Cs-Cr
Improved Latin Square based Secret Sharing Scheme

Learning in a Large Function Space: Privacy-Preserving Mechanisms for SVM Learning

A note on conjugacy search and racks
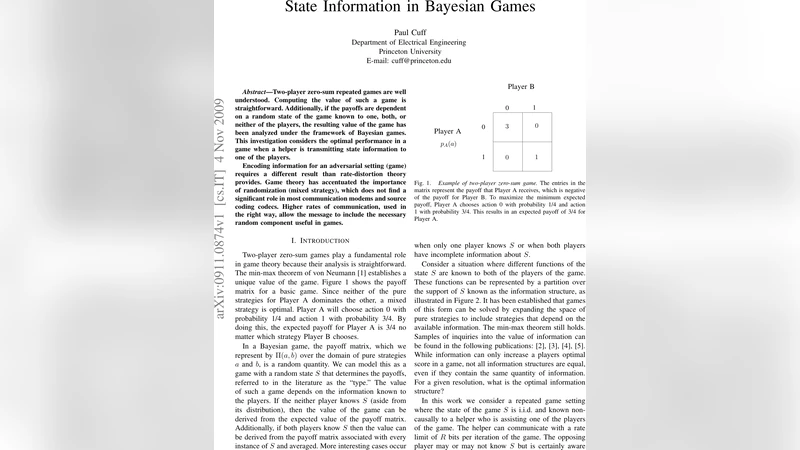
State Information in Bayesian Games

Breaching Euclidean Distance-Preserving Data Perturbation Using Few Known Inputs
A Trust Based Cross Layer Security Protocol for Mobile Ad hoc Networks
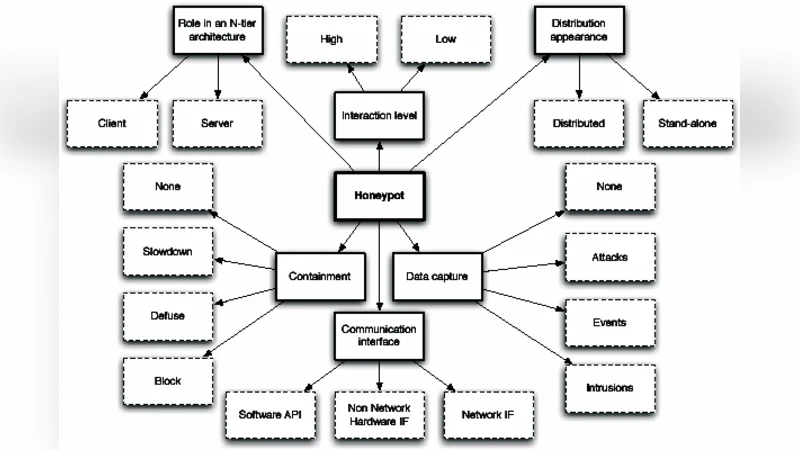
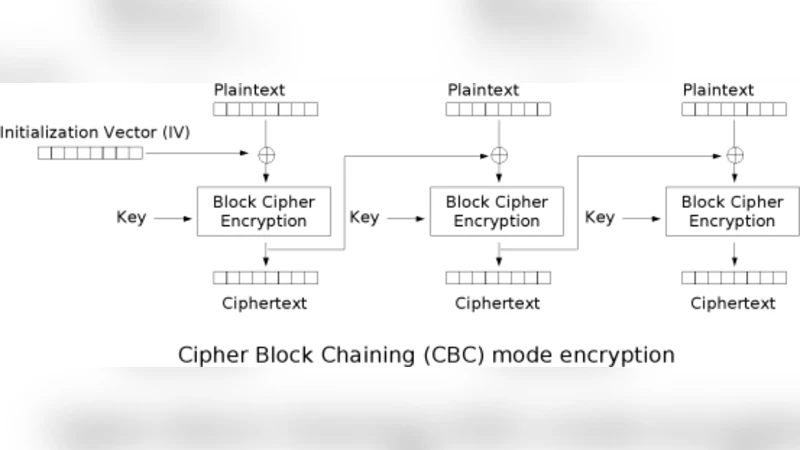
Intrusion Detection System Using Advanced Honeypots

Improved identity-based identification using correcting codes

Biologically Inspired Execution Framework for Vulnerable Workflow Systems
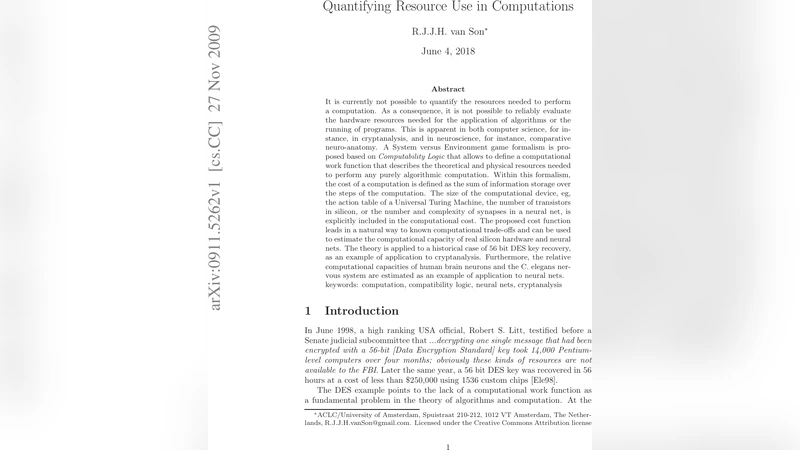
Quantifying Resource Use in Computations
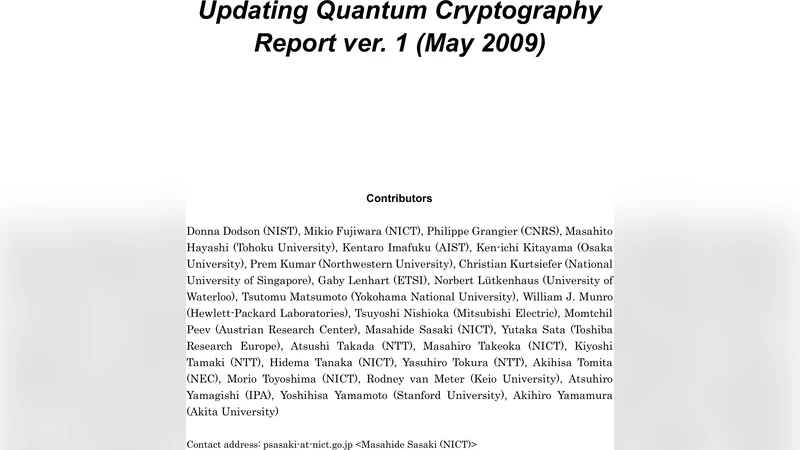
Updating Quantum Cryptography Report ver. 1
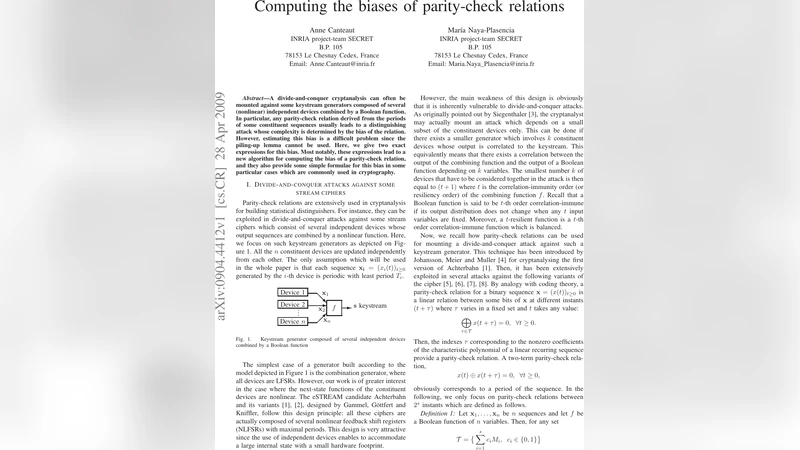
Computing the biases of parity-check relations

A Survey on Cross-Site Scripting Attacks

An Efficient Dynamic and Distributed RSA Accumulator
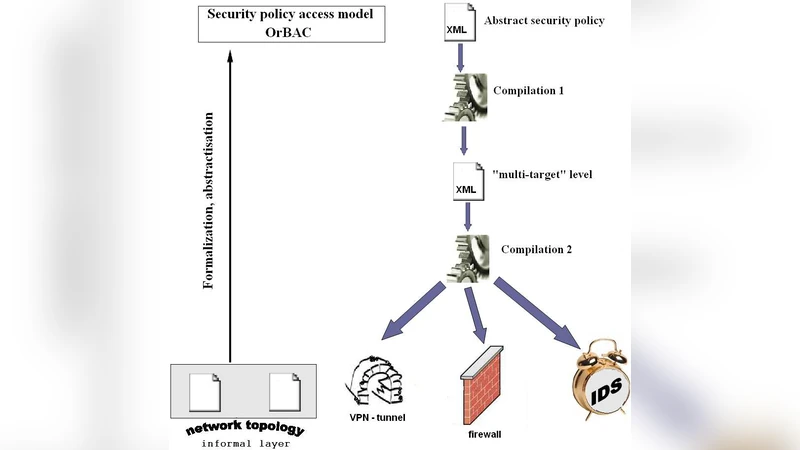
Reliable Process for Security Policy Deployment
Cryptography for Multi-Located Parties

Theoretical framework for constructing matching algorithms in biometric authentication systems

Mathematical and Statistical Opportunities in Cyber Security
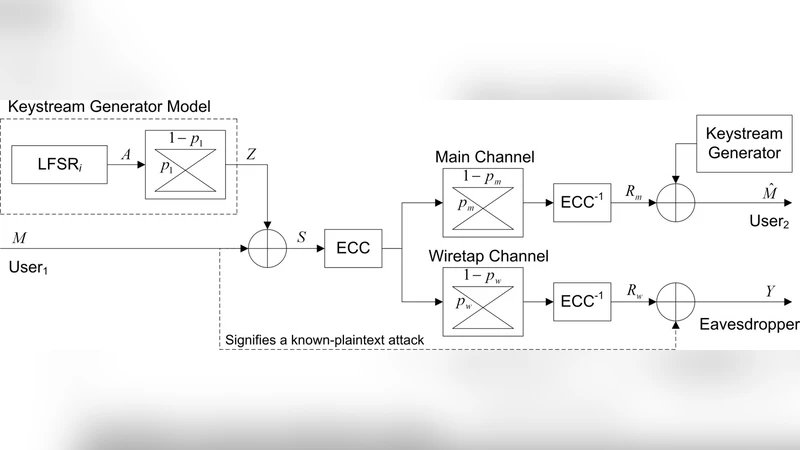
Tandem Coding and Cryptography on Wiretap Channels: EXIT Chart Analysis

Some Proxy Signature and Designated verifier Signature Schemes over Braid Groups

On formal verification of arithmetic-based cryptographic primitives
Watermark Embedding and Detection
