Cs-Cr

Achieving the Secrecy Capacity of Wiretap Channels Using Polar Codes
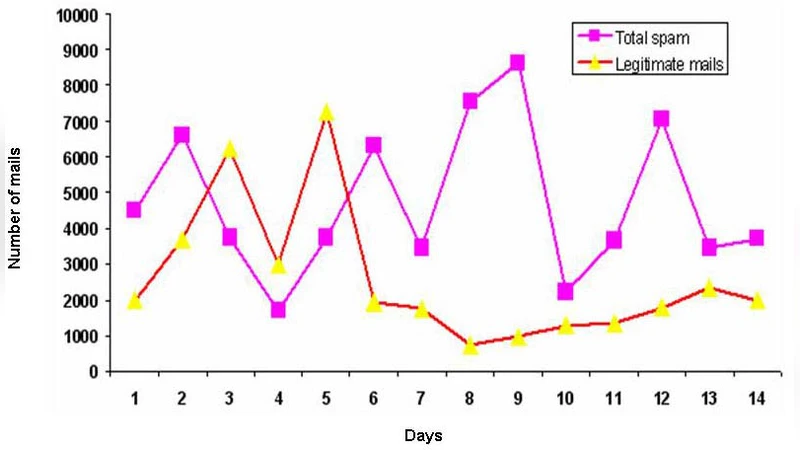
An Empirical Study of Spam and Spam Vulnerable email Accounts

Infinite Families of Optimal Splitting Authentication Codes Secure Against Spoofing Attacks of Higher Order
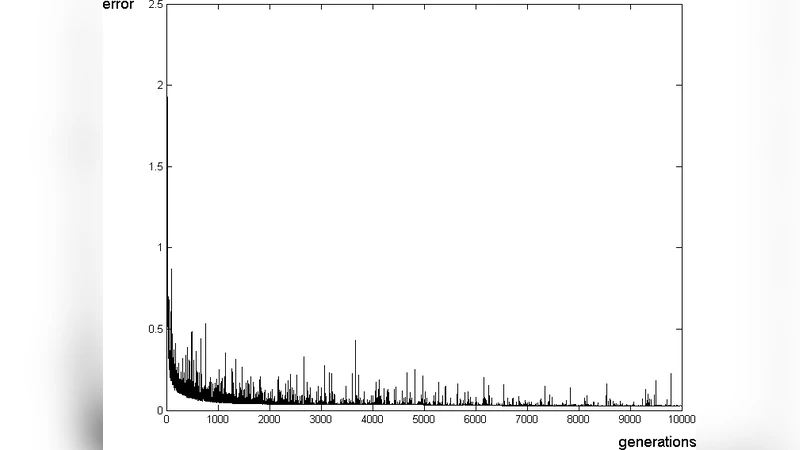
Using Neural Networks to improve classical Operating System Fingerprinting techniques
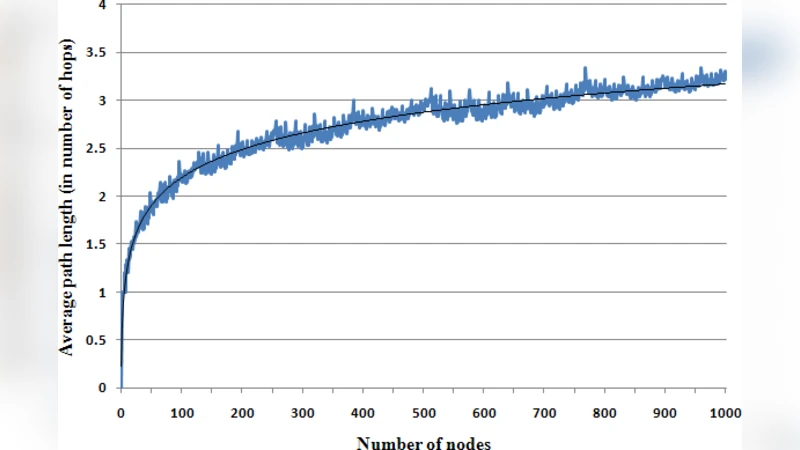
A Key Distribution Scheme for Sensor Networks Using Structured Graphs
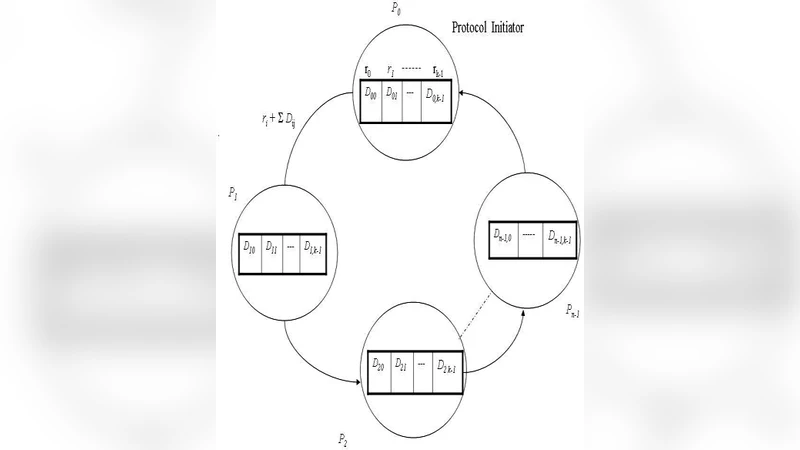
Privacy Preserving k Secure Sum Protocol
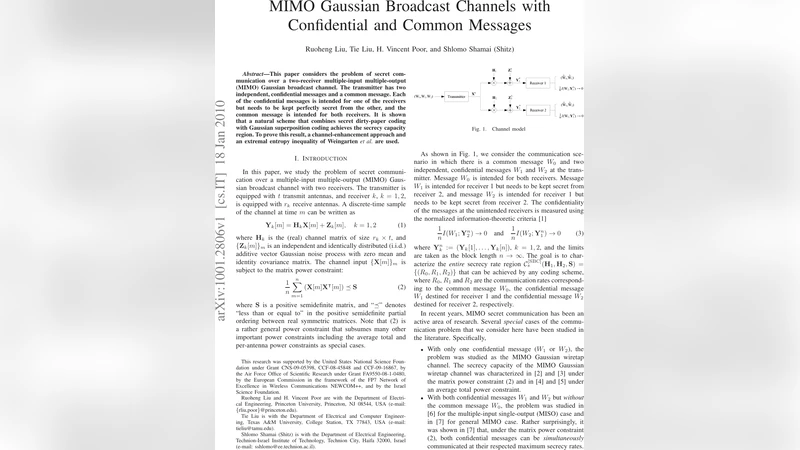
MIMO Gaussian Broadcast Channels with Confidential and Common Messages

Benalohs Dense Probabilistic Encryption Revisited

Interoperability, Trust Based Information Sharing Protocol and Security: Digital Government Key Issues

How to retrieve priced data

Quantum Tagging for Tags Containing Secret Classical Data
Key Substitution in the Symbolic Analysis of Cryptographic Protocols (extended version)
Breaking a Chaotic Cryptographic Scheme Based on Composition Maps

Relating two standard notions of secrecy
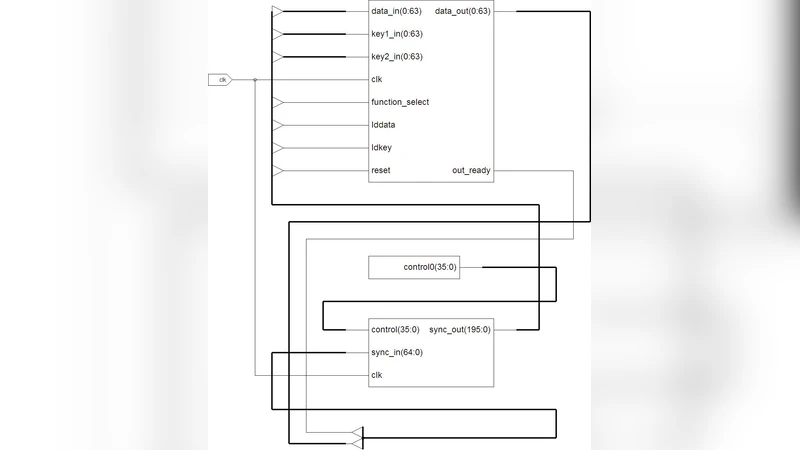
Hardware Implementation of TDES Crypto System with On Chip Verification in FPGA
An Improved Timestamp-Based Password Authentication Scheme Using Smart Cards

One software tool for testing square s-boxes
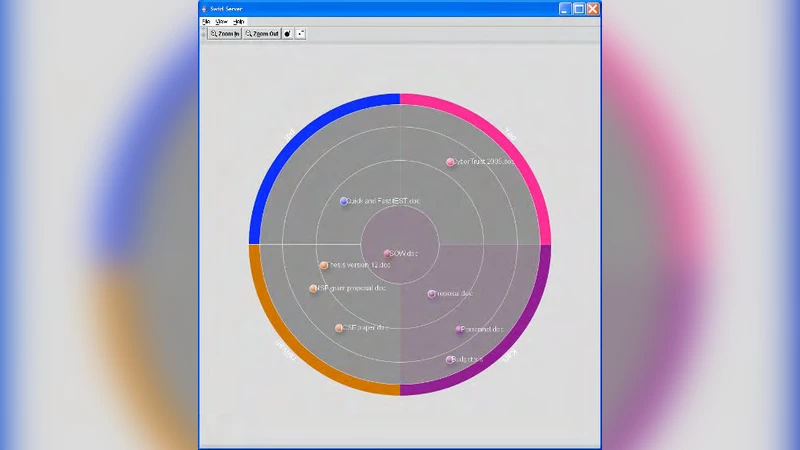
Security Visualization for peer-to-peer resource sharing applications

Analysis of the Security of BB84 by Model Checking

On the Problem of Local Randomness in Privacy Amplification with an Active Adversary
A simple generalization of the ElGamal cryptosystem to non-abelian groups II
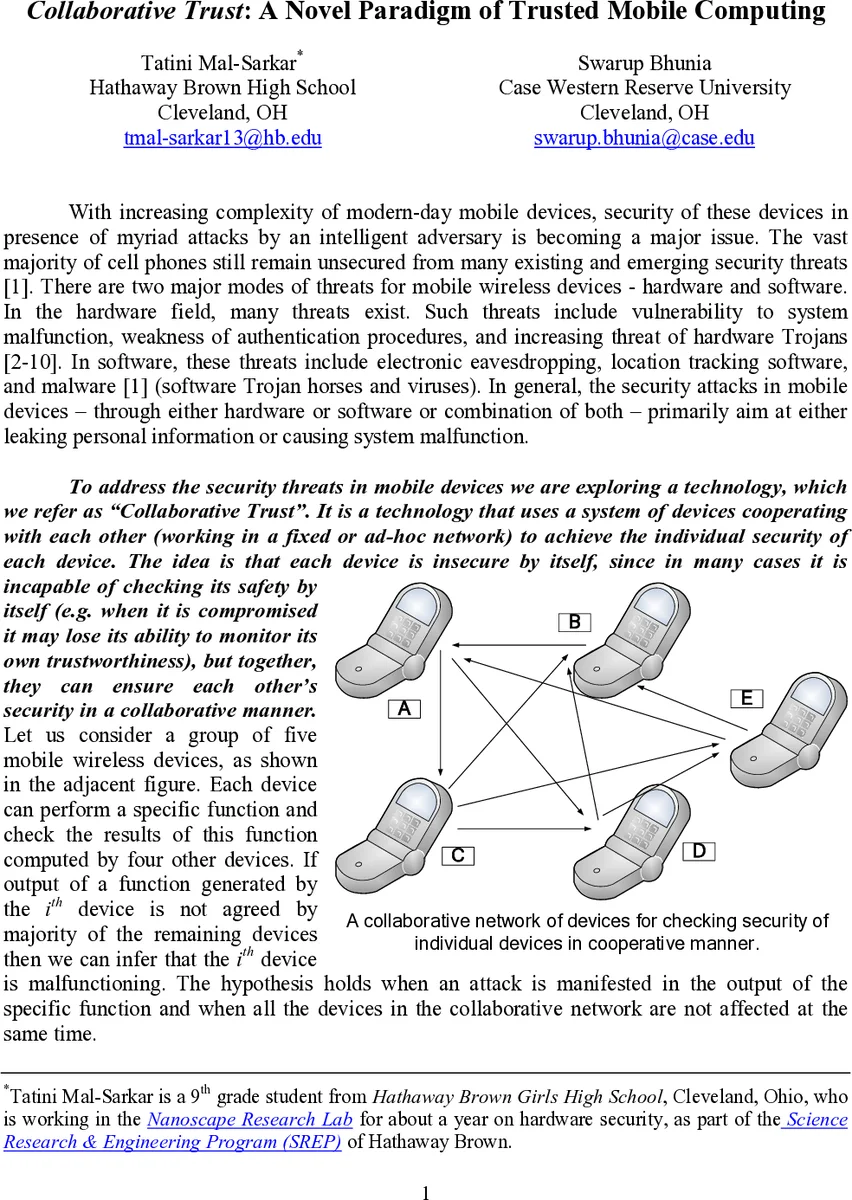
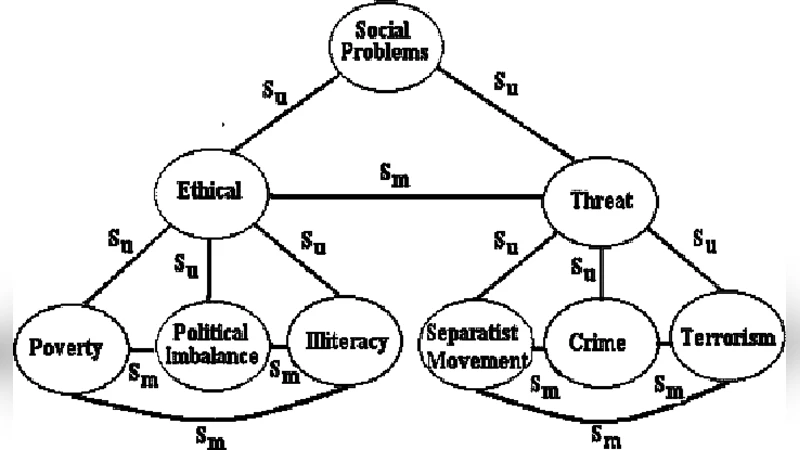
Collaborative Trust: A Novel Paradigm of Trusted Mobile Computing