Cs-Cr
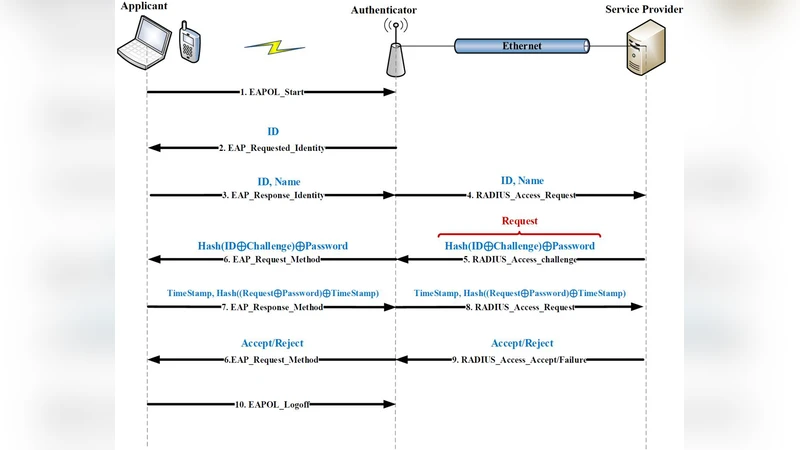
An Idea to Increase the Security of EAP-MD5 Protocol Against Dictionary Attack
Automatic Detection of Online Jihadist Hate Speech
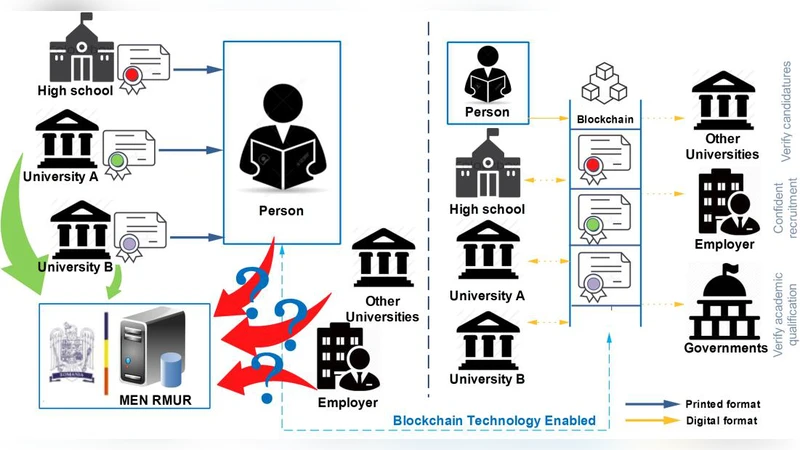
Blockchain and its Potential in Education
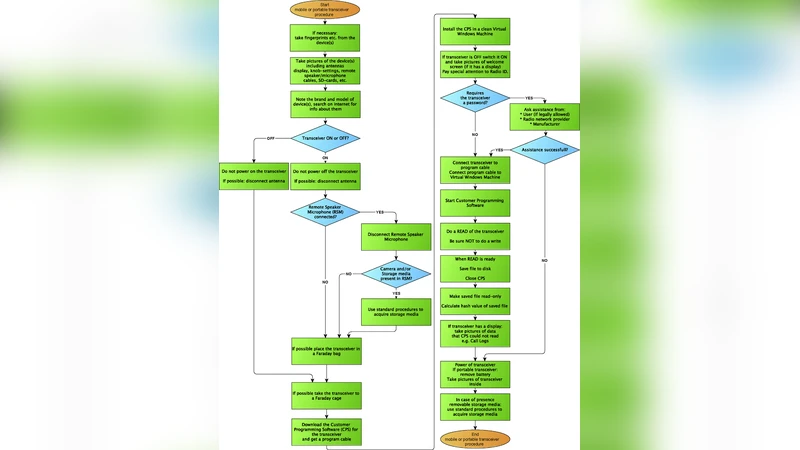
Digital forensic investigation of two-way radio communication equipment and services
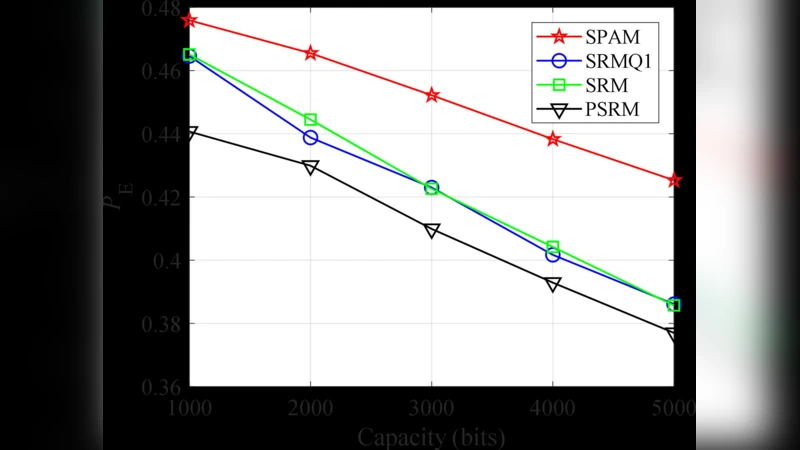
Computing in Covert Domain Using Data Hiding

Security modeling and efficient computation offloading for service workflow in mobile edge computing

A Pseudo Random Numbers Generator Based on Chaotic Iterations. Application to Watermarking

On isogeny classes of Edwards curves over finite fields
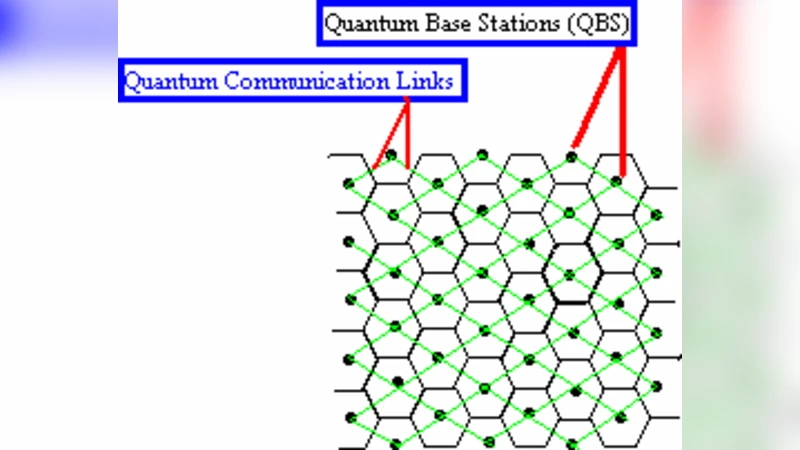
A Quantum Key Distribution Network Through Single Mode Optical Fiber

Maximizing Strength of Digital Watermarks using Fuzzy Logic

Internet of Things Security and Forensics: Challenges and Opportunities

Approximate Privacy: PARs for Set Problems
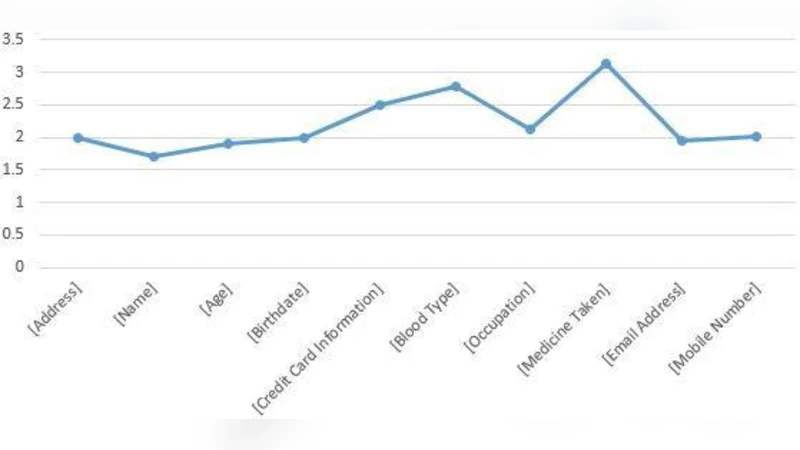
A model for system developers to measure the privacy risk of data
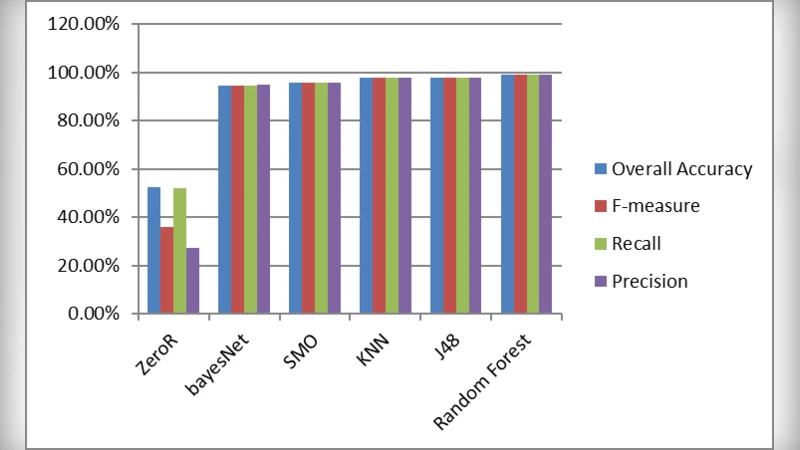
Classification of malware based on file content and characteristics
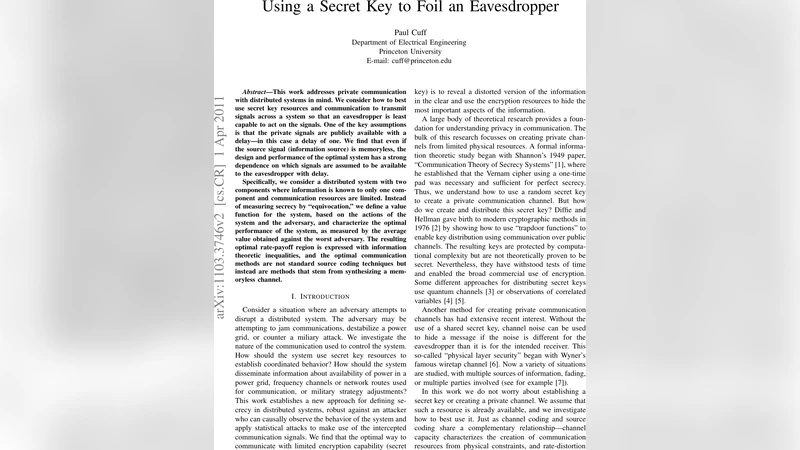
Using a Secret Key to Foil an Eavesdropper
SNEED: Enhancing Network Security Services Using Network Coding and Joint Capacity
Evidence Based Decision Making in Blockchain Economic Systems: From Theory to Practice
Smart False Data Injection attacks against State Estimation in Power Grid
Software-Defined Radio GNSS Instrumentation for Spoofing Mitigation: A Review and a Case Study
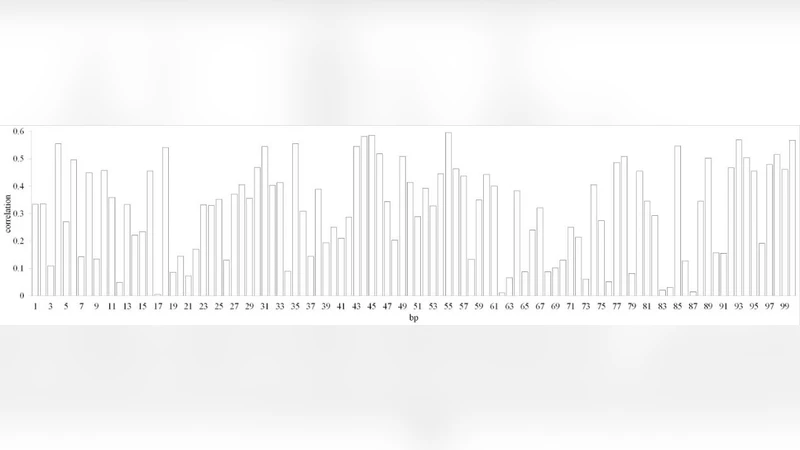
Prediction of Signal Sequences in Abiotic Stress Inducible Genes from Main Crops by Association Rule Mining

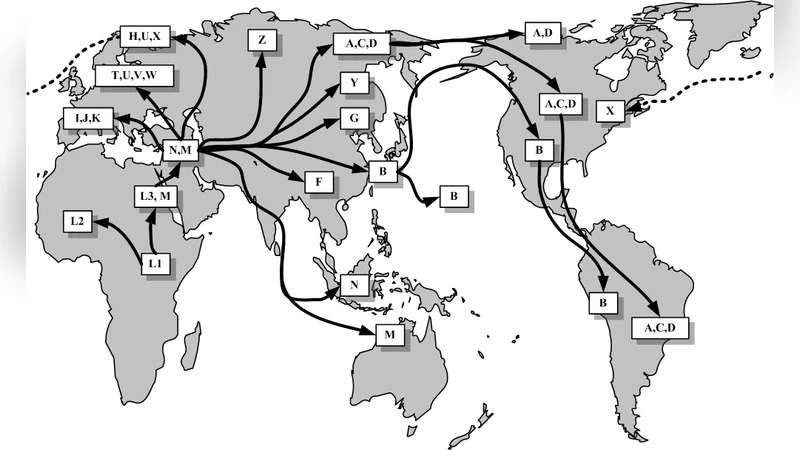
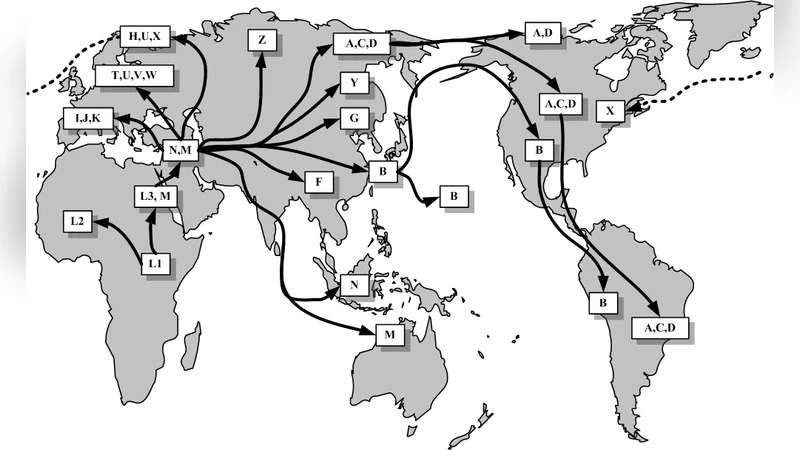
The New Threats of Information Hiding: the Road Ahead

Spatio-temporal Trajectory Dataset Privacy Based on Network Traffic Control