Cs-Cr
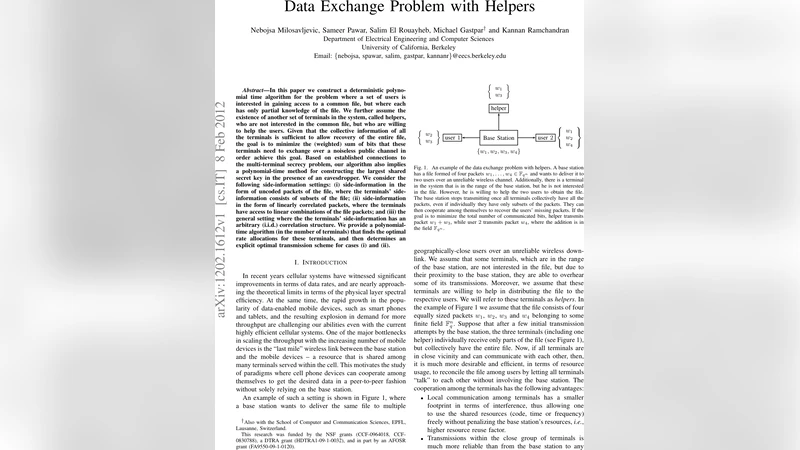
Data Exchange Problem with Helpers
The Effective Key Length of Watermarking Schemes
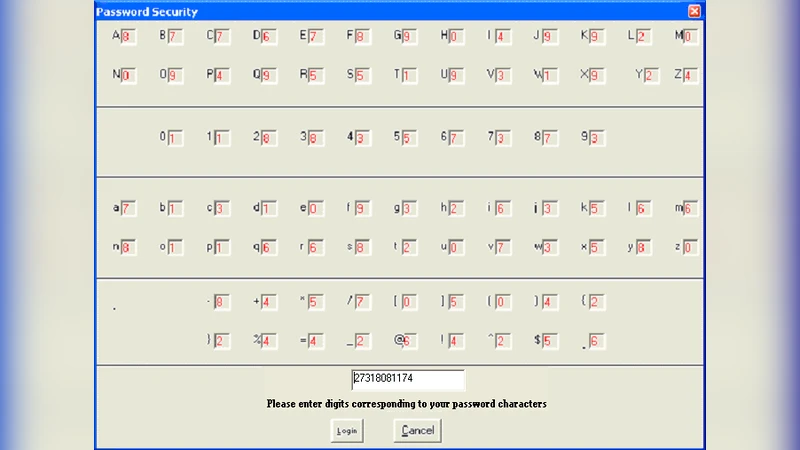
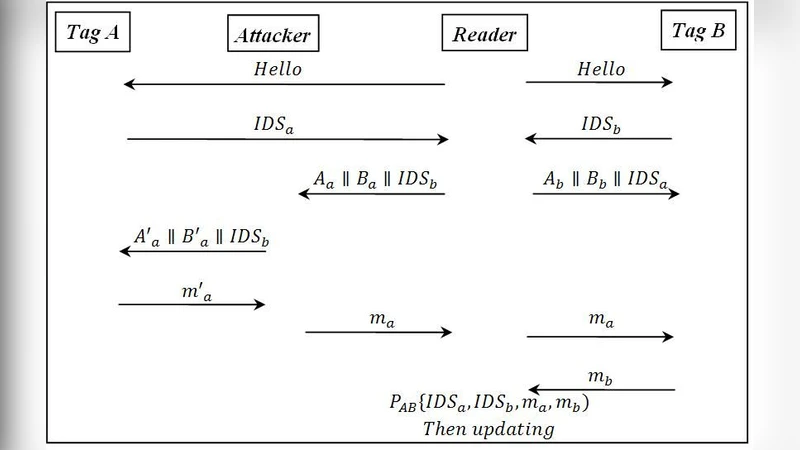
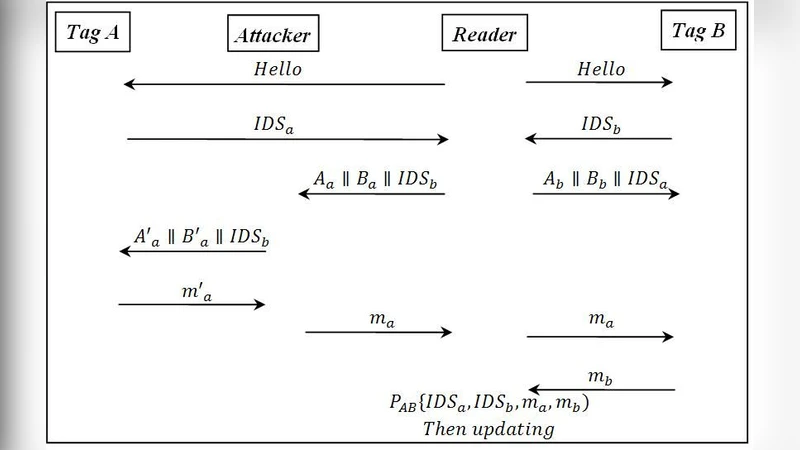
Password Authentication Scheme with Secured Login Interface
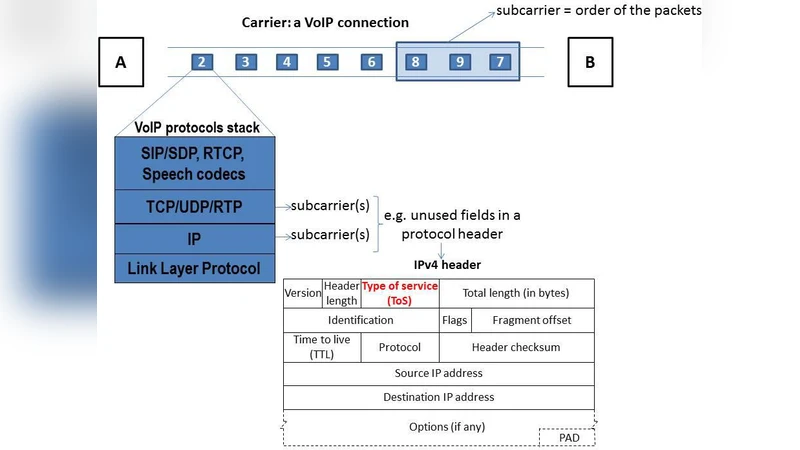
On Importance of Steganographic Cost For Network Steganography
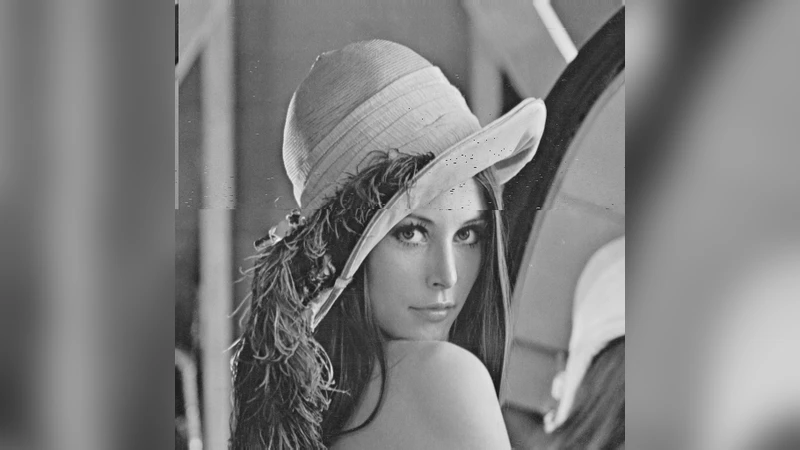
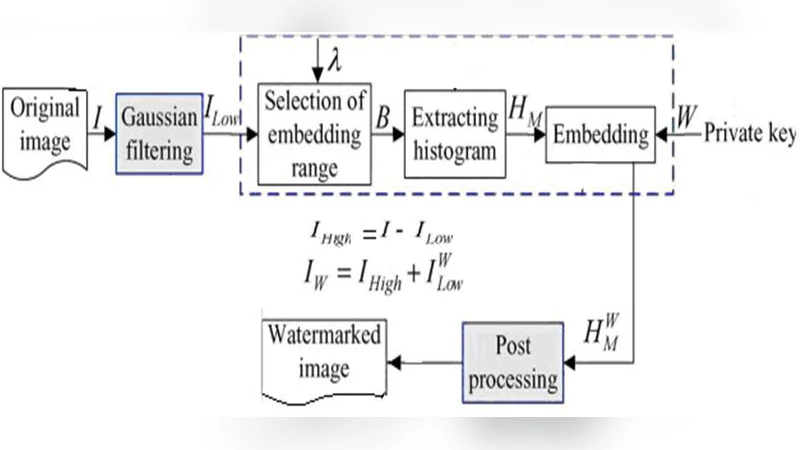
An Approach of Digital Image Copyright Protection by Using Watermarking Technology
Towards the Impossibility of Non-Signalling Privacy Amplification from Time-Like Ordering Constraints

Detecting Spammers via Aggregated Historical Data Set
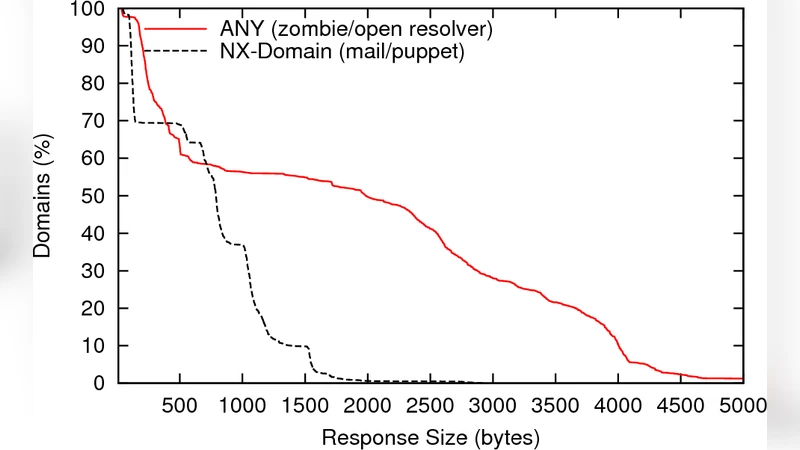
Fragmentation Considered Poisonous
Perfect Secrecy Systems Immune to Spoofing Attacks

On conditions for rho-value is 1 or not of complete family of pairing-friendly elliptic curves
Secrecy Is Cheap if the Adversary Must Reconstruct
Information-Theoretically Secure Three-Party Computation with One Corrupted Party
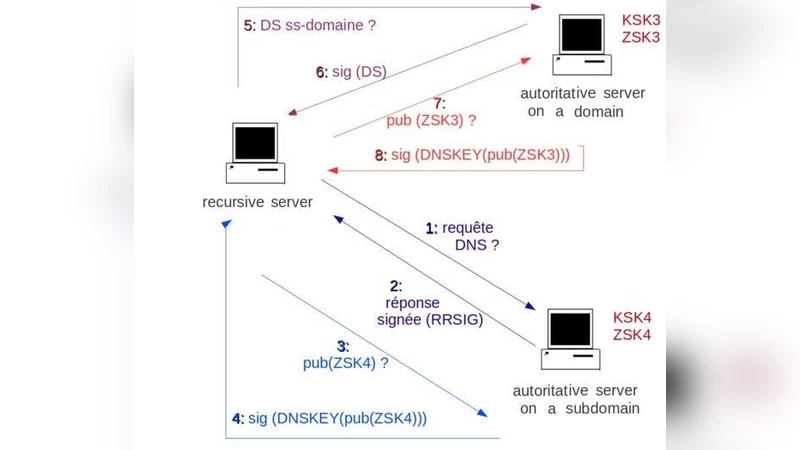
Security of the DNS Protocol - Implementation and Weaknesses Analyses of DNSSEC
Reply to recent scepticism about the foundations of quantum cryptography

Cyber-Insurance in Internet Security: A Dig into the Information Asymmetry Problem

Unconditionally secure device-independent quantum key distribution with only two devices
Non-associative public-key cryptography
Position-Based Quantum Cryptography and the Garden-Hose Game

Nexus Authorization Logic (NAL): Logical Results
Automated Verification of Quantum Protocols using MCMAS
SybilControl: Practical Sybil Defense with Computational Puzzles

Detection techniques of selective forwarding attacks in wireless sensor networks: a survey