Cs-Cr

Improved identity-based identification using correcting codes

Biologically Inspired Execution Framework for Vulnerable Workflow Systems
Quantifying Resource Use in Computations
Updating Quantum Cryptography Report ver. 1
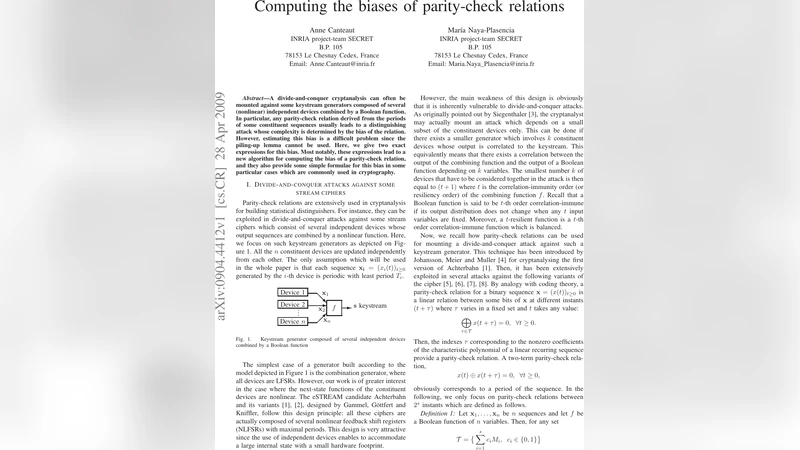
Computing the biases of parity-check relations

A Survey on Cross-Site Scripting Attacks

An Efficient Dynamic and Distributed RSA Accumulator
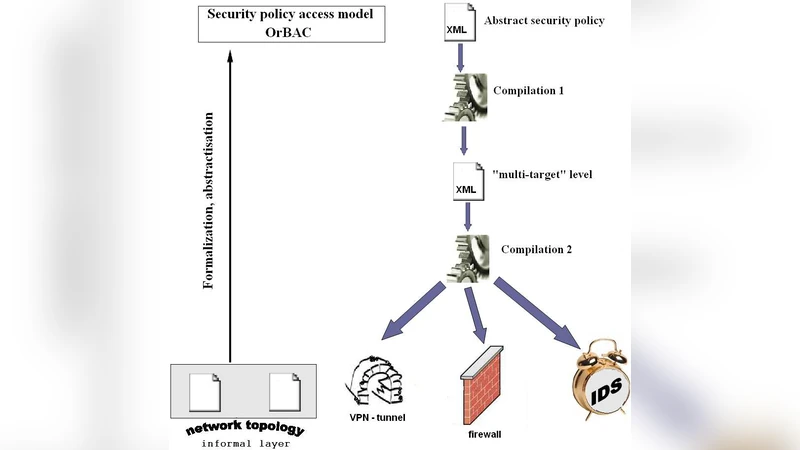
Reliable Process for Security Policy Deployment
Cryptography for Multi-Located Parties

Theoretical framework for constructing matching algorithms in biometric authentication systems

Mathematical and Statistical Opportunities in Cyber Security
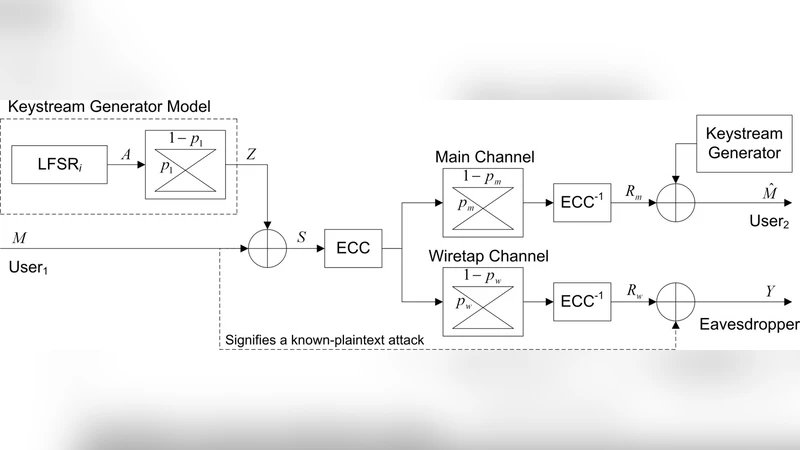
Tandem Coding and Cryptography on Wiretap Channels: EXIT Chart Analysis

Some Proxy Signature and Designated verifier Signature Schemes over Braid Groups

On formal verification of arithmetic-based cryptographic primitives
Watermark Embedding and Detection

Formally Specifying and Proving Operational Aspects of Forensic Lucid in Isabelle

Proxy Signature Scheme with Effective Revocation Using Bilinear Pairings

On Compression of Cryptographic Keys
Role-Based Access Controls

A Dynamic ID-based Remote User Authentication Scheme

A Novel and Efficient Bilateral Remote User Authentication Scheme Using Smart Cards
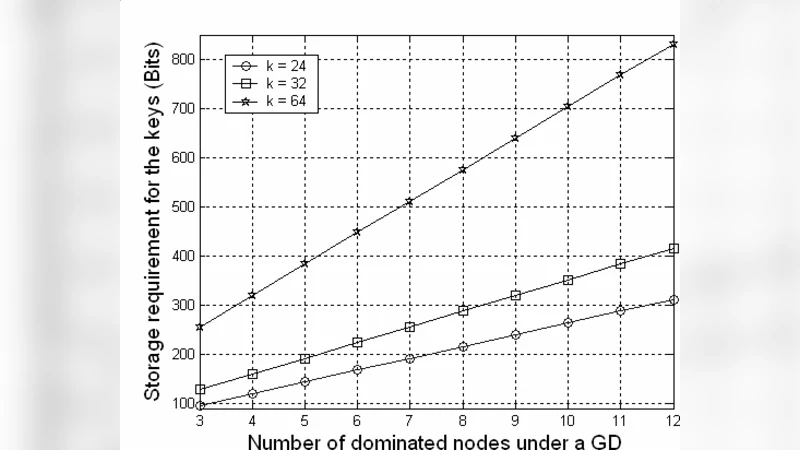
An Efficient PKC-Based Security Architecture for Wireless Sensor Networks
