Cs-Cr


A secure solution on hierarchical access control

Achieving Both Valid and Secure Logistic Regression Analysis on Aggregated Data from Different Private Sources
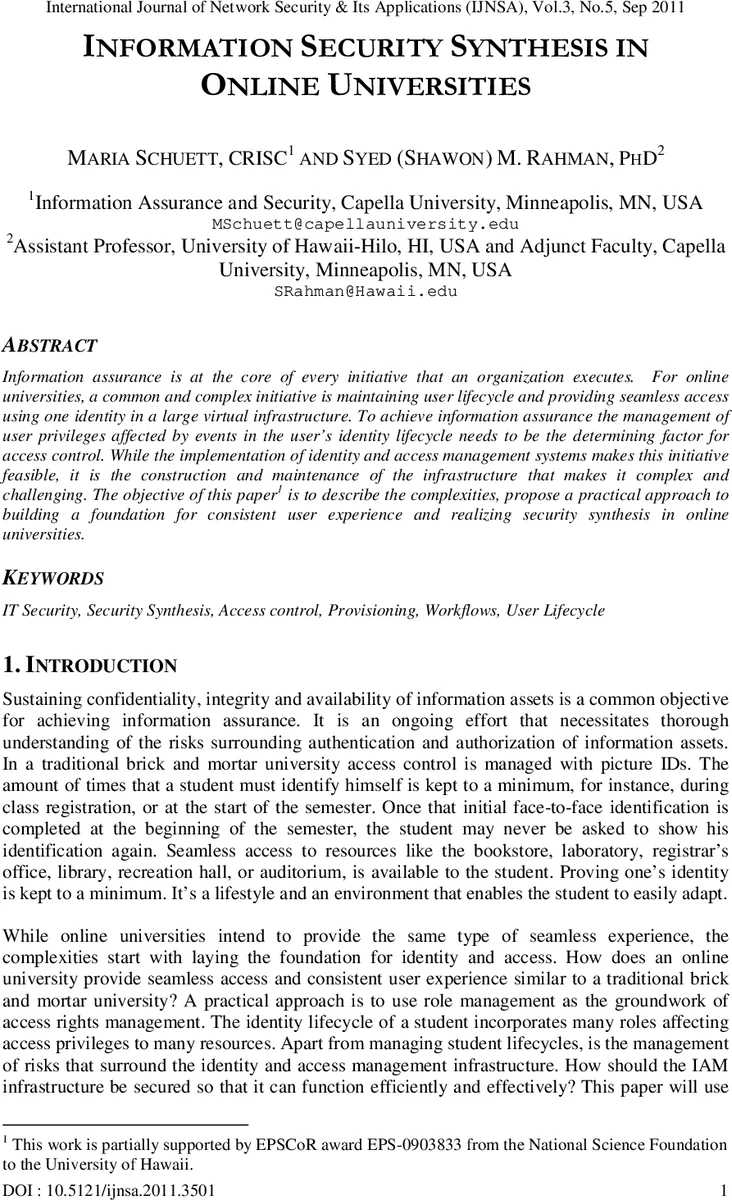
Effective Ways of Secure, Private and Trusted Cloud Computing
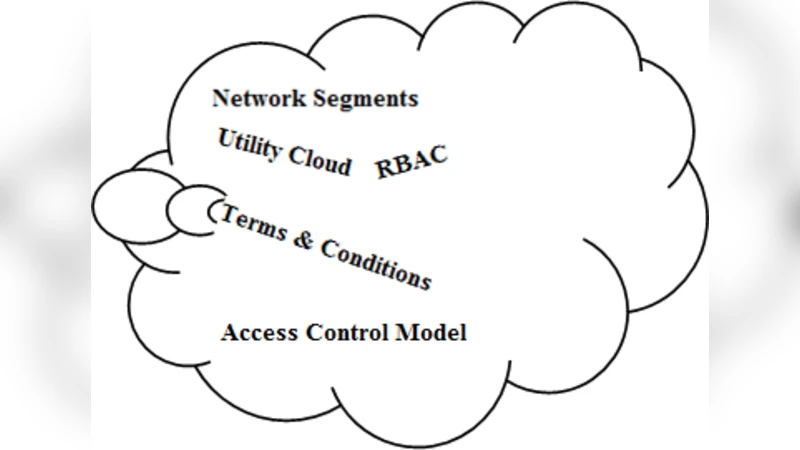
Face Recognition Using Discrete Cosine Transform for Global and Local Features

Two Classes of Crooked Multinomials Inequivalent to Power Functions
Cryptanalysis of two mutual authentication protocols for low-cost RFID

Serf and Turf: Crowdturfing for Fun and Profit

Reversible Data Hiding Based on Two-level HDWT Coefficient Histograms

A Logical Method for Policy Enforcement over Evolving Audit Logs

Fully Simulatable Quantum-Secure Coin-Flipping and Applications

Physical-Layer Security over Correlated Erasure Channels

On the Decidability of Non Interference over Unbounded Petri Nets
Artificial Immune Privileged Sites as an Enhancement to Immuno-Computing Paradigm
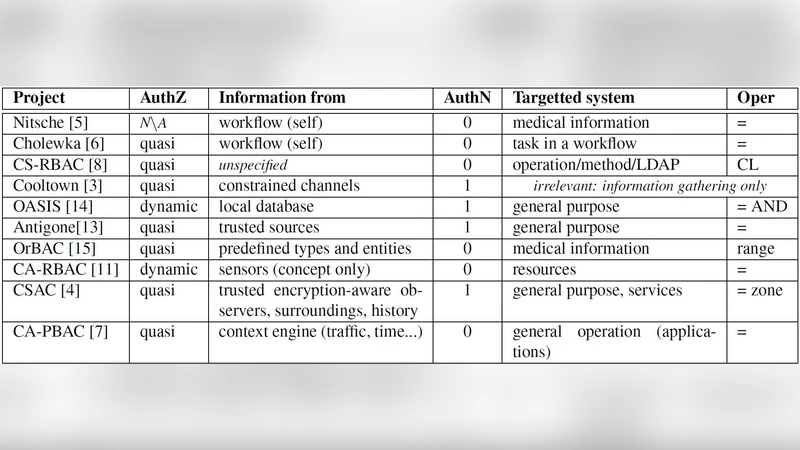
Context-aware Authorization in Highly Dynamic Environments
Information Theoretic Authentication and Secrecy Codes in the Splitting Model

A Spatial-Epistemic Logic for Reasoning about Security Protocols
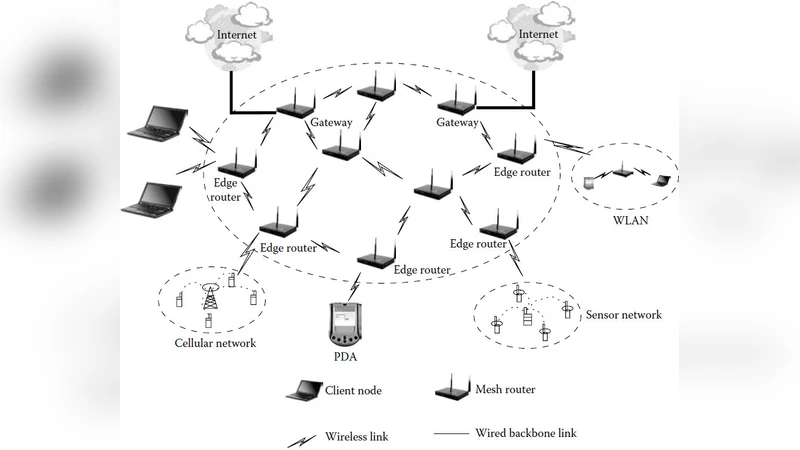
Secure Routing in Wireless Mesh Networks

Asymptotically false-positive-maximizing attack on non-binary Tardos codes
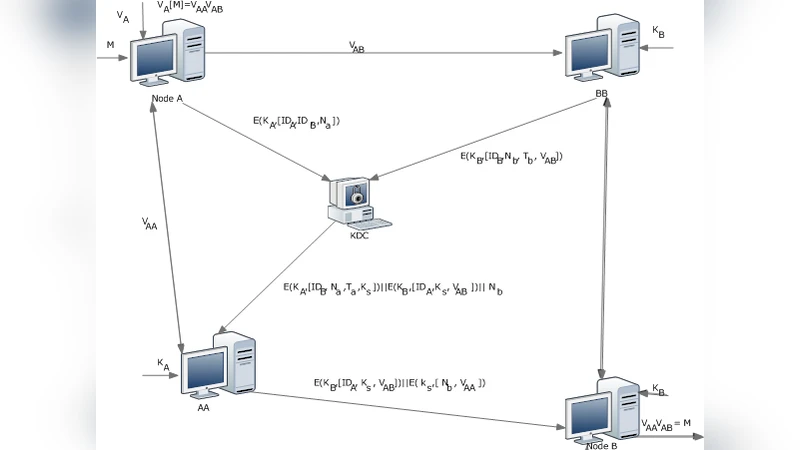
A new protocol implementing authentication transformations for multi-located parties

Covert channel detection using Information Theory
Darwin inside the machines: Malware evolution and the consequences for computer security

DECENT: A Decentralized Architecture for Enforcing Privacy in Online Social Networks