Cs-Cr
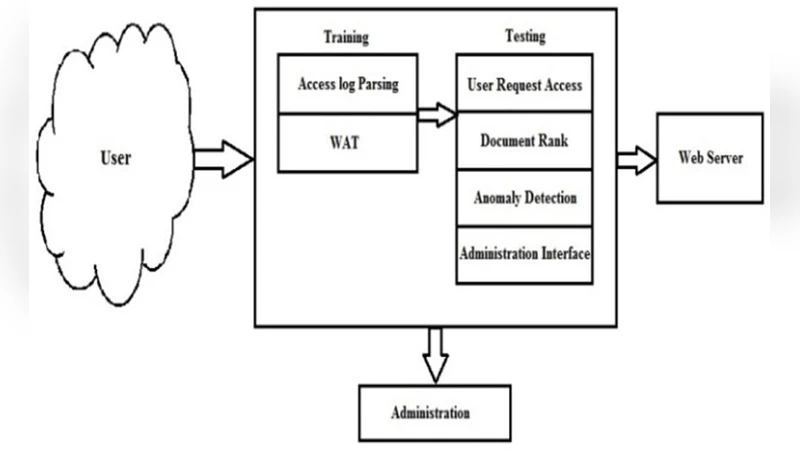
Anomaly Detection Based on Access Behavior and Document Rank Algorithm
Narayana Sequences for Cryptographic Applications
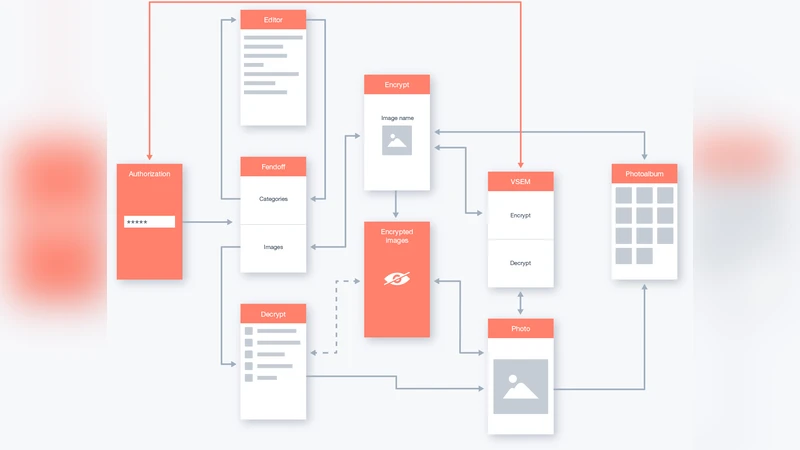
FendOff encryption software to secure personal information on computers and mobile devices
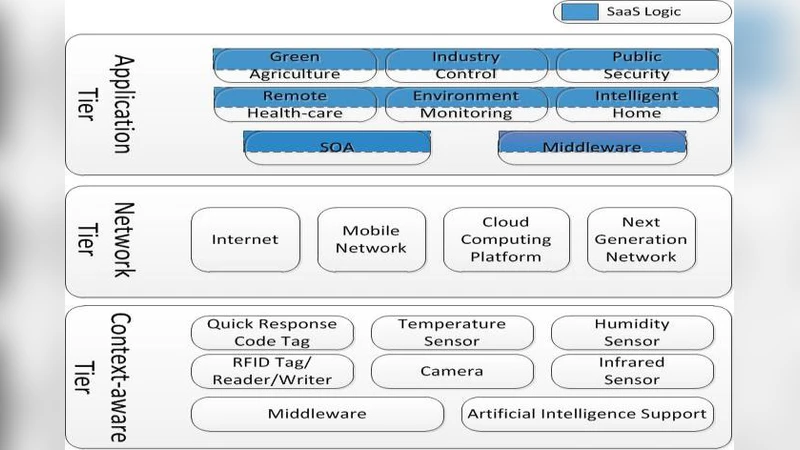
Software as a Service: Analyzing Security Issues
Classification of Various Security Techniques in Databases and their Comparative Analysis
Epistemic Temporal Logic for Information Flow Security

Ring Oscillator Physical Unclonable Function with Multi Level Supply Voltages
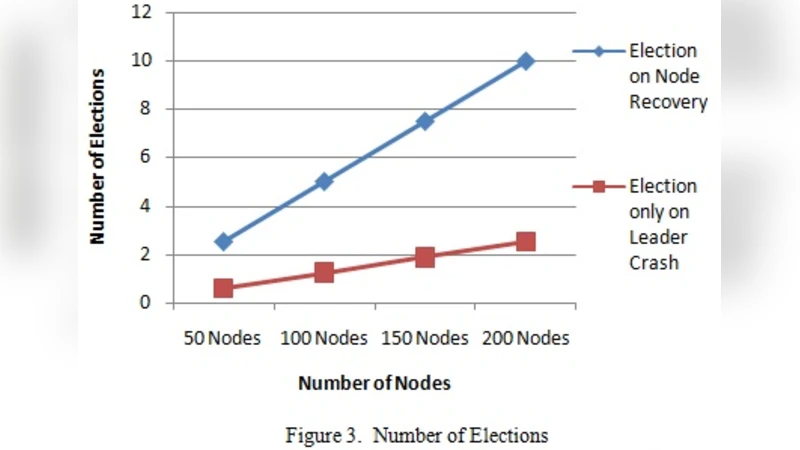
Analysis and Enhancements of Leader Elections algorithms in Mobile Ad Hoc Networks

Recovering Missing Coefficients in DCT-Transformed Images
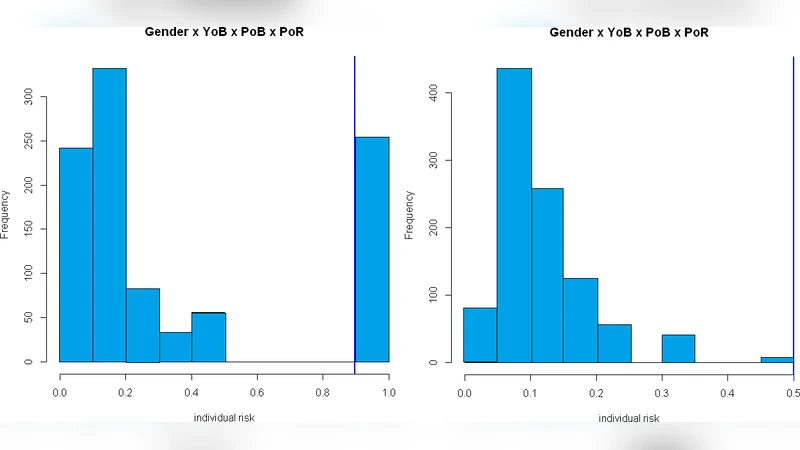
An experimental evaluation of de-identification tools for electronic health records
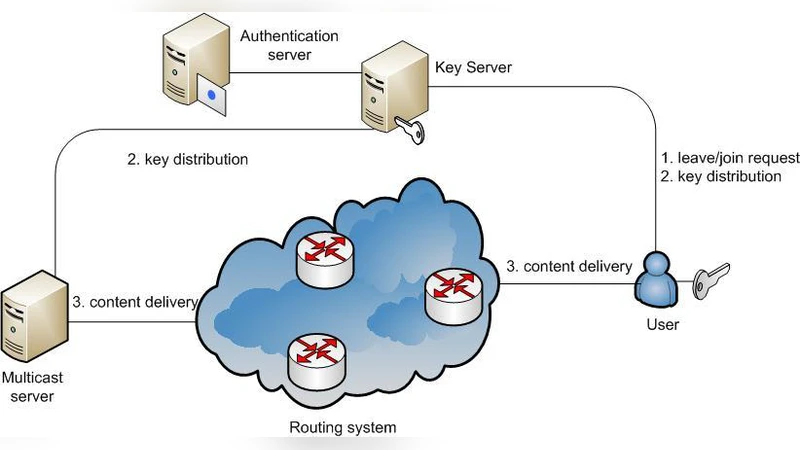
Efficient Group Key Management Schemes for Multicast Dynamic Communication Systems

Goldbach Triples and Key Distribution
Cryptographic Path Hardening: Hiding Vulnerabilities in Software through Cryptography
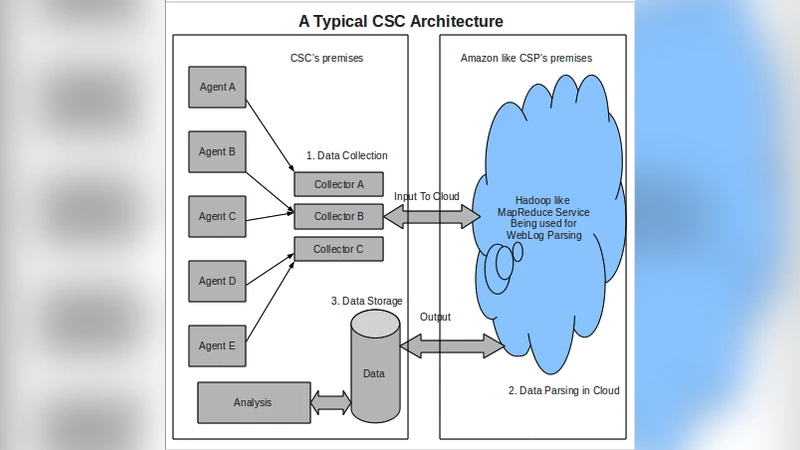
Confidentiality without Encryption For Cloud Computational Privacy

Genetic Programming for Multibiometrics
Security Analysis of a Password-Based Authentication Protocol Proposed to IEEE 1363
Flexible Dynamic Information Flow Control in the Presence of Exceptions
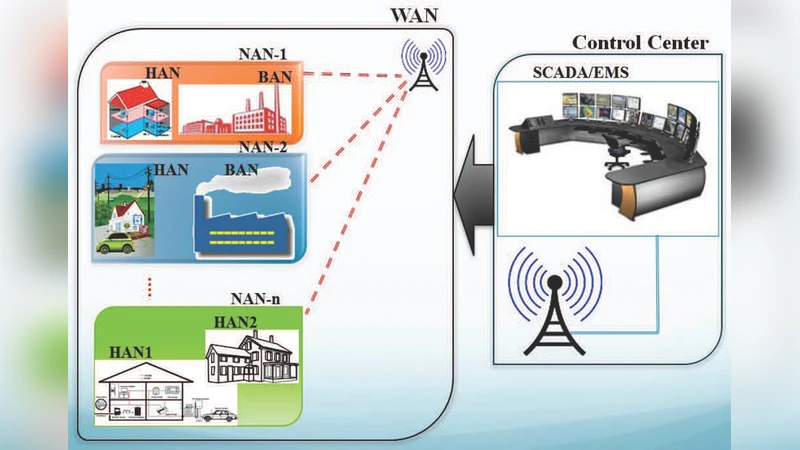
Highly Available Smart Grid Control Centers through Intrusion Tolerance
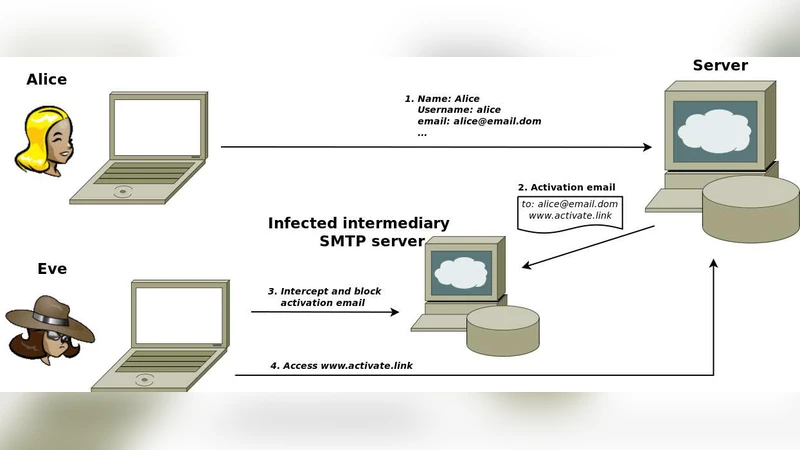
Formal security analysis of registration protocols for interactive systems: a methodology and a case of study
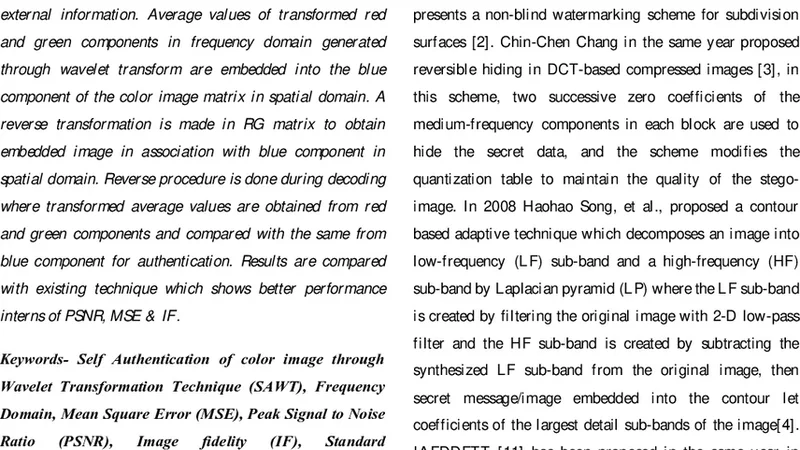
Self Authentication of color image through Wavelet Transformation Technique (SAWT)
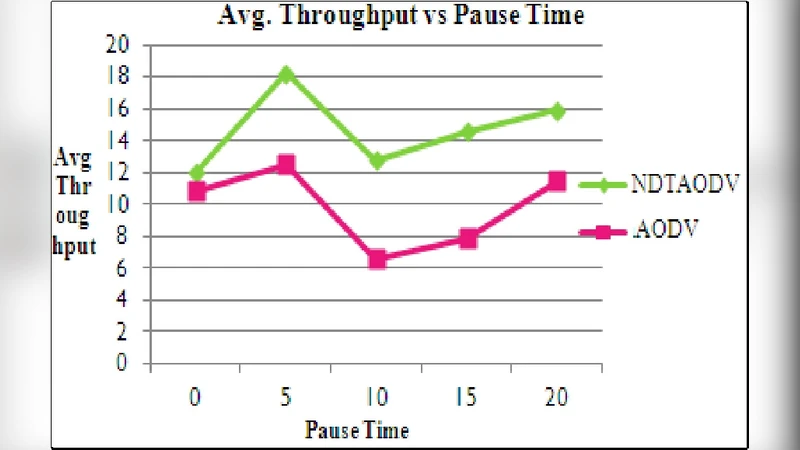
NDTAODV: Neighbor Defense Technique for Ad Hoc On-Demand Distance Vector(AODV) to mitigate flood attack in MANETS
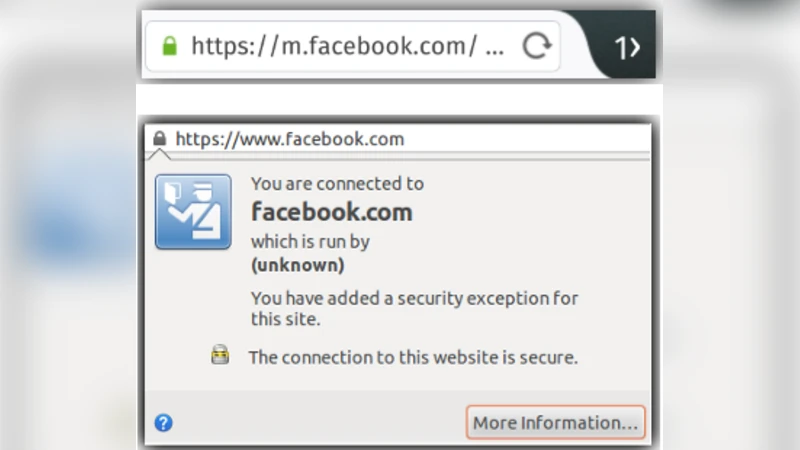
A First Look at Firefox OS Security