
Cs-Cr


Attacking the combination generator
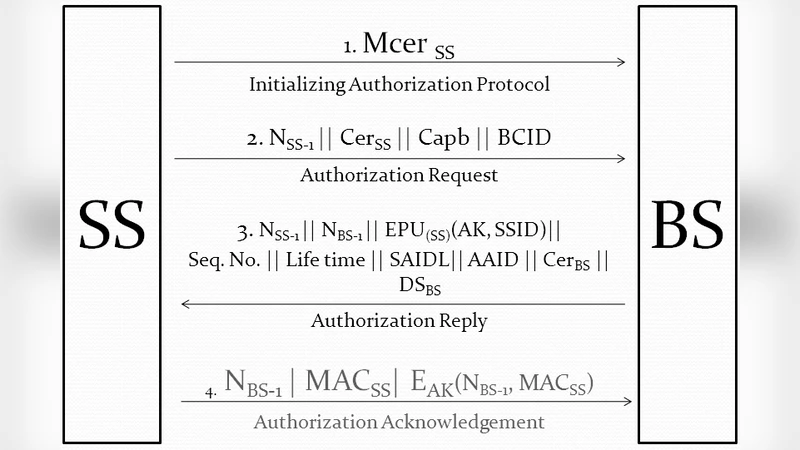
Computational Complexities and Breaches in Authentication Frameworks of Broadband Wireless Access

Philosophical Survey of Passwords
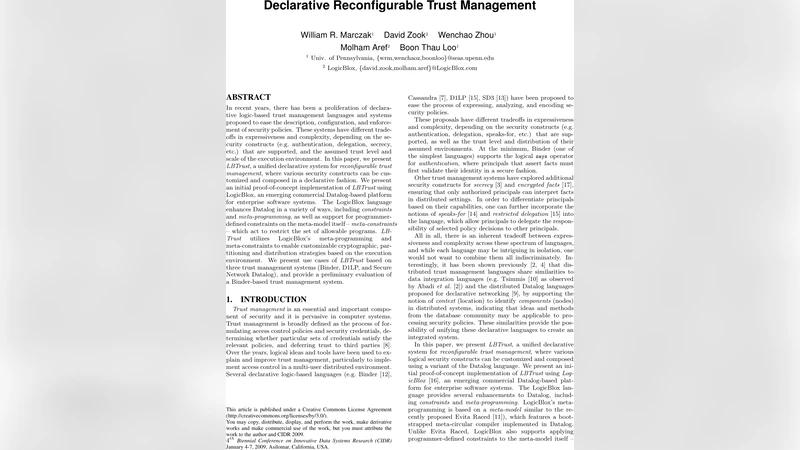
Declarative Reconfigurable Trust Management
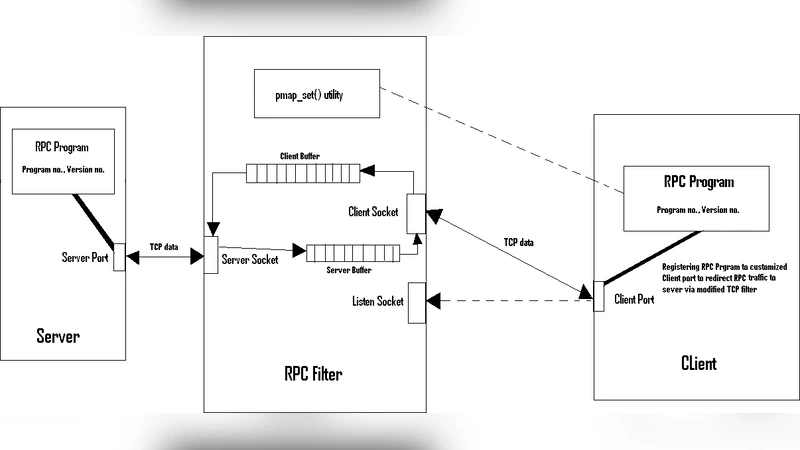
Securing Remote Procedure Calls over HTTPS

Minimizing Cache Timing Attack Using Dynamic Cache Flushing (DCF) Algorithm
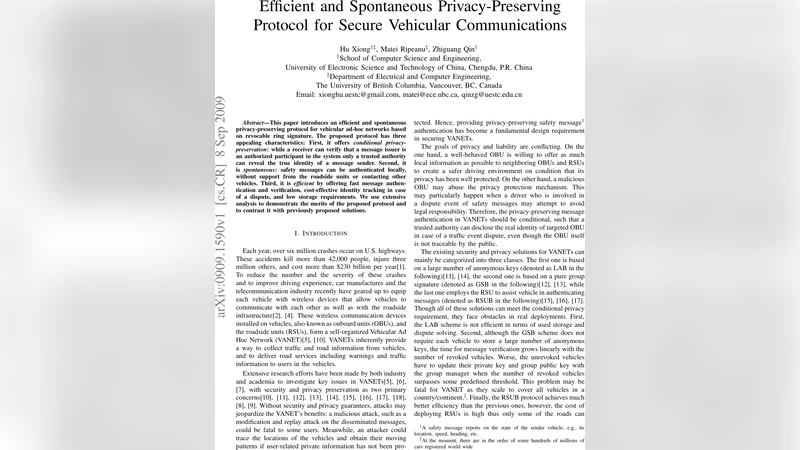
Efficient and Spontaneous Privacy-Preserving Protocol for Secure Vehicular Communications
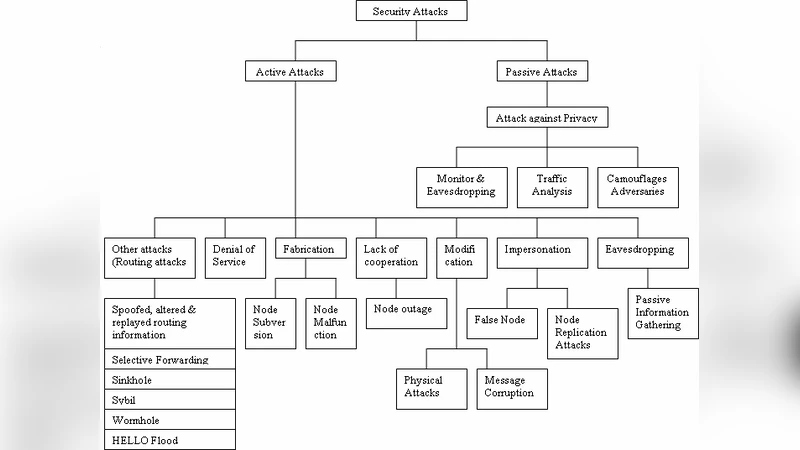
A Survey of Attacks, Security Mechanisms and Challenges in Wireless Sensor Networks
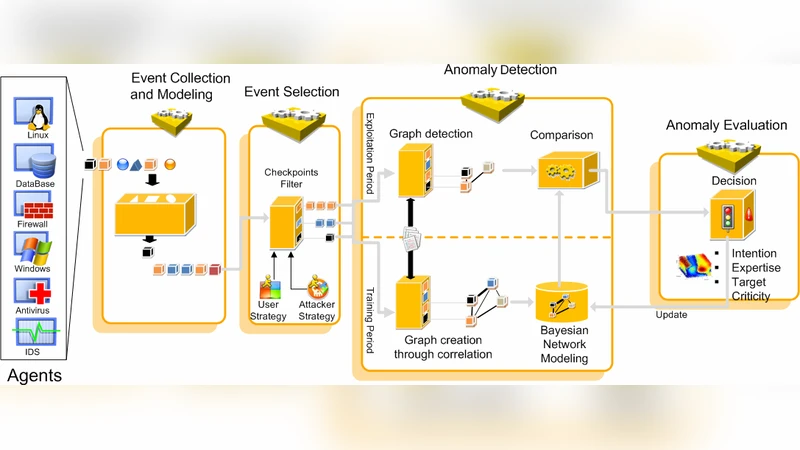
Comprehensive Security Framework for Global Threads Analysis
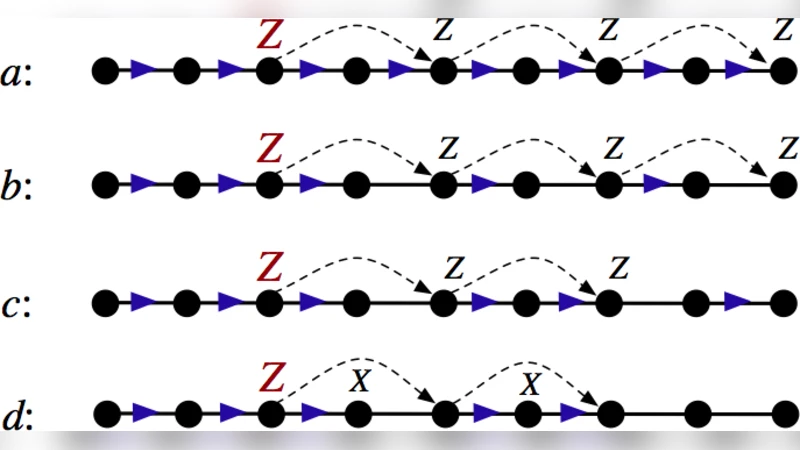
Information Flow in Secret Sharing Protocols
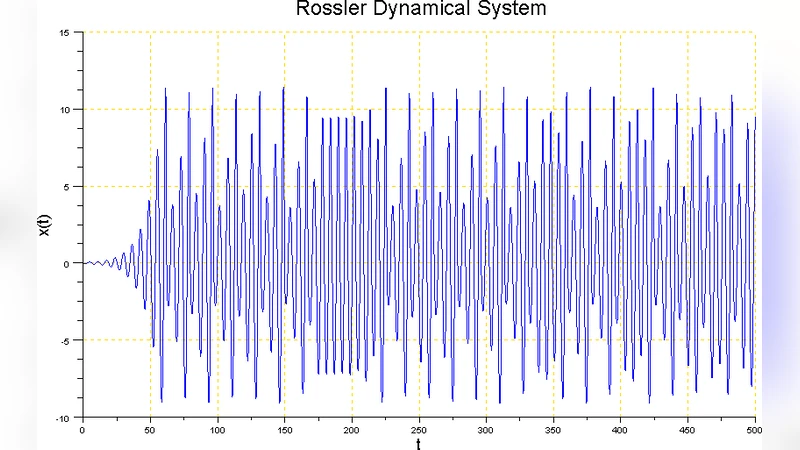
Rossler Nonlinear Dynamical Machine for Cryptography Applications

ODMRP with Quality of Service and local recovery with security Support

An Efficient and Publicly Verifiable Id-Based Multi-Signcryption Scheme

Key Distribution Scheme without Deployment Knowledge
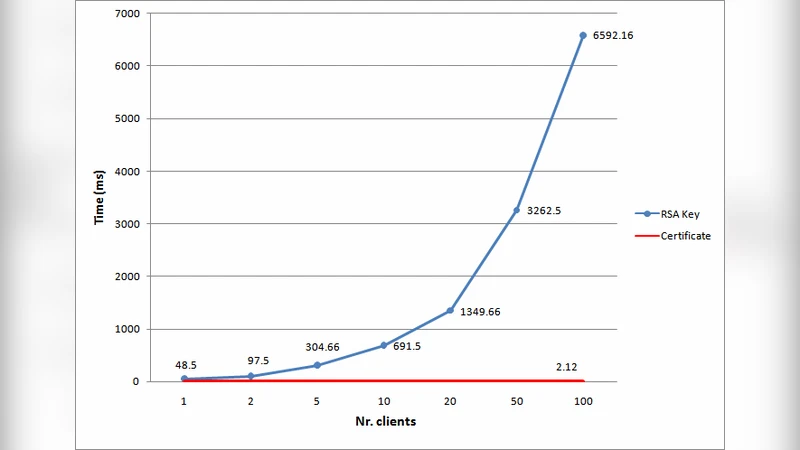
Certificate-based Single Sign-On Mechanism for Multi-Platform Distributed Systems
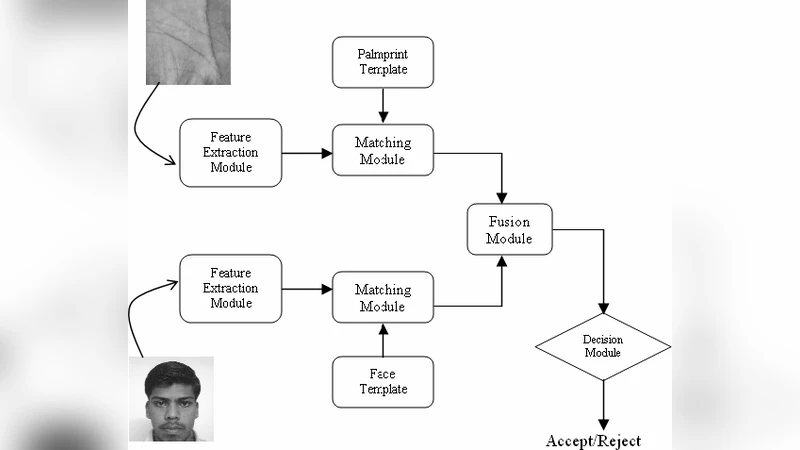
An Efficient Secure Multimodal Biometric Fusion Using Palmprint and Face Image

The monodromy pairing and discrete logarithm on the Jacobian of finite graphs
The SAT solving method as applied to cryptographic analysis of asymmetric ciphers
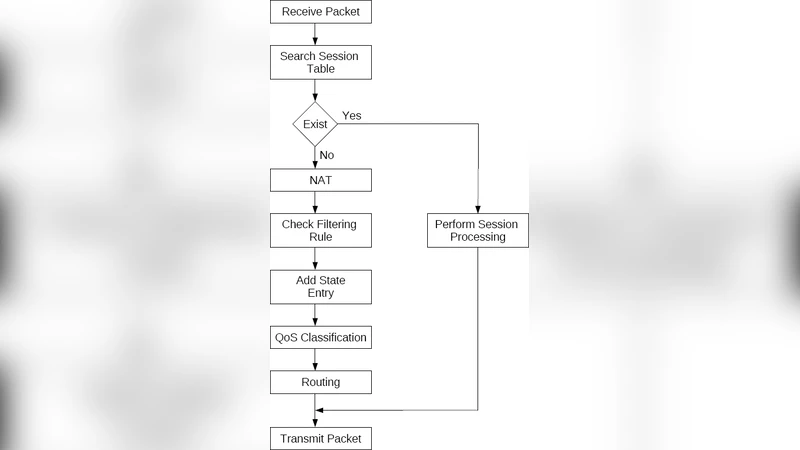
Extending Firewall Session Table to Accelerate NAT, QoS Classification and Routing
PAKE-based mutual HTTP authentication for preventing phishing attacks

Quantifying pervasive authentication: the case of the Hancke-Kuhn protocol
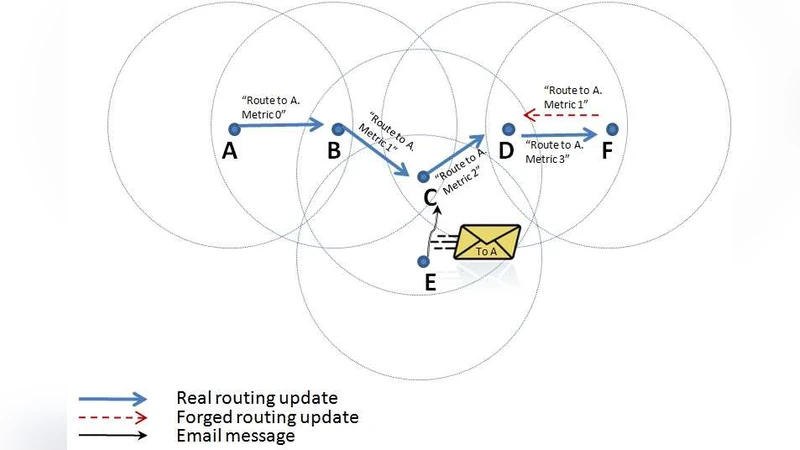
A Secure Wireless Routing Protocol Using Enhanced Chain Signatures
