Cs-Cr


Investigating the Distribution of Password Choices

A Weakest Chain Approach to Assessing the Overall Effectiveness of the 802.11 Wireless Network Security
Group ring cryptography

Anonymous Gossiping

Trust beyond reputation: A computational trust model based on stereotypes
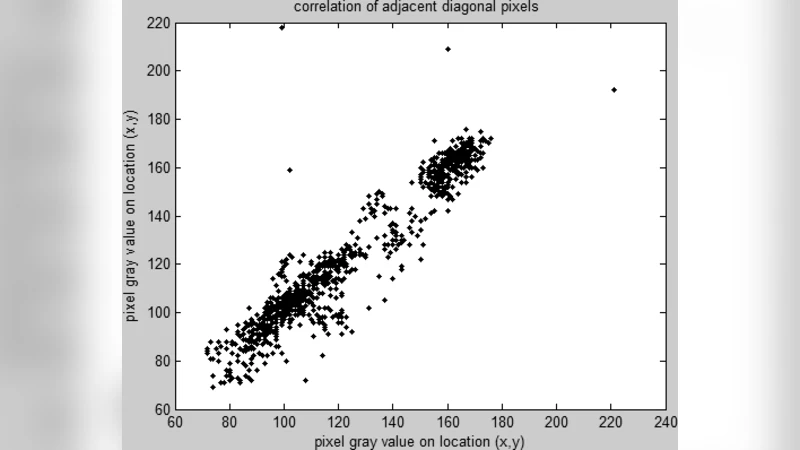
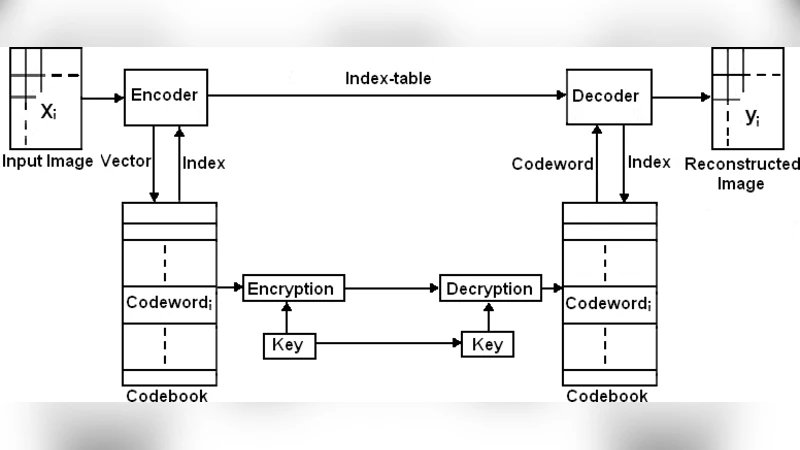
Image Encryption Based on Diffusion and Multiple Chaotic Maps

Universally Attainable Error and Information Exponents, and Equivocation Rate for the Broadcast Channels with Confidential Messages
Algorithms that Remember: Model Inversion Attacks and Data Protection Law
A Survey of Distributed Certificate Authorities in MANETs

Linear Relation on General Ergodic T-Function

Almost-perfect secret sharing
Key Management in Mobile Sensor Networks

Secret Key Generation from Channel Noise with the Help of a Common Key

SIG-DB: leveraging homomorphic encryption to Securely Interrogate privately held Genomic DataBases
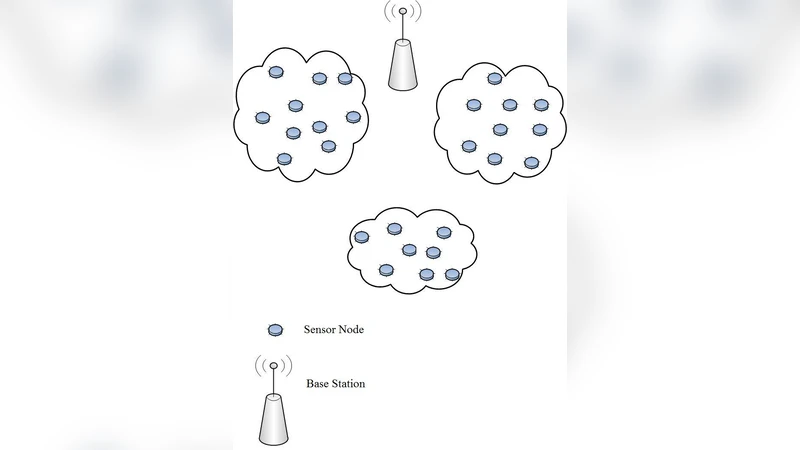
Malware detection techniques for mobile devices
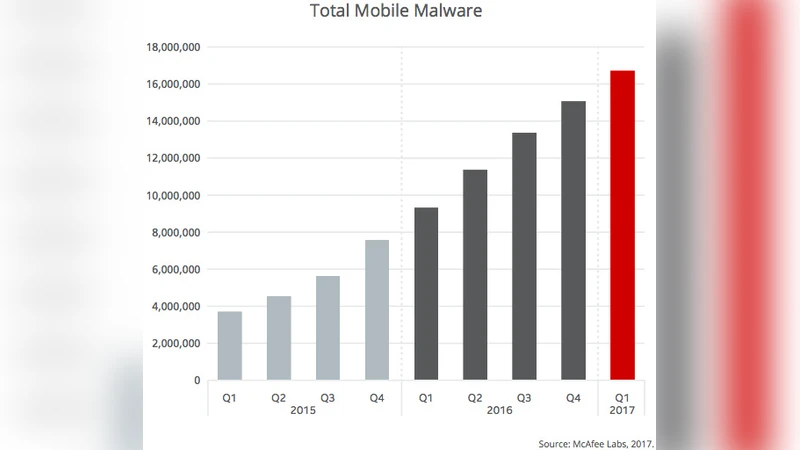
Information Security in Health Care Centre Using Cryptography and Steganography
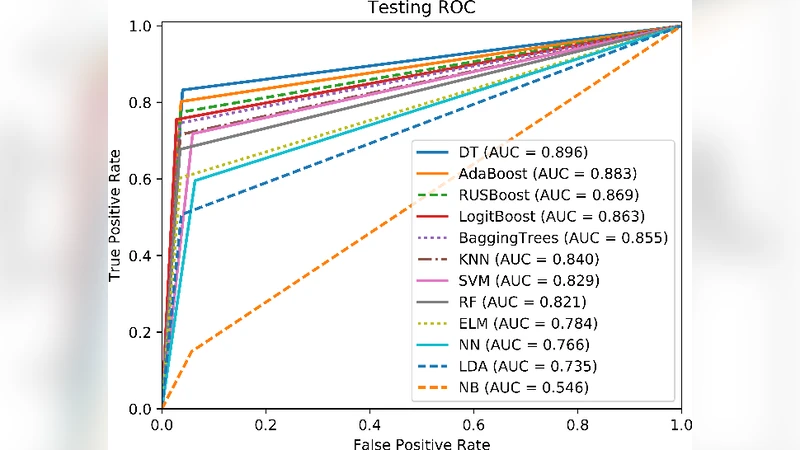
Towards an Efficient Anomaly-Based Intrusion Detection for Software-Defined Networks
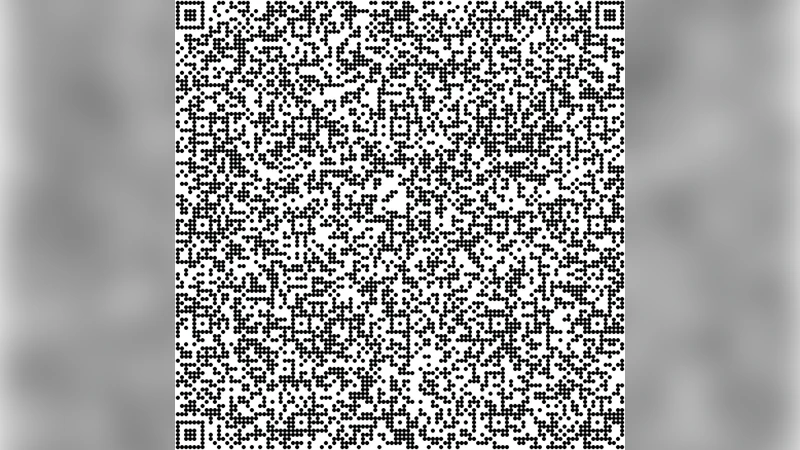
Confidential Encrypted Data Hiding and Retrieval Using QR Authentication System
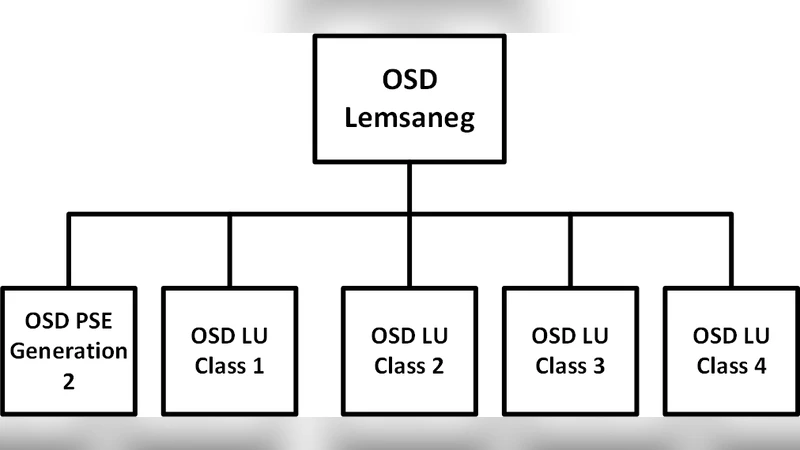
Evaluating Certificate Policy - Certification Practice Statement of Unique Government Certification Authority using Public Key Infrastructure Assessment Guidelines: Research in Progress
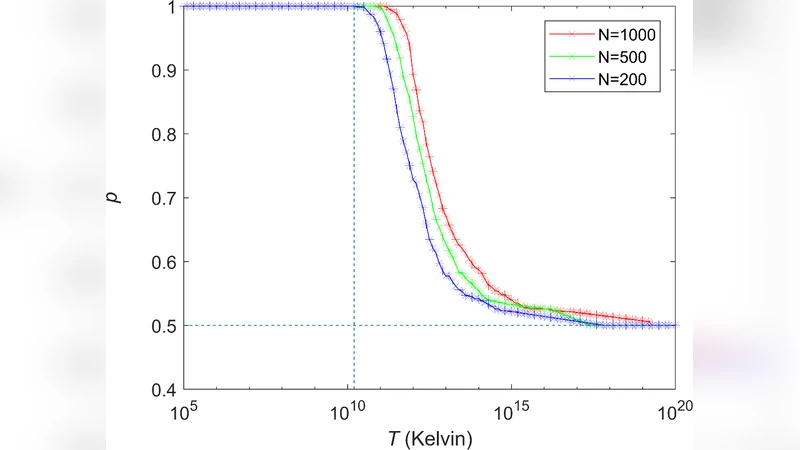
A Static-Loop-Current Attack against the KLJN Secure Key Exchange System

Protecting User Privacy Based on Secret Sharing with Error Tolerance for Big Data in Smart Grid
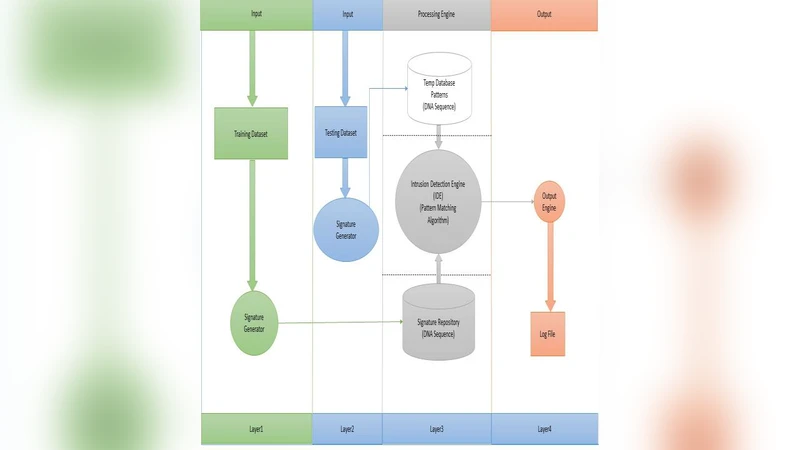
A Lightweight Signature-Based IDS for IoT Environment