Cs-Cr
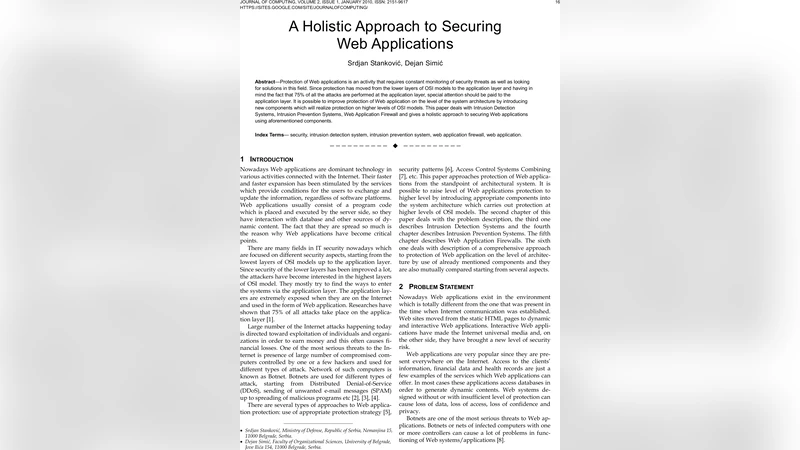
A Holistic Approach to Securing Web Applications

Secret Key Establishment over a Pair of Independent Broadcast Channels
Hiding Data in OFDM Symbols of IEEE 802.11 Networks

Matroids and Quantum Secret Sharing Schemes

Healthcare IT: Is your Information at Risk?
Analysis of Phishing Attacks and Countermeasures
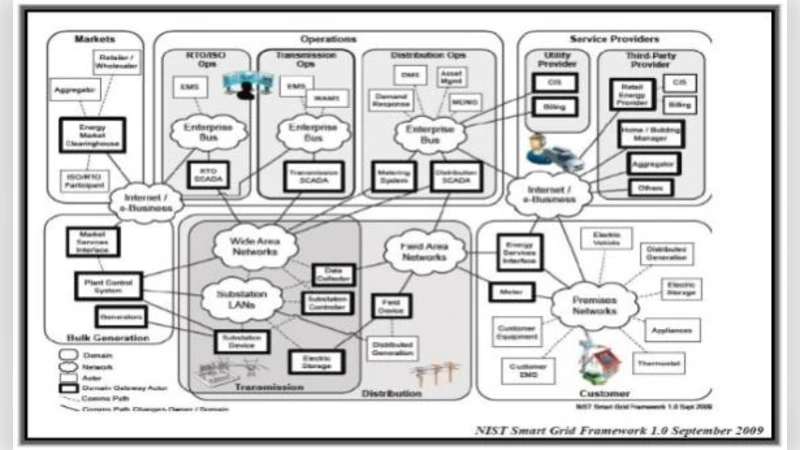
A Security Plan for Smart Grid Systems Based On AGC4ISR
A Cryptographic Scheme Of Mellin Transform
An Experimental Study of Cryptography Capability using Chained Key Exchange Scheme for Embedded Devices
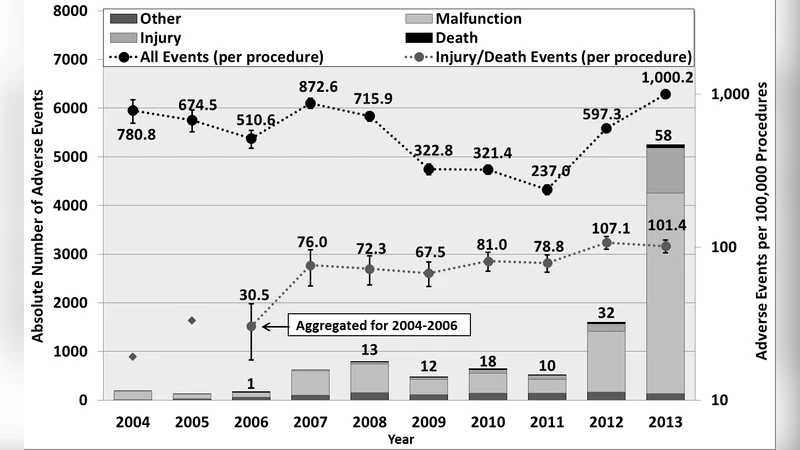
Adverse Events in Robotic Surgery: A Retrospective Study of 14 Years of FDA Data

Security Threats Analysis in Bluetooth-Enabled Mobile Devices
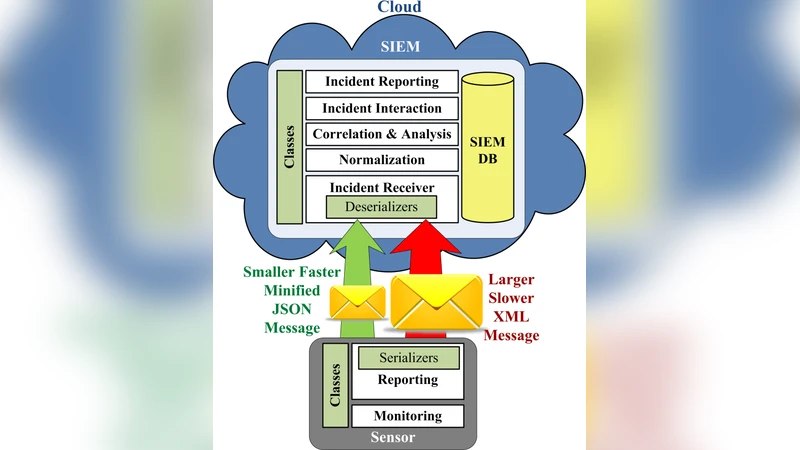
XML Schema-based Minification for Communication of Security Information and Event Management (SIEM) Systems in Cloud Environments
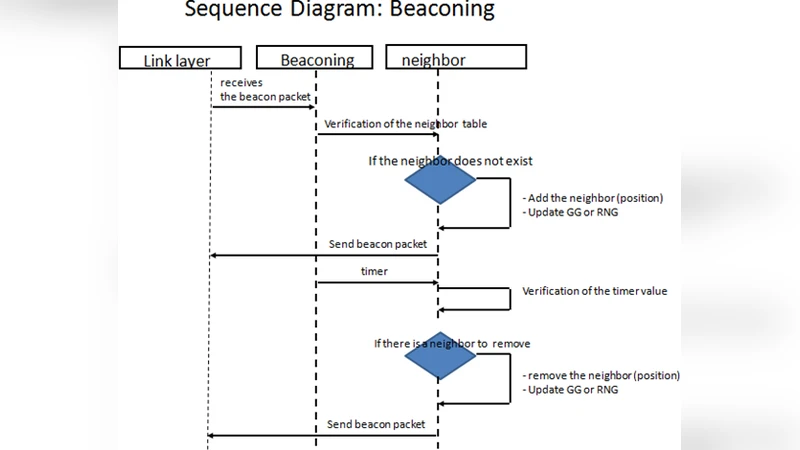
A beaconing approach whith key exchange in vehicular ad hoc networks

Application Security framework for Mobile App Development in Enterprise setup

Homomorphic Payment Addresses and the Pay-to-Contract Protocol
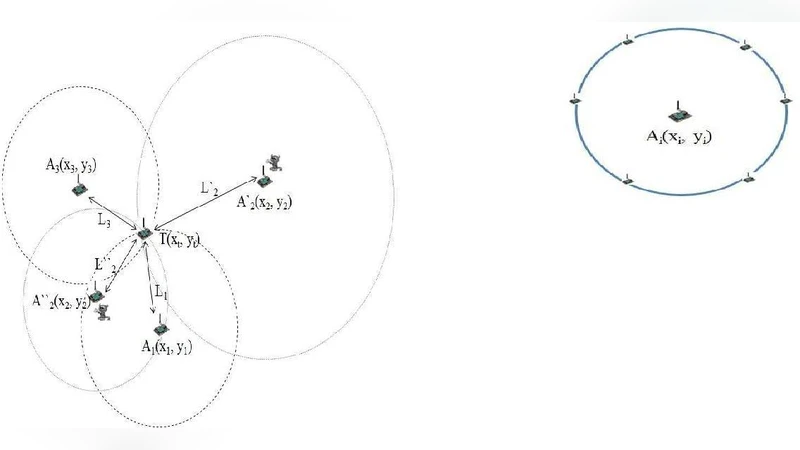
Identifying Cheating Anchor Nodes using Maximum Likelihood and Mahalanobis Distance
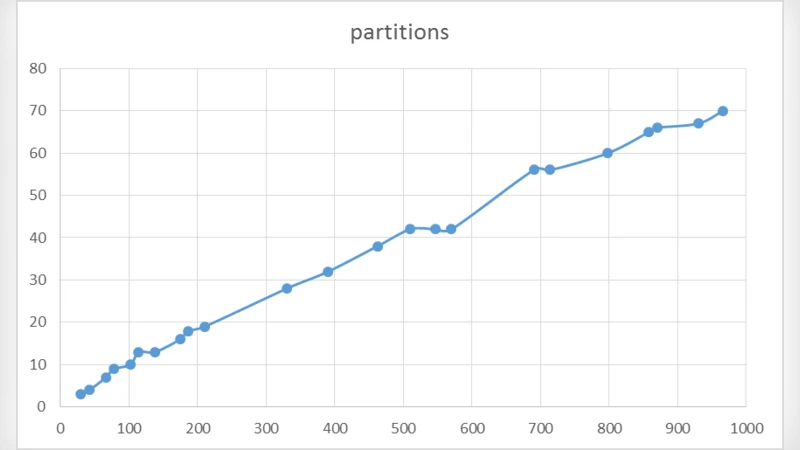
Generating Primes Using Partitions
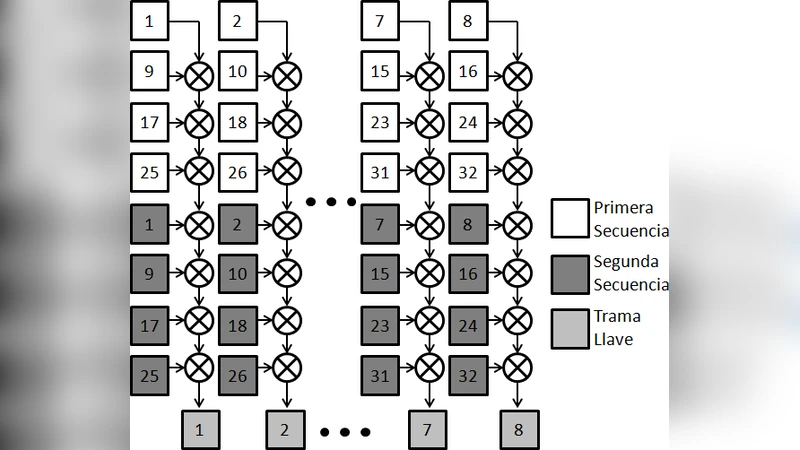
Implementation of a Stream Cipher Based on Bernoullis Map
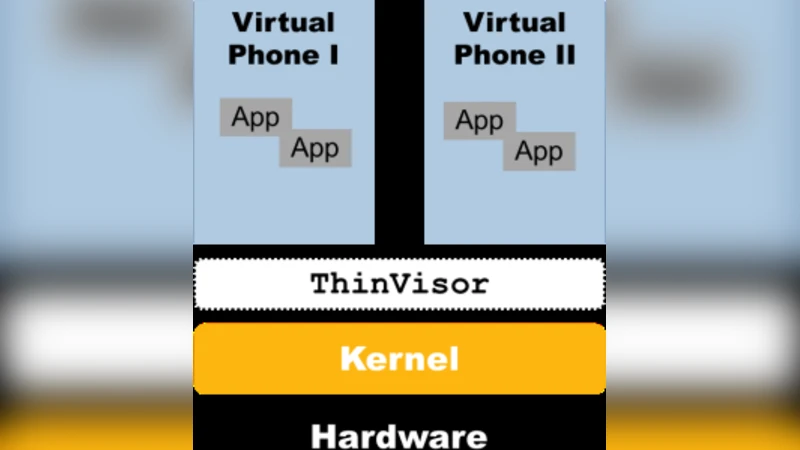
Evaluation of Security Solutions for Android Systems

Instantly Obsoleting the Address-code Associations: A New Principle for Defending Advanced Code Reuse Attack
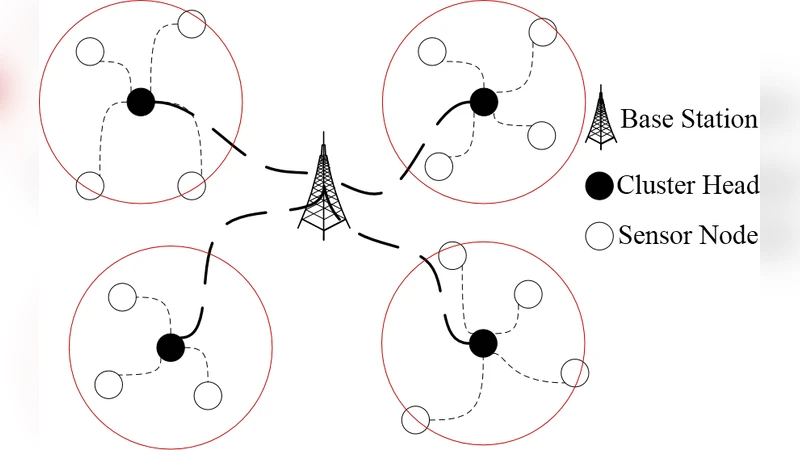
A Hierarchical Key Management Scheme for Wireless Sensor Networks Based on Identity-based Encryption
"The Good, The Bad And The Ugly": Evaluation of Wi-Fi Steganography