Cs-Cr
Position-Based Quantum Cryptography and the Garden-Hose Game

Nexus Authorization Logic (NAL): Logical Results
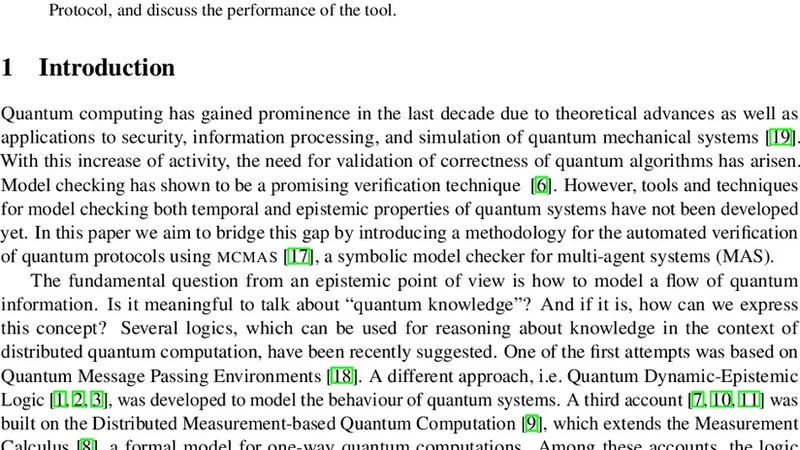
Automated Verification of Quantum Protocols using MCMAS
SybilControl: Practical Sybil Defense with Computational Puzzles

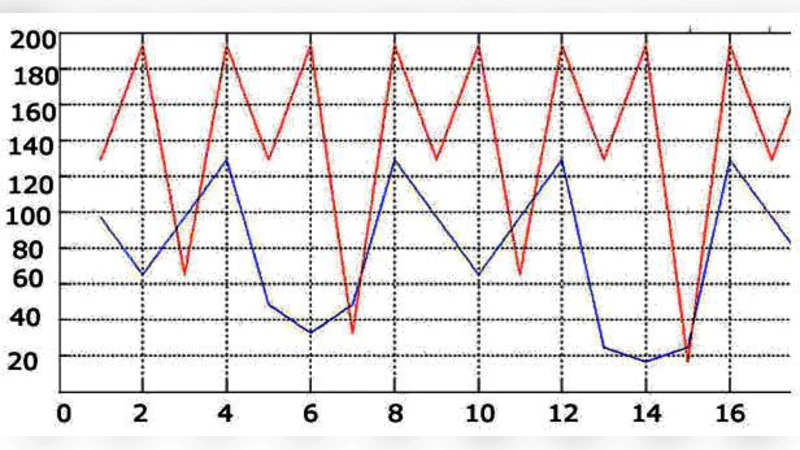
Detection techniques of selective forwarding attacks in wireless sensor networks: a survey
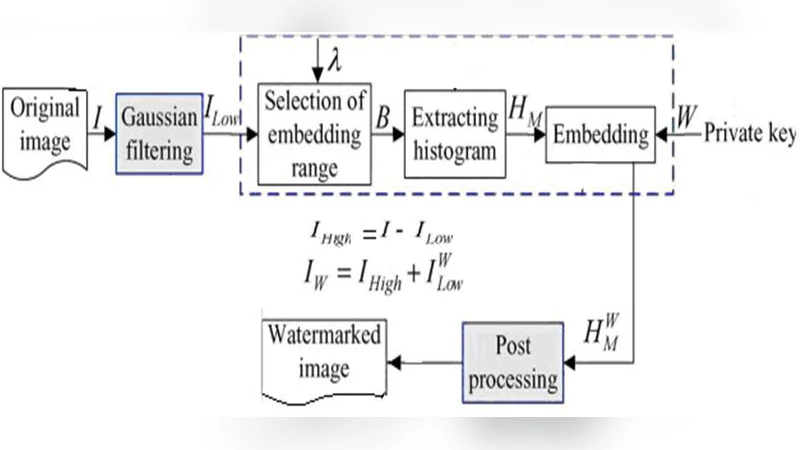
Multilayer image watermarking scheme for providing high security
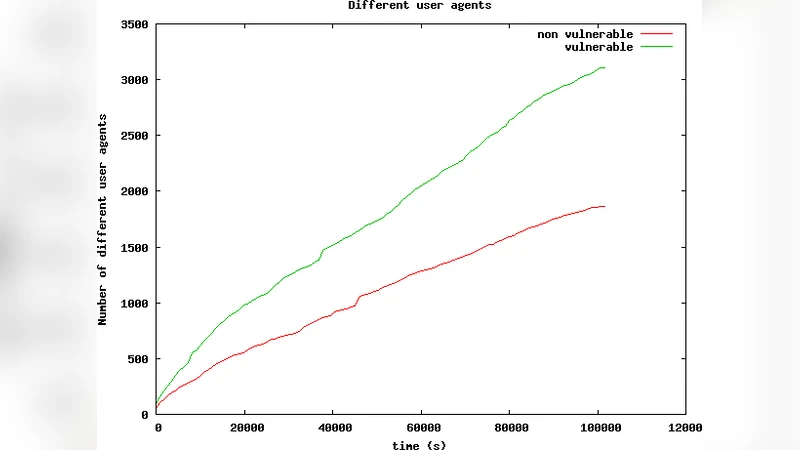
Torinj : Automated Exploitation Malware Targeting Tor Users
A Novel Advanced Heap Corruption and Security Method
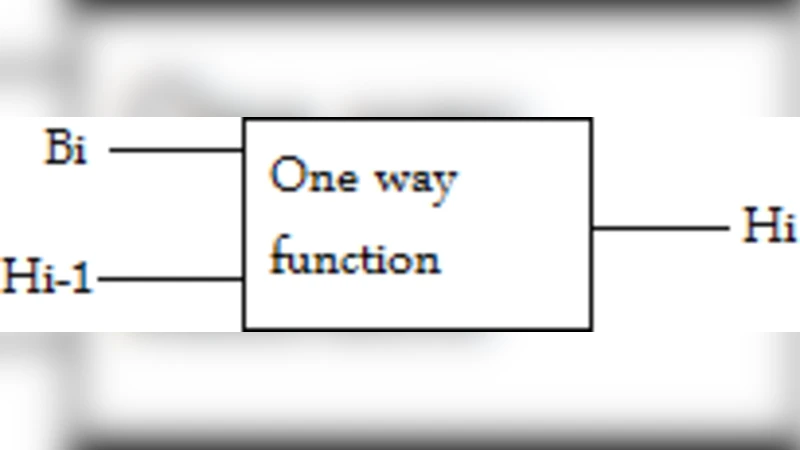
A Class of Non Invertible Matrices in GF (2) for Practical One Way Hash Algorithm

Secondary Constructions of Bent Functions and Highly Nonlinear Resilient Functions
Distributed Denial of Service Prevention Techniques

Optimizing One Fair Document Exchange Protocol
Security Penetration Test Framework for the Diameter Protocol
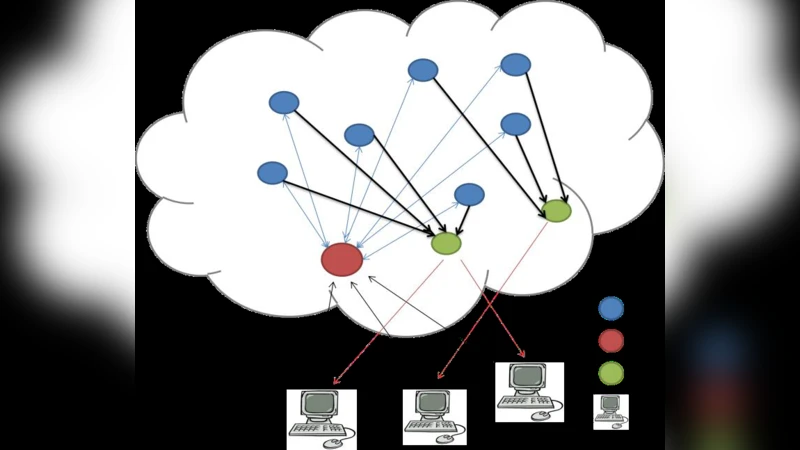
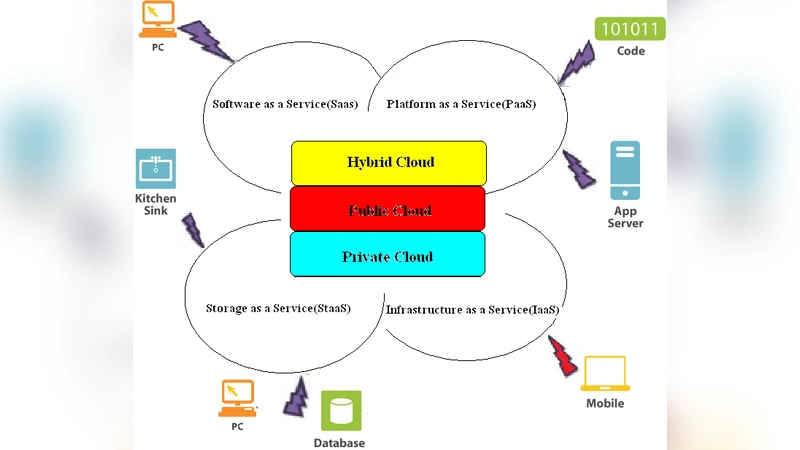
On the use of homomorphic encryption to secure cloud computing, services, and routing protocols
A PAXOS based State Machine Replication System for Anomaly Detection
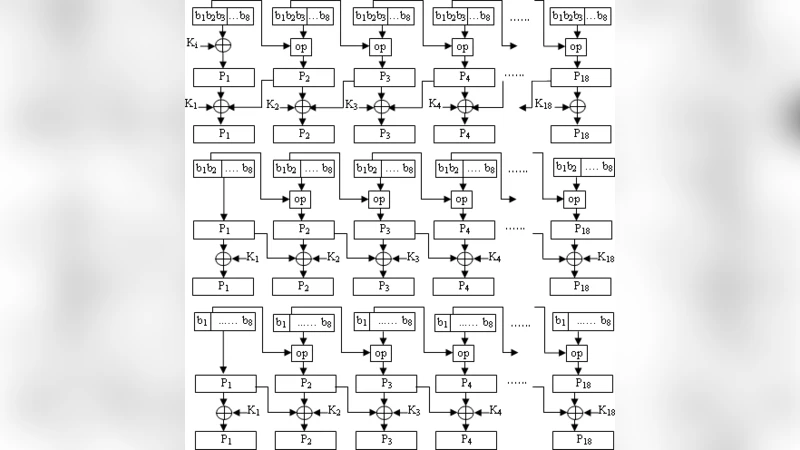
Proposal of a New Block Cipher reasonably Non-Vulnerable against Cryptanalytic Attacks
Design and Analysis of a Novel Digital Image Encryption Scheme

Public Key Cryptography Standards: PKCS
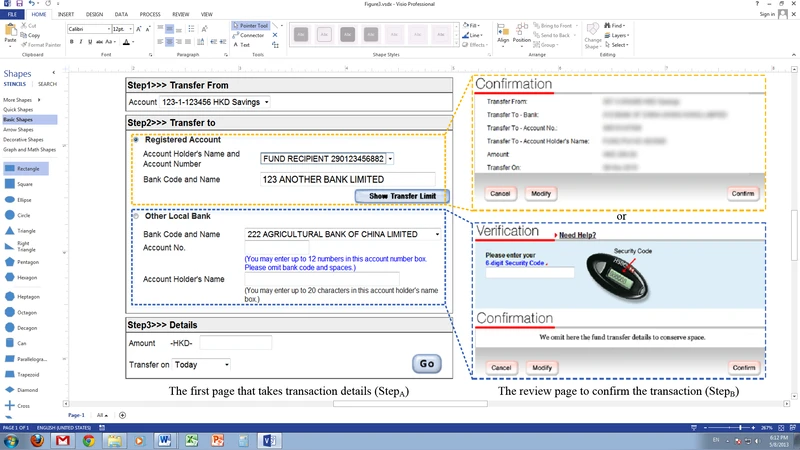
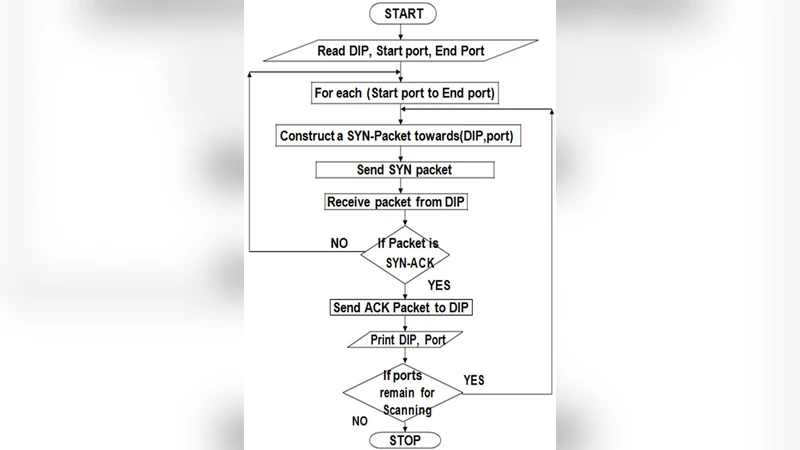
Scanning of Rich Web Applications for Parameter Tampering Vulnerabilities

Auditing for Distributed Storage Systems
High Security Image Steganography with Modified Arnold cat map
Securing the Data in Clouds with Hyperelliptic Curve Cryptography