Cs-Cr

Statistical Analysis of Privacy and Anonymity Guarantees in Randomized Security Protocol Implementations
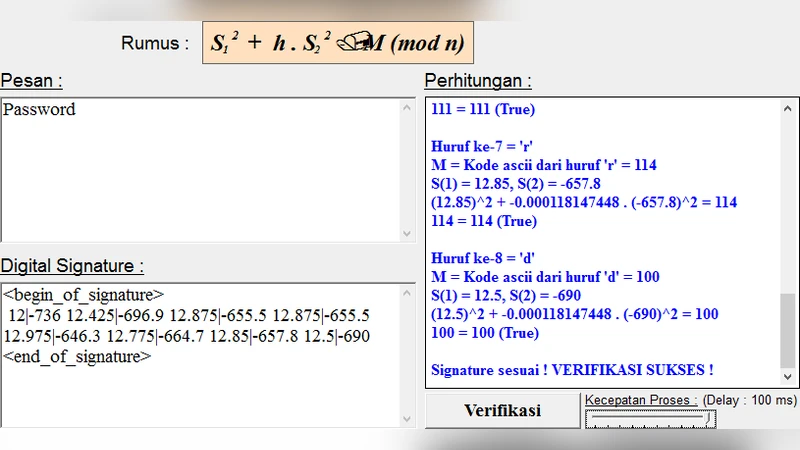
Digital Signature Security in Data Communication

Public Key Protocol Based on Amalgamated Free Product
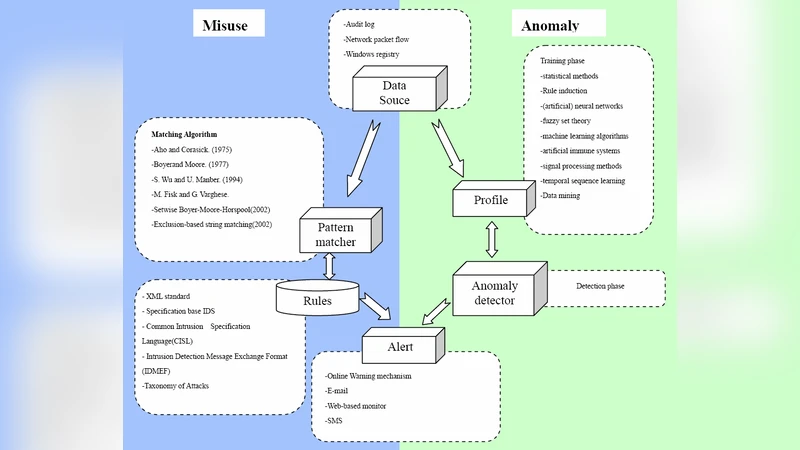
Using Rough Set and Support Vector Machine for Network Intrusion Detection

Intrusion-aware Alert Validation Algorithm for Cooperative Distributed Intrusion Detection Schemes of Wireless Sensor Networks

Secret-Key Generation using Correlated Sources and Channels

Secure Vehicular Communication Systems: Design and Architecture

Defense Strategies Against Modern Botnets
Unconditional security from noisy quantum storage

AIS for Misbehavior Detection in Wireless Sensor Networks: Performance and Design Principles
Mitigating the ICA Attack against Rotation Based Transformation for Privacy Preserving Clustering
On the Decidability of (ground) Reachability Problems for Cryptographic Protocols (extended version)
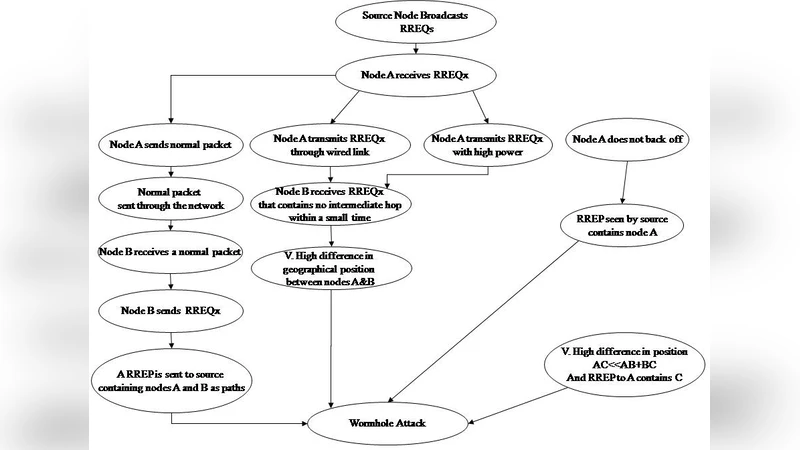
A Full Image of the Wormhole Attacks - Towards Introducing Complex Wormhole Attacks in wireless Ad Hoc Networks

Liberalizing Dependency
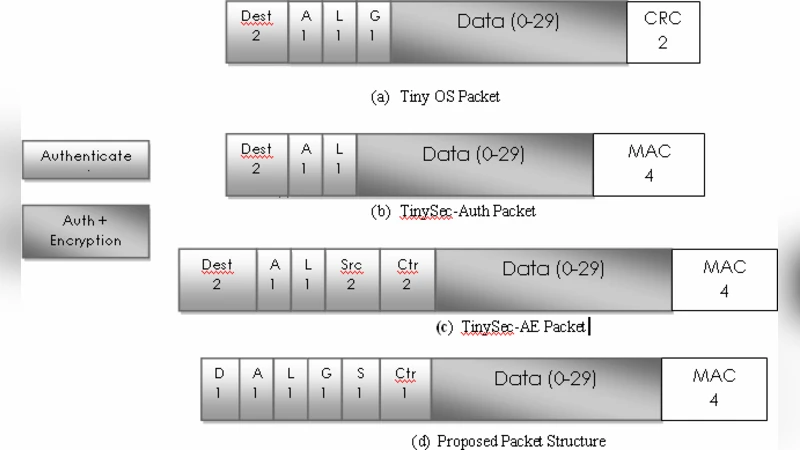
Complete Security Framework for Wireless Sensor Networks

SocialFilter: Collaborative Spam Mitigation using Social Networks

Performance Evaluation of Mesh based Multicast Reactive Routing Protocol under Black Hole Attack
Randomization for Security in Half-Duplex Two-Way Gaussian Channels
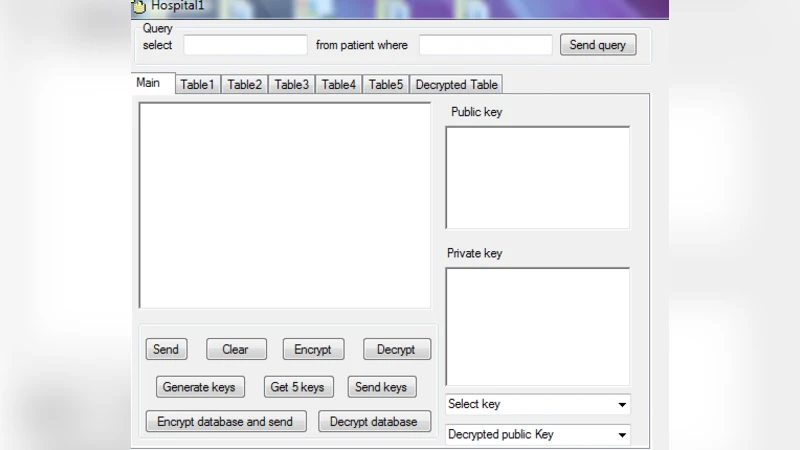
Preserving Privacy and Sharing the Data in Distributed Environment using Cryptographic Technique on Perturbed data
Space Efficient Secret Sharing: A Recursive Approach

An Algebraic Watchdog for Wireless Network Coding
Identification with Encrypted Biometric Data
