geographic Location
Zwei Anwendungen des Paillier-Kryptosystems: Blinde Signatur und Three-Pass-Protocol

A Distributed Approach to Privacy on the Cloud

A Framework for Analysis and Comparison of Dynamic Malware Analysis Tools

A Generation-based Text Steganography Method using SQL Queries

A New Chaos-Based Cryptosystem for Secure Transmitted Images
A New Covert Channel over Cellular Voice Channel in Smartphones
