Cs-Cr
FedSecureFormer: A Fast, Federated and Secure Transformer Framework for Lightweight Intrusion Detection in Connected and Autonomous Vehicles
FAST-IDS: A Fast Two-Stage Intrusion Detection System with Hybrid Compression for Real-Time Threat Detection in Connected and Autonomous Vehicles
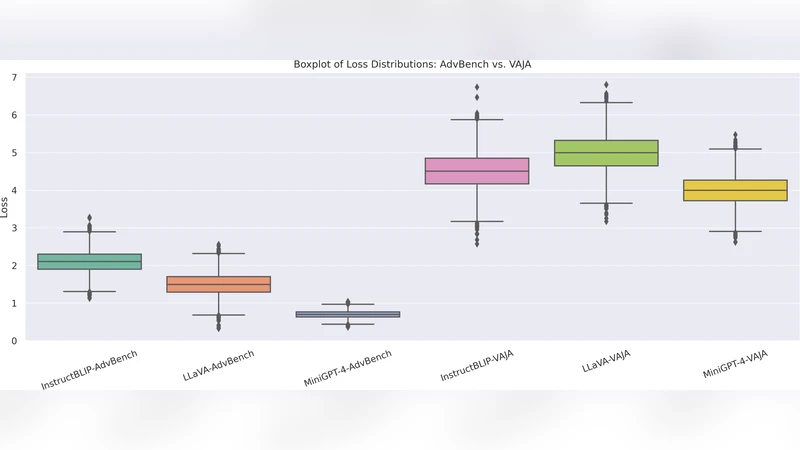
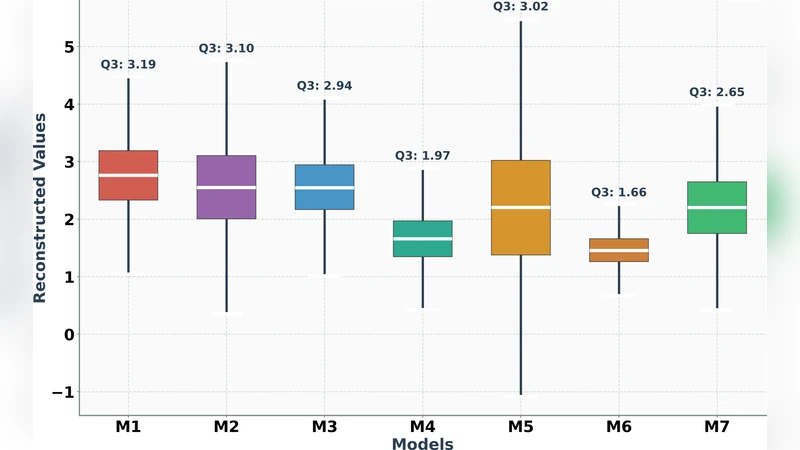
Crafting Adversarial Inputs for Large Vision-Language Models Using Black-Box Optimization
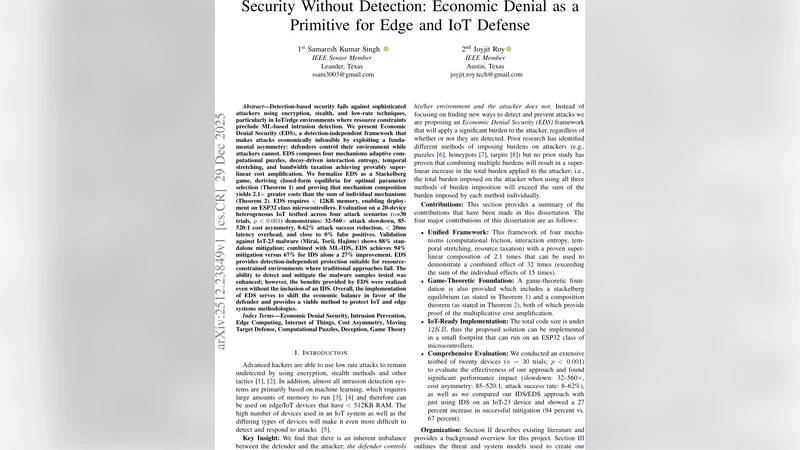
Security Without Detection: Economic Denial as a Primitive for Edge and IoT Defense
Towards Shift Tolerant Visual Secret Sharing Schemes

Fingerprinting with Minimum Distance Decoding

Modelling Nonlinear Sequence Generators in terms of Linear Cellular Automata

JConstHide: A Framework for Java Source Code Constant Hiding
Semi-Trusted Mixer Based Privacy Preserving Distributed Data Mining for Resource Constrained Devices
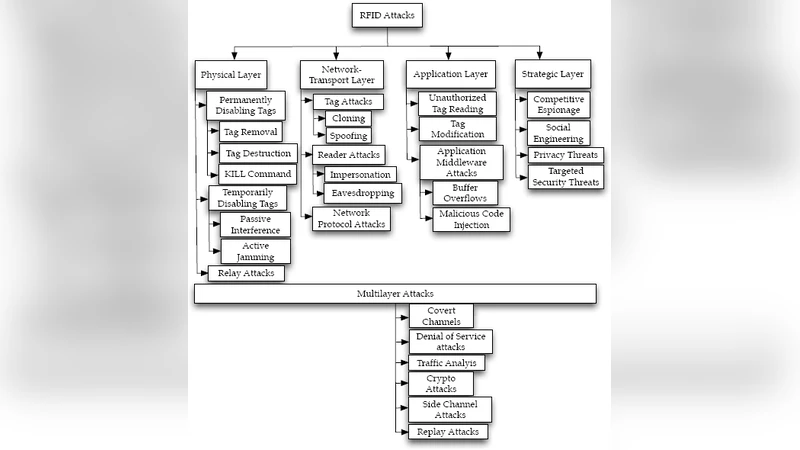
Lightweight Mutual Authentication Protocol for Low Cost RFID Tags
C-sanitized: a privacy model for document redaction and sanitization
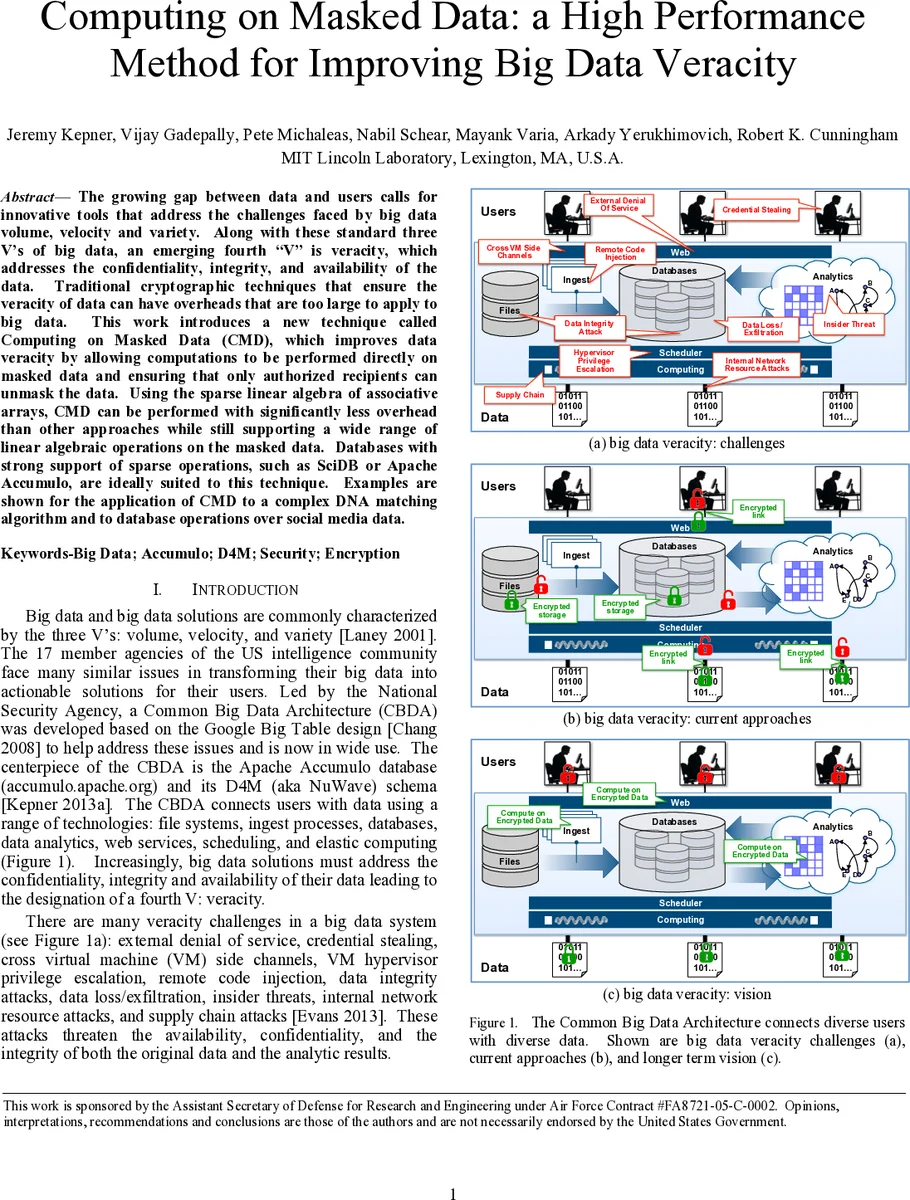
Computing on Masked Data: a High Performance Method for Improving Big Data Veracity
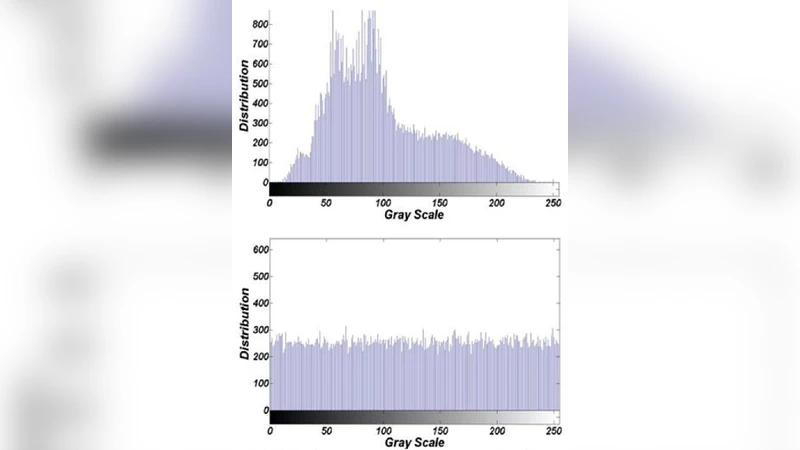
Chaotic trigonometric Haar wavelet with focus on image encryption

On the Boundaries of Trust and Security in Computing and Communications Systems

Near-Optimal Blacklisting

Non linearite des fonctions booleennes donnees par des traces de polyn^omes de degre binaire 3
Privacy-Preserving Protocols for Eigenvector Computation

Pan-private Algorithms: When Memory Does Not Help

Discrete logarithms in curves over finite fields

Constructions of Almost Optimal Resilient Boolean Functions on Large Even Number of Variables
Construction of Codes for Wiretap Channel and Secret Key Agreement from Correlated Source Outputs by Using Sparse Matrices

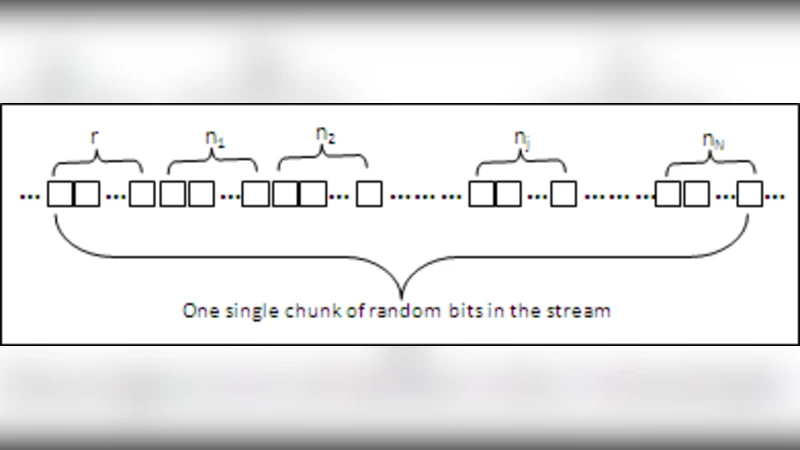
A DHT Based Measure of Randomness