Cs-Cr


Homomorphic Payment Addresses and the Pay-to-Contract Protocol
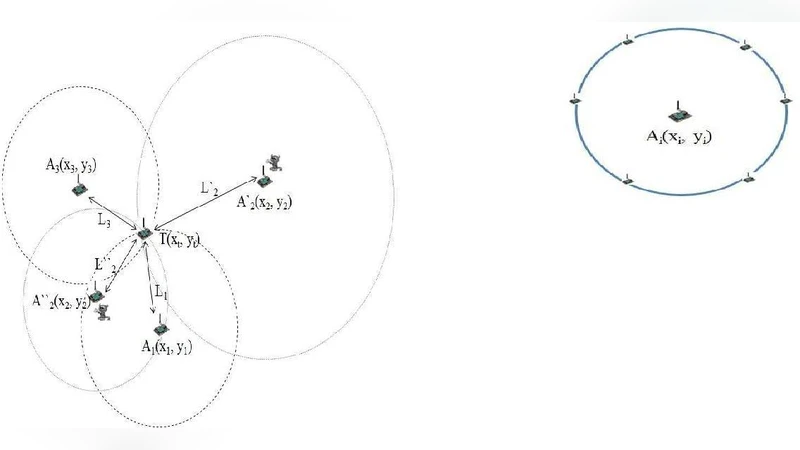
Identifying Cheating Anchor Nodes using Maximum Likelihood and Mahalanobis Distance
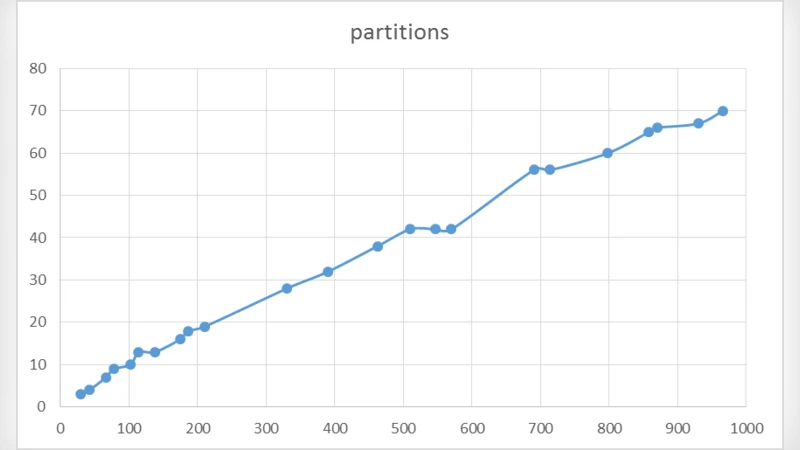
Generating Primes Using Partitions
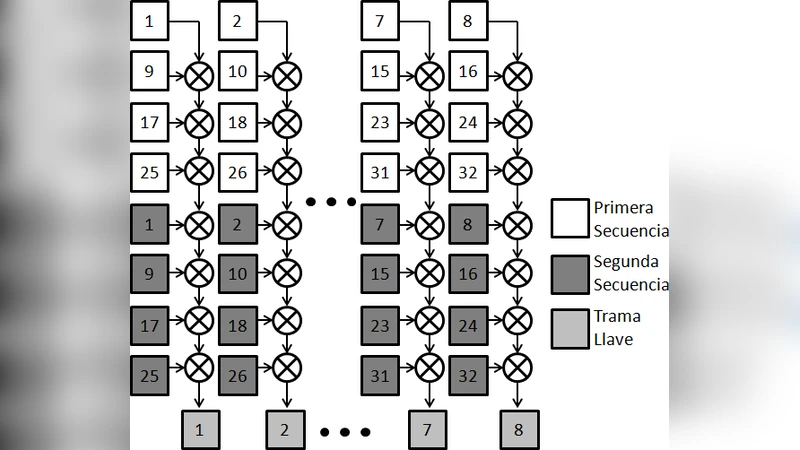
Implementation of a Stream Cipher Based on Bernoullis Map
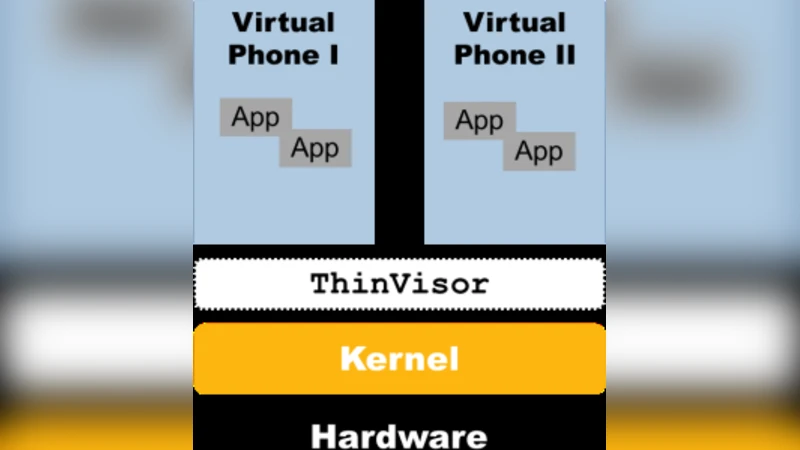
Evaluation of Security Solutions for Android Systems

Instantly Obsoleting the Address-code Associations: A New Principle for Defending Advanced Code Reuse Attack
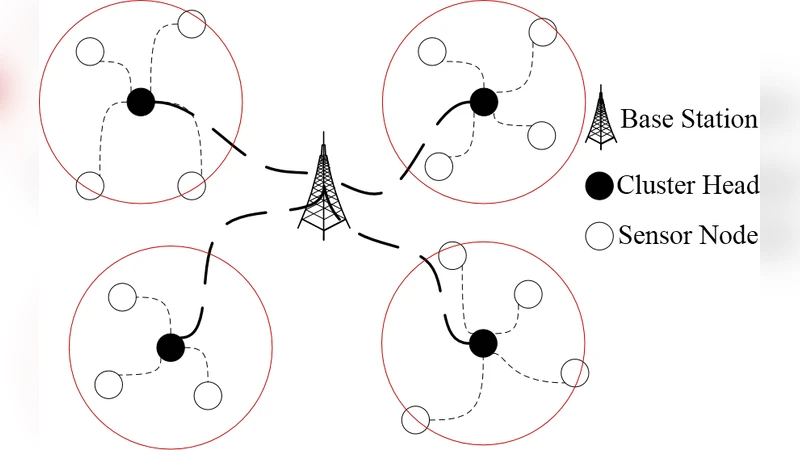
A Hierarchical Key Management Scheme for Wireless Sensor Networks Based on Identity-based Encryption
"The Good, The Bad And The Ugly": Evaluation of Wi-Fi Steganography
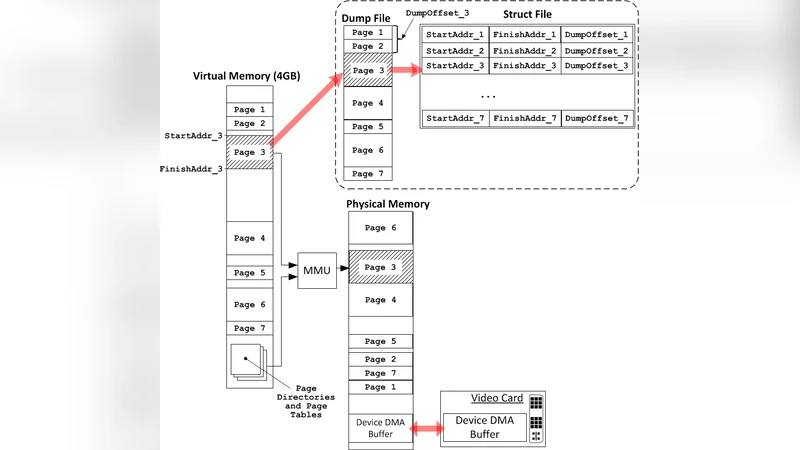
Applying Memory Forensics to Rootkit Detection
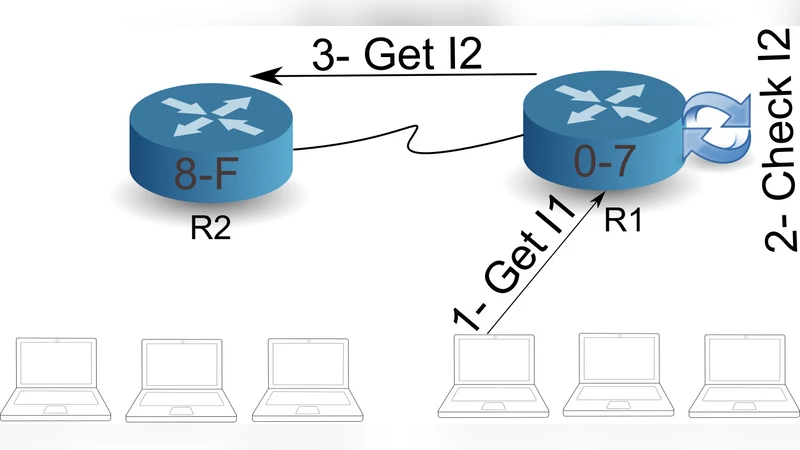
A Secure Communication in Mobile Agent System
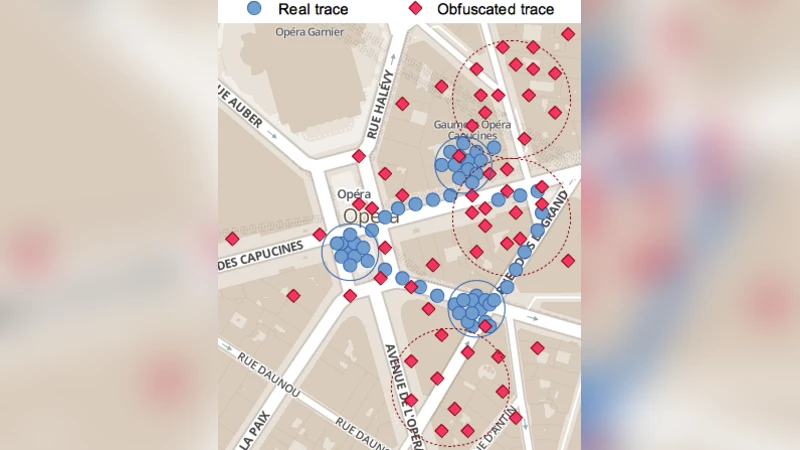
Differentially Private Location Privacy in Practice
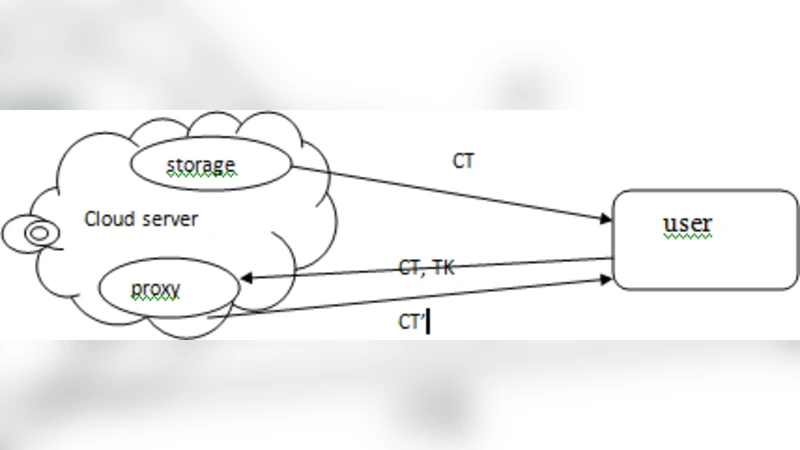
Concrete Attribute-Based Encryption Scheme with Verifiable Outsourced Decryption
Non-commutative Digital Signatures

A Public Key Cryptoscheme Using Bit-pairs and Probabilistic Mazes
A Piggybank Protocol for Quantum Cryptography

A Provenance-Policy Based Access Control Model For Data Usage Validation In Cloud
Goldbach Circles and Balloons and Their Cross Correlation
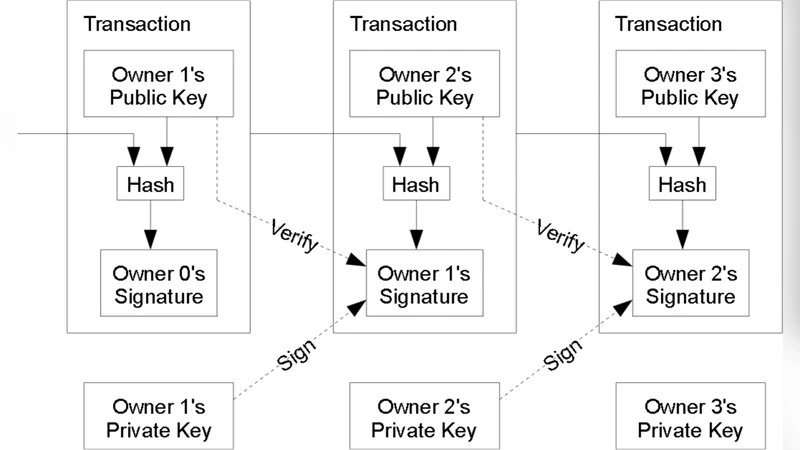
Transaction Remote Release (TRR): A New Anonymization Technology for Bitcoin

A new Watermarking Technique for Medical Image using Hierarchical Encryption

A Forensically Sound Adversary Model for Mobile Devices
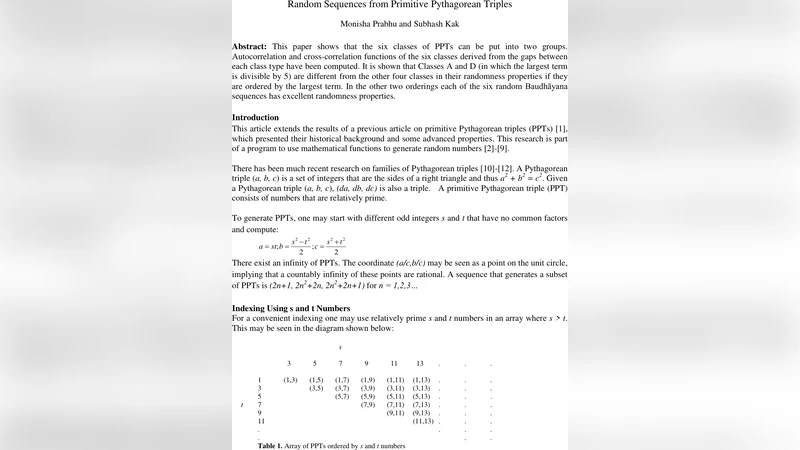
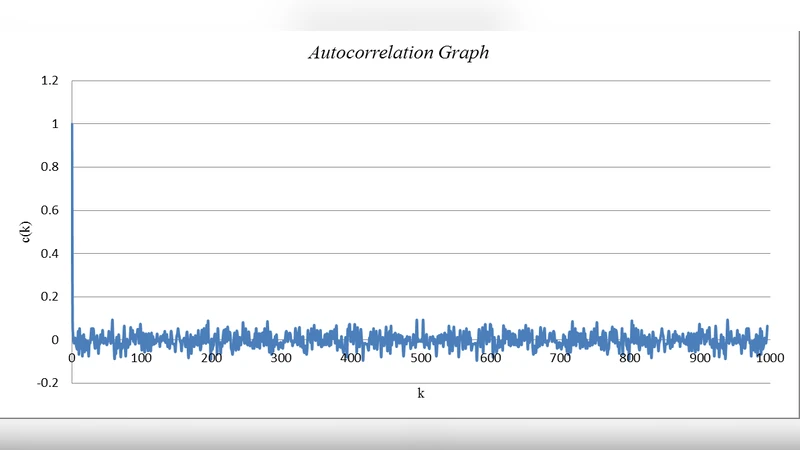
Random Sequences from Primitive Pythagorean Triples
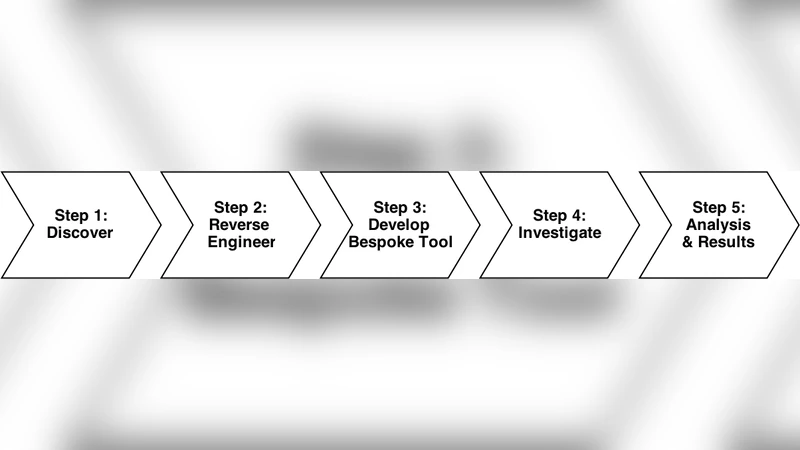
The Case for a Collaborative Universal Peer-to-Peer Botnet Investigation Framework