Cs-Cr

Evaluating the Utility of Anonymized Network Traces for Intrusion Detection

Privacy in Location Based Services: Primitives Toward the Solution

Probabilistic Visual Secret Sharing Schemes for Gray-scale images and Color images

Information-theoretic security without an honest majority
An Experimental Investigation of Secure Communication With Chaos Masking

The Impossibility Of Secure Two-Party Classical Computation

On the Performance Evaluation of Encounter-based Worm Interactions Based on Node Characteristics

Supervised secure entanglement sharing for faithful quantum teleportation via tripartite W states

Encounter-based worms: Analysis and Defense
Cryptography from Noisy Storage

Key Agreement and Authentication Schemes Using Non-Commutative Semigroups

Very fast watermarking by reversible contrast mapping
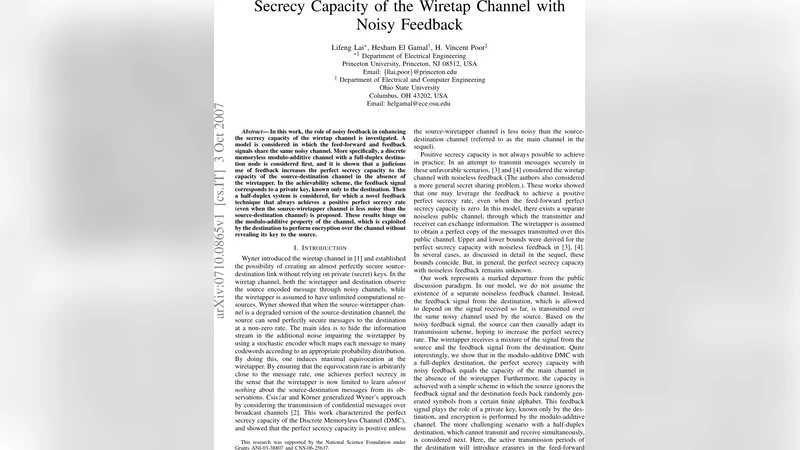
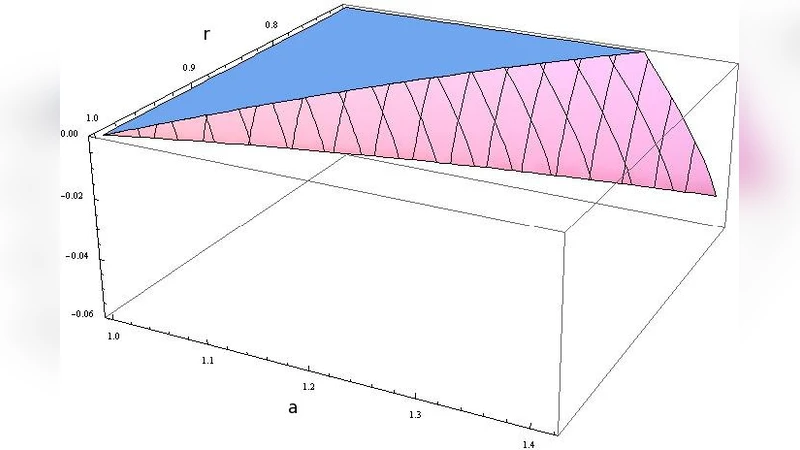
Secrecy Capacity of the Wiretap Channel with Noisy Feedback

Performance Considerations for an Embedded Implementation of OMA DRM 2

Using Kolmogorov Complexity for Understanding Some Limitations on Steganography

New families of cryptographic systems
Predicting the Presence of Internet Worms using Novelty Detection
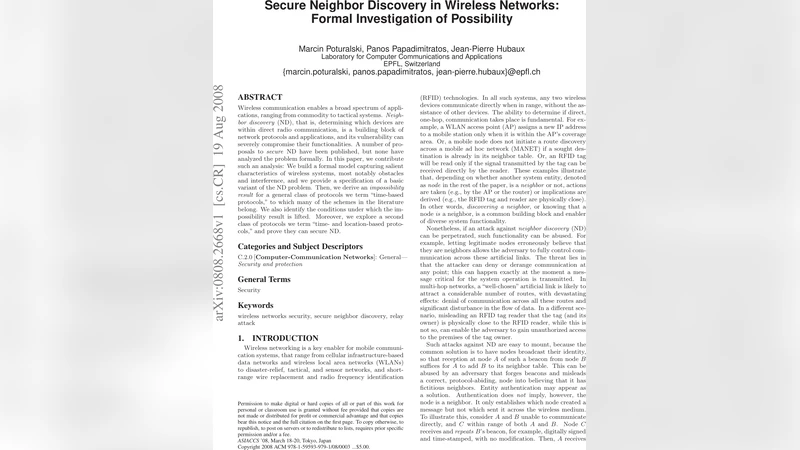
Secure Neighbor Discovery in Wireless Networks: Formal Investigation of Possibility
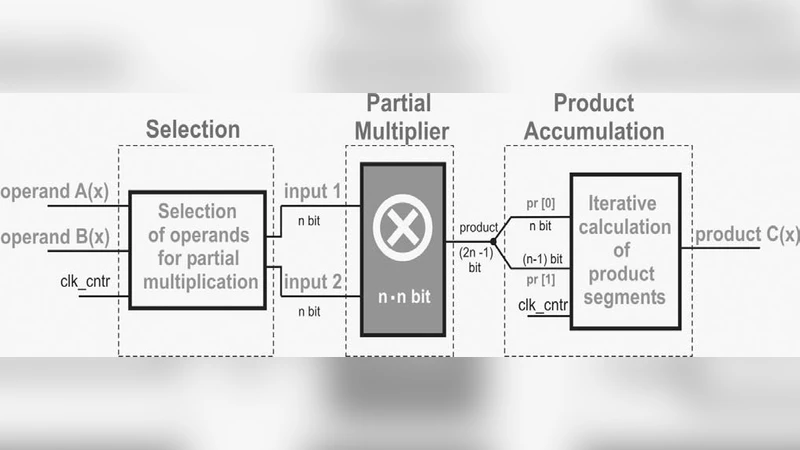
Area Efficient Hardware Implementation of Elliptic Curve Cryptography by Iteratively Applying Karatsubas Method
Jamming in Fixed-Rate Wireless Systems with Power Constraints - Part I: Fast Fading Channels
An extension of Massey scheme for secret sharing
Deterministic Secure Positioning in Wireless Sensor Networks