Cs-Cr

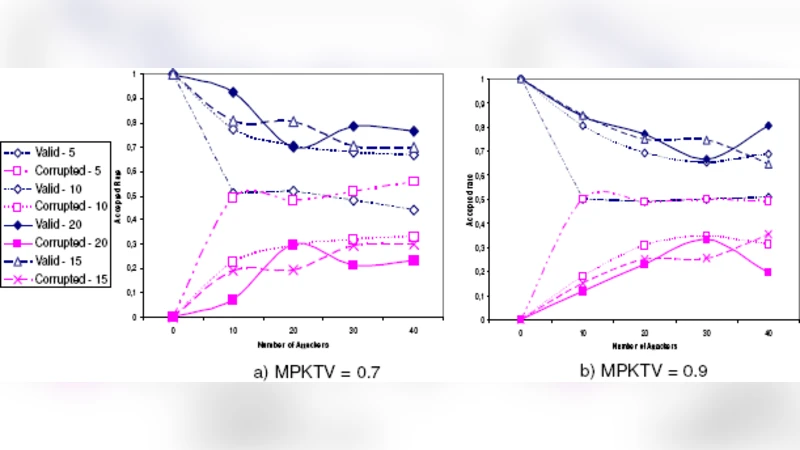
An Efficient Security Mechanism for High-Integrity Wireless Sensor Networks
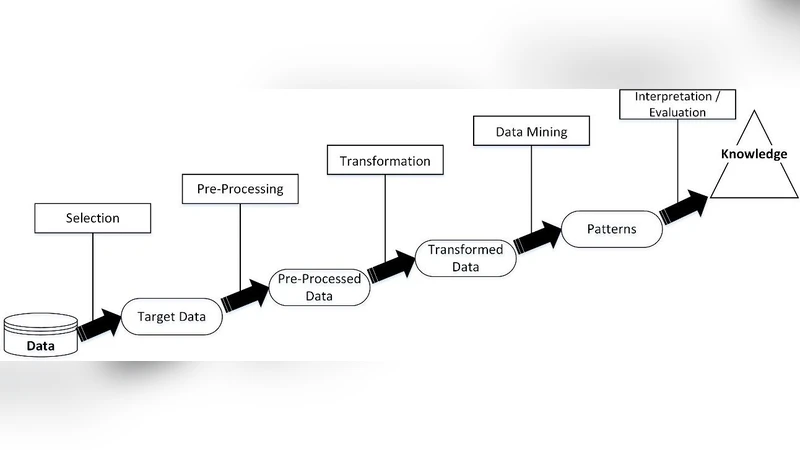
Data Science Methodology for Cybersecurity Projects

Adversarial vs behavioural-based defensive AI with joint, continual and active learning: automated evaluation of robustness to deception, poisoning and concept drift

IOTA Feasibility and Perspectives for Enabling Vehicular Applications

Efficient Determination of Equivalence for Encrypted Data
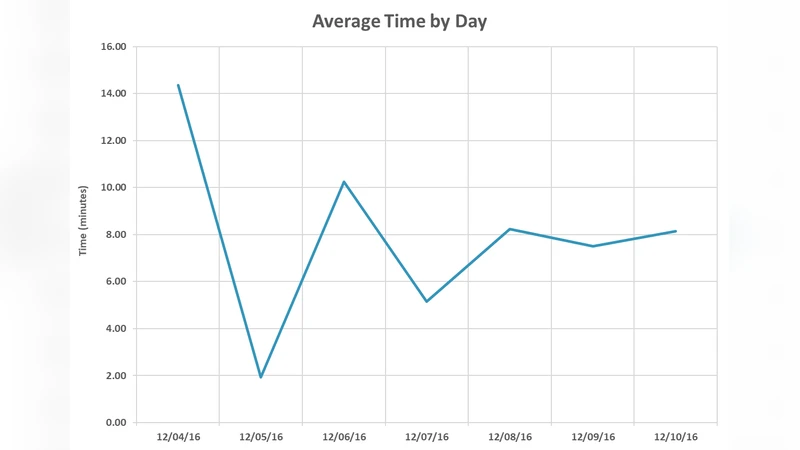
Digital Blues: An Investigation into the Use of Bluetooth Protocols
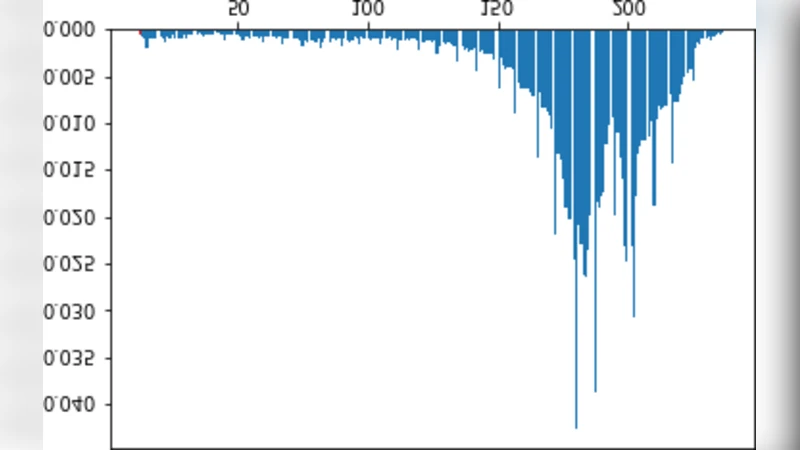
Hide the Image in FC-DenseNets to another Image
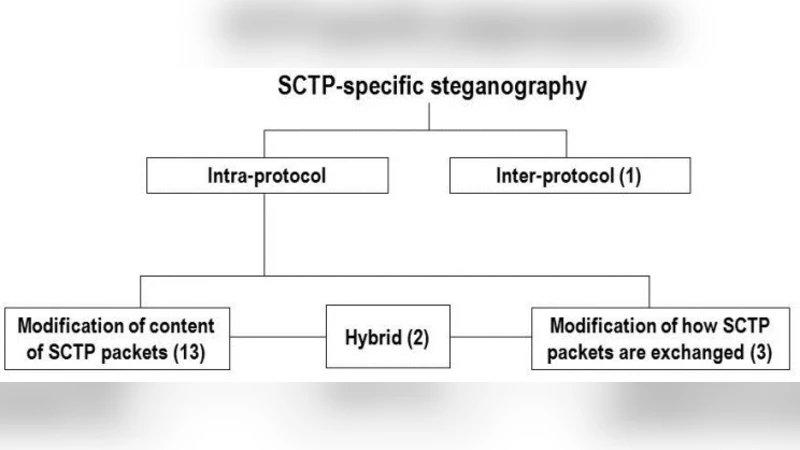
Hiding Information in a Stream Control Transmission Protocol
Automatic Web Security Unit Testing: XSS Vulnerability Detection

A Smart Approach for GPT Cryptosystem Based on Rank Codes

Distributed Private Data Analysis: On Simultaneously Solving How and What
Clustering based Privacy Preserving of Big Data using Fuzzification and Anonymization Operation
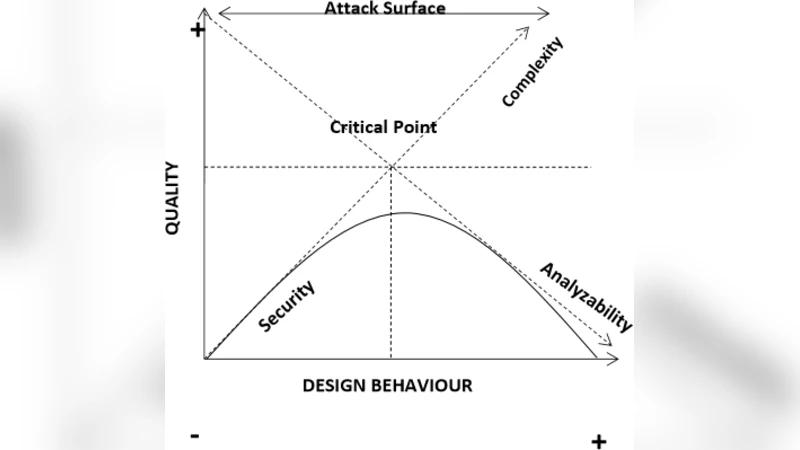
On the Relationship between Software Complexity and Security

Managing Delegation in Access Control Models
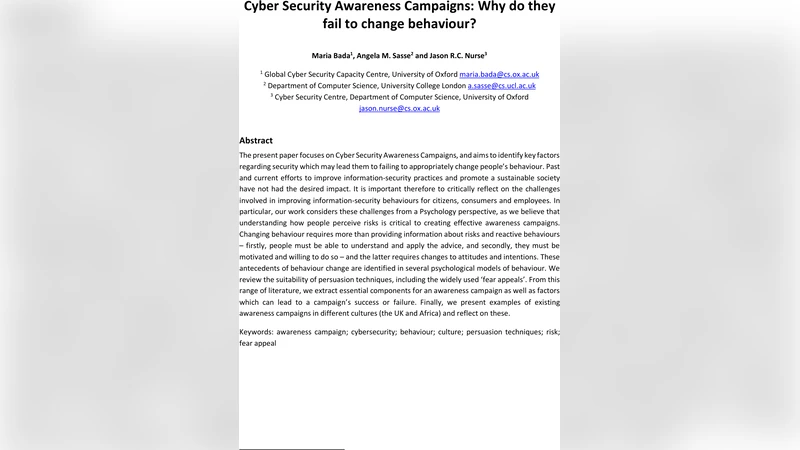
Cyber Security Awareness Campaigns: Why do they fail to change behaviour?
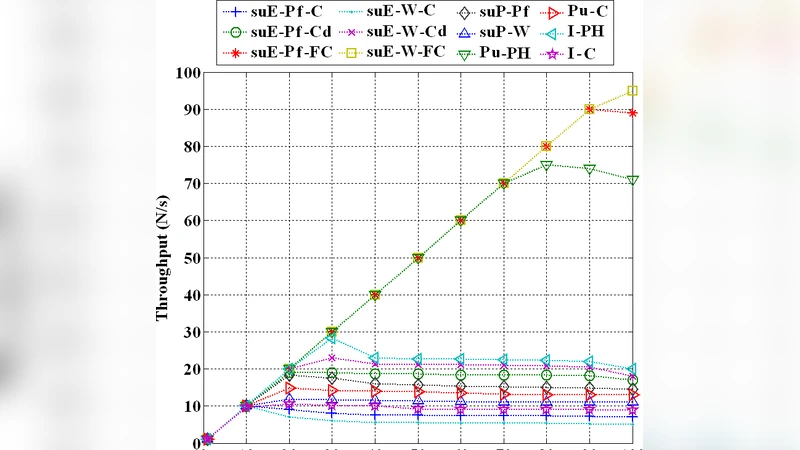
Performance Evaluation of Shared Hosting Security Methods
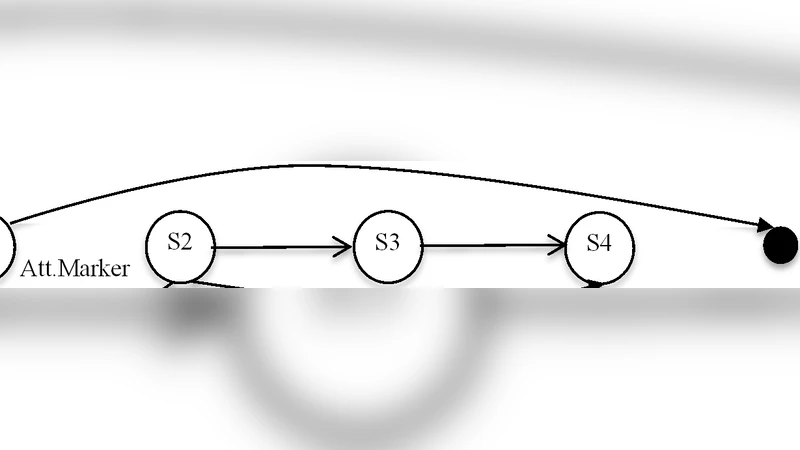
Secure Information Flow by Model Checking Pushdown System

Detecting cyber threats through social network analysis: short survey

A closer look at Intrusion Detection System for web applications
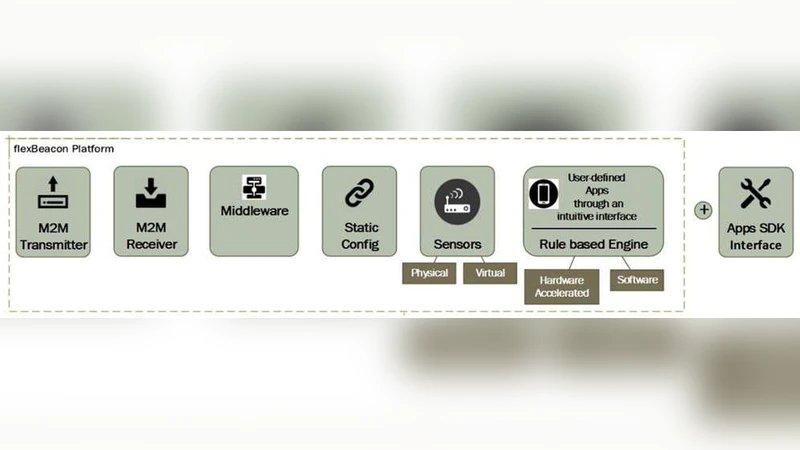
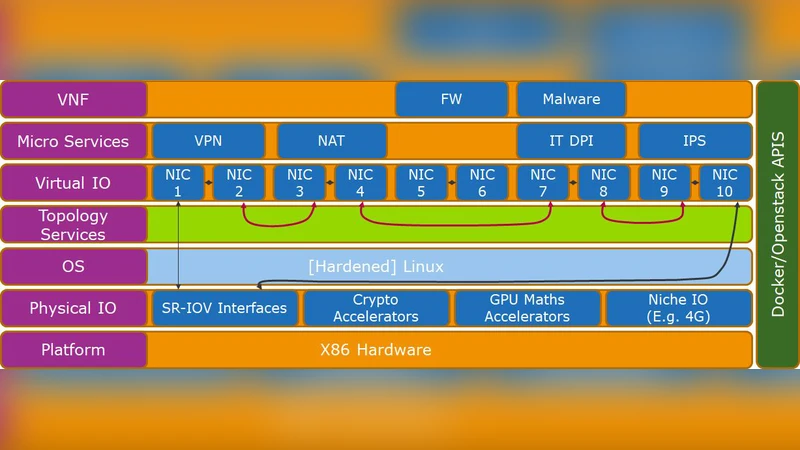
Softwarization of Internet of Things Infrastructure for Secure and Smart Healthcare
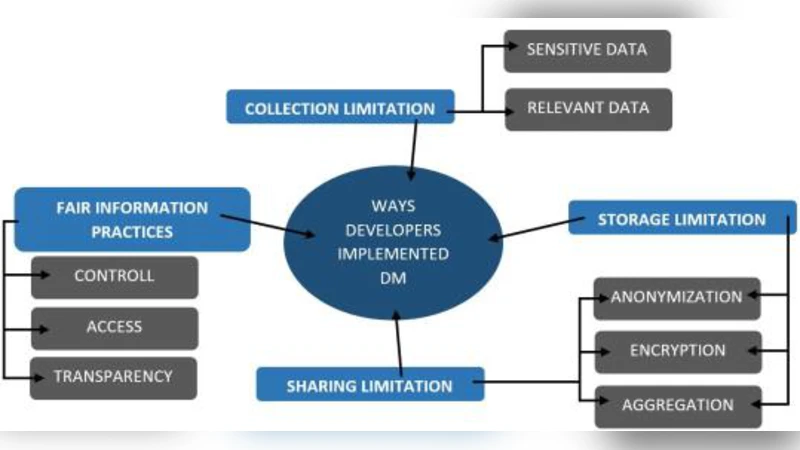
Understanding Software Developers Approach towards Implementing Data Minimization
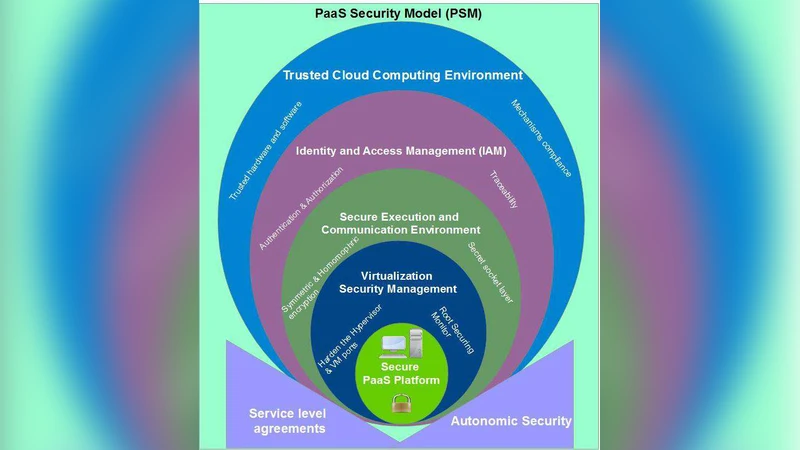
MPSM: Multi-prospective PaaS Security Model