Cs-Cr
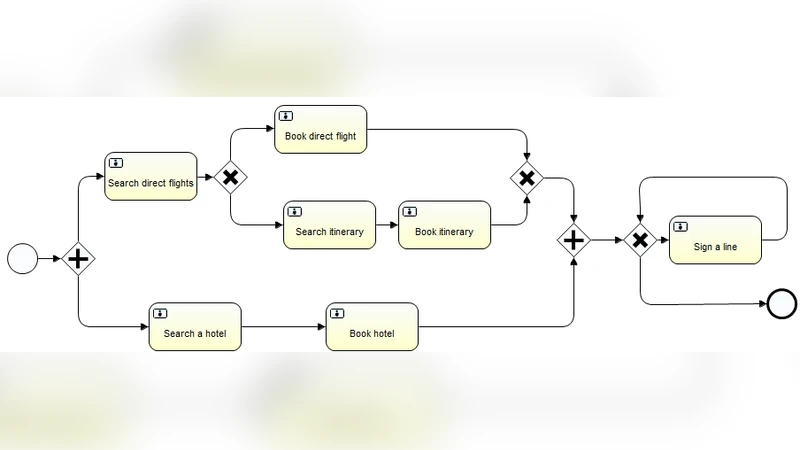
Metric-Aware Secure Service Orchestration

IPv6 Prefix Alteration: An Opportunity to Improve Online Privacy
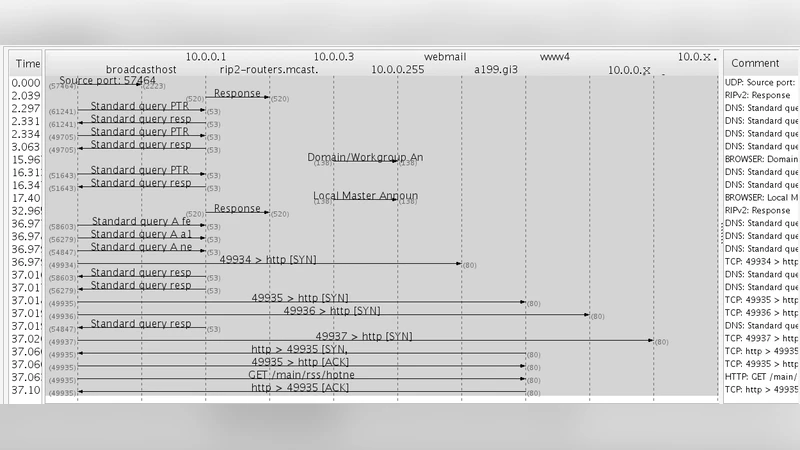
Implementation of Portion Approach in Distributed Firewall Application for Network Security Framework
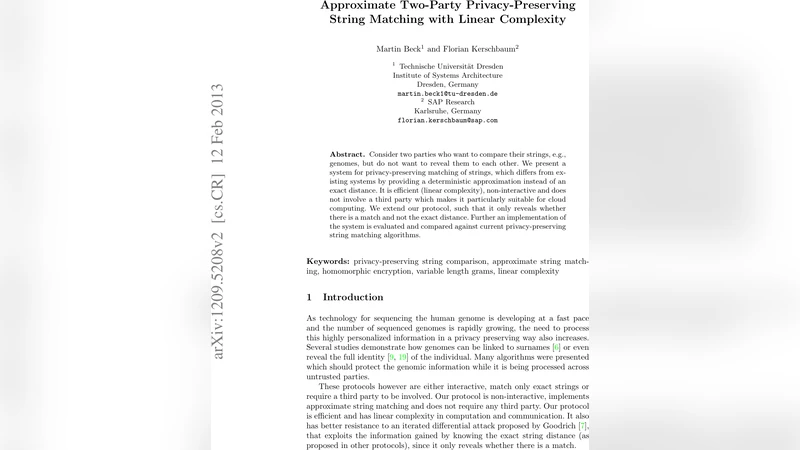
Approximate Two-Party Privacy-Preserving String Matching with Linear Complexity

A Novel Framework using Elliptic Curve Cryptography for Extremely Secure Transmission in Distributed Privacy Preserving Data Mining
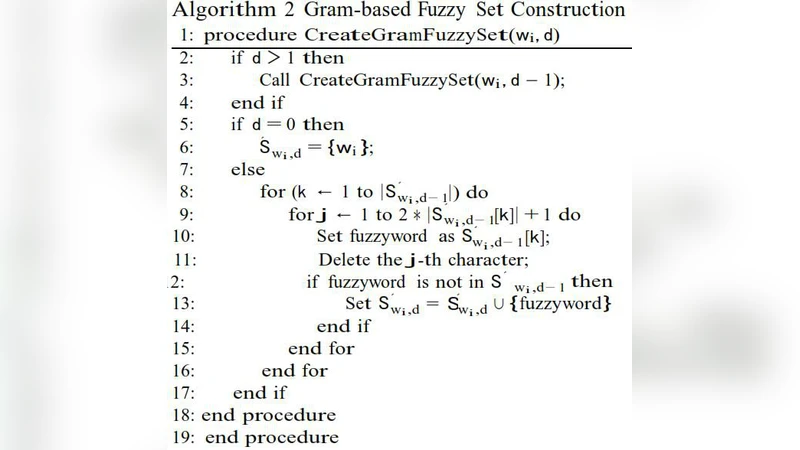
Fuzzy Keyword Search over Encrypted Data using Symbol-Based Trie-traverse Search Scheme in Cloud Computing

Unilateral Antidotes to DNS Cache Poisoning
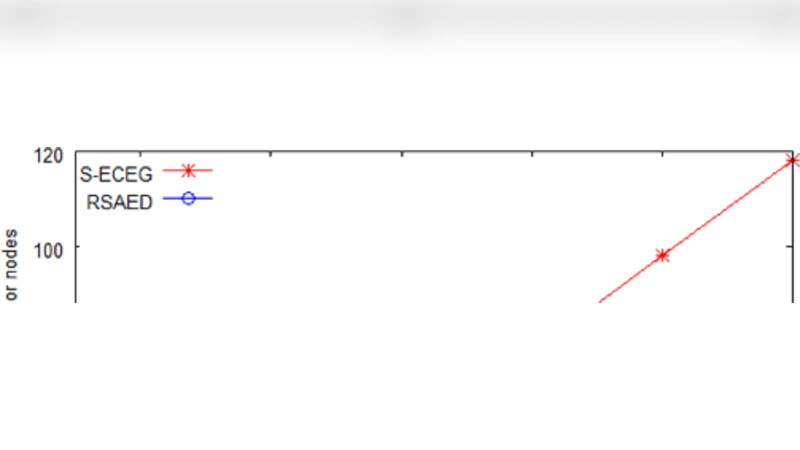
RSAED: Robust and Secure Aggregation of Encrypted Data in Wireless Sensor Networks

SecureSMART: A Security Architecture for BFT Replication Libraries
Information Hiding as a Challenge for Malware Detection

Sparse extractor families for all the entropy
ReDS: A Framework for Reputation-Enhanced DHTs

Distributed Secret Dissemination Across a Network

Cryptanalysis of a Public-key Cryptosystem Using Lattice Basis Reduction Algorithm

Proofs of Writing for Efficient and Robust Storage
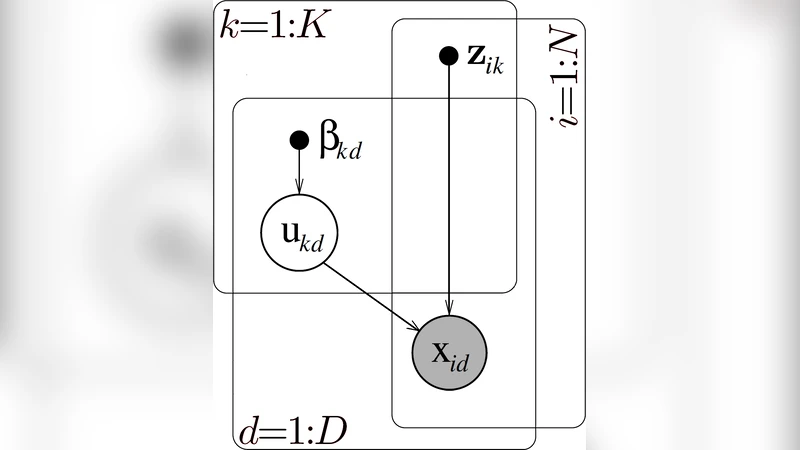
Role Mining with Probabilistic Models

Brandts Fully Private Auction Protocol Revisited

Practical, scalable alternative session encryption using one-time pads

Partial-indistinguishability obfuscation using braids
Exploring Relay Cooperation Scheme for Load-Balance Control in Two-hop Secure Communication System

Trends in Combating Image Spam E-mails

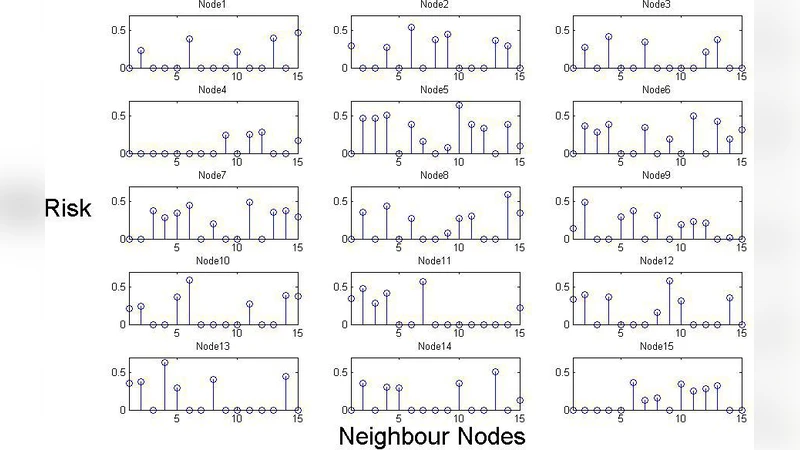
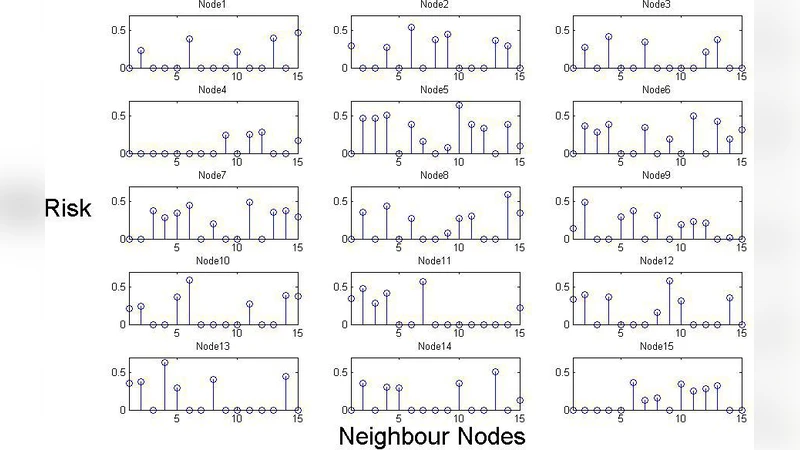
The risk assessment and treatment approach in order to provide lan security based on isms standard