Cs-Cr

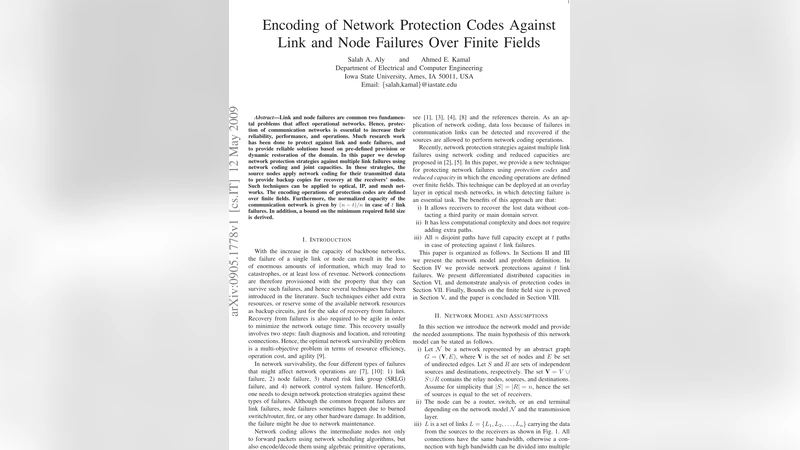
Encoding of Network Protection Codes Against Link and Node Failures Over Finite Fields
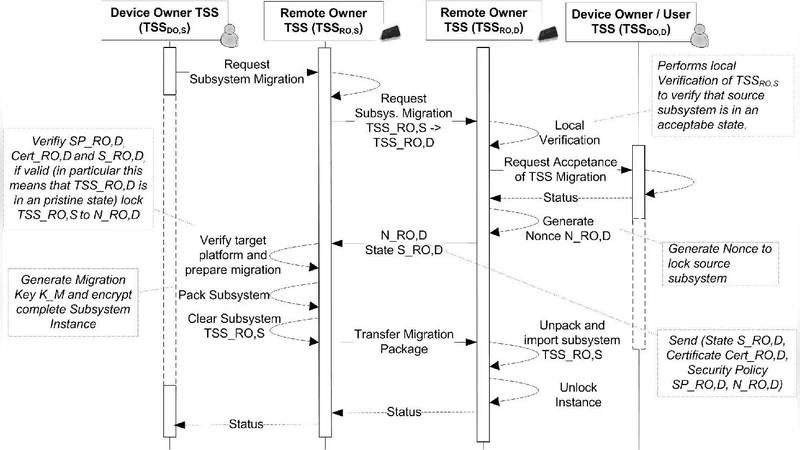
On the deployment of Mobile Trusted Modules
Software Security Rules, SDLC Perspective

Efficient FPGA-based multipliers for F_{3^97} and F_{3^{6*97}}

GossiCrypt: Wireless Sensor Network Data Confidentiality Against Parasitic Adversaries

Direct and Reverse Secret-Key Capacities of a Quantum Channel

INDECT Advanced Security Requirements

Optimal Iris Fuzzy Sketches
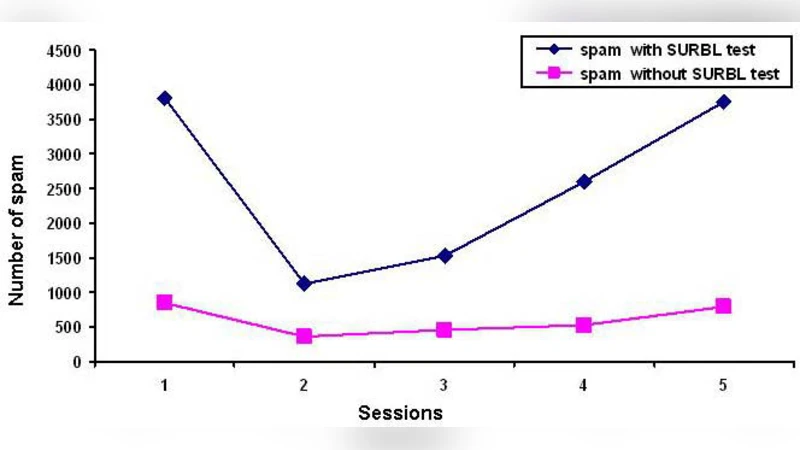
Multi Layer Approach to Defend DDoS Attacks Caused by Spam

General Hardness Amplification of Predicates and Puzzles
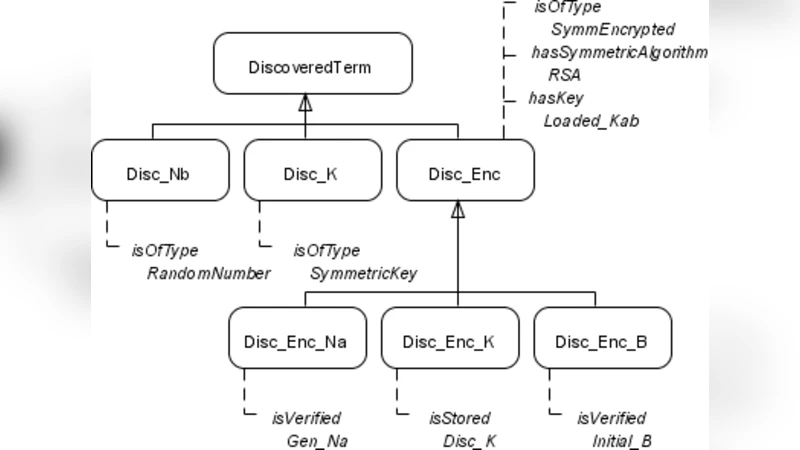
A Modeling Framework for Generating Security Protocol Specifications

Safer in the Clouds (Extended Abstract)

Cryptanalysis of group-based key agreement protocols using subgroup distance functions
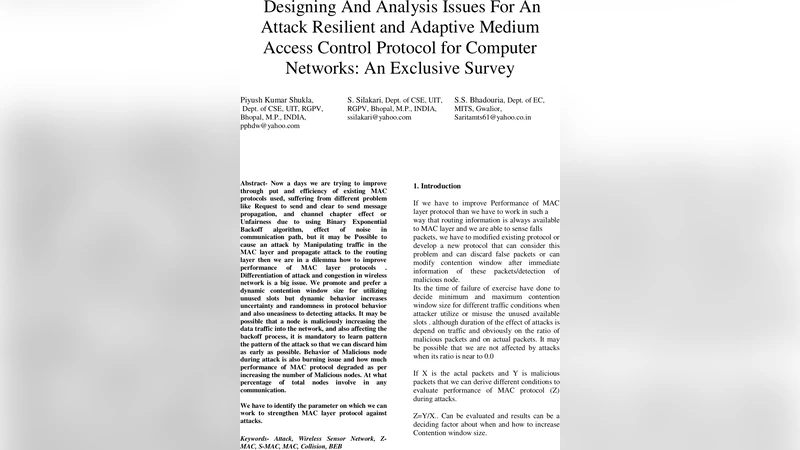
Design and Analysis of an Attack Resilient and Adaptive Medium access Control Protocol for Computer Networks
Emoji-Based Jailbreaking of Large Language Models
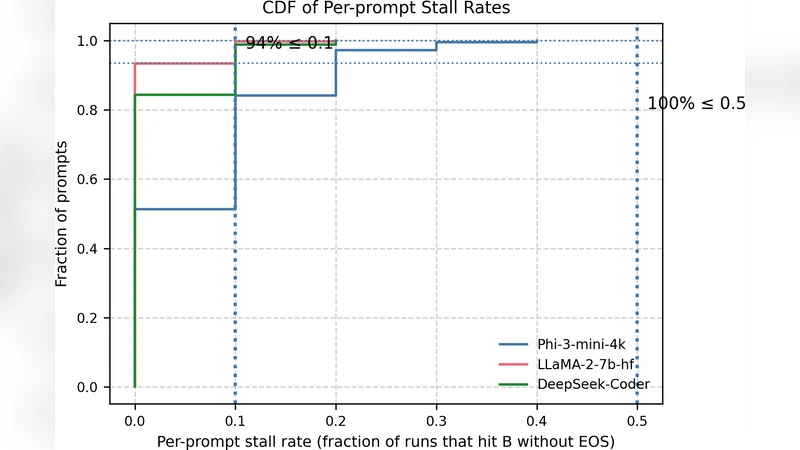
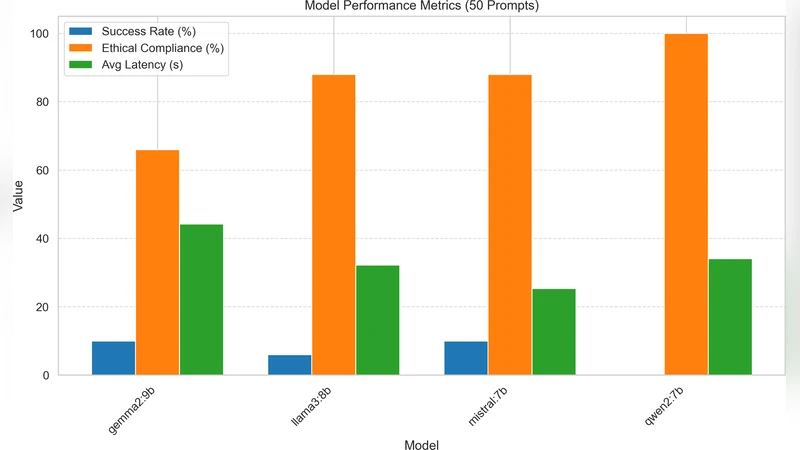
Prompt-Induced Over-Generation as Denial-of-Service: A Black-Box Attack-Side Benchmark
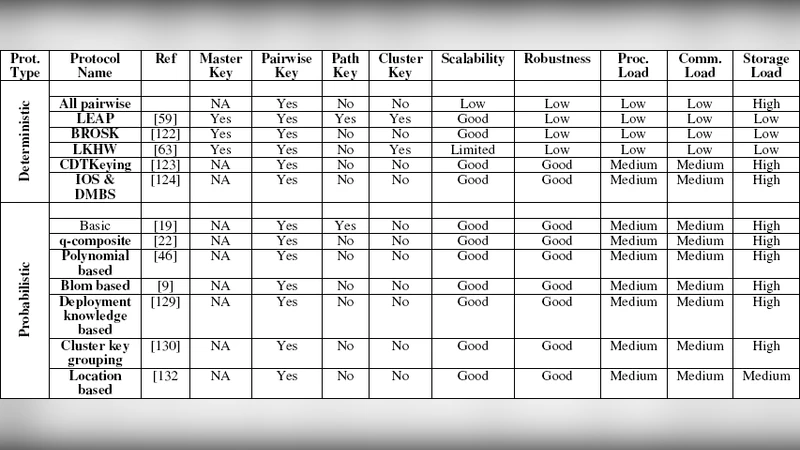
A Survey on Wireless Sensor Network Security
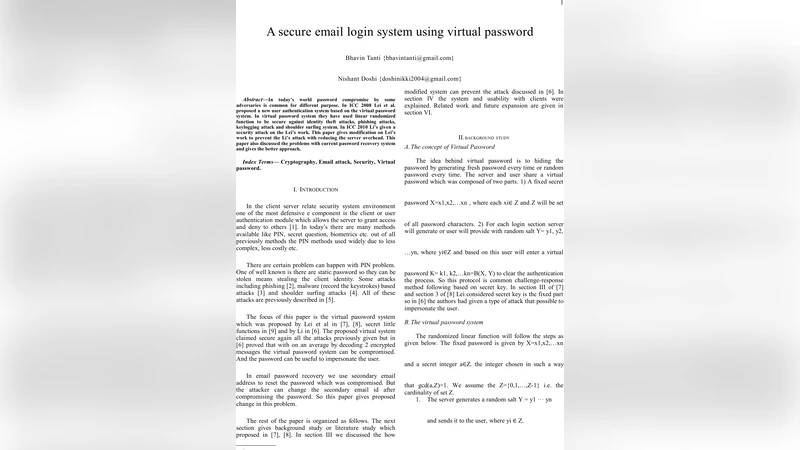
A secure email login system using virtual password
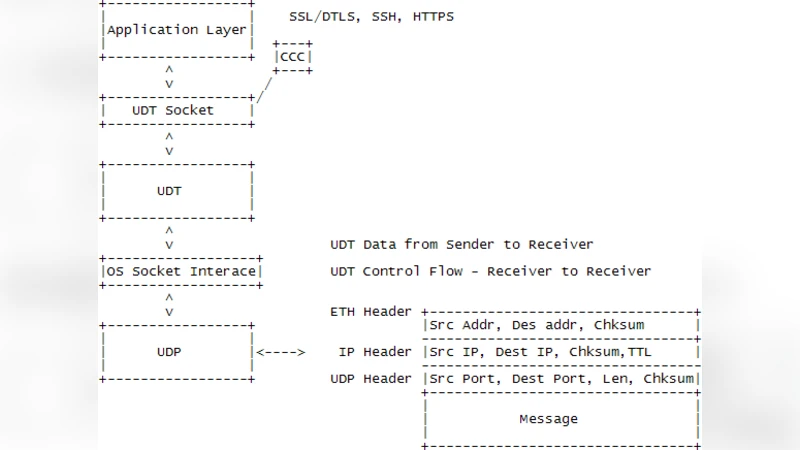
Securing data transfer in the cloud through introducing identification packet and UDT-authentication option field: a characterization
Anti-Collusion Digital Fingerprinting Codes via Partially Cover-Free Families

Reducing Protocol Analysis with XOR to the XOR-free Case in the Horn Theory Based Approach
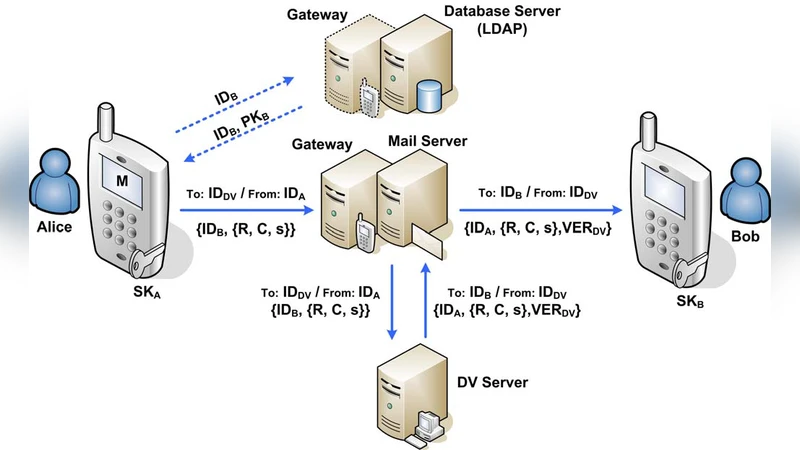
SMEmail - A New Protocol for the Secure E-mail in Mobile Environments