Cs-Cr
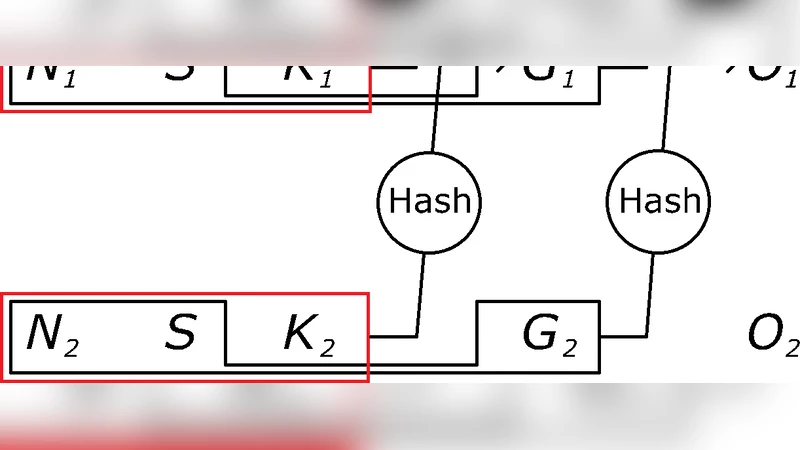
Hasq Hash Chains
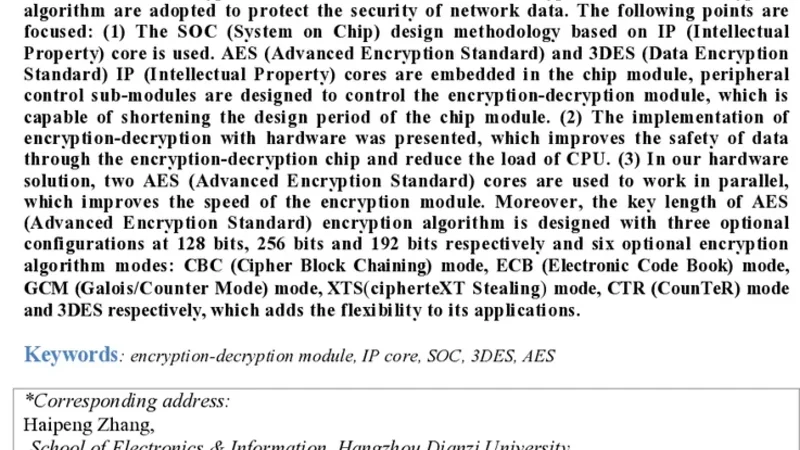
Design of an Encryption-Decryption Module Oriented for Internet Information Security SOC Design
Reaction to New Security Threat Class
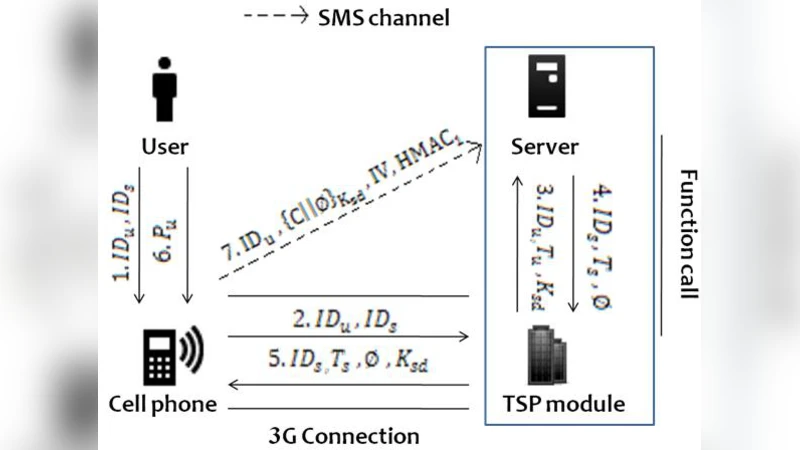
Authentication Mechanism for Resistance to Password Stealing and Reuse Attack

An Application Package Configuration Approach to Mitigating Android SSL Vulnerabilities
A Study Of Cyber Security Challenges And Its Emerging Trends On Latest Technologies
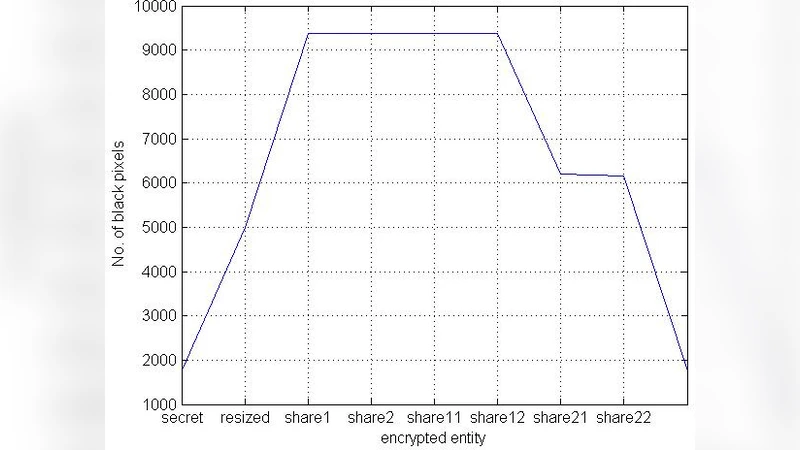
Design and Implementation of Hierarchical Visual cryptography with Expansion less Shares
Proactive Web Server Protocol for Complaint Assessment
Secure and Image Retrieval based on Multipurpose Watermarking for Mammography Images Database
Analysis of Attacks on Hybrid DWT-DCT Algorithm for Digital Image Watermarking With MATLAB
Security Threats in MANETS : A Review
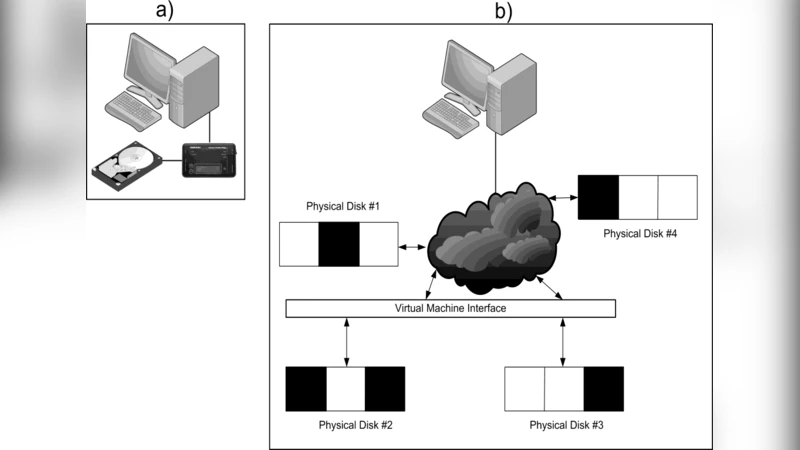
Calm Before the Storm: The Challenges of Cloud Computing in Digital Forensics
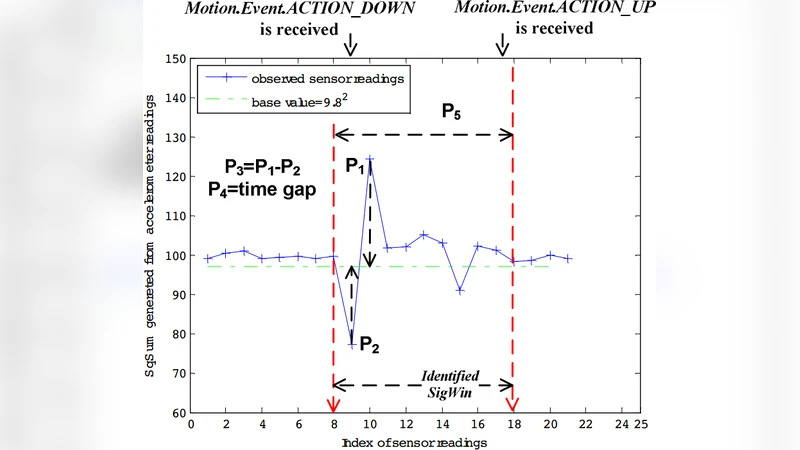
Two Novel Defenses against Motion-Based Keystroke Inference Attacks
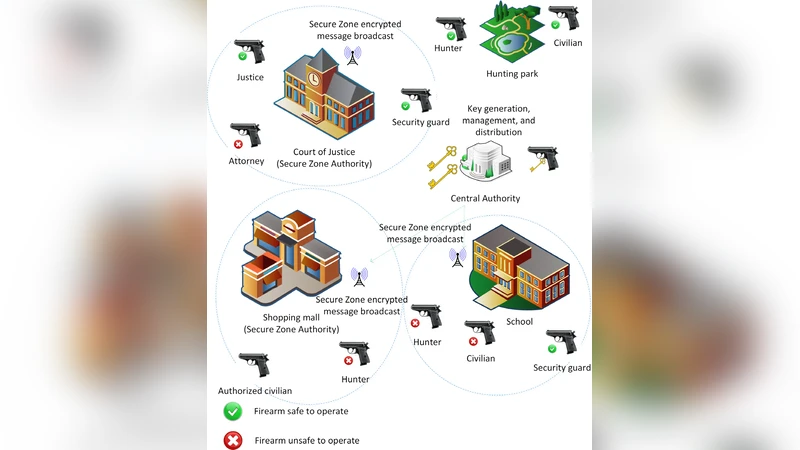
Wireless-Delimited Secure Zones with Encrypted Attribute-Based Broadcast for Safe Firearms
A Robust Biometric-Based Three-factor Remote User Authentication Scheme
A New Non-MDS Hash Function Resisting Birthday Attack and Meet-in-the-middle Attack

Nano-artifact metrics based on random collapse of resist

Secure Debit Card Device Model
A Fast Compressive Sensing Based Digital Image Encryption Technique using Structurally Random Matrices and Arnold Transform

Attack on Fully Homomorphic Encryption over the Integers

A New Type of Cipher

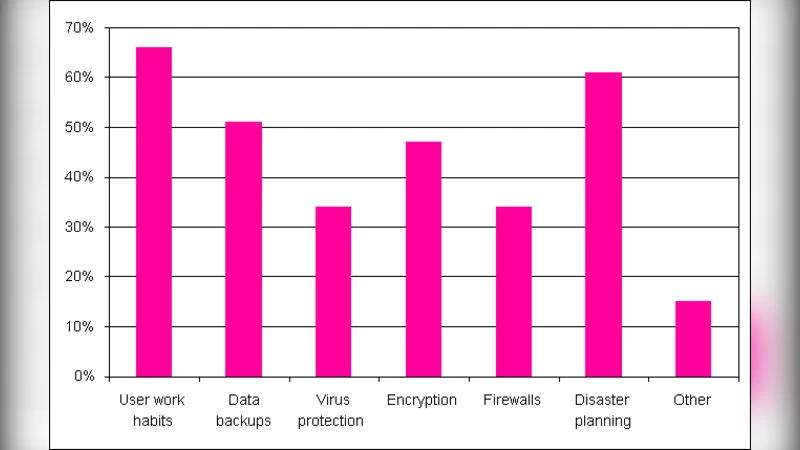
Take it or Leave it: Running a Survey when Privacy Comes at a Cost