Cs-Cr
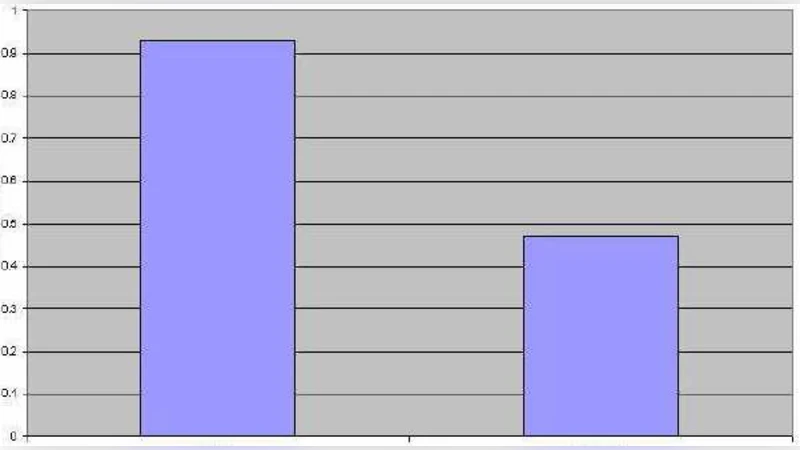
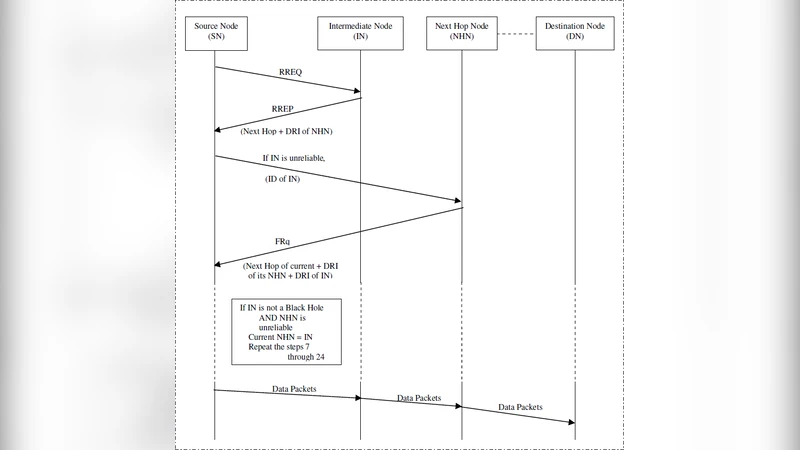
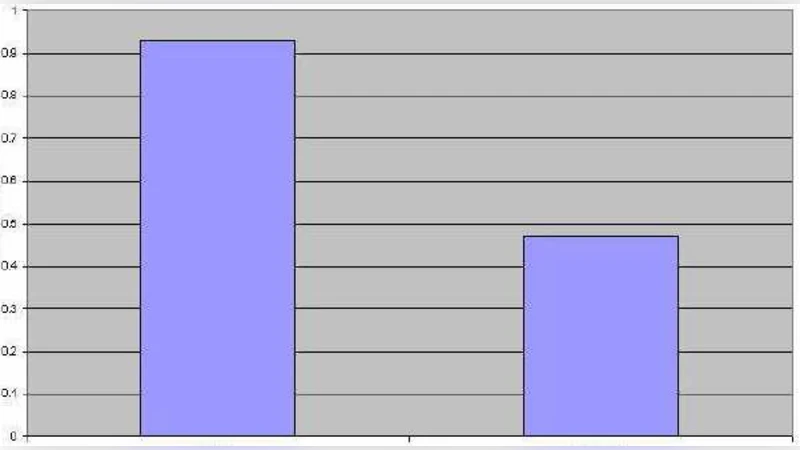
A Mechanism for Detection of Cooperative Black Hole Attack in Mobile Ad Hoc Networks
Information Security Plan for Flight Simulator Applications
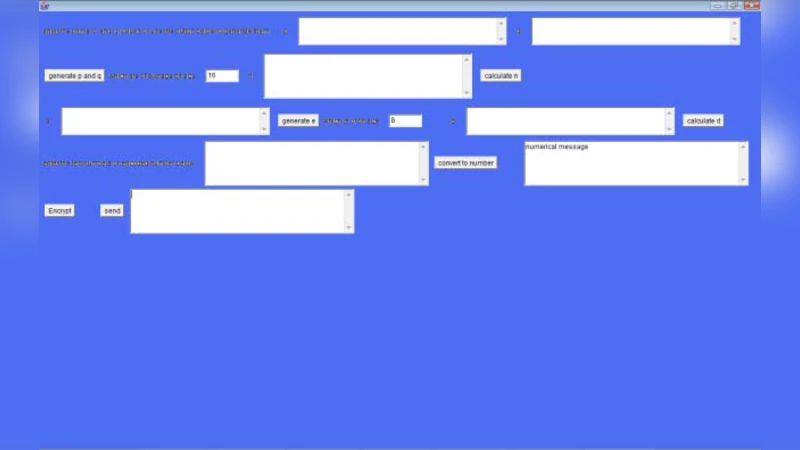
Three Tier Encryption Algorithm For Secure File Transfer

Reversed Space Attacks
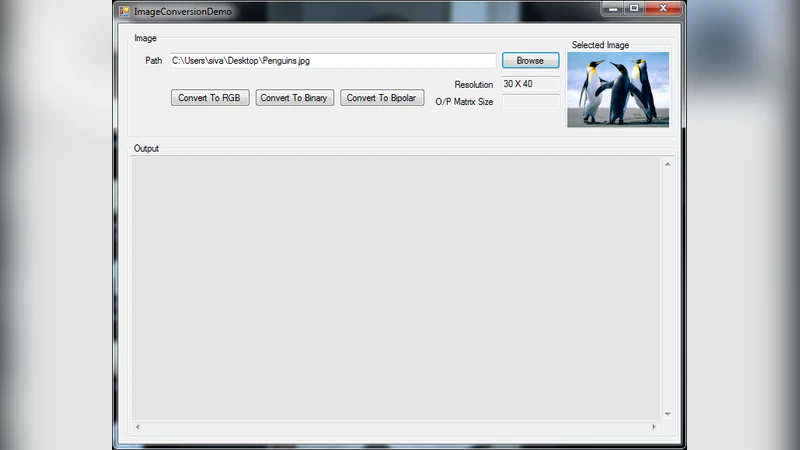
A Novel Approach for Pass Word Authentication using Brain -State -In -A Box (BSB) Model

Constructing and Counting Even-Variable Symmetric Boolean Functions with Algebraic Immunity not Less Than $d$
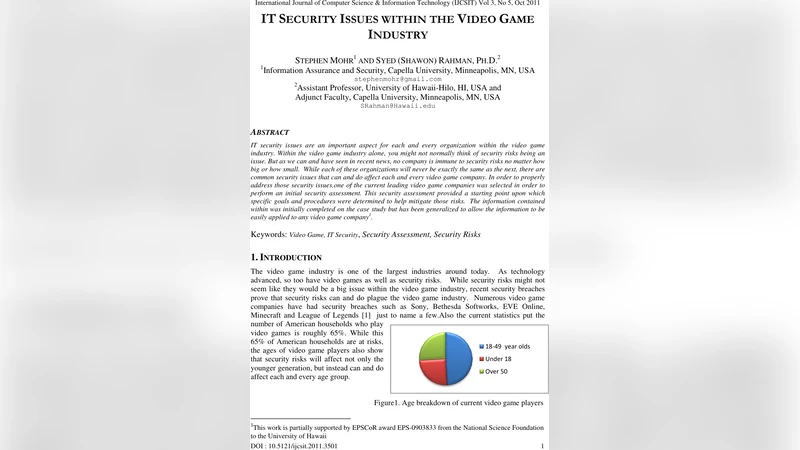
IT Security Issues Within the Video Game Industry

PTaCL: A Language for Attribute-Based Access Control in Open Systems

Formal approaches to information hiding: An analysis of interactive systems, statistical disclosure control, and refinement of specifications
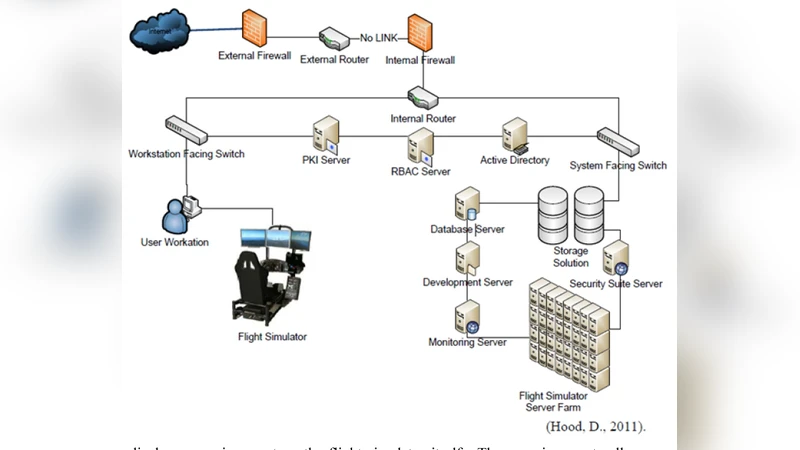
IT Security Plan for Flight Simulation Program
On the Measurement of Privacy as an Attackers Estimation Error
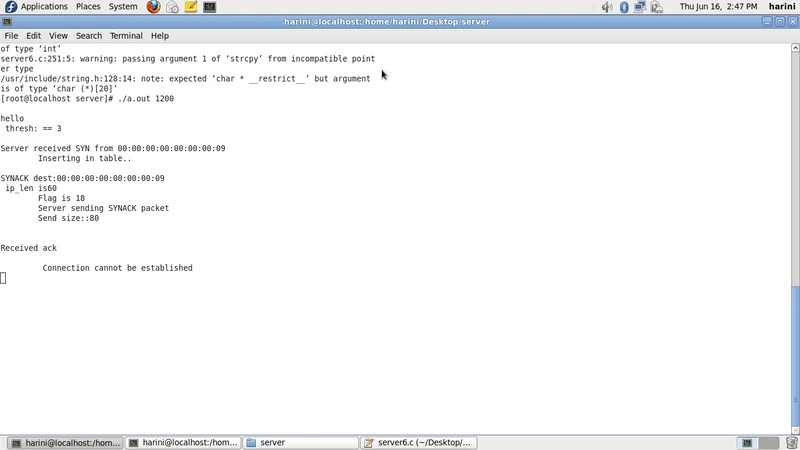
CNoA: Challenging Number Approach for uncovering TCP SYN flooding using SYN spoofing attack
Secure Execution of Distributed Session Programs

Exploring Linkablility of Community Reviewing

A Multi-Factor Security Protocol for Wireless Payment - Secure Web Authentication using Mobile Devices

Fast Private Data Release Algorithms for Sparse Queries

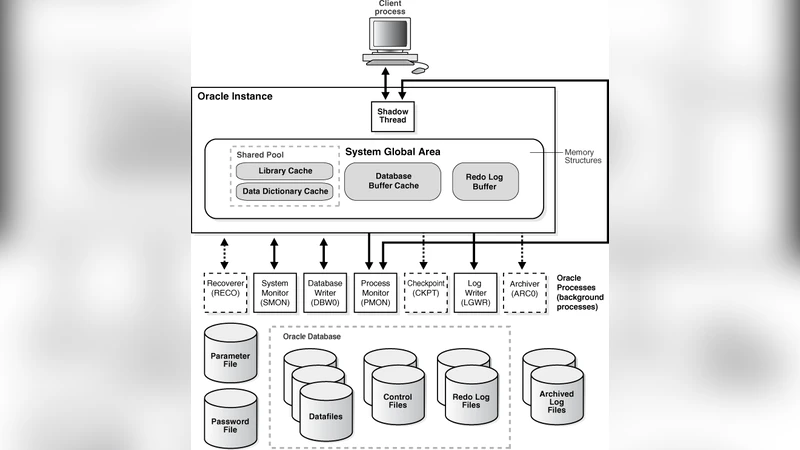
Grid Security and Integration with Minimal Performance Degradation
Universal Secure Multiplex Network Coding with Dependent and Non-Uniform Messages
Mirage: Towards Deployable DDoS Defense for Web Applications

A Novel Elliptic curve cryptography Processor using NoC design
Rotation, Scaling and Translation Analysis of Biometric Signature Templates
ARBAC Policy for a Large Multi-National Bank
