
Cs-Cr

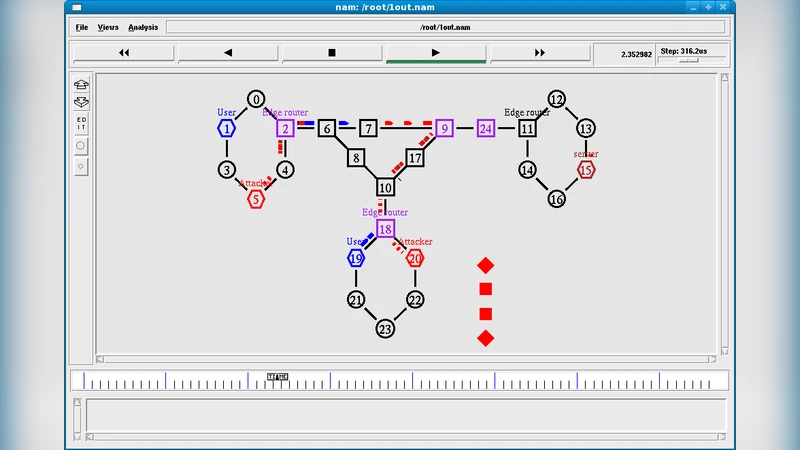
Distributed Denial of Service (DDoS) Attacks Detection Mechanism
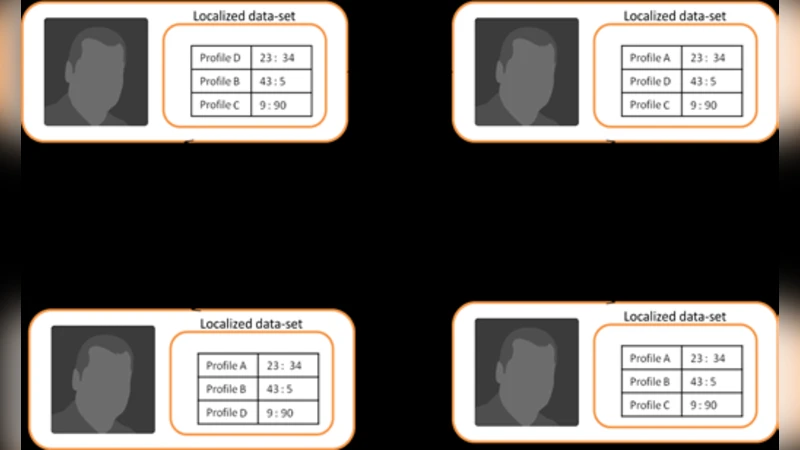
A Heuristic Reputation Based System to Detect Spam activities in a Social Networking Platform, HRSSSNP
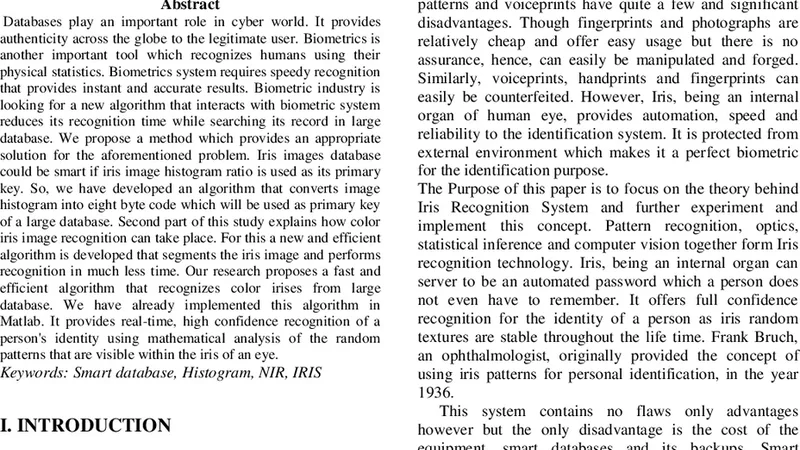
Fast Subsequent Color Iris Matching in large Database
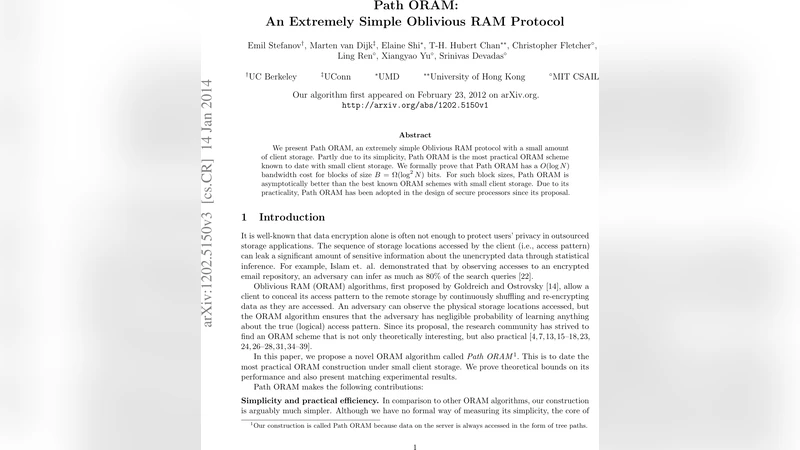
Path ORAM: An Extremely Simple Oblivious RAM Protocol

An Efficient Analytical Solution to Thwart DDoS Attacks in Public Domain

A coding theory foundation for the analysis of general unconditionally secure proof-of-retrievability schemes for cloud storage
Securing Instrumented Environments over Content-Centric Networking: the Case of Lighting Control
Efficient Quasigroup Block Cipher for Sensor Networks
Algorithm for searching bridges of specified types in the protection graph for Take-Grant protection model

Functional Programming and Security

An efficient classification in IBE Provide with an improvement of BB2 to an efficient Commutative Blinding scheme

Preserving privacy for secure and outsourcing for Linear Programming in cloud computing

Quantitative Information Flow as Safety and Liveness Hyperproperties
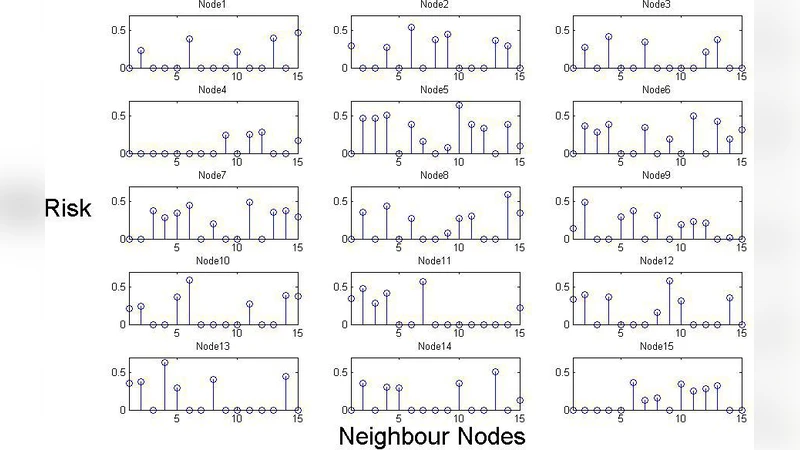
Risk Assessment Algorithm in Wireless Sensor Networks using Beta Distribution
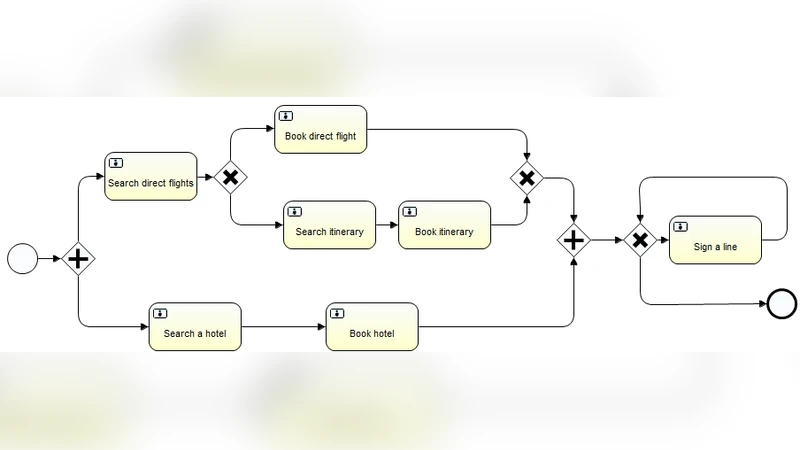
Metric-Aware Secure Service Orchestration

IPv6 Prefix Alteration: An Opportunity to Improve Online Privacy
Implementation of Portion Approach in Distributed Firewall Application for Network Security Framework
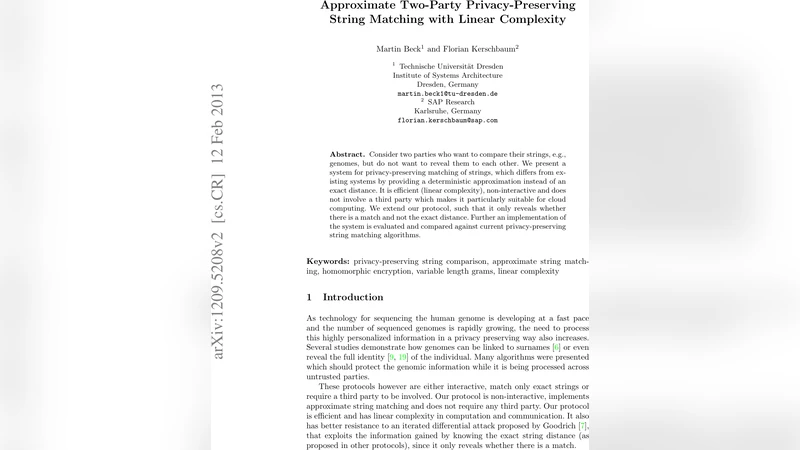
Approximate Two-Party Privacy-Preserving String Matching with Linear Complexity

A Novel Framework using Elliptic Curve Cryptography for Extremely Secure Transmission in Distributed Privacy Preserving Data Mining
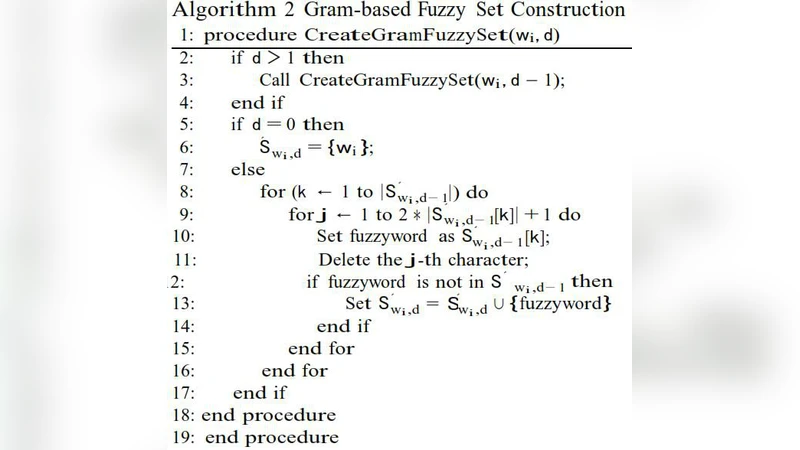
Fuzzy Keyword Search over Encrypted Data using Symbol-Based Trie-traverse Search Scheme in Cloud Computing

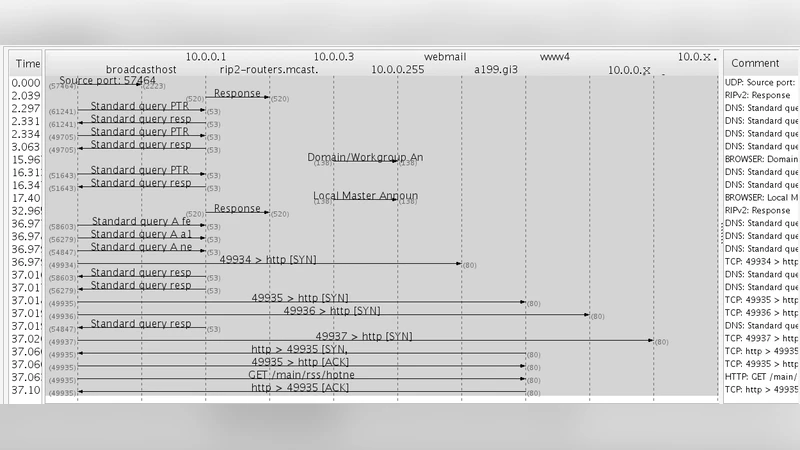
Unilateral Antidotes to DNS Cache Poisoning
RSAED: Robust and Secure Aggregation of Encrypted Data in Wireless Sensor Networks
