Cs-Cr

Defending against malicious peripherals with Cinch
Desiging a logical security framework for e-commerce system based on soa
Detection of Information leakage in cloud
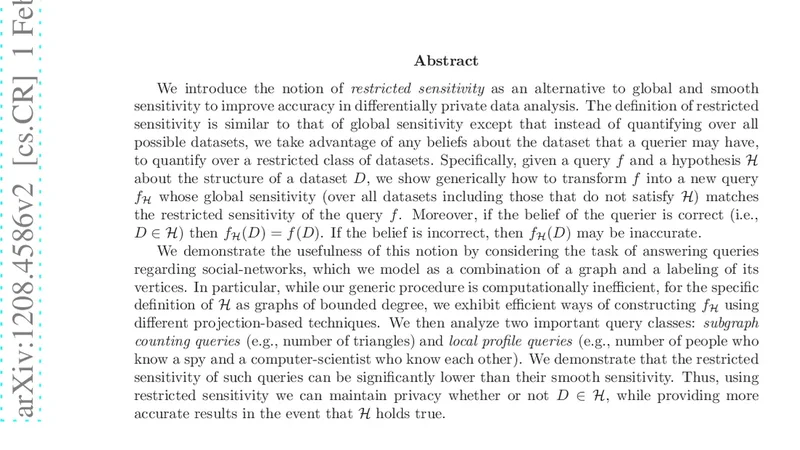
Differentially Private Data Analysis of Social Networks via Restricted Sensitivity
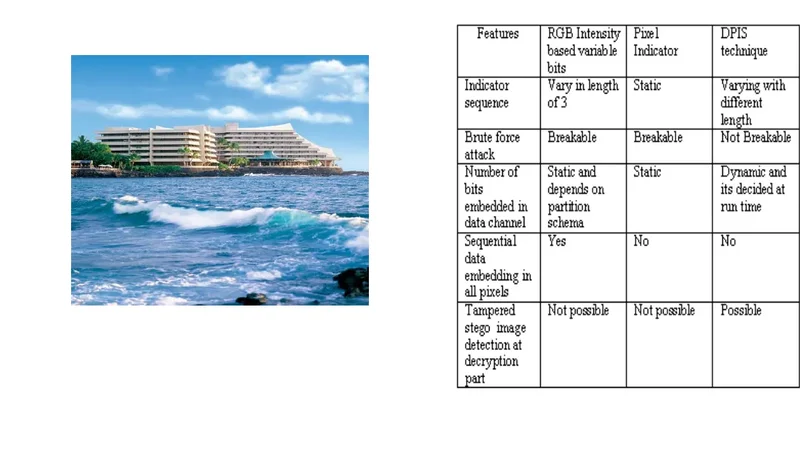
Dynamic Pattern Based Image Steganography

Efficient Design for the Implementation of Wong-Lam Multicast Authentication Protocol Using Two-Levels of Parallelism
End-to-End Privacy for Open Big Data Markets
End-to-end verifiability

Enhancing the security of caesar cipher substitution method using a randomized approach for more secure communication

Environment Based Secure Transfer of Data in Wireless Sensor Networks

Evolution of an Emerging Symmetric Quantum Cryptographic Algorithm
Facts, myths and fights about the KLJN classical physical key exchanger
Formalising Surveillance and Identity
Framework for Wireless Network Security using Quantum Cryptography
Graph Theory Applications in Network Security
Hidden and Uncontrolled - On the Emergence of Network Steganographic Threats
Implementation of Secure Quantum Protocol using Multiple Photons for Communication
Improved Secure Address Resolution Protocol

Information Retrieval From Internet Applications For Digital Forensic
iPrivacy: a Distributed Approach to Privacy on the Cloud
Is Your Data Gone? Comparing Perceived Effectiveness of Thumb Drive Deletion Methods to Actual Effectiveness
JASF: Jasta Security Framework