
Cs-Cr


A Survey on Authentication and Key Agreement Protocols in Heterogeneous Networks
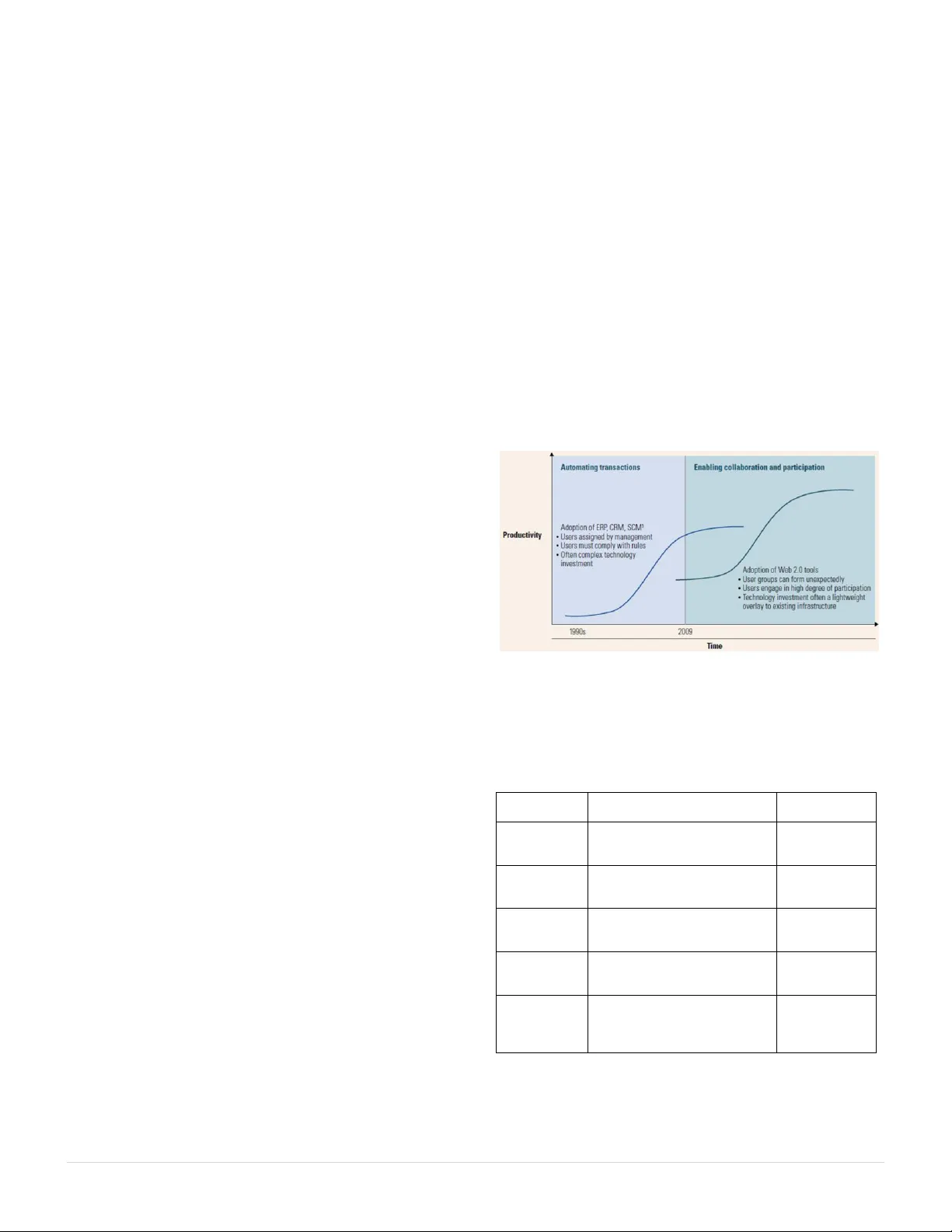
Web 2.0 Technologies and Social Networking Security Fears in Enterprises

Genetic Algorithm to Make Persistent Security and Quality of Image in Steganography from RS Analysis

A Precise Information Flow Measure from Imprecise Probabilities

Polynomial functions of degree 20 which are APN infinitely often

An Analysis of the CAVES Attestation Protocol using CPSA

Implementing Access Control Markov Decision Processes with GLPK/GMPL

Functional Magnetic Resonance Imaging and the Challenge of Balancing Human Security with State Security

Memoryless Near-Collisions, Revisited

Secure CDMA Sequences

Towards Trustworthy Mobile Social Networking Services for Disaster Response

Symbian `vulnerability and Mobile Threats

A Logic of Interactive Proofs (Formal Theory of Knowledge Transfer)

A formal methodology for integral security design and verification of network protocols
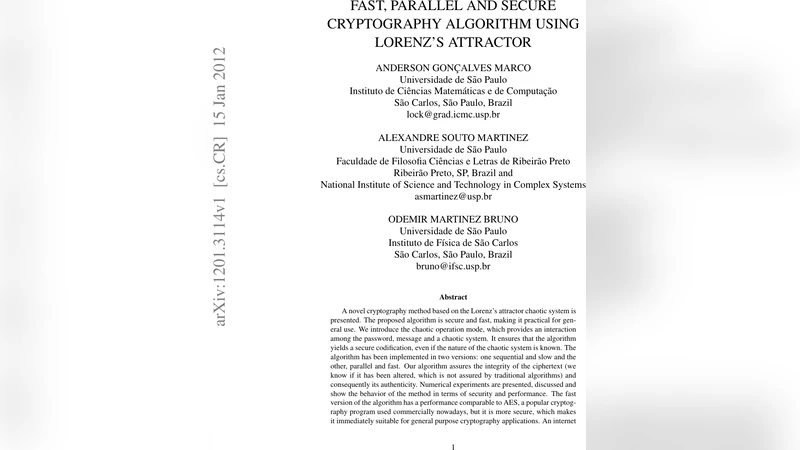
Fast, parallel and secure cryptography algorithm using Lorenzs attractor

A Novel Chaotic Encryption Scheme based on Pseudorandom Bit Padding

Improvements in closest point search based on dual HKZ-bases

Dynamic Session Key Exchange Method using Two S-Boxes
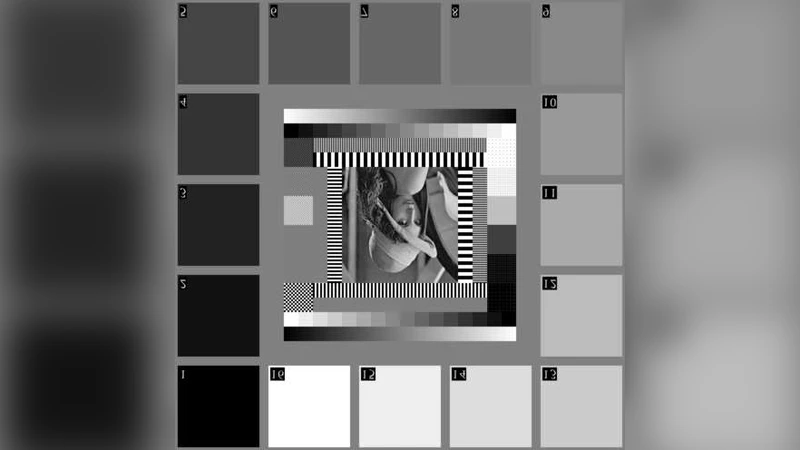
GA based robust blind digital watermarking

Influence of Speech Codecs Selection on Transcoding Steganography

Time Stamp Attack in Smart Grid: Physical Mechanism and Damage Analysis

Increasing the security of the ping-pong protocol by using many mutually unbiased bases
