Cs-Cr

Braid Group Cryptography
Condition for Energy Efficient Watermarking with Random Vector Model without WSS Assumption
Multiple-Input Multiple-Output Gaussian Broadcast Channels with Confidential Messages
On the Delay Limited Secrecy Capacity of Fading Channels
Refuting the Pseudo Attack on the REESSE1+ Cryptosystem

Studying Maximum Information Leakage Using Karush-Kuhn-Tucker Conditions
The discrete logarithm problem in the group of non-singular circulant matrices
The Minimal Polynomial over F_q of Linear Recurring Sequence over F_{q^m}

Quantum money from knots

Composability in quantum cryptography
Examples of the Generalized Quantum Permanent Compromise Attack to the Blum-Micali Construction

Statistical Analysis of Privacy and Anonymity Guarantees in Randomized Security Protocol Implementations
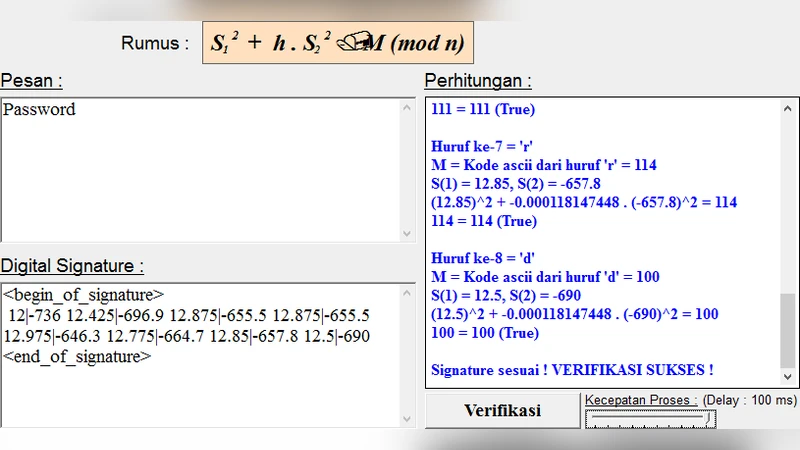
Digital Signature Security in Data Communication

Public Key Protocol Based on Amalgamated Free Product
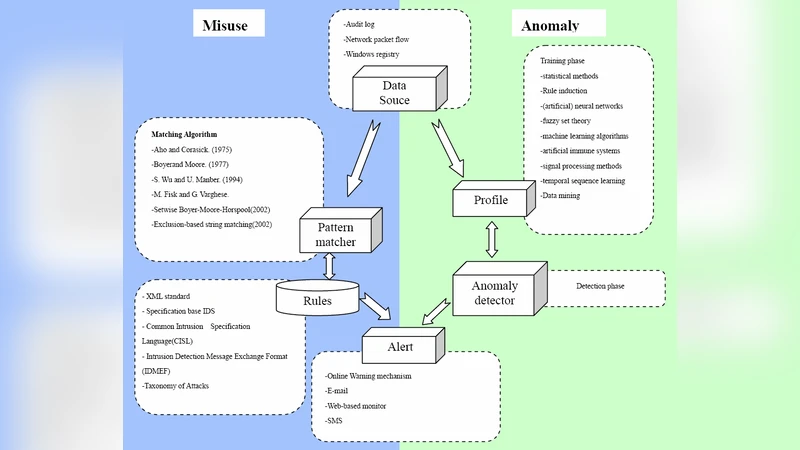
Using Rough Set and Support Vector Machine for Network Intrusion Detection

Intrusion-aware Alert Validation Algorithm for Cooperative Distributed Intrusion Detection Schemes of Wireless Sensor Networks

Secret-Key Generation using Correlated Sources and Channels

Secure Vehicular Communication Systems: Design and Architecture

Defense Strategies Against Modern Botnets
Unconditional security from noisy quantum storage

AIS for Misbehavior Detection in Wireless Sensor Networks: Performance and Design Principles
Mitigating the ICA Attack against Rotation Based Transformation for Privacy Preserving Clustering