Cs-Cr

A Trace Based Bisimulation for the Spi Calculus
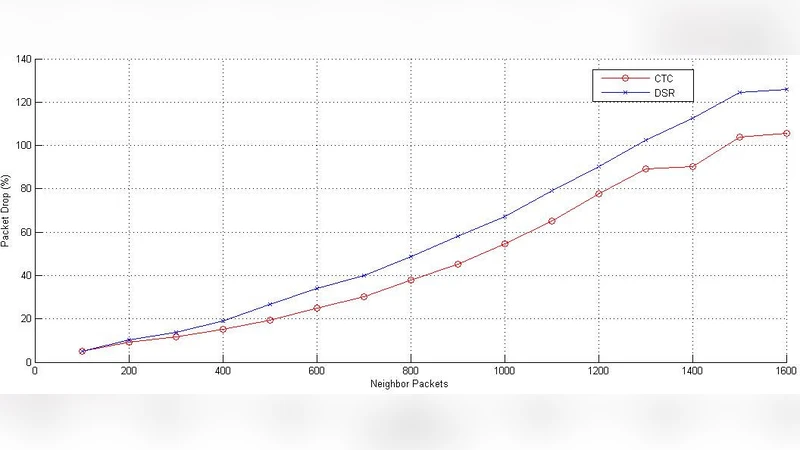
A New Scheme for Minimizing Malicious Behavior of Mobile Nodes in Mobile Ad Hoc Networks
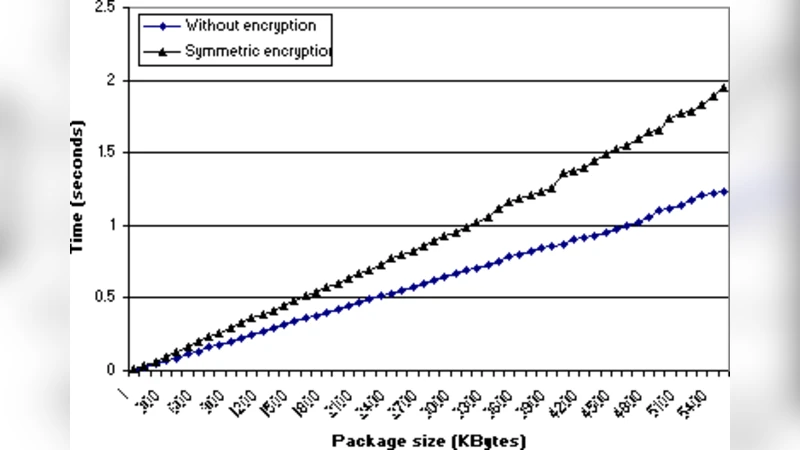
Extending WS-Security to Implement Security Protocols for Web Services
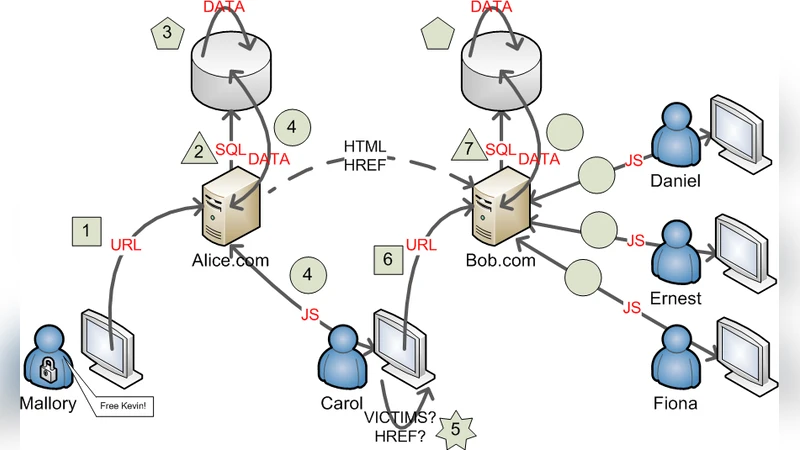
SQL/JavaScript Hybrid Worms As Two-stage Quines
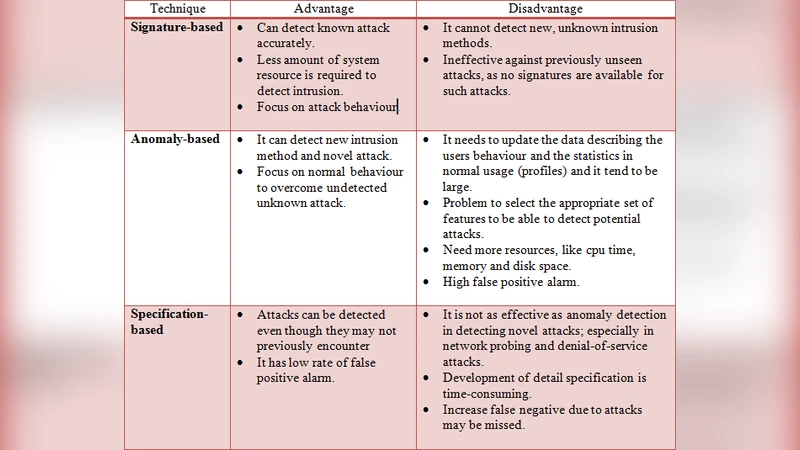
A New Generic Taxonomy on Hybrid Malware Detection Technique

Pairings on hyperelliptic curves

Informal specification-based performance evaluation of security protocols

Hard Fault Analysis of Trivium

Practical Schemes For Privacy & Security Enhanced RFID

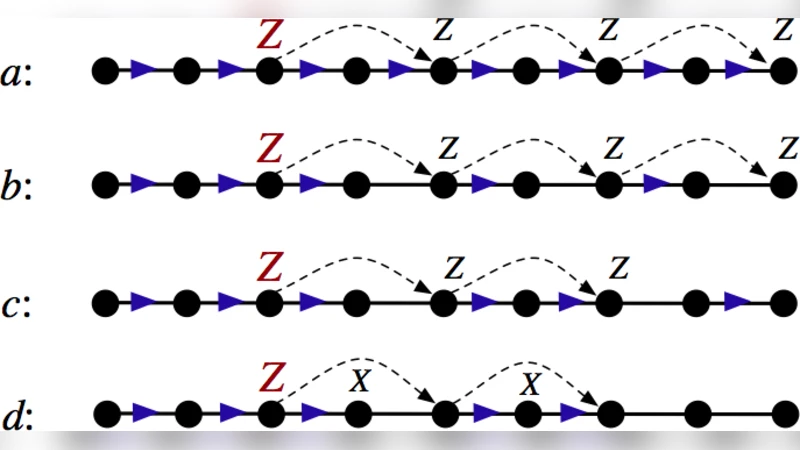
Attacking the combination generator
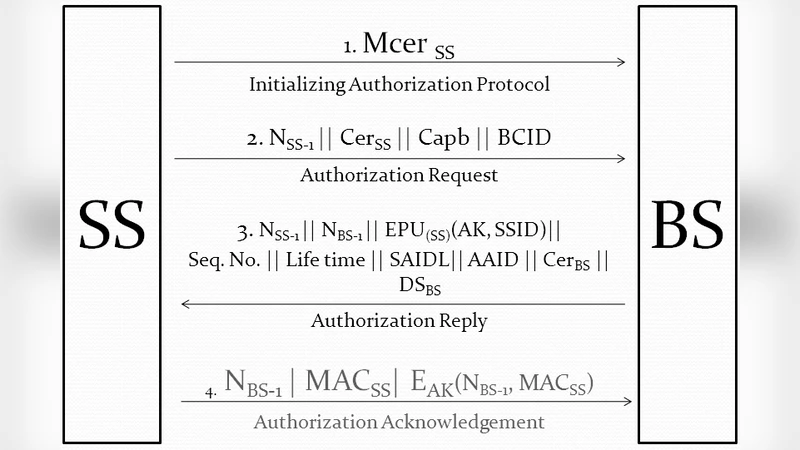
Computational Complexities and Breaches in Authentication Frameworks of Broadband Wireless Access

Philosophical Survey of Passwords
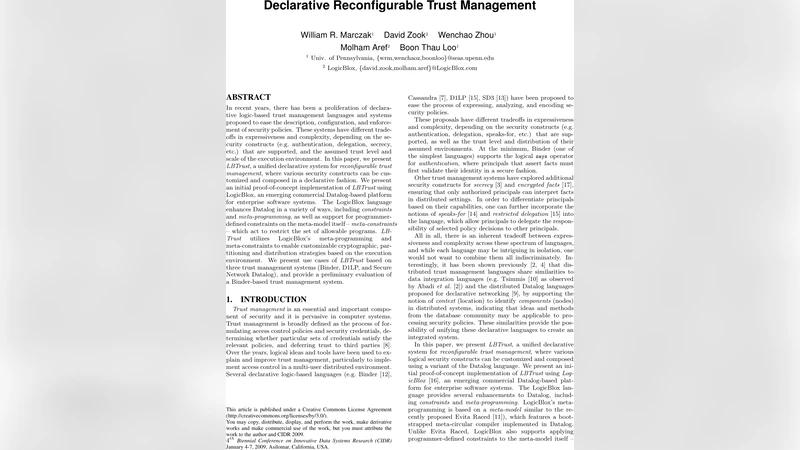
Declarative Reconfigurable Trust Management
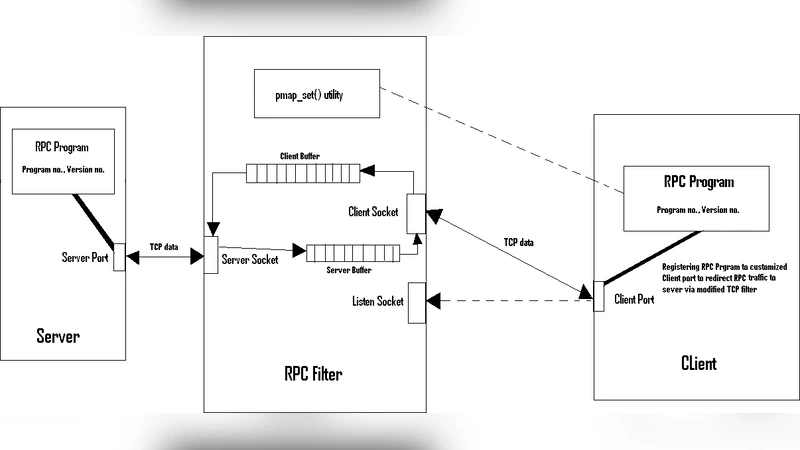
Securing Remote Procedure Calls over HTTPS

Minimizing Cache Timing Attack Using Dynamic Cache Flushing (DCF) Algorithm
Efficient and Spontaneous Privacy-Preserving Protocol for Secure Vehicular Communications
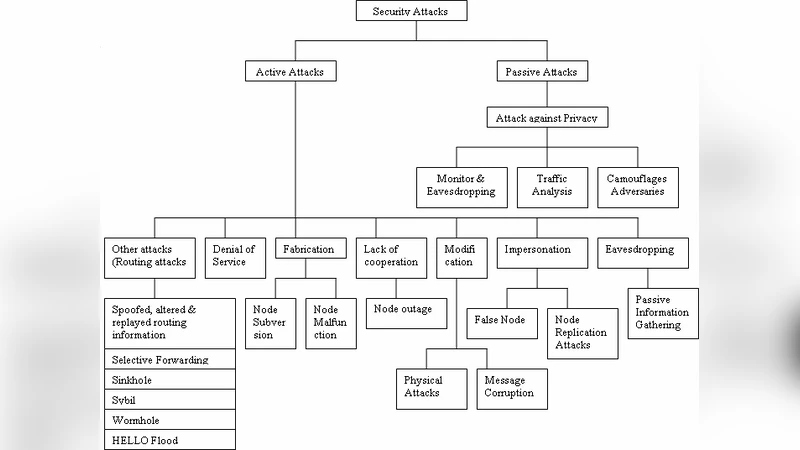
A Survey of Attacks, Security Mechanisms and Challenges in Wireless Sensor Networks
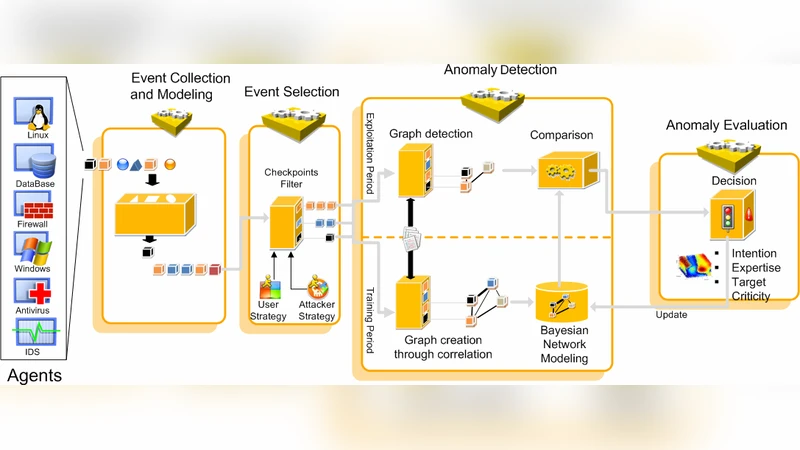
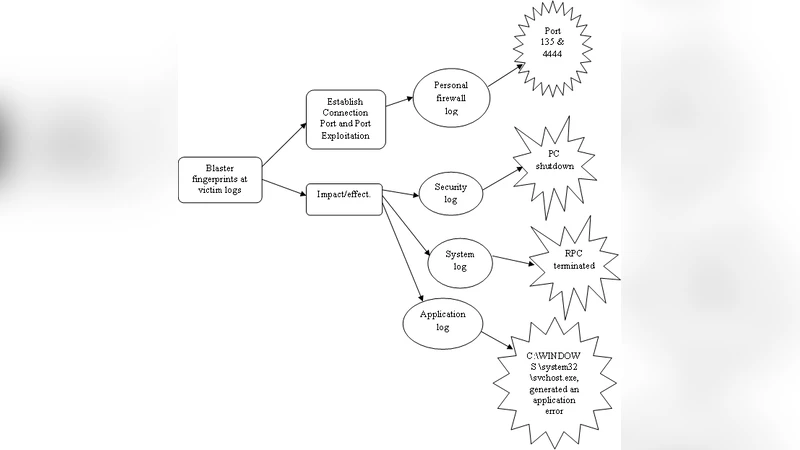
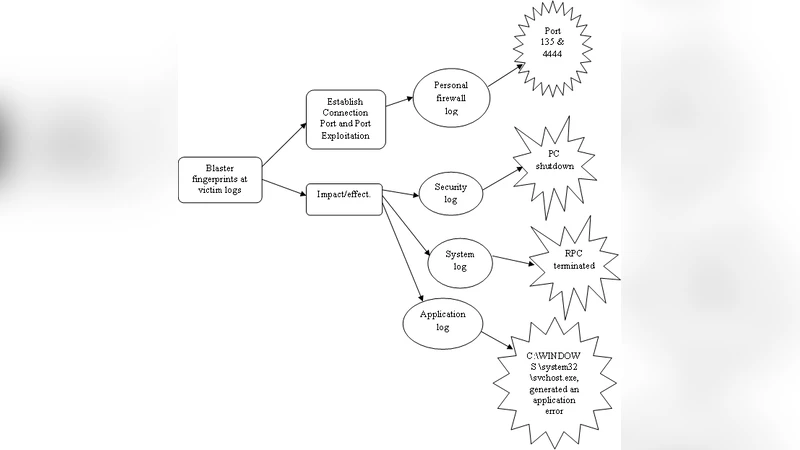
Comprehensive Security Framework for Global Threads Analysis
Information Flow in Secret Sharing Protocols
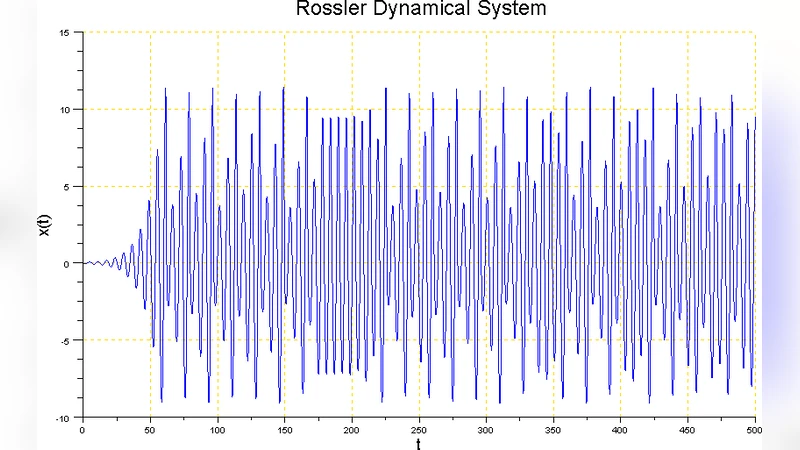
Rossler Nonlinear Dynamical Machine for Cryptography Applications

ODMRP with Quality of Service and local recovery with security Support

An Efficient and Publicly Verifiable Id-Based Multi-Signcryption Scheme
