Cs-Cr


Text-Independent Speaker Recognition for Low SNR Environments with Encryption
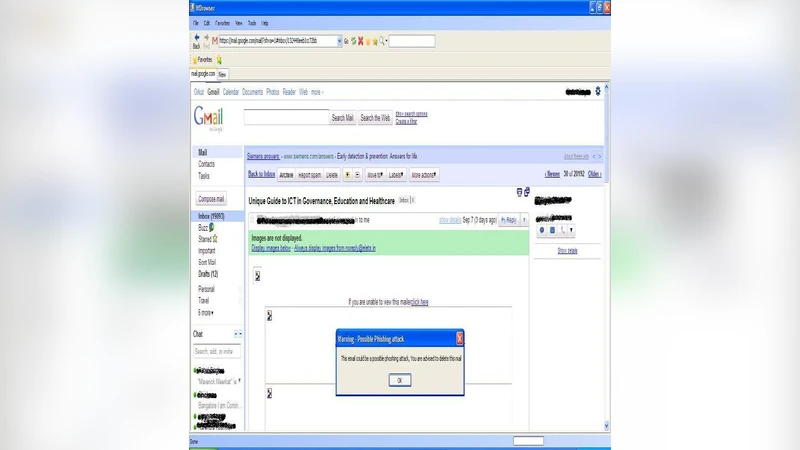
Implementing a Web Browser with Phishing Detection Techniques
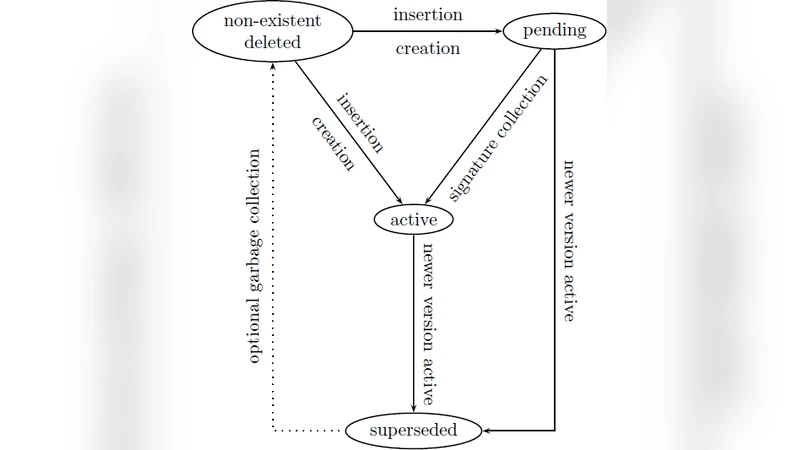
DDNFS: a Distributed Digital Notary File System
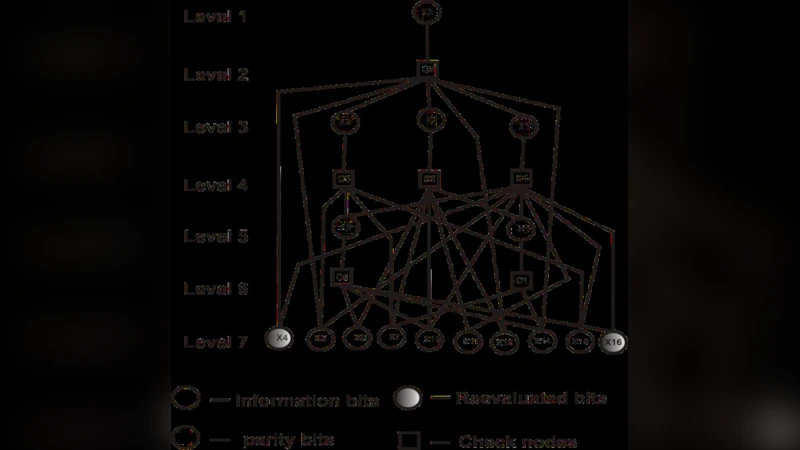
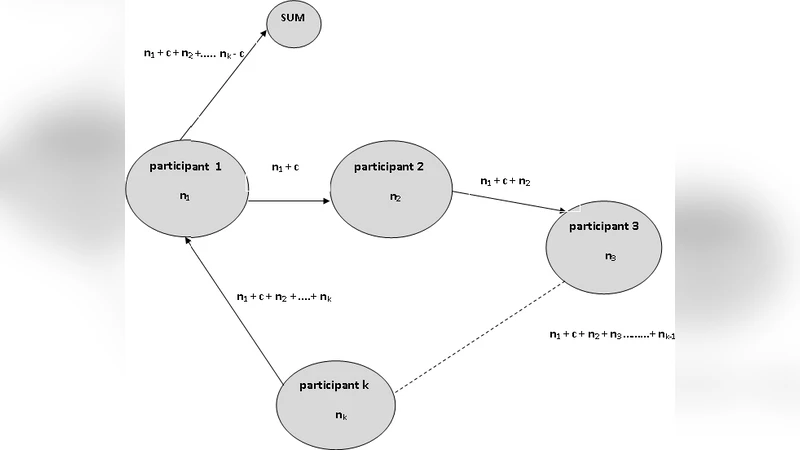
Error Detection and Correction for Distributed Group Key Agreement Protocol
Wiretap Channels: Implications of the More Capable Condition and Cyclic Shift Symmetry
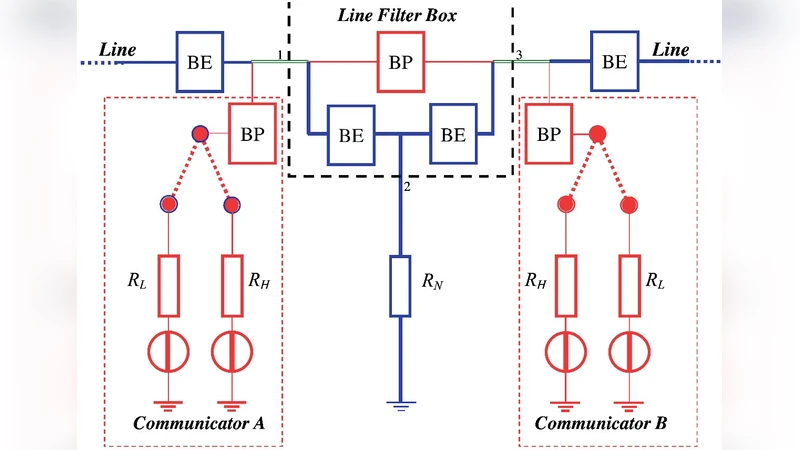
Information Networks Secured by the Laws of Physics
Countering Gattaca: Efficient and Secure Testing of Fully-Sequenced Human Genomes (Full Version)
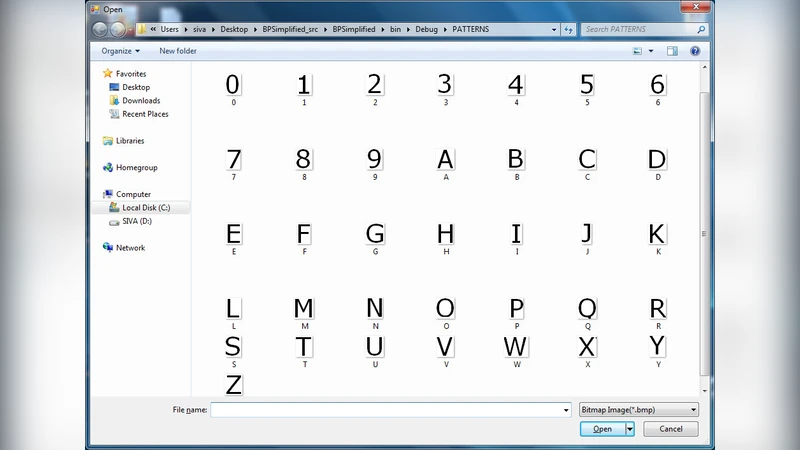
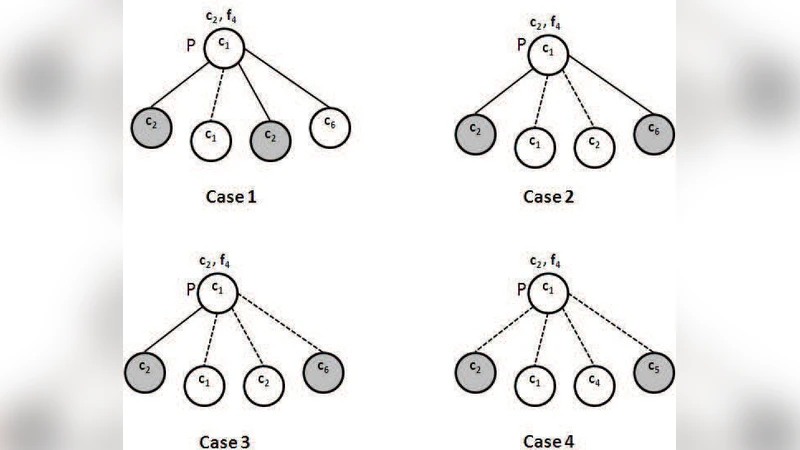
Handwritten Text Image Authentication using Back Propagation
Indices of Power in Optimal IDS Default Configuration: Theory and Examples

Extracting and Verifying Cryptographic Models from C Protocol Code by Symbolic Execution
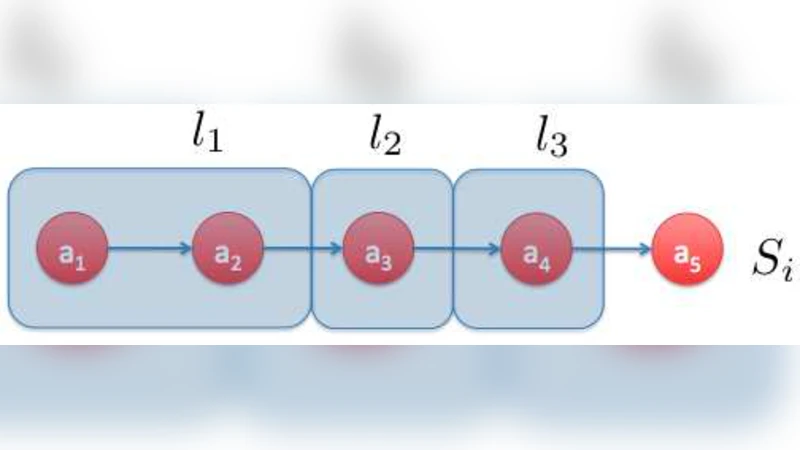
Privacy-Enhanced Methods for Comparing Compressed DNA Sequences

Attacker Control and Impact for Confidentiality and Integrity
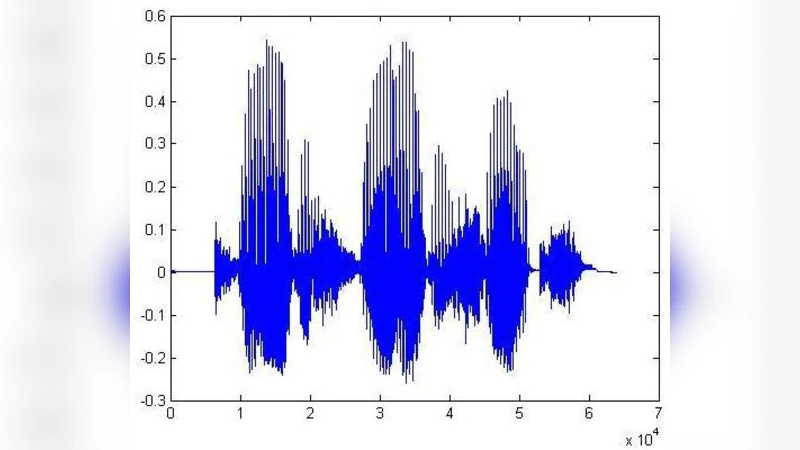
Audio Watermarking with Error Correction
Hilbert Matrix Based Cryptosystem using a Session Key
Prevention of Wormhole Attack in Wireless Sensor Network

Iterative Constructions and Private Data Release
Secure and Privacy- Aware Searching in Peer-to-Peer Networks
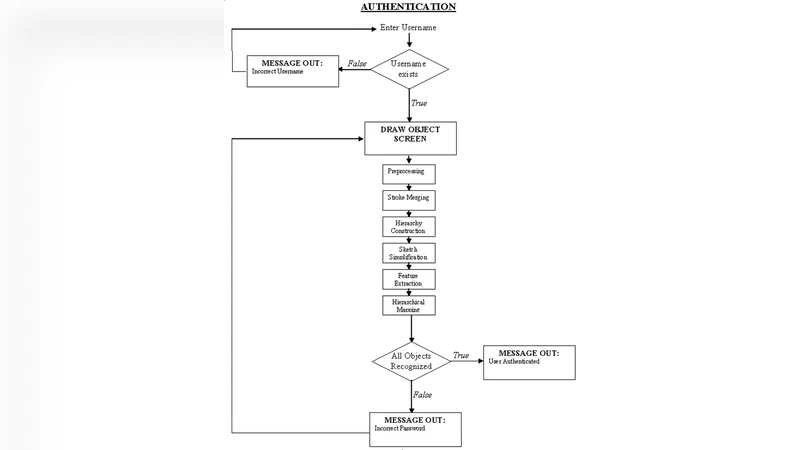
A Graphical Password Based System for Small Mobile Devices
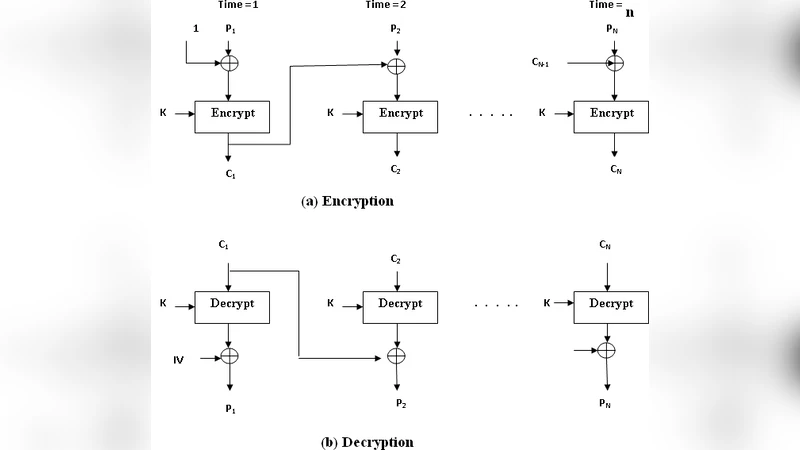
A Cryptosystem Based on Hilbert Matrix using Cipher Block Chaining Mode
Analysis of Differential Phase Shift Quantum Key Distribution
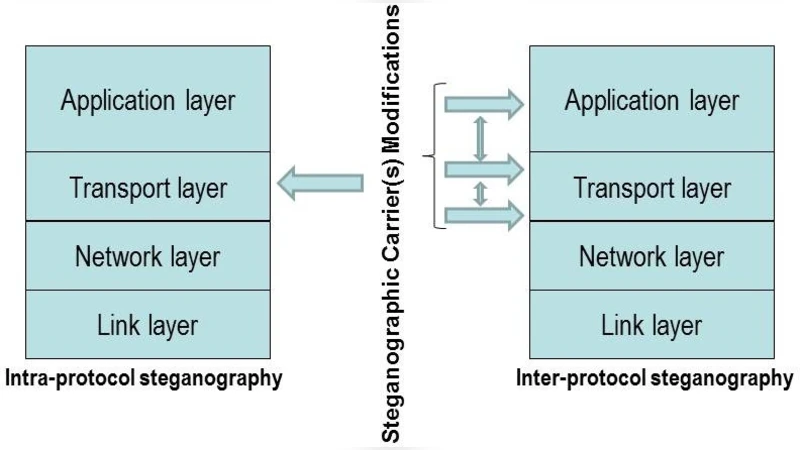
How Hidden Can Be Even More Hidden?
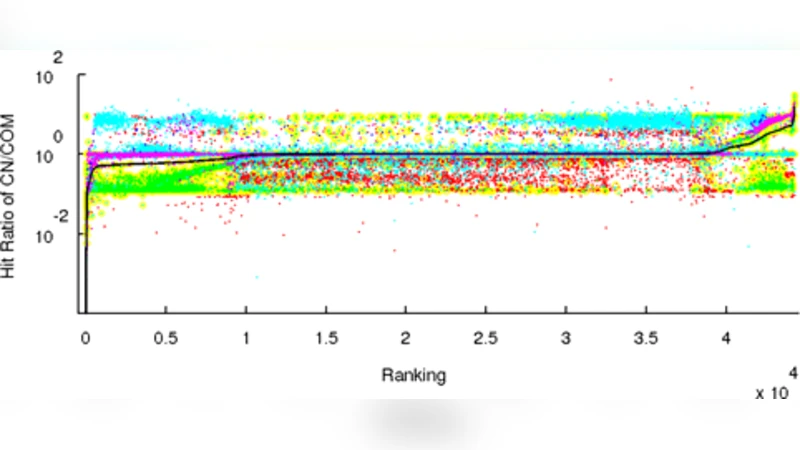
An Analysis of Chinese Search Engine Filtering