Cs-Cr

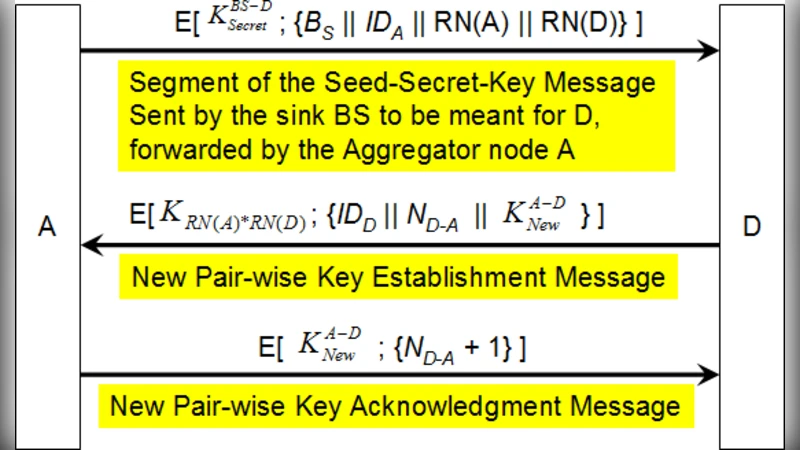
A Pair-wise Key Distribution Mechanism and Distributed Trust Evaluation Model for Secure Data Aggregation in Mobile Sensor Networks
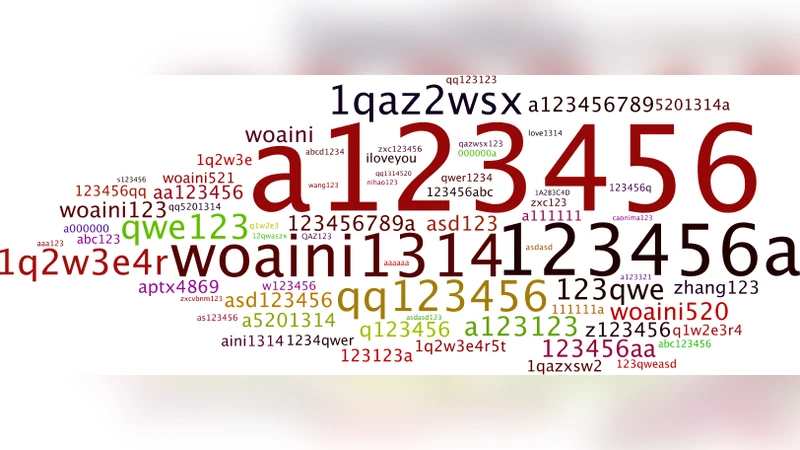
The Scale-free Network of Passwords : Visualization and Estimation of Empirical Passwords
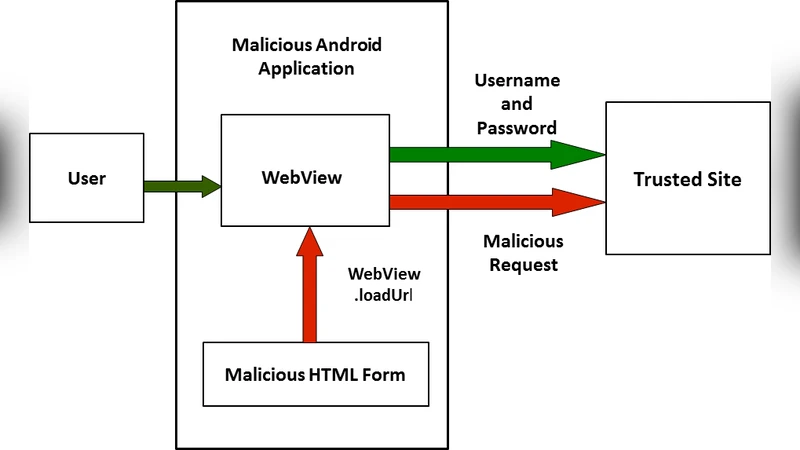
Cross Site Request Forgery on Android WebView

Analysis of Applicability of ISO 9564 PIN based Authentication to Closed-Loop Mobile Payment Systems
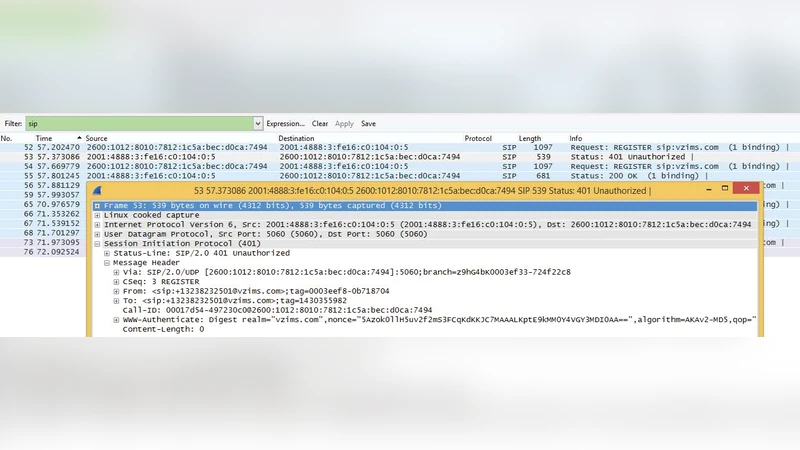
New Threats to SMS-Assisted Mobile Internet Services from 4G LTE: Lessons Learnt from Distributed Mobile-Initiated Attacks towards Facebook and Other Services
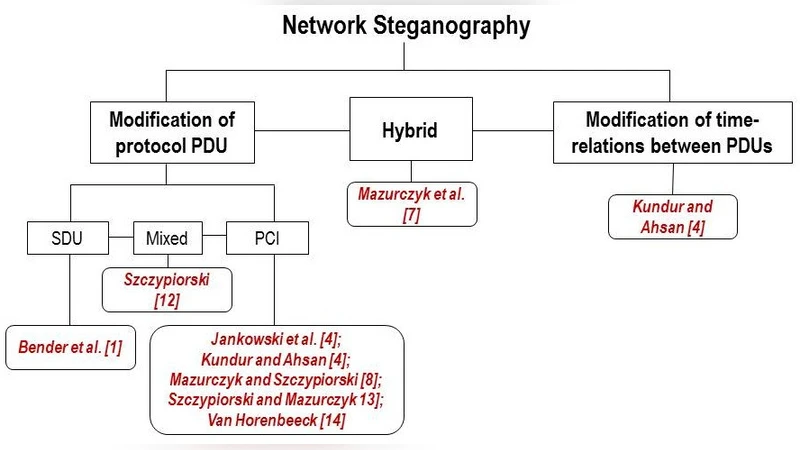
Principles and Overview of Network Steganography
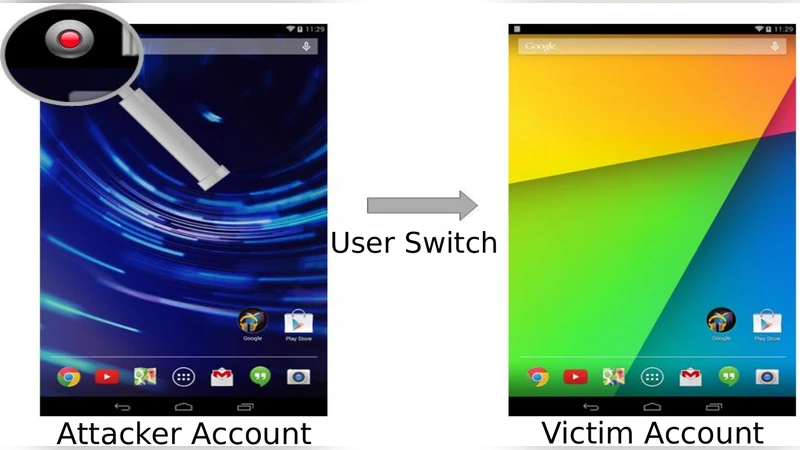
A Systematic Security Evaluation of Androids Multi-User Framework

Review of Considerations for Mobile Device based Secure Access to Financial Services and Risk Handling Strategy for CIOs, CISOs and CTOs
Identifying User Behavior from Residual Data in Cloud-based Synchronized Apps
IP Tracing and Active Network Response
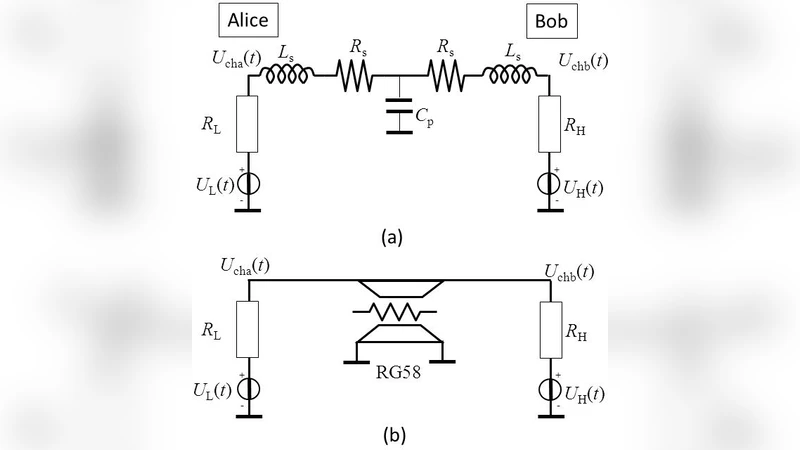
Cable Capacitance Attack against the KLJN Secure Key Exchange
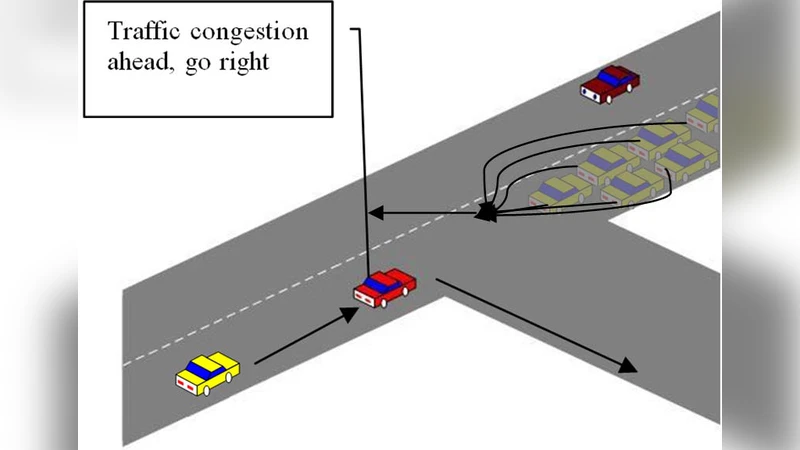
Security Analysis of Vehicular Ad Hoc Networks (VANET)
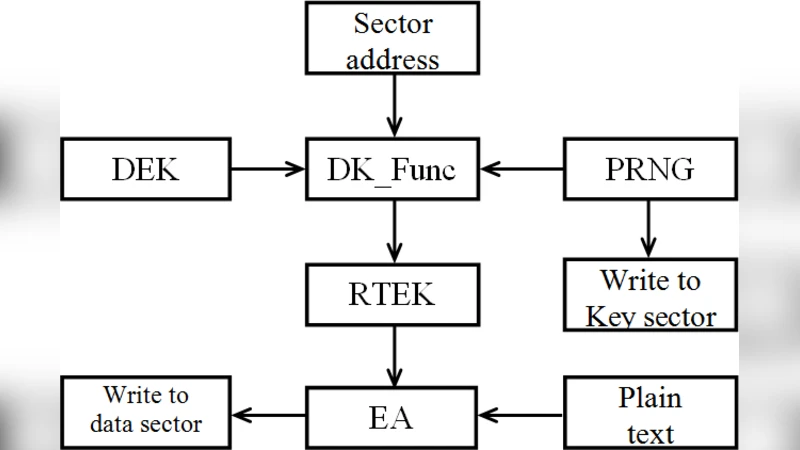
SDMS-based Disk Encryption Method
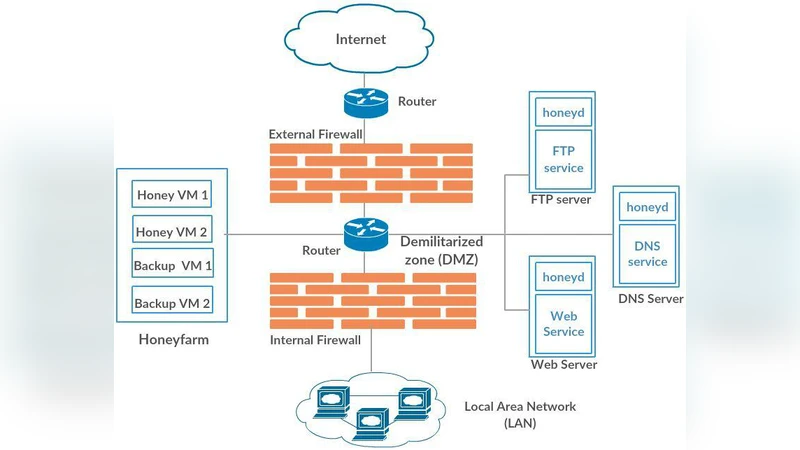
HoneyMesh: Preventing Distributed Denial of Service Attacks using Virtualized Honeypots
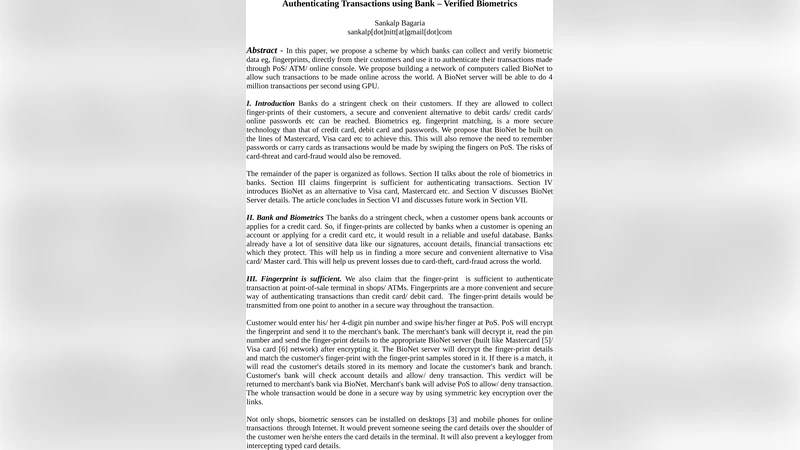
Authenticating Transactions using Bank-Verified Biometrics

The Discrete Logarithm Problem in Bergmans non-representable ring

An ideal multi-secret sharing scheme based on minimal privileged coalitions

Limits of privacy amplification against non-signalling memory attacks

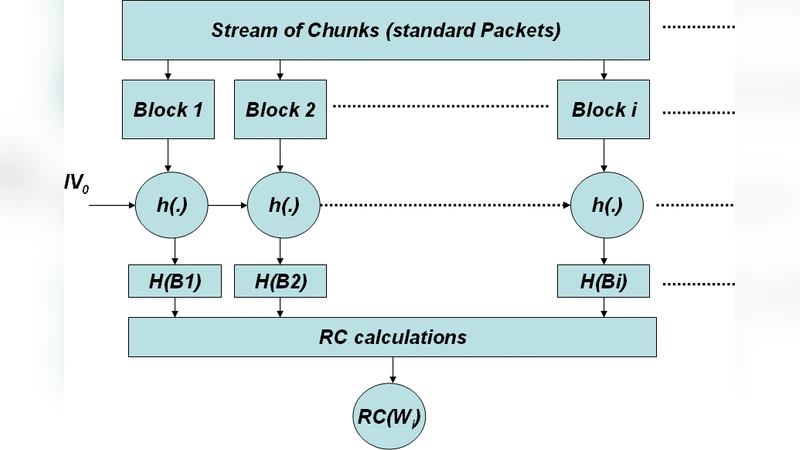
I Have the Proof: Providing Proofs of Past Data Possession in Cloud Forensics
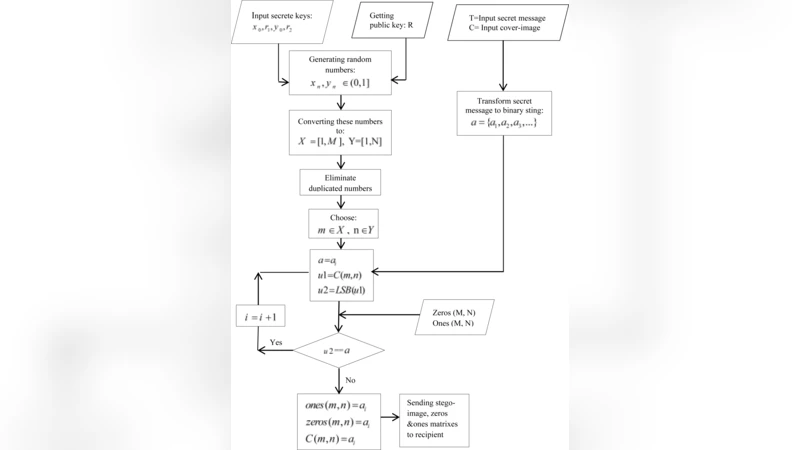
Public key Steganography Using Discrete Cross-Coupled Chaotic Maps

Impacts of Bad Data on the PMU based Line Outage Detection

Letter counting: a stem cell for Cryptology, Quantitative Linguistics, and Statistics