Cs-Cr
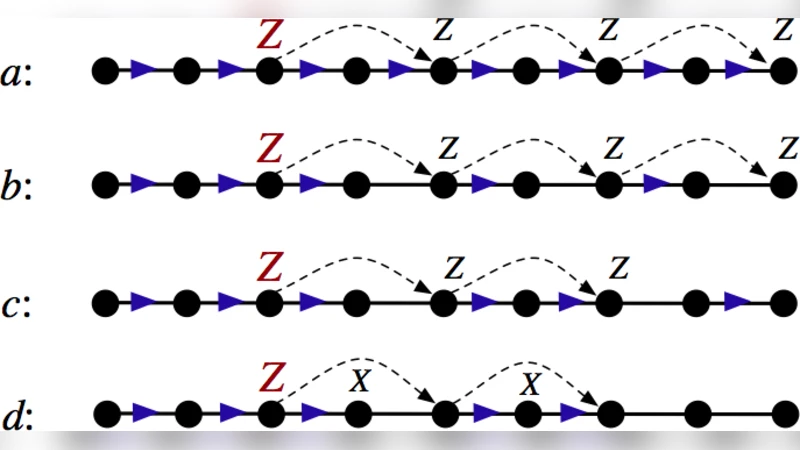
Rossler Nonlinear Dynamical Machine for Cryptography Applications

ODMRP with Quality of Service and local recovery with security Support

An Efficient and Publicly Verifiable Id-Based Multi-Signcryption Scheme

Key Distribution Scheme without Deployment Knowledge
Certificate-based Single Sign-On Mechanism for Multi-Platform Distributed Systems
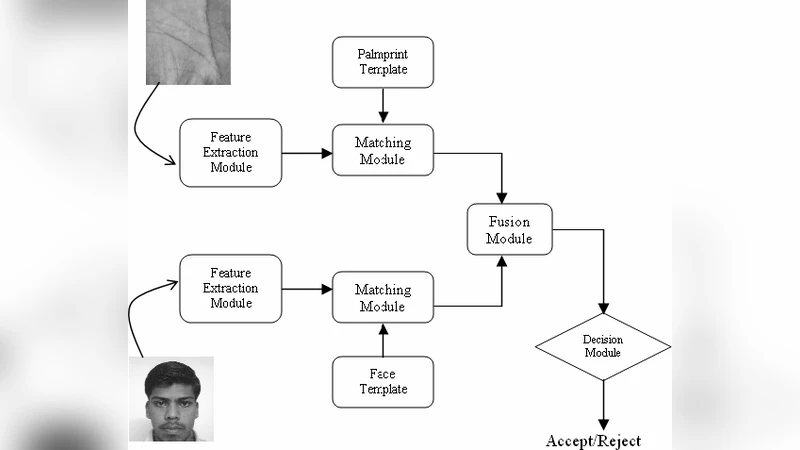
An Efficient Secure Multimodal Biometric Fusion Using Palmprint and Face Image

The monodromy pairing and discrete logarithm on the Jacobian of finite graphs
The SAT solving method as applied to cryptographic analysis of asymmetric ciphers
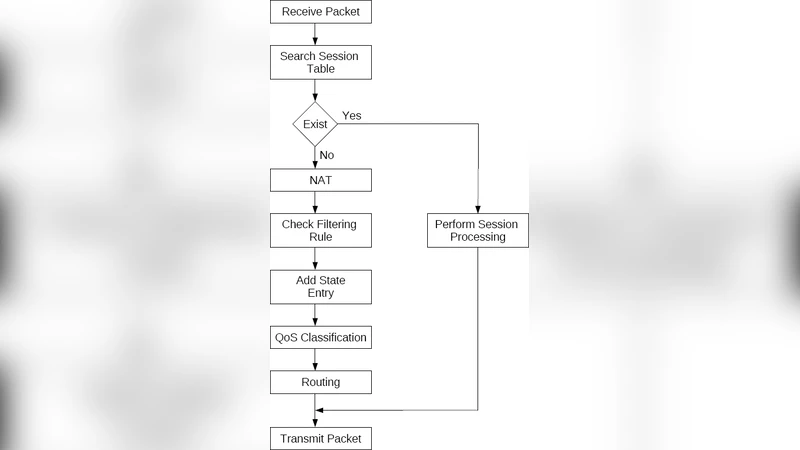
Extending Firewall Session Table to Accelerate NAT, QoS Classification and Routing
PAKE-based mutual HTTP authentication for preventing phishing attacks

Quantifying pervasive authentication: the case of the Hancke-Kuhn protocol
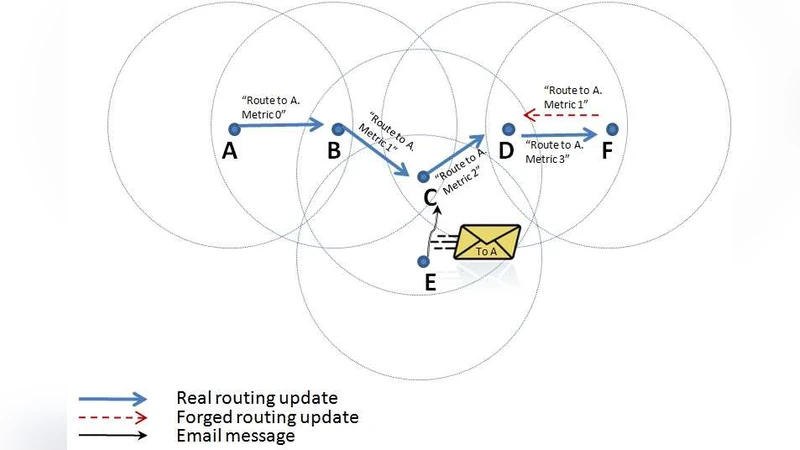
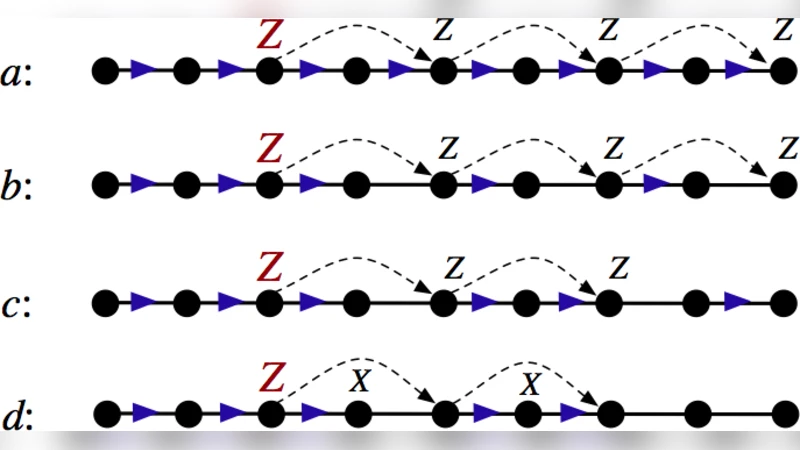
A Secure Wireless Routing Protocol Using Enhanced Chain Signatures

Revisiting Fermats Factorization for the RSA Modulus

Towards Plugging Privacy Leaks in Domain Name System
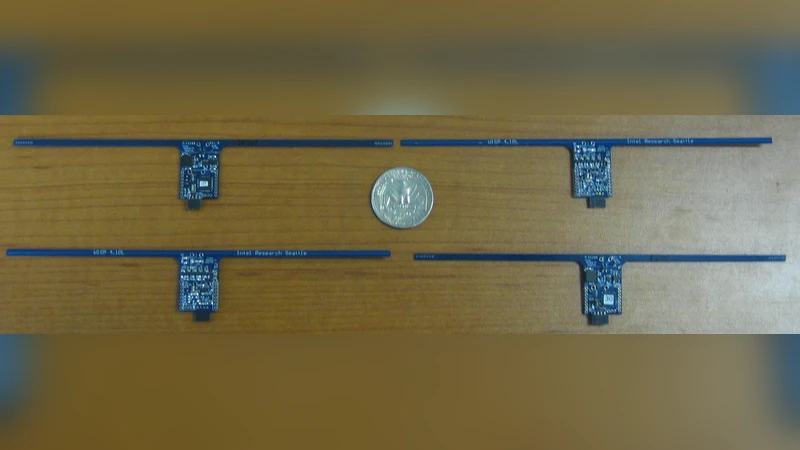
We Can Remember It for You Wholesale: Implications of Data Remanence on the Use of RAM for True Random Number Generation on RFID Tags (RFIDSec 2009)

Fair Exchange in Strand Spaces

Fast Algebraic Attacks and Decomposition of Symmetric Boolean Functions
Improving Integral Cryptanalysis against Rijndael with Large Blocks
Evaluating Trust in Grid Certificates
Information-theoretically Secret Key Generation for Fading Wireless Channels

Stealth-MITM DoS Attacks on Secure Channels
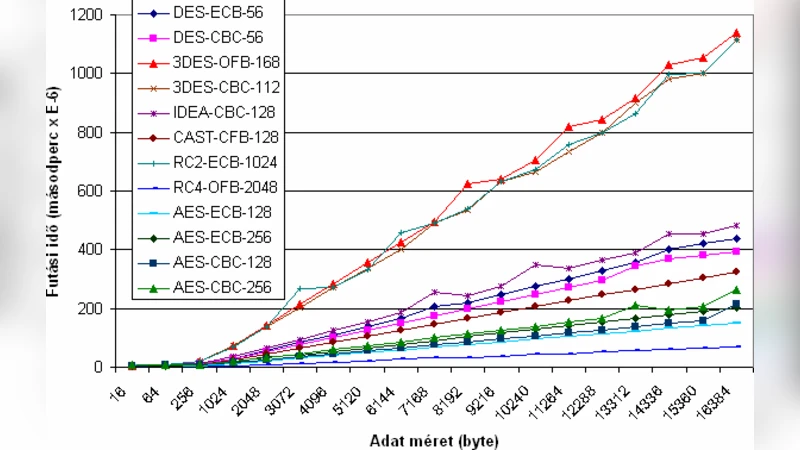
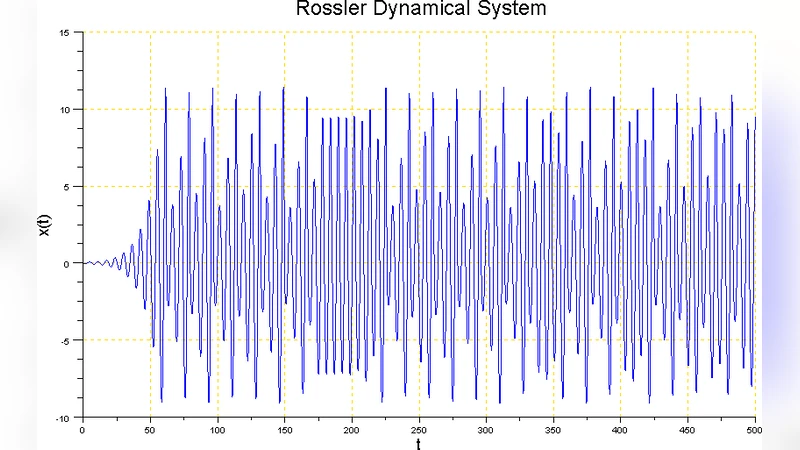
Performance Evaluation of Security Protocols
