Cs-Cr

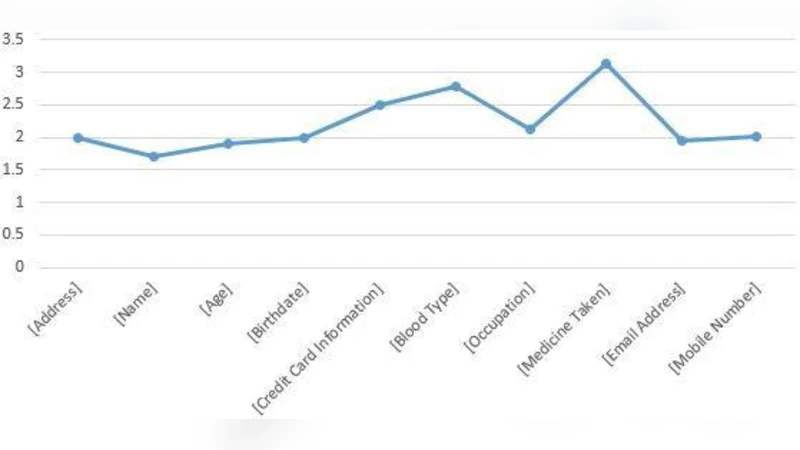
A model for system developers to measure the privacy risk of data
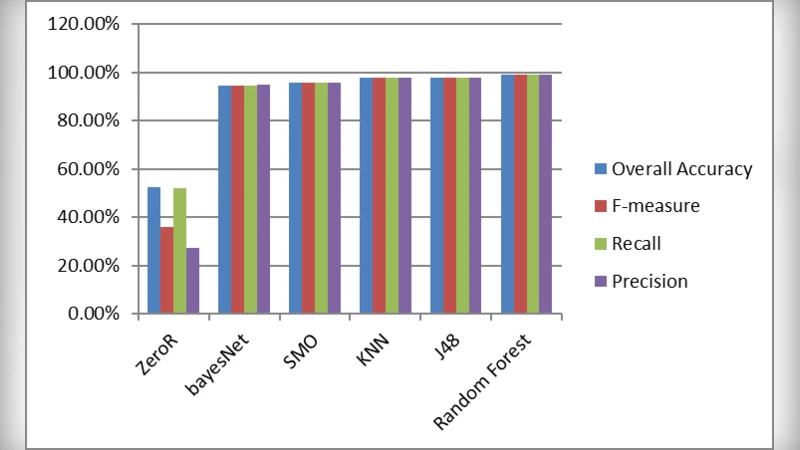
Classification of malware based on file content and characteristics
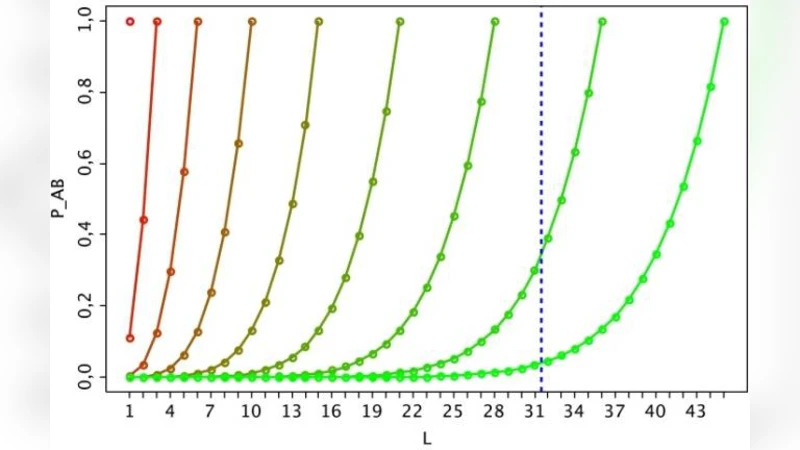
Using a Secret Key to Foil an Eavesdropper
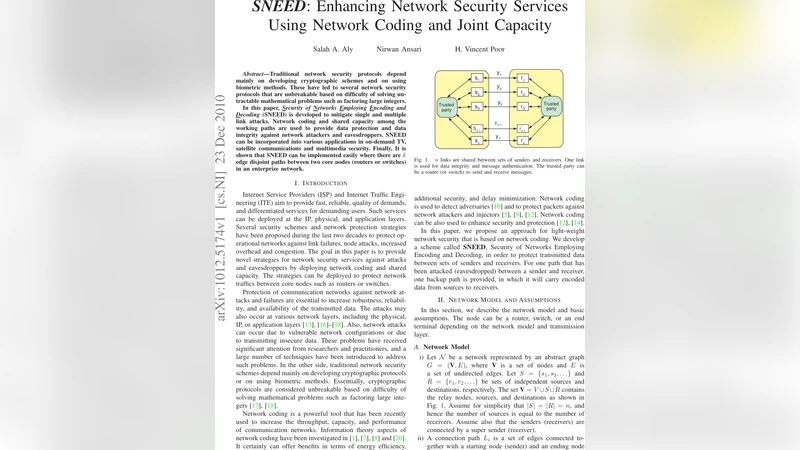
SNEED: Enhancing Network Security Services Using Network Coding and Joint Capacity
Evidence Based Decision Making in Blockchain Economic Systems: From Theory to Practice
Smart False Data Injection attacks against State Estimation in Power Grid
Software-Defined Radio GNSS Instrumentation for Spoofing Mitigation: A Review and a Case Study
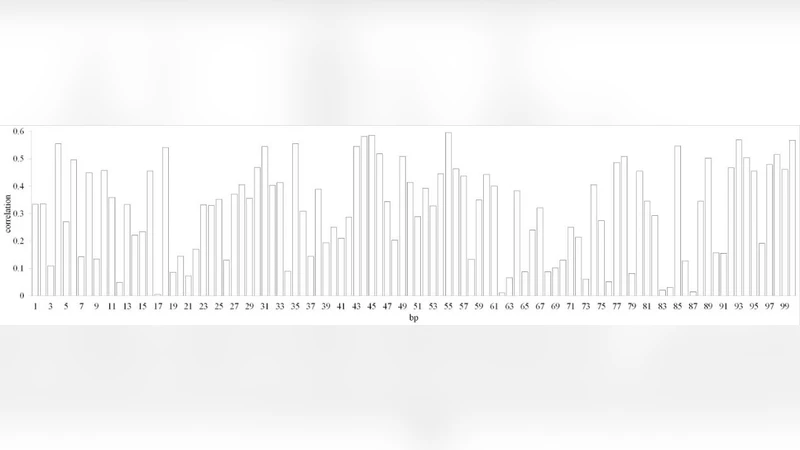
Prediction of Signal Sequences in Abiotic Stress Inducible Genes from Main Crops by Association Rule Mining

The New Threats of Information Hiding: the Road Ahead

Spatio-temporal Trajectory Dataset Privacy Based on Network Traffic Control
Building Computer Network Attacks
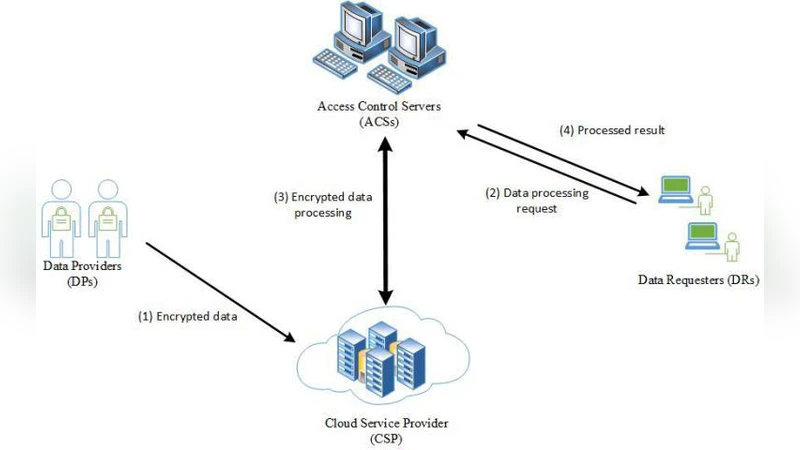
Secure outsourced calculations with homomorphic encryption

A Secure RFID Deactivation/Activation Mechanism for Supporting Customer Service and Consumer Shopping
A Rolling Blockchain for a Dynamic WSNs in a Smart City
A Taxonomy to Assess and Tailor Risk-based Testing in Recent Testing Standards
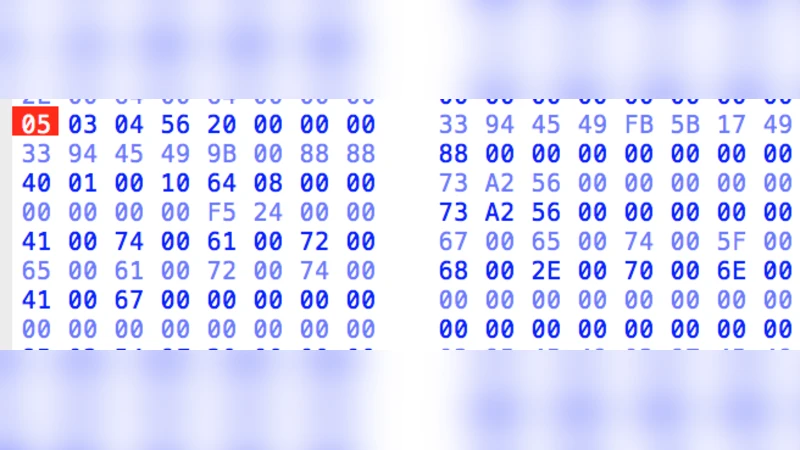
Forensic Analysis of the exFAT artefacts

Improving random number generators by chaotic iterations. Application in data hiding
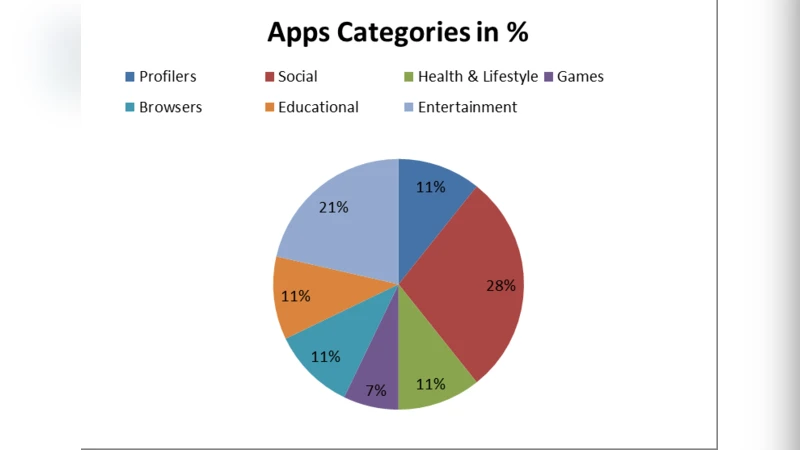
Review of Mobile Apps Permissions and Associated Intrusive Privacy Threats
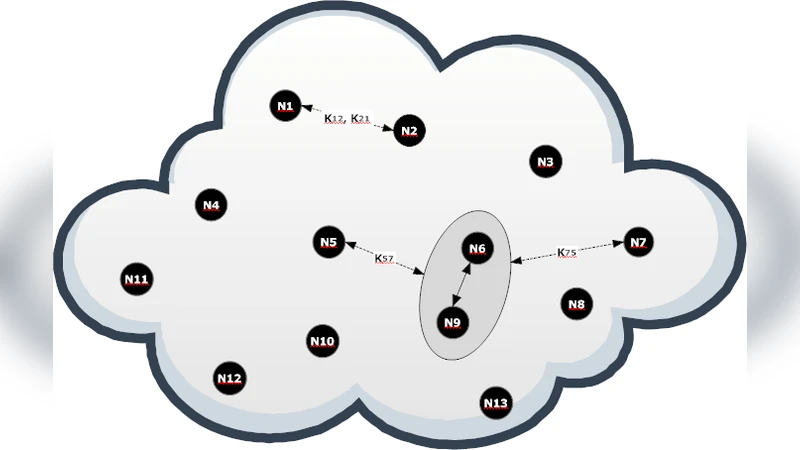
Key Management in Wireless Sensor Networks Using a Modified Blom Scheme

On the provable security of BEAR and LION schemes

Aspects of Nonabelian Group Based Cryptography: A Survey and Open Problems

Attack--Defense Trees and Two-Player Binary Zero-Sum Extensive Form Games Are Equivalent - Technical Report with Proofs