Cs-Cr

AIS for Misbehavior Detection in Wireless Sensor Networks: Performance and Design Principles
Mitigating the ICA Attack against Rotation Based Transformation for Privacy Preserving Clustering
On the Decidability of (ground) Reachability Problems for Cryptographic Protocols (extended version)
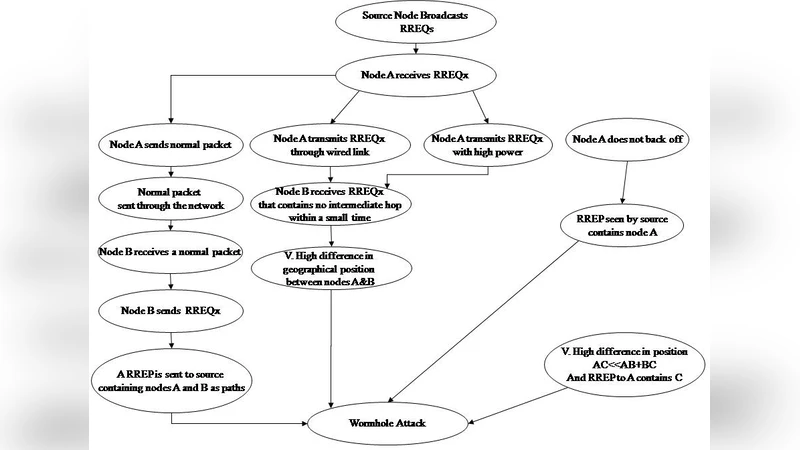
A Full Image of the Wormhole Attacks - Towards Introducing Complex Wormhole Attacks in wireless Ad Hoc Networks

Liberalizing Dependency
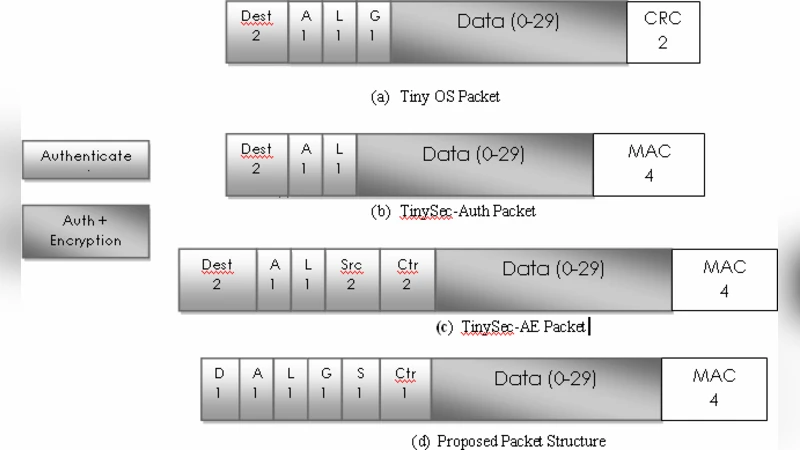
Complete Security Framework for Wireless Sensor Networks

SocialFilter: Collaborative Spam Mitigation using Social Networks

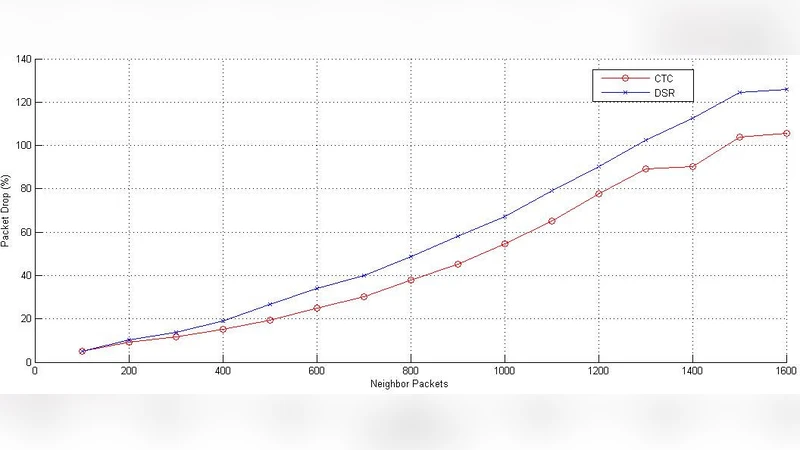
Performance Evaluation of Mesh based Multicast Reactive Routing Protocol under Black Hole Attack
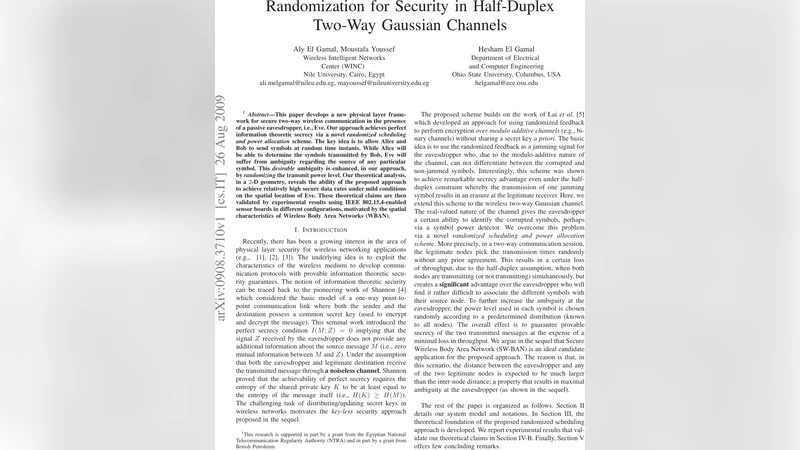
Randomization for Security in Half-Duplex Two-Way Gaussian Channels
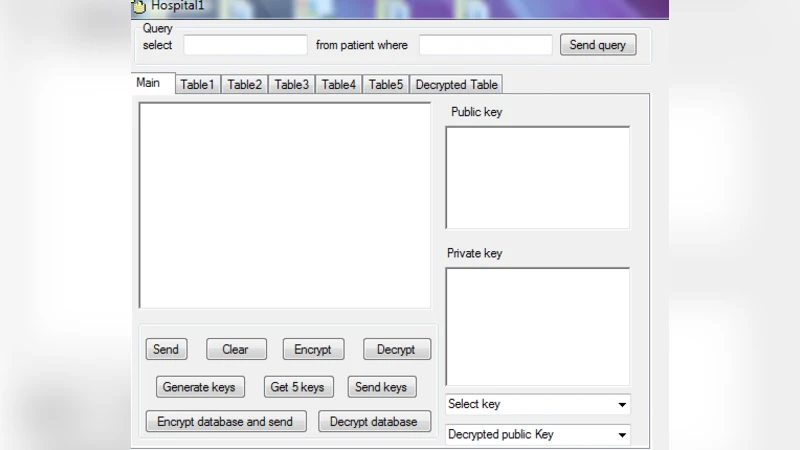
Preserving Privacy and Sharing the Data in Distributed Environment using Cryptographic Technique on Perturbed data
Space Efficient Secret Sharing: A Recursive Approach

An Algebraic Watchdog for Wireless Network Coding
Identification with Encrypted Biometric Data

Towards a Theory of Anonymous Networking
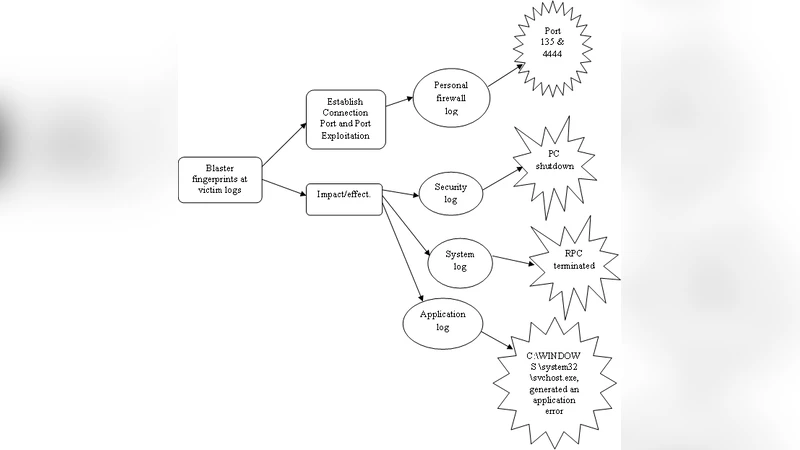
Tracing Technique for Blaster Attack

A Trace Based Bisimulation for the Spi Calculus
A New Scheme for Minimizing Malicious Behavior of Mobile Nodes in Mobile Ad Hoc Networks
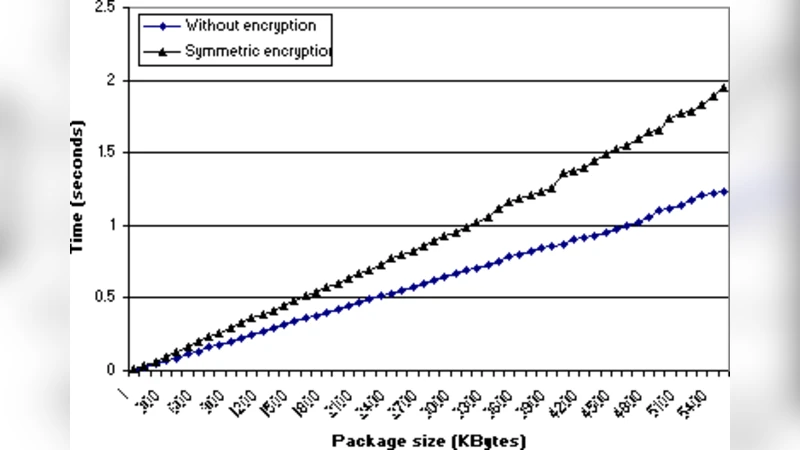
Extending WS-Security to Implement Security Protocols for Web Services
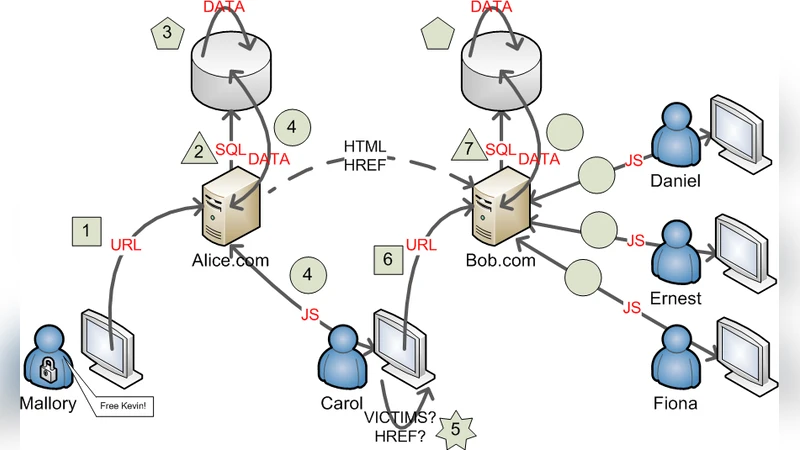
SQL/JavaScript Hybrid Worms As Two-stage Quines
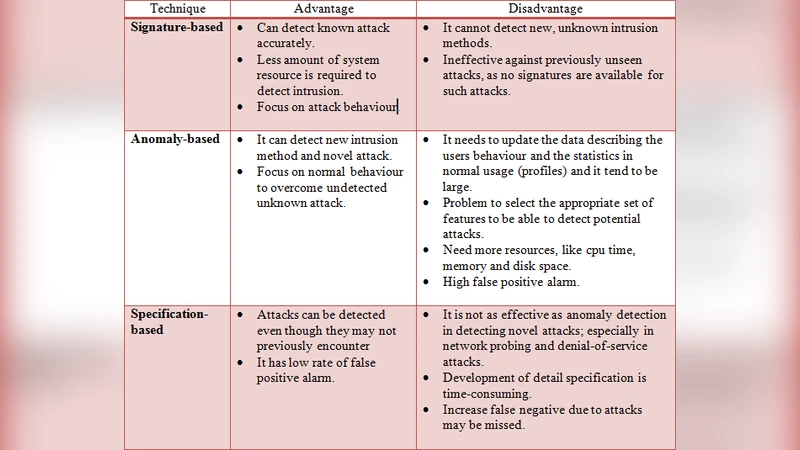
A New Generic Taxonomy on Hybrid Malware Detection Technique

Pairings on hyperelliptic curves

Informal specification-based performance evaluation of security protocols
