Cs-Cr
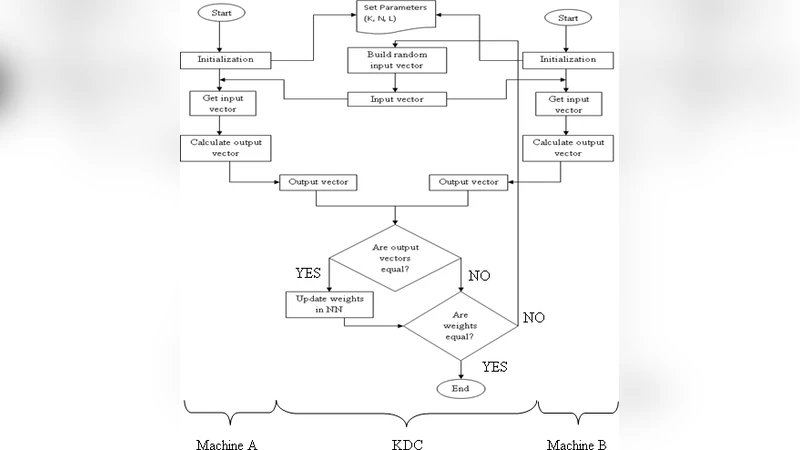
Design of an Efficient Neural Key Distribution Centre
Applying static code analysis to firewall policies for the purpose of anomaly detection

A Formalization of Polytime Functions
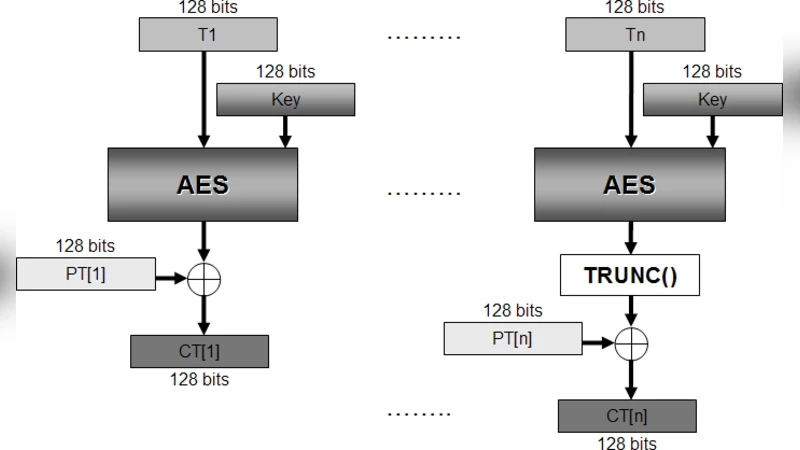
EPS Confidentiality and Integrity mechanisms Algorithmic Approach

On Communication Protocols that Compute Almost Privately

Improving Anonymity in Shared Key Primitives Based on Perfect Hash Families

Assisted Common Information: Further Results

On the Semantics of Purpose Requirements in Privacy Policies

Asymptotic fingerprinting capacity for non-binary alphabets
Minutiae Extraction from Fingerprint Images - a Review

CompChall: Addressing Password Guessing Attacks

A secure solution on hierarchical access control

Achieving Both Valid and Secure Logistic Regression Analysis on Aggregated Data from Different Private Sources
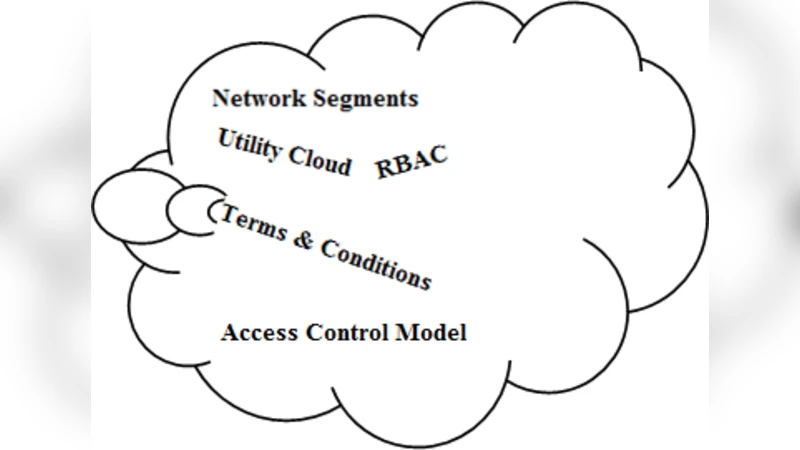
Effective Ways of Secure, Private and Trusted Cloud Computing
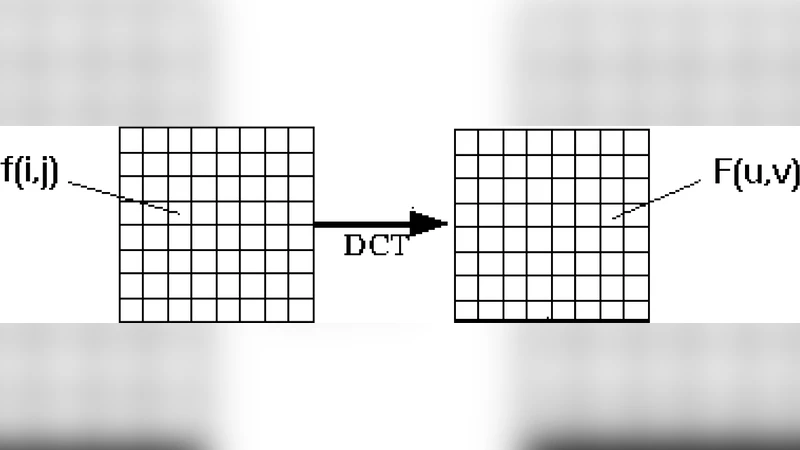
Face Recognition Using Discrete Cosine Transform for Global and Local Features

Two Classes of Crooked Multinomials Inequivalent to Power Functions
Cryptanalysis of two mutual authentication protocols for low-cost RFID

Serf and Turf: Crowdturfing for Fun and Profit

Reversible Data Hiding Based on Two-level HDWT Coefficient Histograms

A Logical Method for Policy Enforcement over Evolving Audit Logs

Fully Simulatable Quantum-Secure Coin-Flipping and Applications

Physical-Layer Security over Correlated Erasure Channels
