Cs-Cr
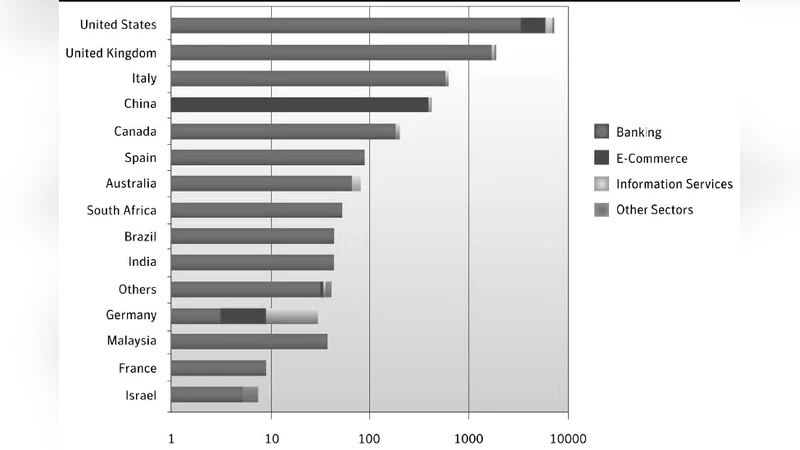
Case Study On Social Engineering Techniques for Persuasion
Aryabhatas Mathematics

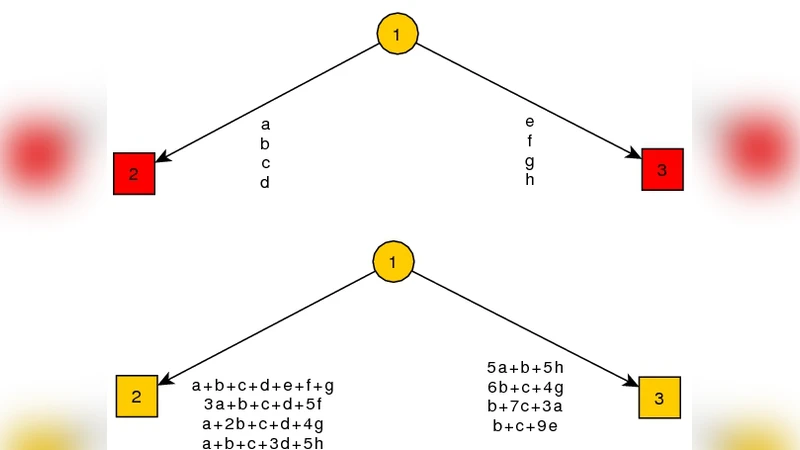
Common Representation of Information Flows for Dynamic Coalitions
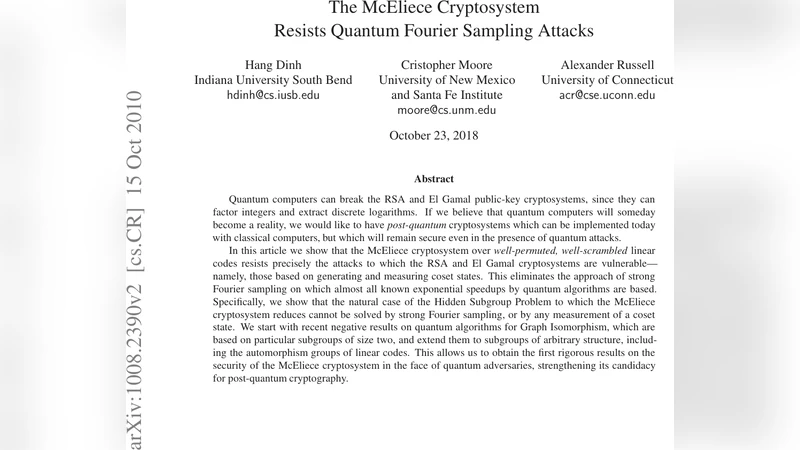
The McEliece Cryptosystem Resists Quantum Fourier Sampling Attacks
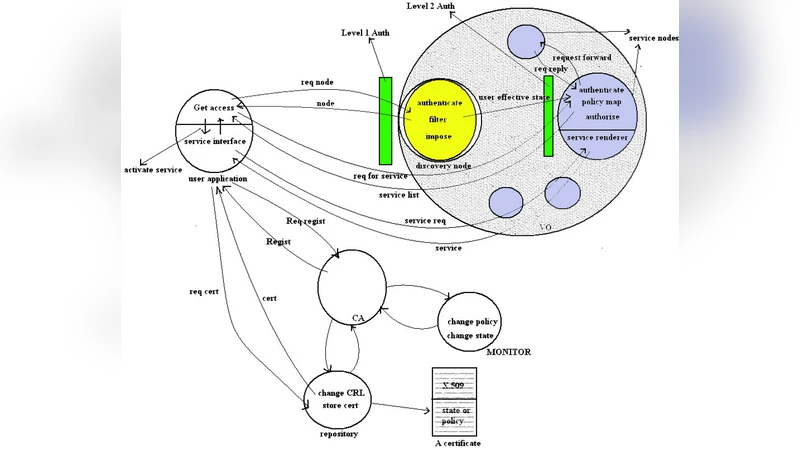
Certification Authority Monitored Multilevel and Stateful Policy Based Authorization in Services Oriented Grids
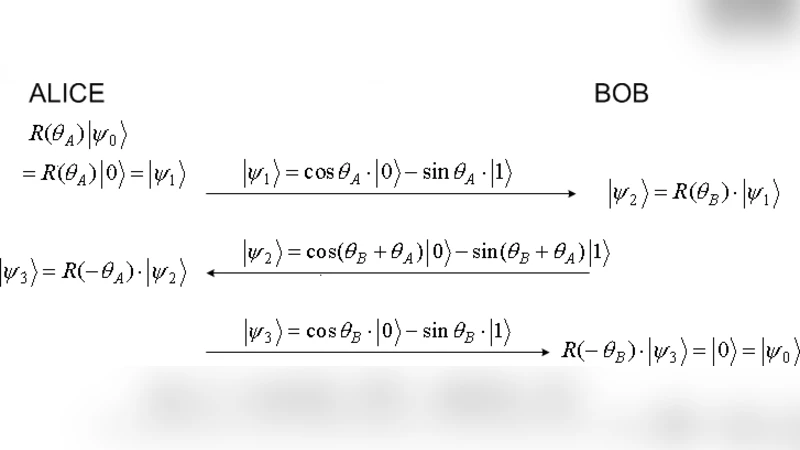
Quantum Three-Pass protocol: Key distribution using quantum superposition states
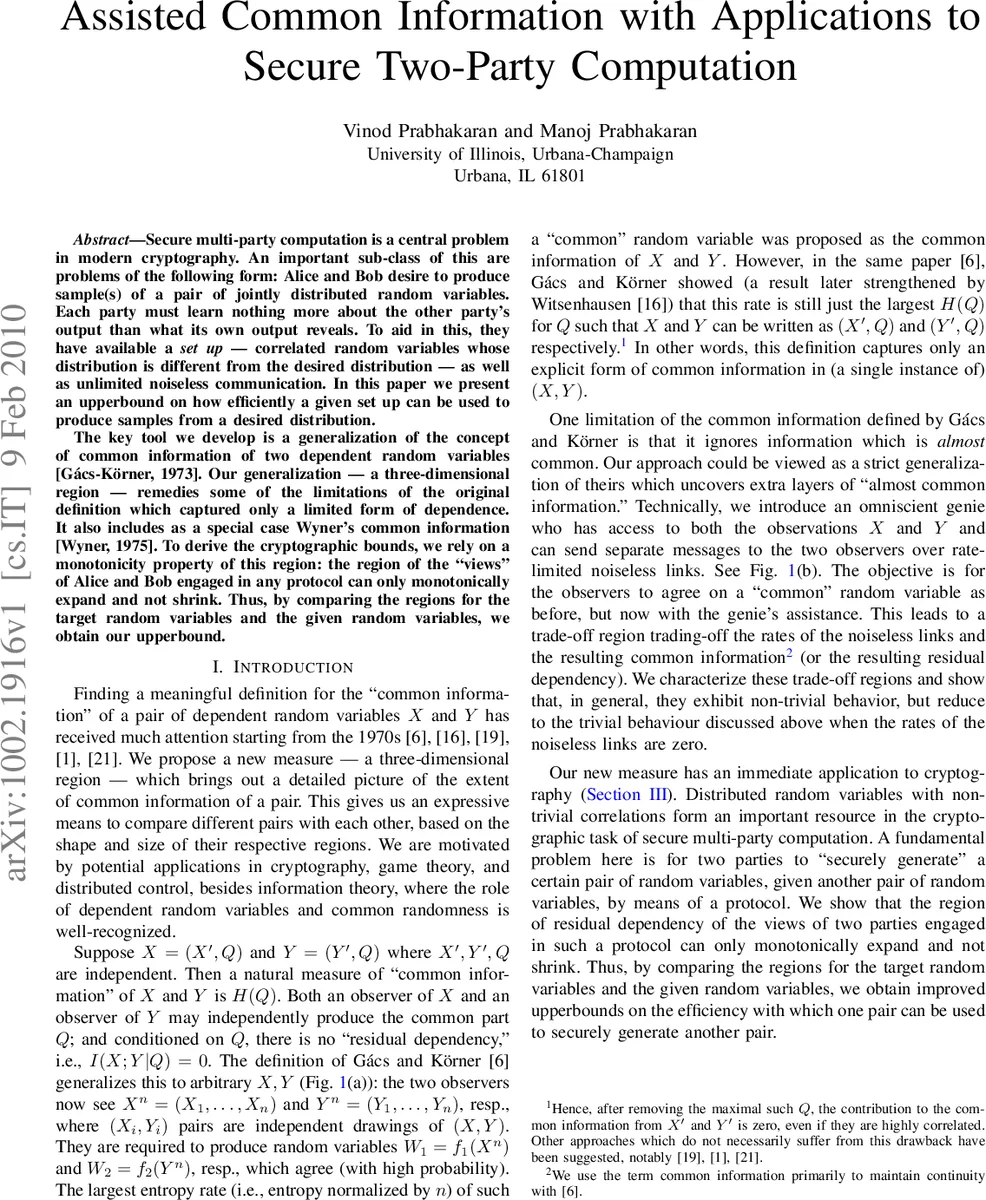
Assisted Common Information with Applications to Secure Two-Party Computation
Intrusions into Privacy in Video Chat Environments: Attacks and Countermeasures

Little Dragon Two: An efficient Multivariate Public Key Cryptosystem

Network Coding-Based Protection Strategy Against Node Failures
HF-hash : Hash Functions Using Restricted HFE Challenge-1

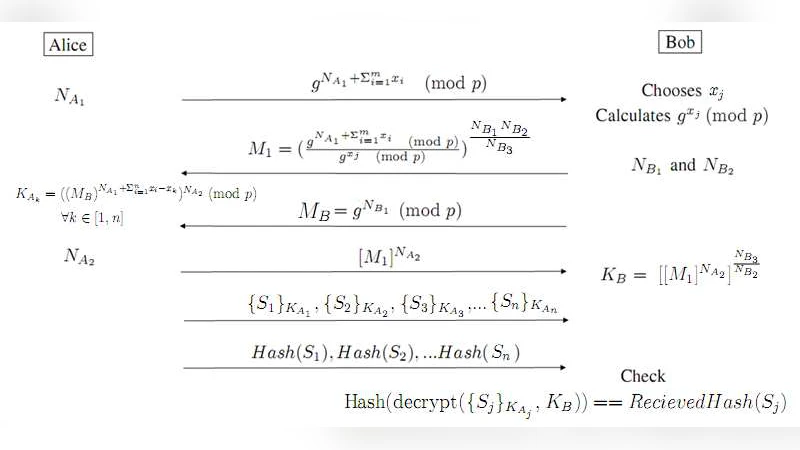
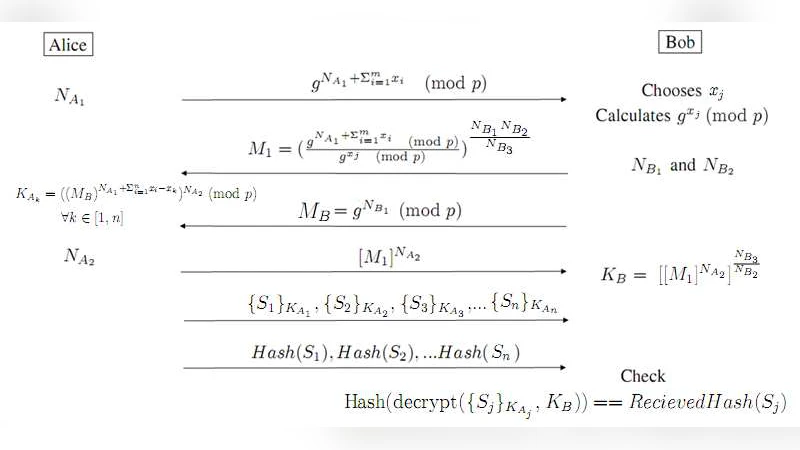
A Novel Scheme for Secured Data Transfer Over Computer Networks
MIMO-Assisted Channel-Based Authentication in Wireless Networks
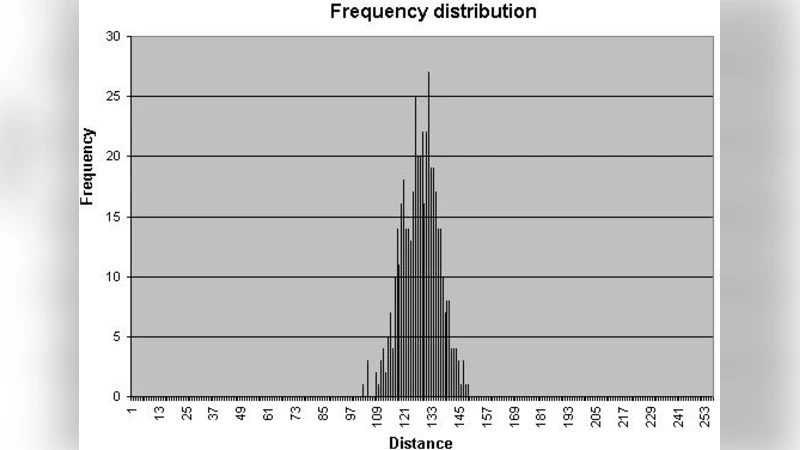
Double Sided Watermark Embedding and Detection with Perceptual Analysis
Composable Security in the Bounded-Quantum-Storage Model

Bounds on the degree of APN polynomials The Case of $x^{-1}+g(x)$
Course Material Selection Rubric for Creating Network Security Courses

Efficient Steganography with Provable Security Guarantees
SECOQC Business White Paper
Efficient Authenticated Data Structures for Graph Connectivity and Geometric Search Problems

Secure Two-party Protocols for Point Inclusion Problem
Random Linear Network Coding: A free cipher?
