Cs-Cr

Differentially Private Grids for Geospatial Data
A mathematical problem for security analysis of hash functions and pseudorandom generators
APRAP: Another Privacy Preserving RFID Authentication Protocol
Study of Security Issues in Pervasive Environment of Next Generation Internet of Things
Optical Encryption with Jigsaw Transform using Matlab

FuGeIDS: Fuzzy Genetic paradigms in Intrusion Detection Systems

Simplification Resilient LDPC-Coded Sparse-QIM Watermarking for 3D-Meshes

Time Synchronization Attack in Smart Grid-Part II: Cross Layer Detection Mechanism
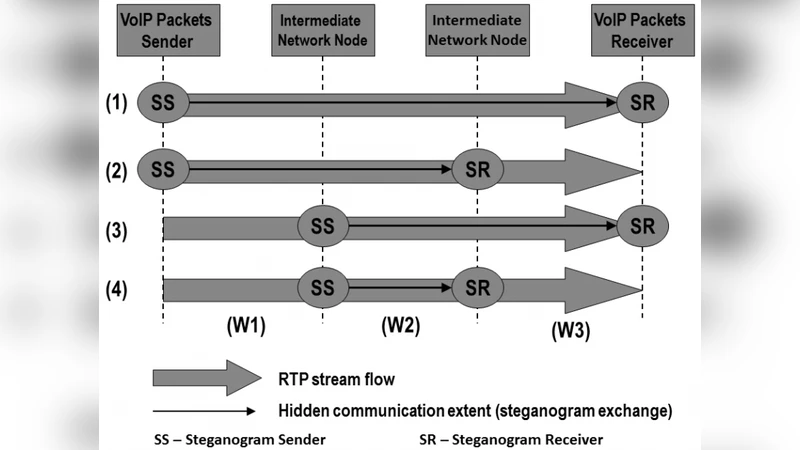
VoIP Steganography and Its Detection - A Survey
Personal data disclosure and data breaches: the customers viewpoint

BotMosaic: Collaborative Network Watermark for Botnet Detection
A Novel Data Hiding Scheme for Binary Images

On Randomness of Goldbach Sequences
A Key Pre-Distribution Scheme based on Multiple Block Codes for Wireless Sensor Networks

Torsion Limits and Riemann-Roch Systems for Function Fields and Applications

Noninterference with Local Policies
Breaking a novel colour image encryption algorithm based on chaos
Stream on the Sky: Outsourcing Access Control Enforcement for Stream Data to the Cloud
Mining Permission Request Patterns from Android and Facebook Applications (extended author version)
A machine learning approach to anomaly-based detection on Android platforms
A Socio-Technical approach to address the Information security: Using the 27001 Manager Artefact
A Survey on Detection of Sinkhole Attack in Wireless Sensor Network