Cs-Cr

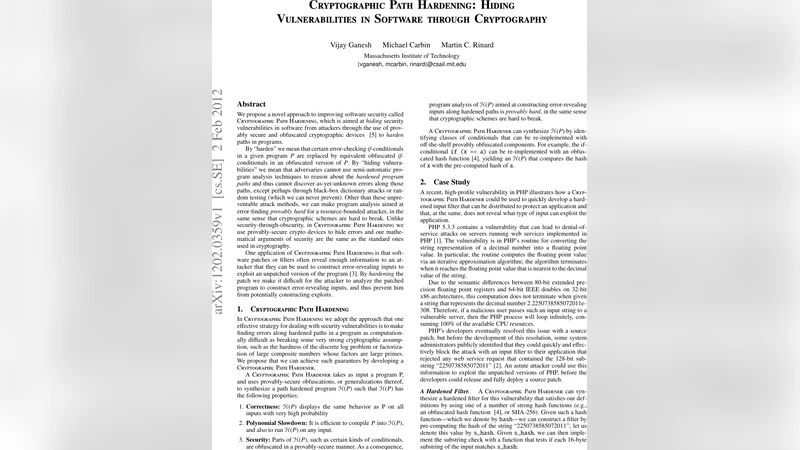
Cryptographic Path Hardening: Hiding Vulnerabilities in Software through Cryptography
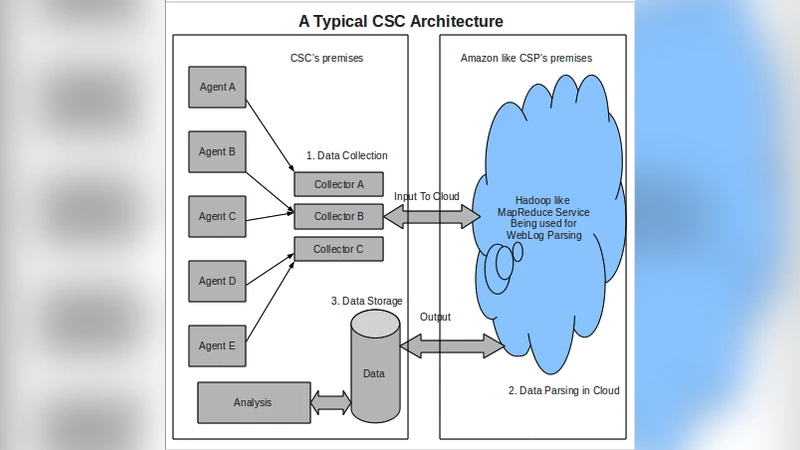
Confidentiality without Encryption For Cloud Computational Privacy

Genetic Programming for Multibiometrics
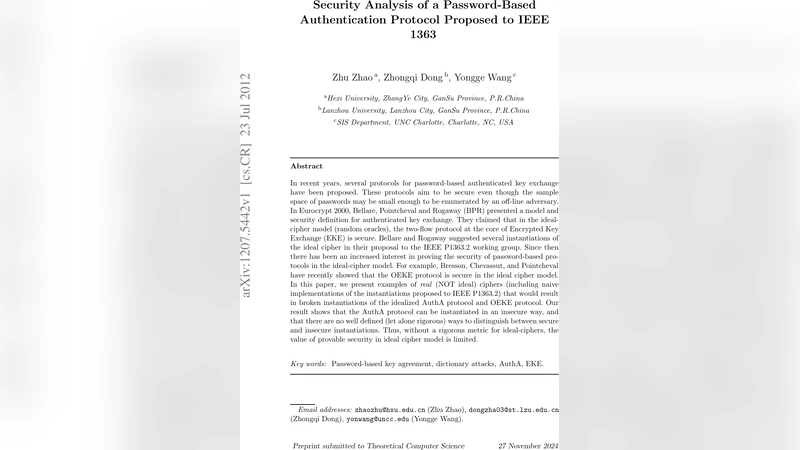
Security Analysis of a Password-Based Authentication Protocol Proposed to IEEE 1363
Flexible Dynamic Information Flow Control in the Presence of Exceptions
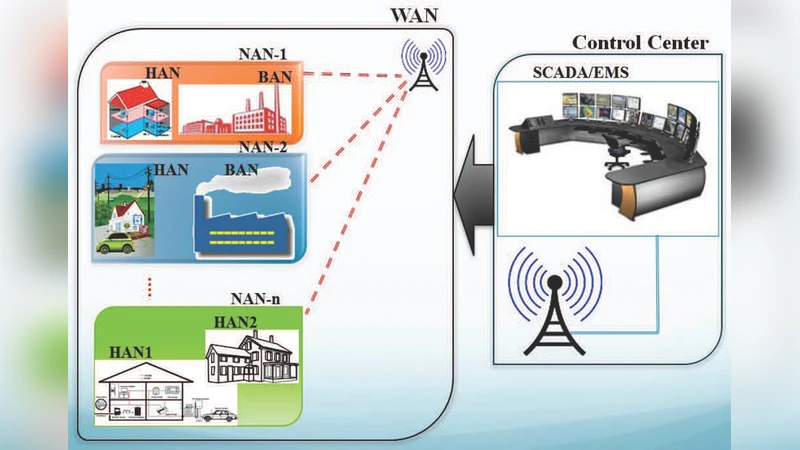
Highly Available Smart Grid Control Centers through Intrusion Tolerance
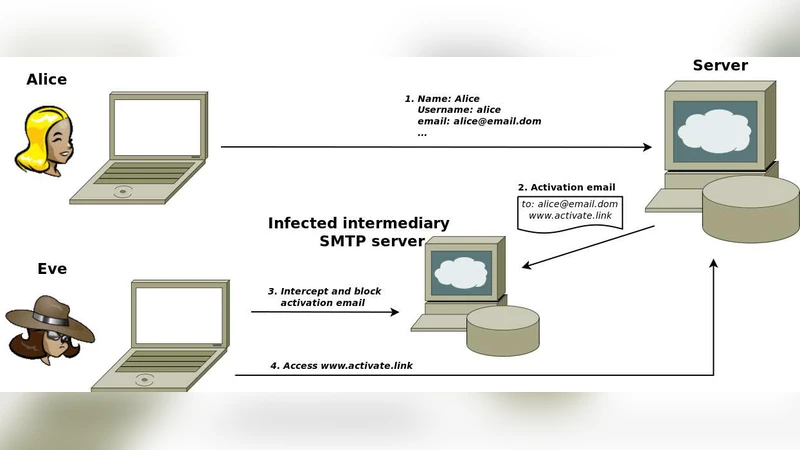
Formal security analysis of registration protocols for interactive systems: a methodology and a case of study
Self Authentication of color image through Wavelet Transformation Technique (SAWT)
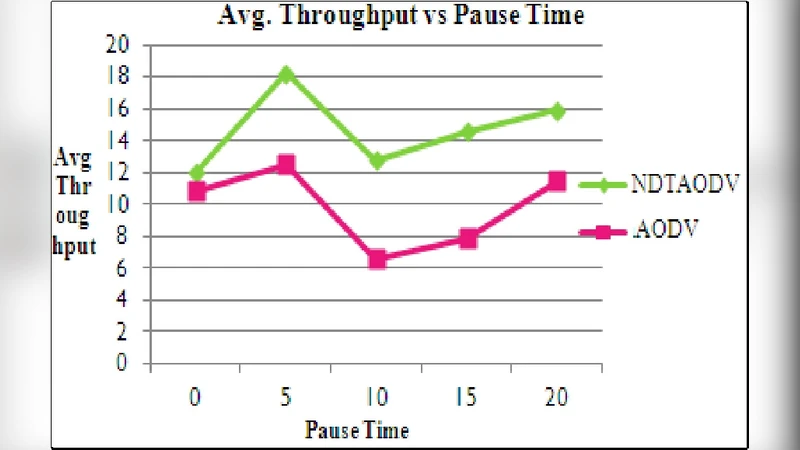
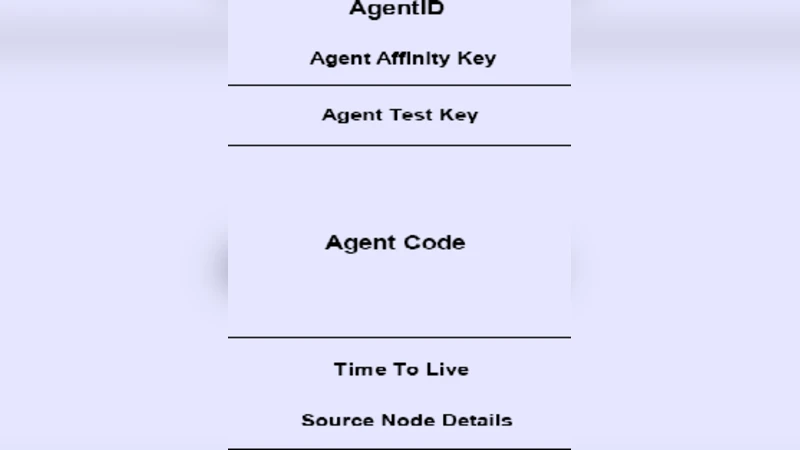
NDTAODV: Neighbor Defense Technique for Ad Hoc On-Demand Distance Vector(AODV) to mitigate flood attack in MANETS
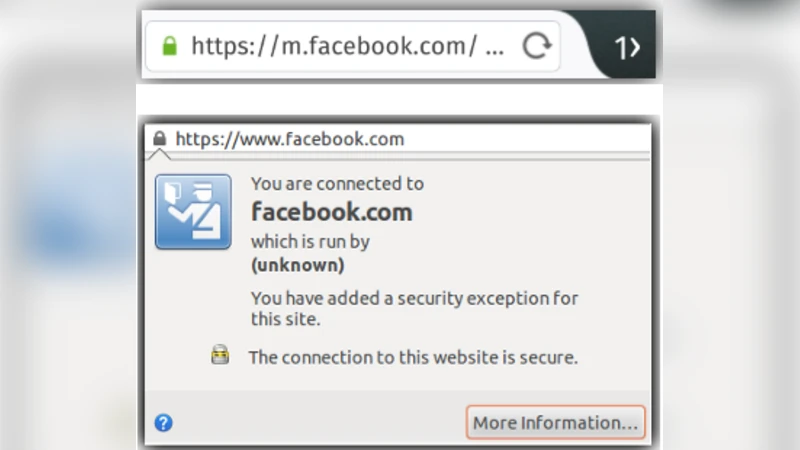
A First Look at Firefox OS Security
Towards Metamorphic Virus Recognition Using Eigenviruses
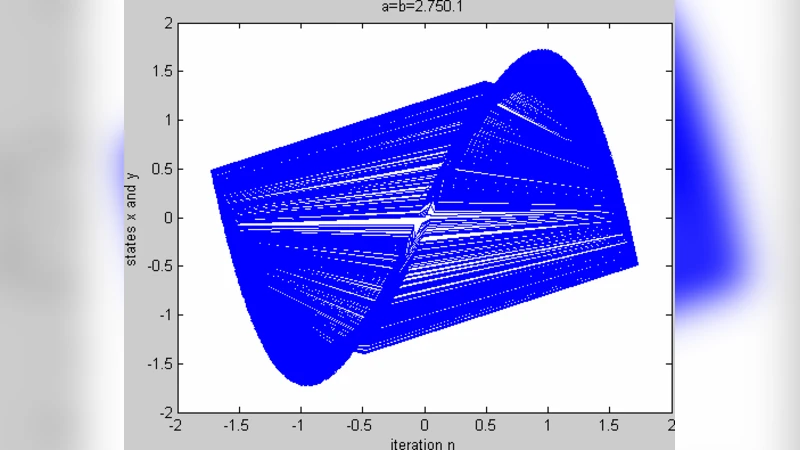
Message Embedded cipher using 2-D chaotic map
Bio Inspired Approach to Secure Routing in MANETs
A Review of Man-in-the-Middle Attacks
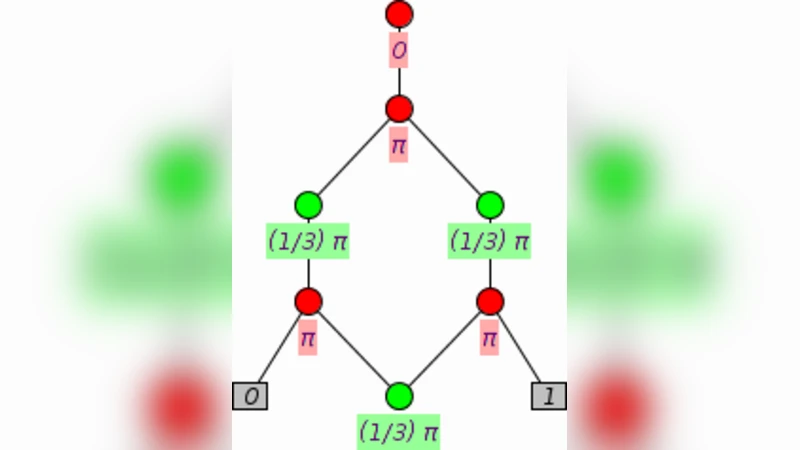
Superdense Coding with GHZ and Quantum Key Distribution with W in the ZX-calculus
TCP Injections for Fun and Clogging

Construction of LDGM lattices

Enforcing Access Control in Virtual Organizations Using Hierarchical Attribute-Based Encryption

A bias-free quantum random number generation using photon arrival time selectively
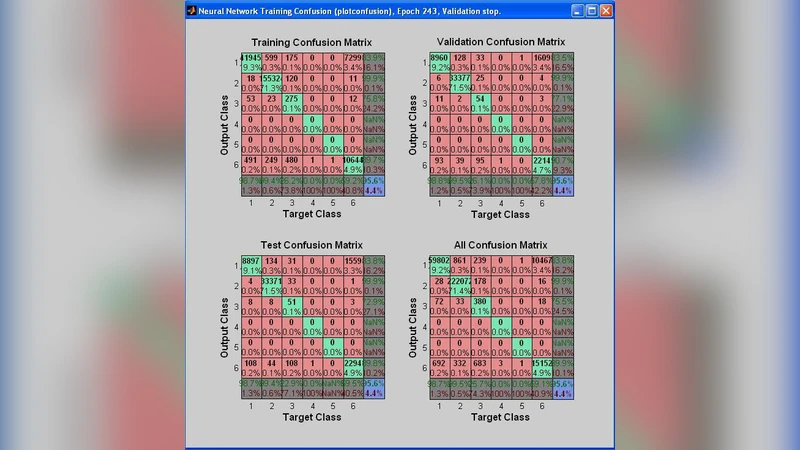
VHDL Modeling of Intrusion Detection & Prevention System (IDPS) A Neural Network Approach
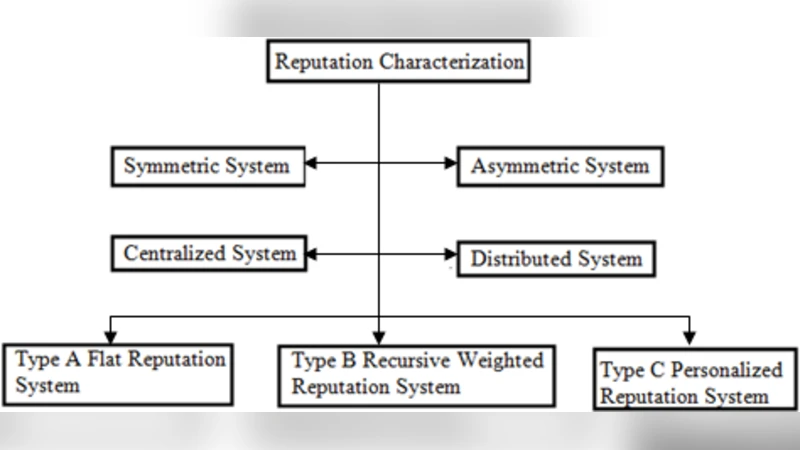
Referencing Tool for Reputation and Trust in Wireless Sensor Networks

You Only Live Twice or "The Years We Wasted Caring about Shoulder-Surfing"