
Cs-Cr


A Recruitment and Human Resource Management Technique Using Blockchain Technology for Industry 4.0
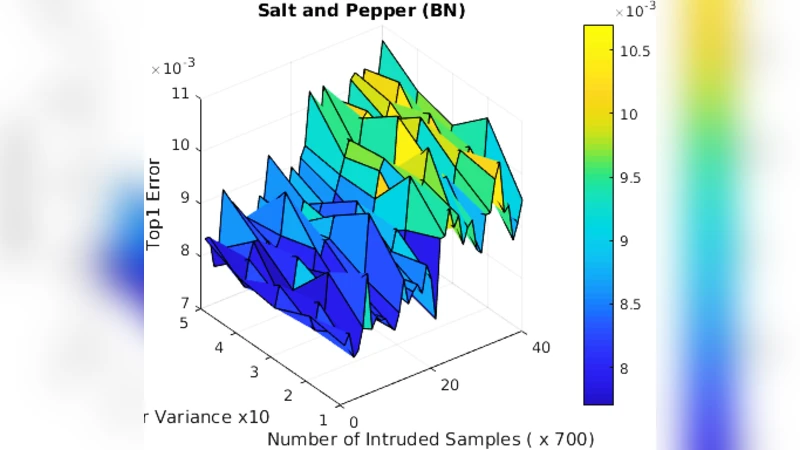
Security for Machine Learning-based Systems: Attacks and Challenges during Training and Inference

RNNSecureNet: Recurrent neural networks for Cyber security use-cases
Pricing and Investments in Internet Security: A Cyber-Insurance Perspective
Notions for RSA integers
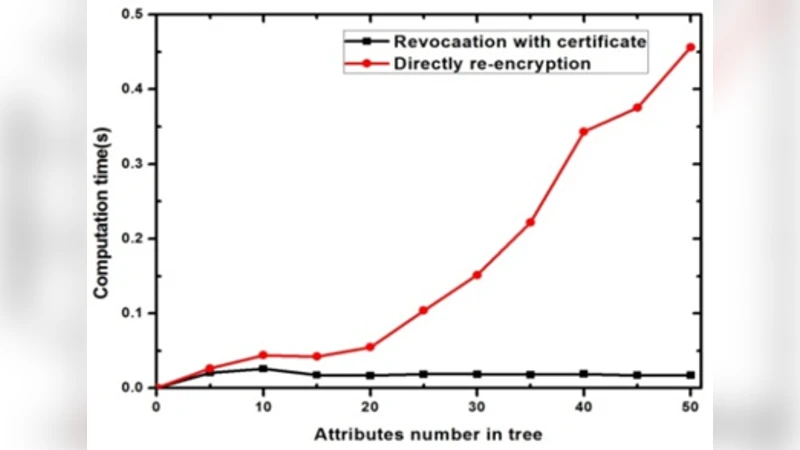
Secure Data Access for Wireless Body Sensor Networks
Replication Attack Mitigations for Static and Mobile WSN
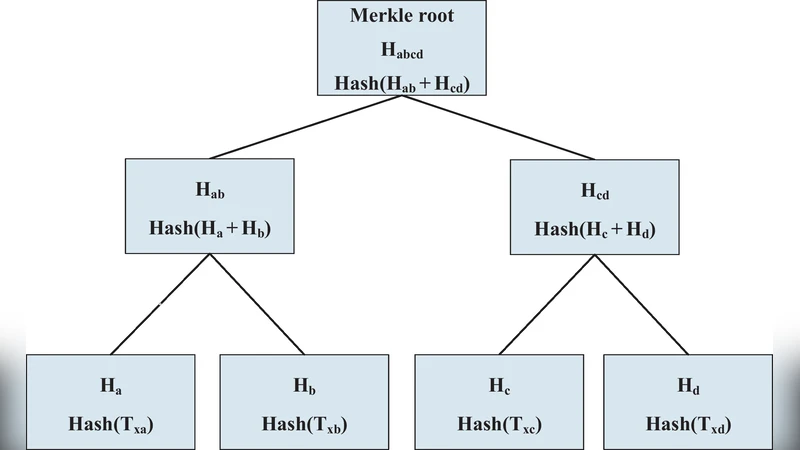
IoTChain: A Three-Tier Blockchain-based IoT Security Architecture
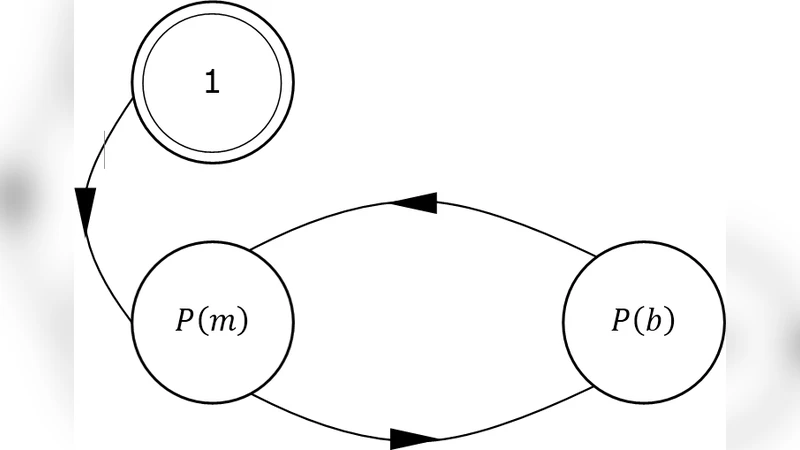
PoW, PoS, & Hybrid protocols: A Matter of Complexity?
Augmented Rotation-Based Transformation for Privacy-Preserving Data Clustering

An Unconditionally Secure Key Management Scheme for Large-Scale Heterogeneous Wireless Sensor Networks
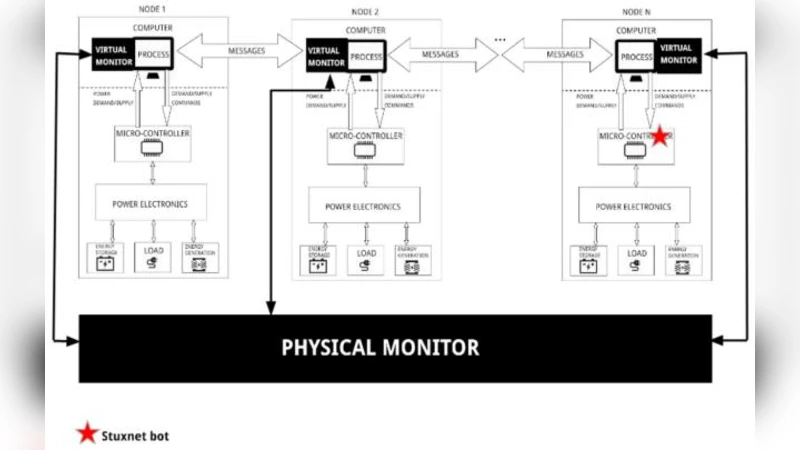
Introduction of a Hybrid Monitor to Cyber-Physical Systems
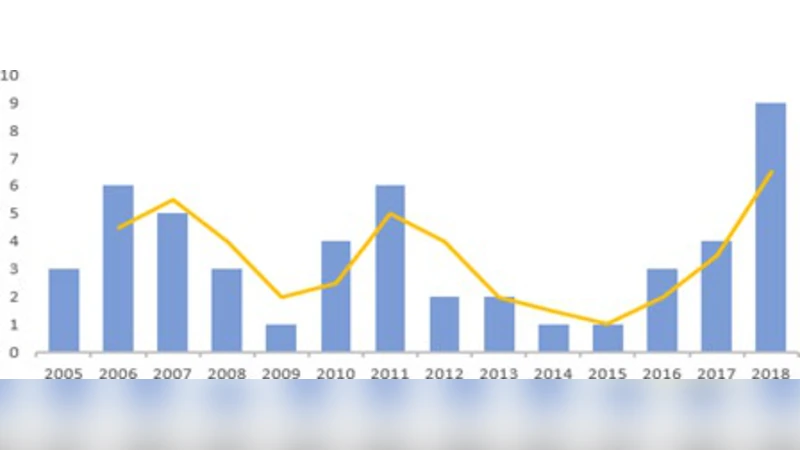
All About Phishing: Exploring User Research through a Systematic Literature Review
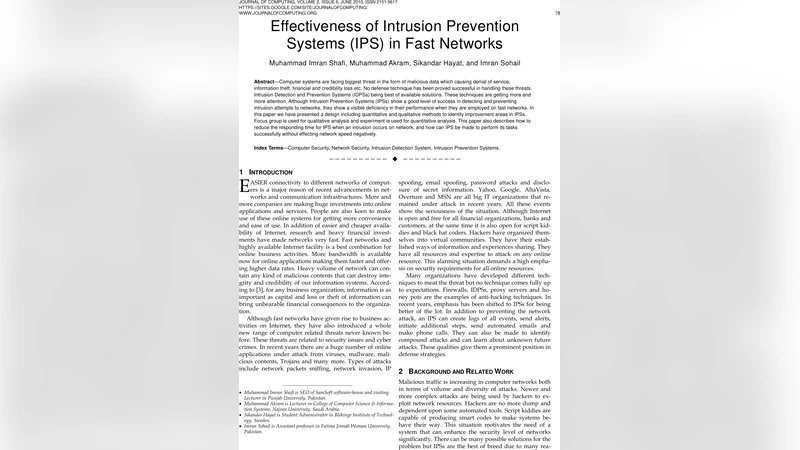
Effectiveness of Intrusion Prevention Systems (IPS) in Fast Networks
The Trailer of Blockchain Governance Game

Static Malware Detection & Subterfuge: Quantifying the Robustness of Machine Learning and Current Anti-Virus

An Improved Efficient Key Distribution Mechanism for Large-Scale Heterogeneous Mobile Sensor Networks
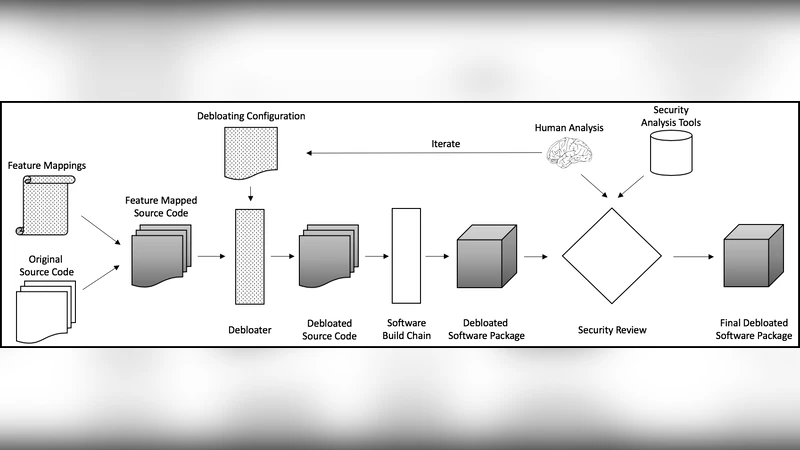
CARVE: Practical Security-Focused Software Debloating Using Simple Feature Set Mappings
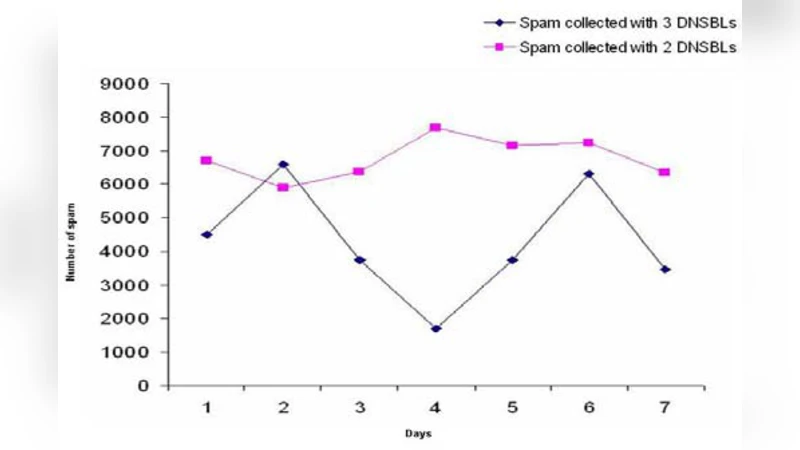
Novel Mechanism to Defend DDoS Attacks Caused by Spam
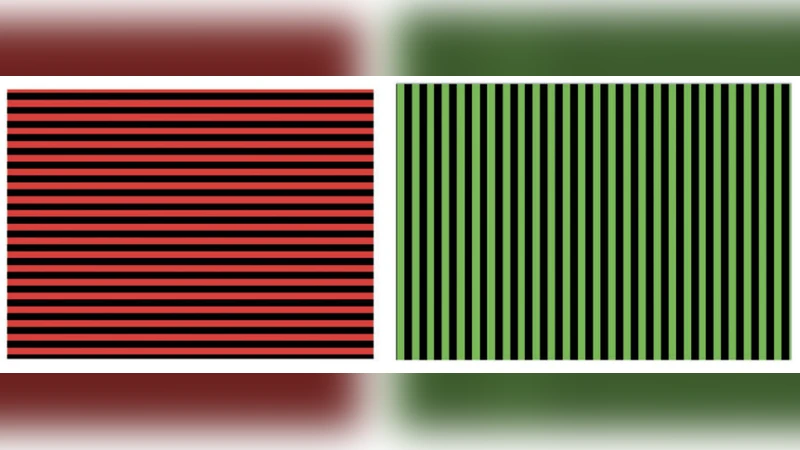
Challenges and New Directions in Augmented Reality, Computer Security, and Neuroscience -- Part 1: Risks to Sensation and Perception

Understanding Security Requirements and Challenges in Internet of Things (IoTs): A Review

Cryptanalysis of a Chaos-Based Fast Image Encryption Algorithm for Embedded Systems
