
Cs-Cr


Integrated Key based Strict Friendliness Verification of Neighbors in MANET

Globally reasoning about localised security policies in distributed systems

Deducing Security Goals From Shape Analysis Sentences

Data Aggregation without Secure Channel: How to Evaluate a Multivariate Polynomial Securely

Pixastic: Steganography based Anti-Phihsing Browser Plug-in

Data Hiding Techniques using number decompositions

A Novel Effective, Secure and Robust CDMA Digital Image Watermarking in YUV Color Space Using DWT2
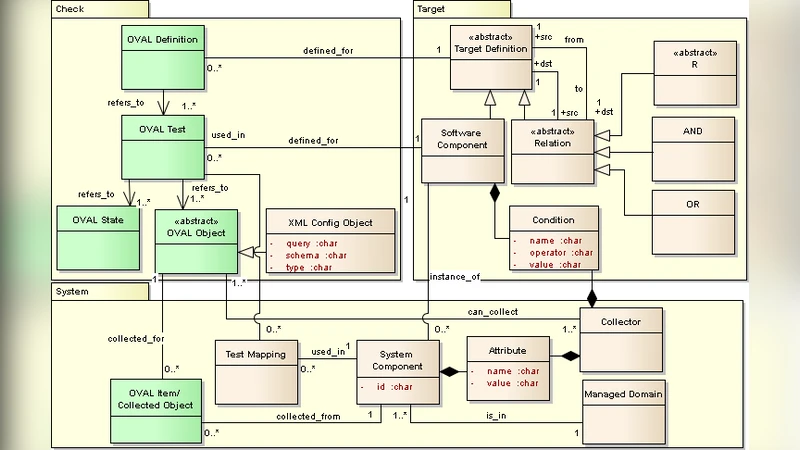
Detection of Configuration Vulnerabilities in Distributed (Web) Environments

Refining a Quantitative Information Flow Metric
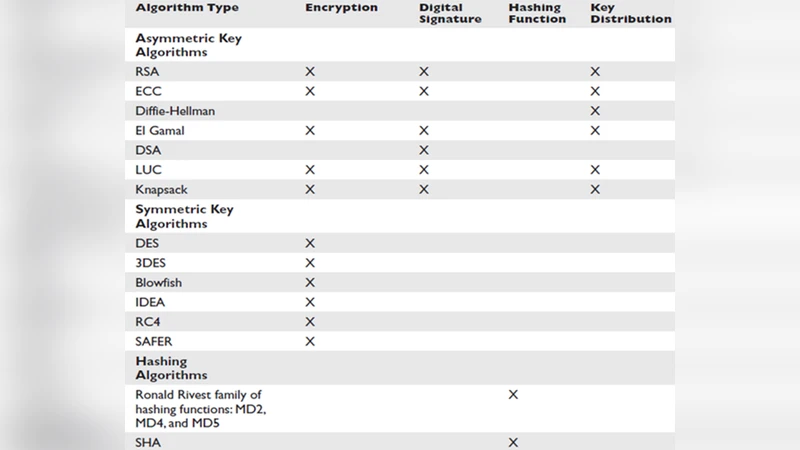
A Robust Cryptographic System using Neighborhood-Generated Keys

Cryptanalysis and Improvements on Some Graph-based Authentication Schemes

Algebraic properties of generalized Rijndael-like ciphers

A Review of Techniques to Mitigate Sybil Attacks

Wireless Public key Infrastructure for Mobile Phones
Exploring Relay Cooperation for Secure and Reliable Transmission in Two-Hop Wireless Networks

Low Rank Mechanism for Optimizing Batch Queries under Differential Privacy

A Text Steganography Method Using Pangram and Image Mediums

Multilevel Image Encryption

IP over Voice-over-IP for censorship circumvention

In-Vivo Bytecode Instrumentation for Improving Privacy on Android Smartphones in Uncertain Environments

On Constant-Round Concurrent Zero-Knowledge from a Knowledge Assumption

Poisoning Attacks against Support Vector Machines
