
Cs-Cr


Cryptanalysis of an image encryption scheme based on the Hill cipher

Attribute Weighting with Adaptive NBTree for Reducing False Positives in Intrusion Detection
Secure Nested Codes for Type II Wiretap Channels

Randomness Extraction via Delta-Biased Masking in the Presence of a Quantum Attacker
SEPIA: Security through Private Information Aggregation
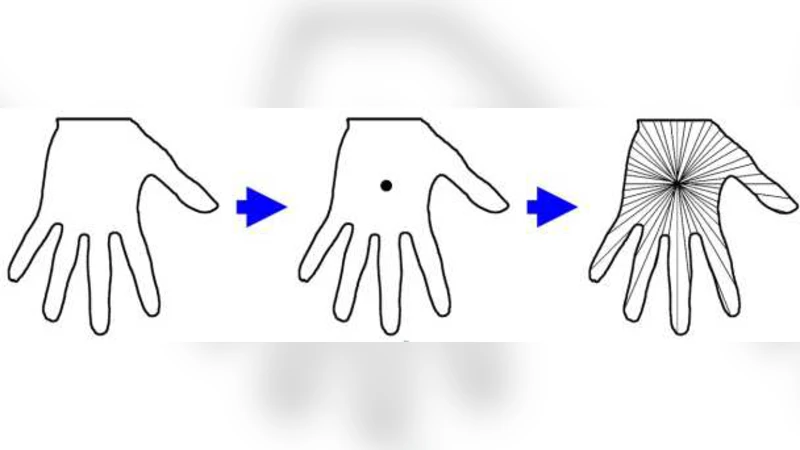
Making Hand Geometry Verification System More Accurate Using Time Series Representation with R-K Band Learning

New Constructions for Query-Efficient Locally Decodable Codes of Subexponential Length
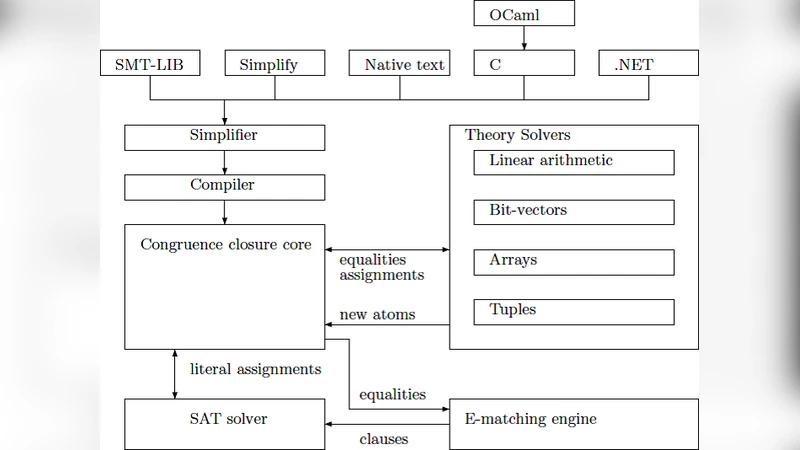
Breaking Mignottes Sequence Based Secret Sharing Scheme Using SMT Solver

Intrusion Detection Using Cost-Sensitive Classification
Classical Knowledge for Quantum Security
Game Theory with Costly Computation
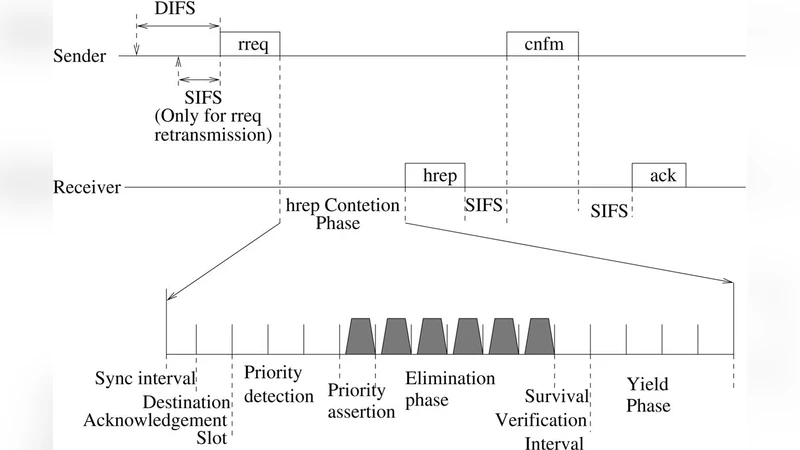
Enhanced Authentication and Locality Aided - Destination Mobility in Dynamic Routing Protocol for MANET
Trident, a new pseudo random number generator based on coupled chaotic maps

Jamming in Fixed-Rate Wireless Systems with Power Constraints - Part II: Parallel Slow Fading Channels

Privacy-Preserving Querying in Sensor Networks

Final Architecture Specification of security, privacy, and incentive mechanisms

Bootstrapped Oblivious Transfer and Secure Two-Party Function Computation

Two-Level Fingerprinting Codes

The Role of Self-Forensics in Vehicle Crash Investigations and Event Reconstruction

Generic Unpacking of Self-modifying, Aggressive, Packed Binary Programs

More on Combinatorial Batch Codes
Proposed platform for improving grid security by trust management system
