Cs-Cr
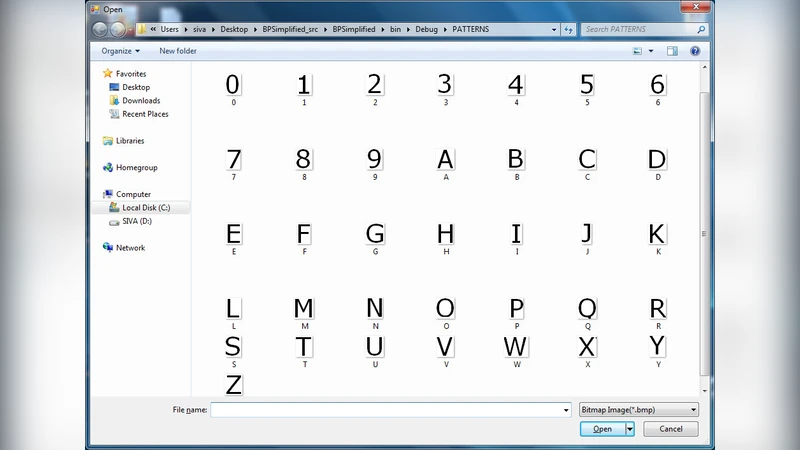
Handwritten Text Image Authentication using Back Propagation
Indices of Power in Optimal IDS Default Configuration: Theory and Examples

Extracting and Verifying Cryptographic Models from C Protocol Code by Symbolic Execution
Privacy-Enhanced Methods for Comparing Compressed DNA Sequences

Attacker Control and Impact for Confidentiality and Integrity
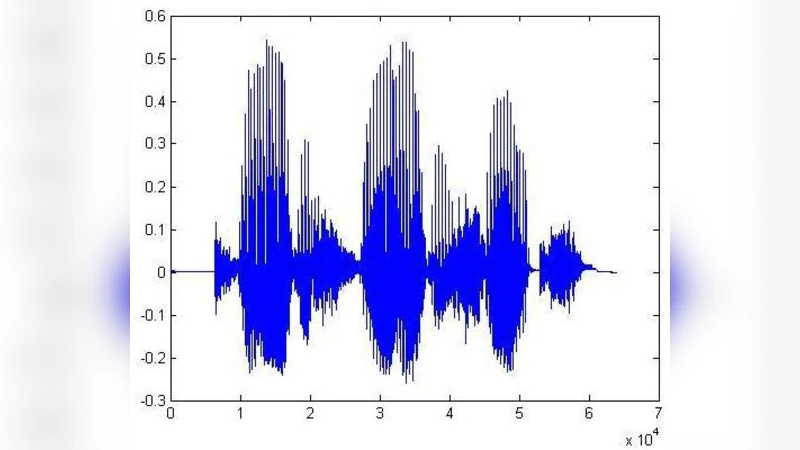
Audio Watermarking with Error Correction
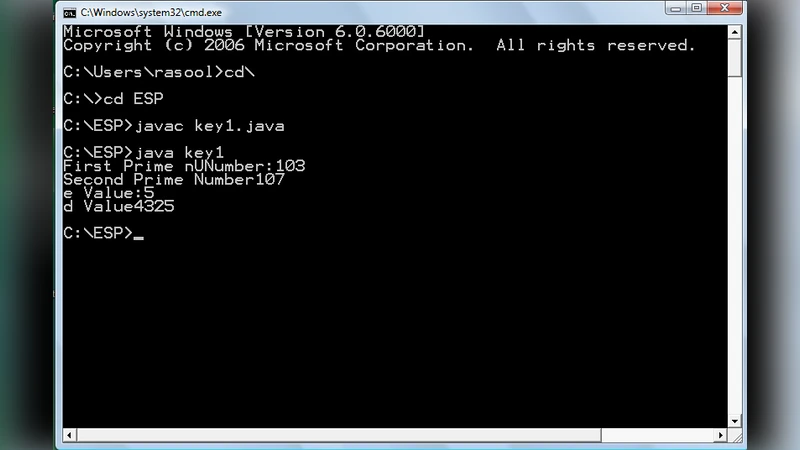
Hilbert Matrix Based Cryptosystem using a Session Key
Prevention of Wormhole Attack in Wireless Sensor Network

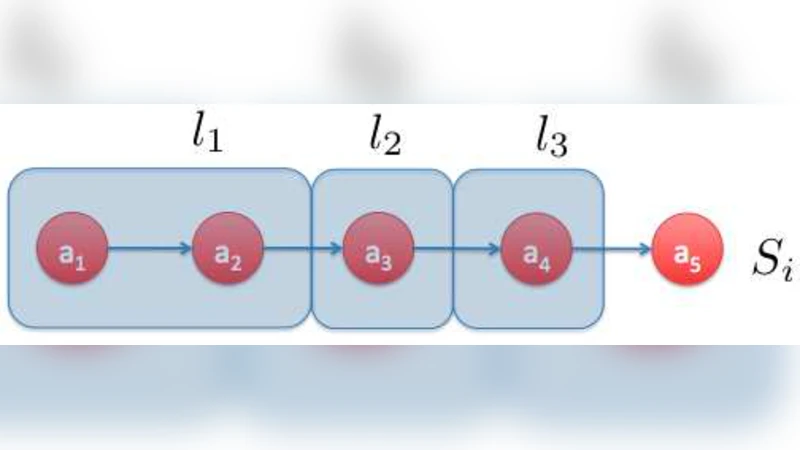
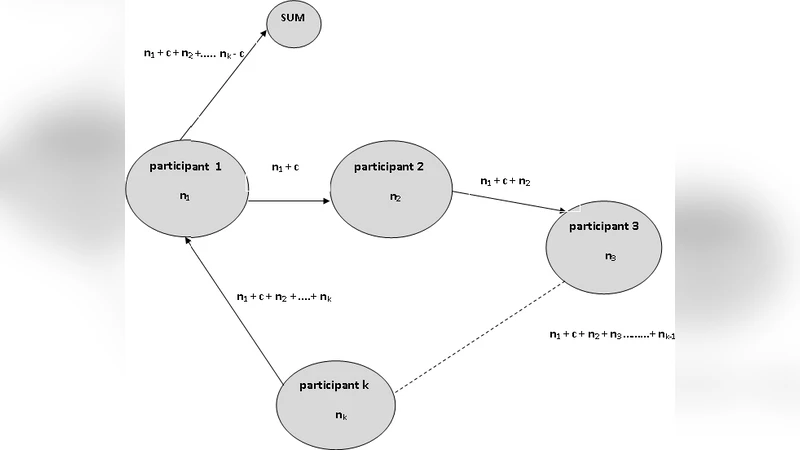
Iterative Constructions and Private Data Release
Secure and Privacy- Aware Searching in Peer-to-Peer Networks
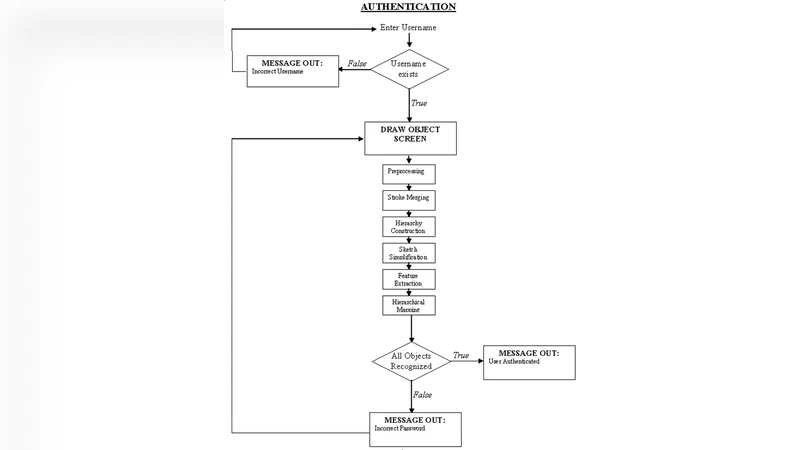
A Graphical Password Based System for Small Mobile Devices
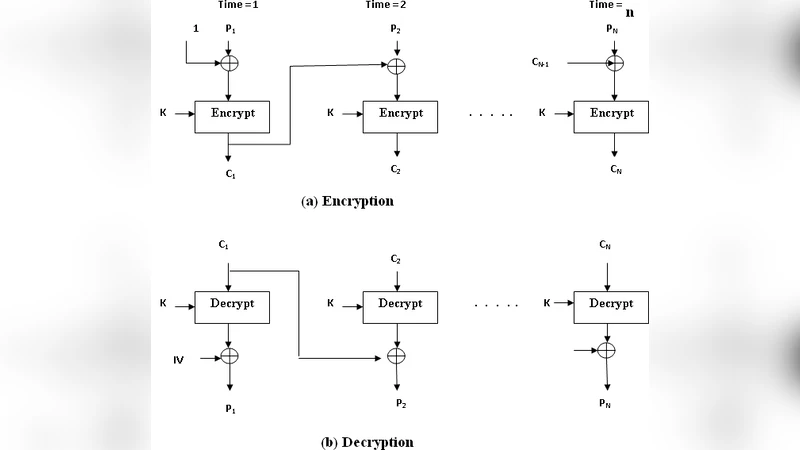
A Cryptosystem Based on Hilbert Matrix using Cipher Block Chaining Mode
Analysis of Differential Phase Shift Quantum Key Distribution
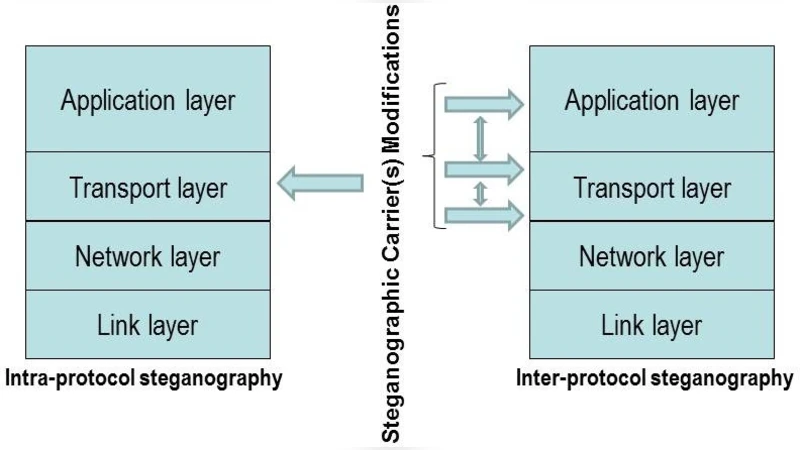
How Hidden Can Be Even More Hidden?
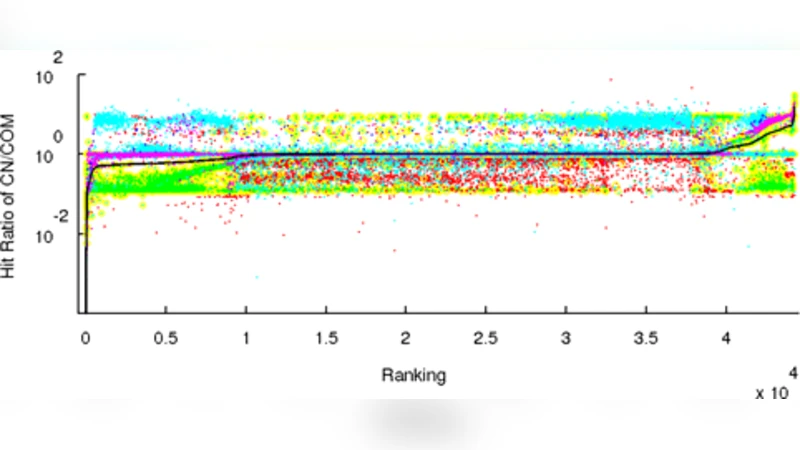
An Analysis of Chinese Search Engine Filtering
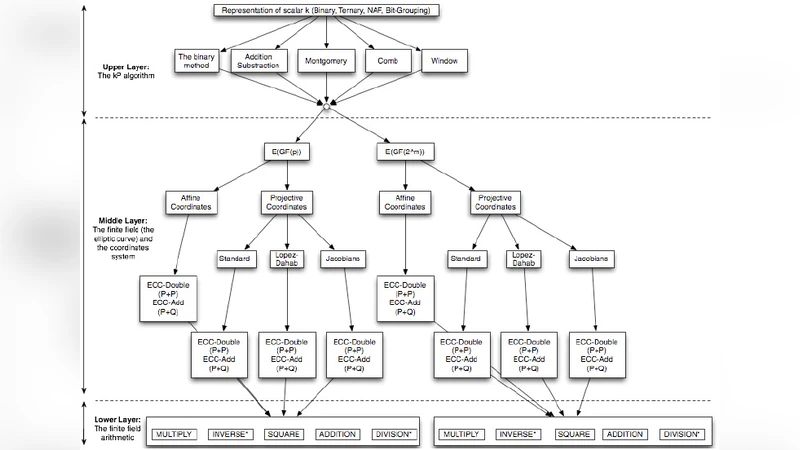
A Review on Elliptic Curve Cryptography for Embedded Systems
Enhanced Secure Algorithm for Message Communion
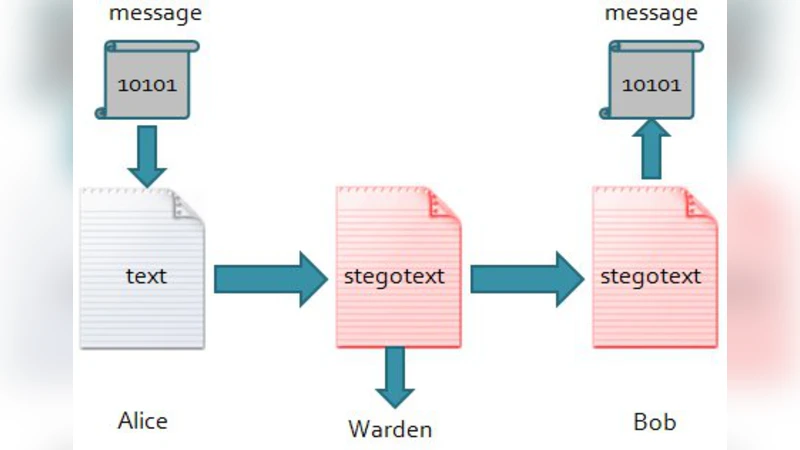
Applying statistical methods to text steganography
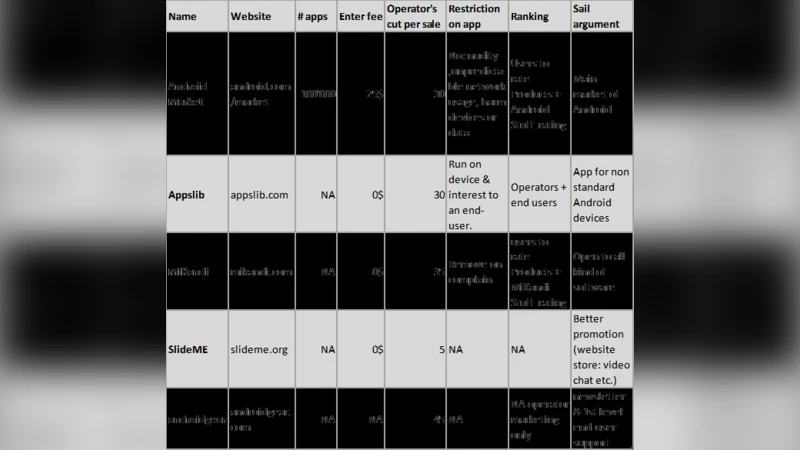
Misbehavior in Mobile Application Markets

Where Have You Been? Secure Location Provenance for Mobile Devices
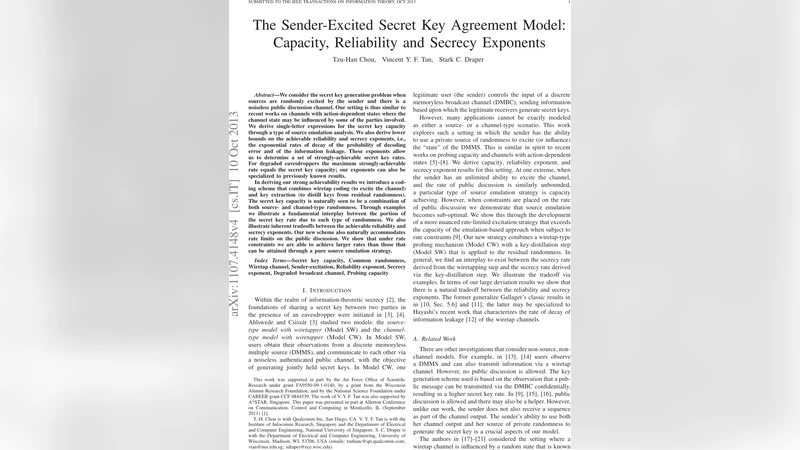
The Sender-Excited Secret Key Agreement Model: Capacity, Reliability and Secrecy Exponents
Oblivious RAM Simulation with Efficient Worst-Case Access Overhead