Cs-Cr

How to Work with Honest but Curious Judges? (Preliminary Report)
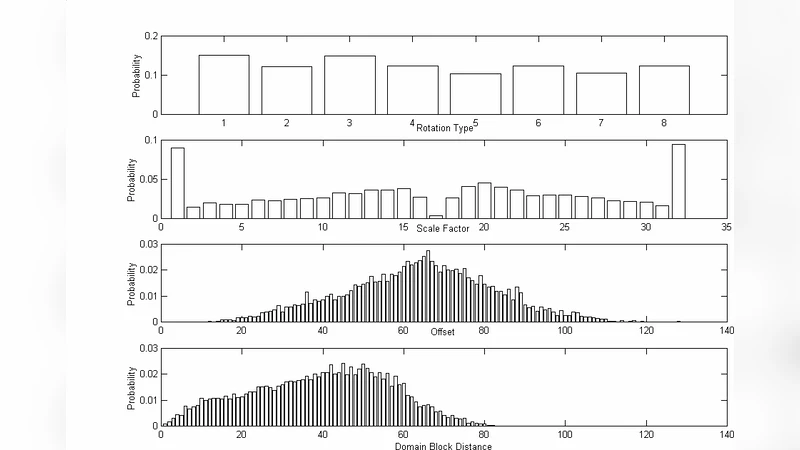
Secure Fractal Image Coding

Robustness of the Digital Image Watermarking Techniques against Brightness and Rotation Attack

Isogenies of Elliptic Curves: A Computational Approach

Review on the Advancements of DNA Cryptography

A novel approach for implementing Steganography with computing power obtained by combining Cuda and Matlab
Security for Wiretap Networks via Rank-Metric Codes
Ftklipse - Design and Implementation of an Extendable Computer Forensics Environment: Specification Design Document

ARQ Secrecy: From Theory to Practice
A Differential Cryptanalysis of Yen-Chen-Wu Multimedia Cryptography System (MCS)
Darknet-Based Inference of Internet Worm Temporal Characteristics

Binary Random Sequences Obtained From Decimal Sequences

Finding matching initial states for equivalent NLFSRs in the fibonacci and the galois configurations
Comments on "Improved Efficient Remote User Authentication Schemes"

GSM Security Using Identity-based Cryptography
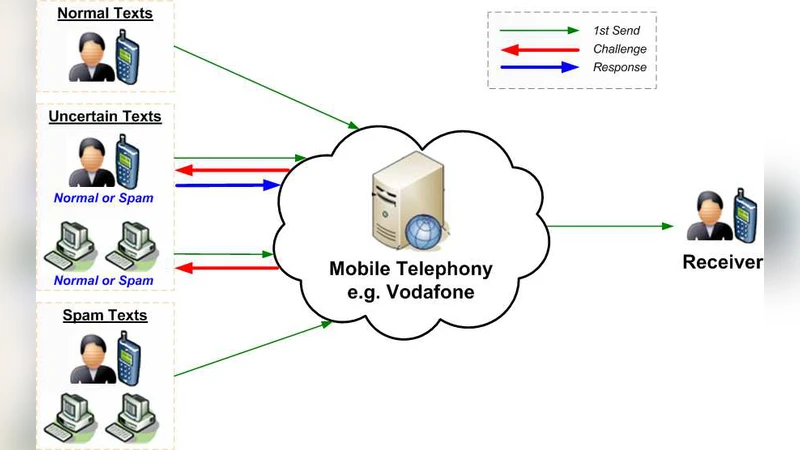
Hybrid Spam Filtering for Mobile Communication

Some A Priori Torah Decryption Principles

A chaos-based approach for information hiding security

Lightweight Security for Network Coding

Privately Releasing Conjunctions and the Statistical Query Barrier

Cryptanalysis of an Image Encryption Scheme Based on a Compound Chaotic Sequence

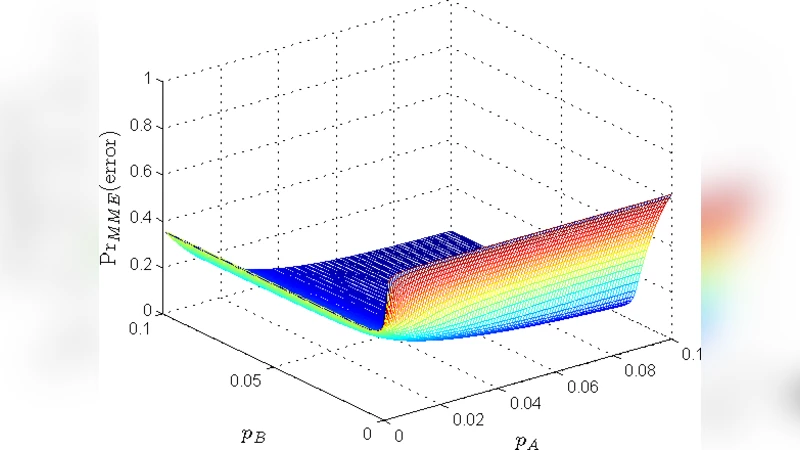
On the Performance of Joint Fingerprint Embedding and Decryption Scheme
