Cs-Cr
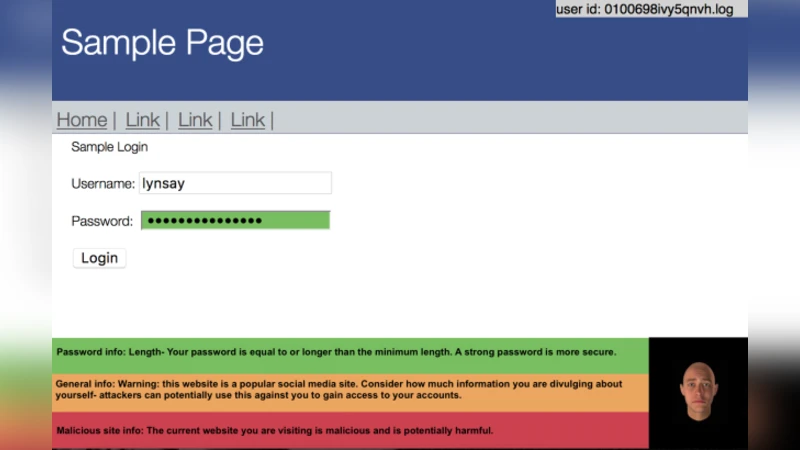
Security Awareness and Affective Feedback: Categorical Behaviour vs. Reported Behaviour
Data-Oblivious External-Memory Algorithms for the Compaction, Selection, and Sorting of Outsourced Data

Blockchain Technology Overview

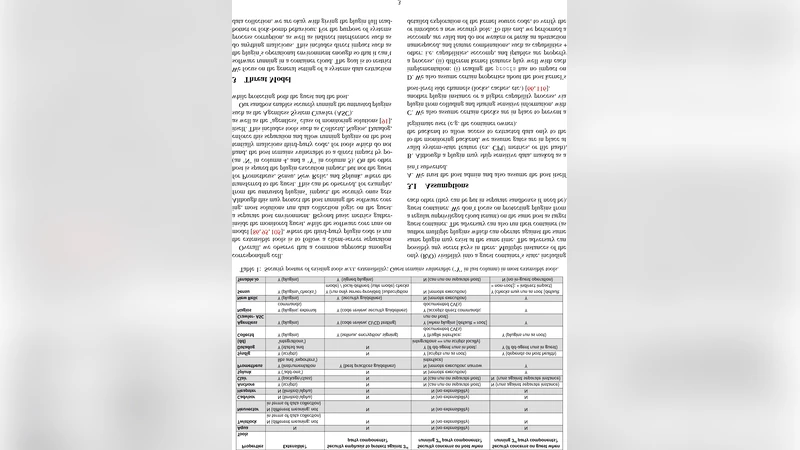
Secret Sharing and Proactive Renewal of Shares in Hierarchical Groups

A New Family of Practical Non-Malleable Diffie-Hellman Protocols
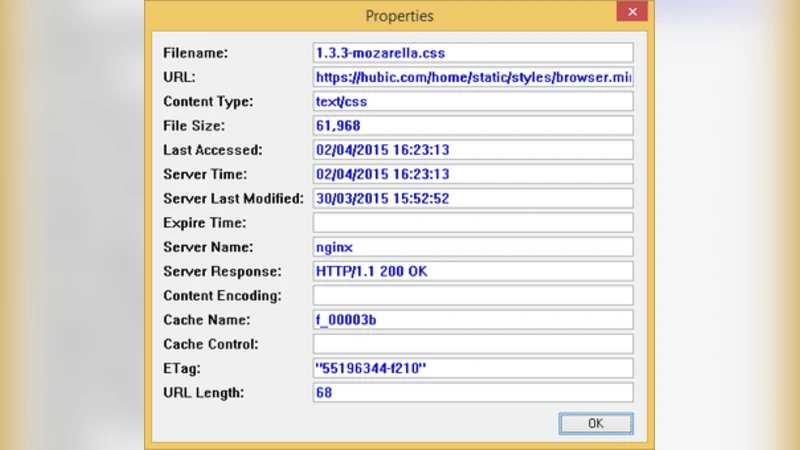
Cloud Storage Forensic: hubiC as a Case-Study
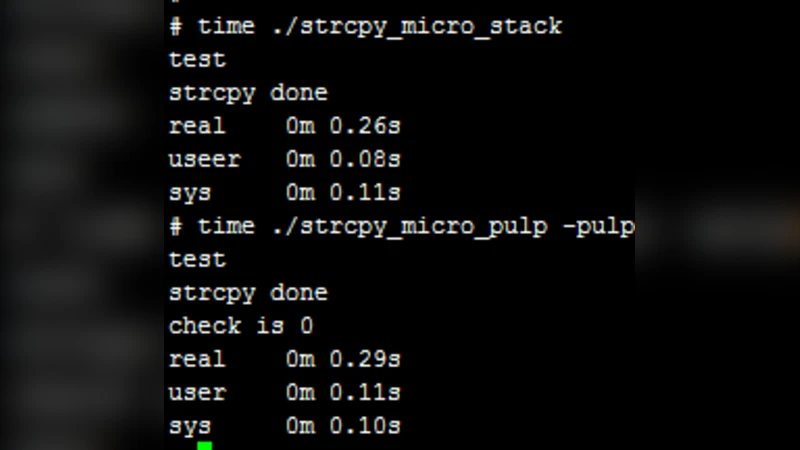
PULP: Inner-process Isolation based on the Program Counter and Data Memory Address

Counting Fixed Points, Two-Cycles, and Collisions of the Discrete Exponential Function using p-adic Methods
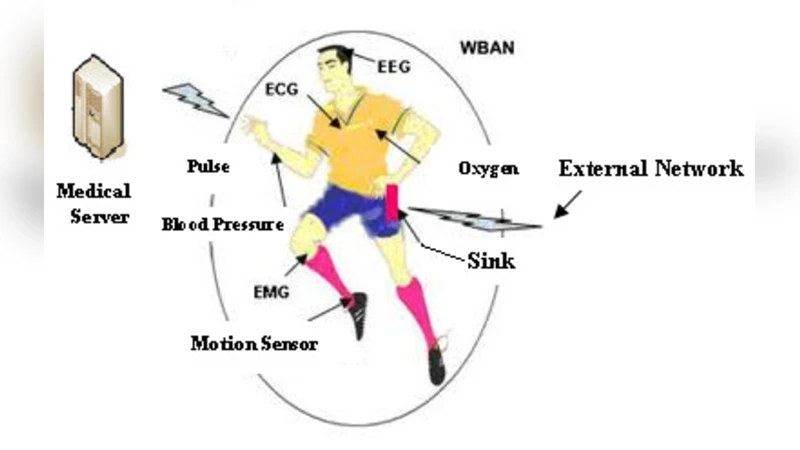
A Light Weight Protocol to Provide Location Privacy in Wireless Body Area networks
A Review on the Application of Blockchain for the Next Generation of Cybersecure Industry 4.0 Smart Factories
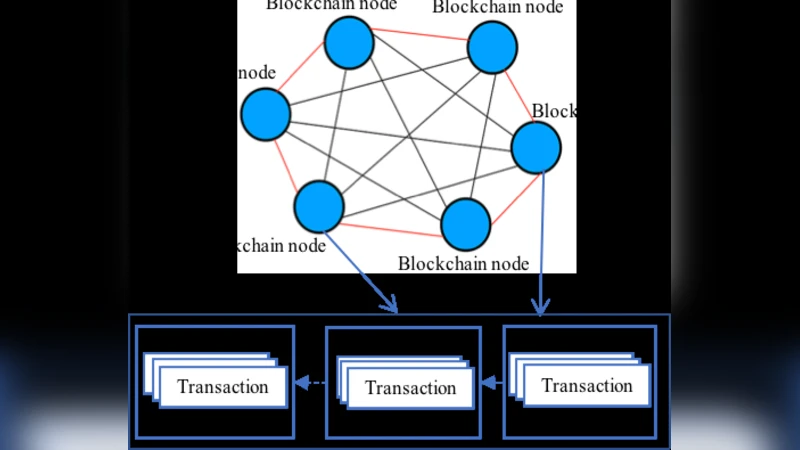
Security Services Using Blockchains: A State of the Art Survey
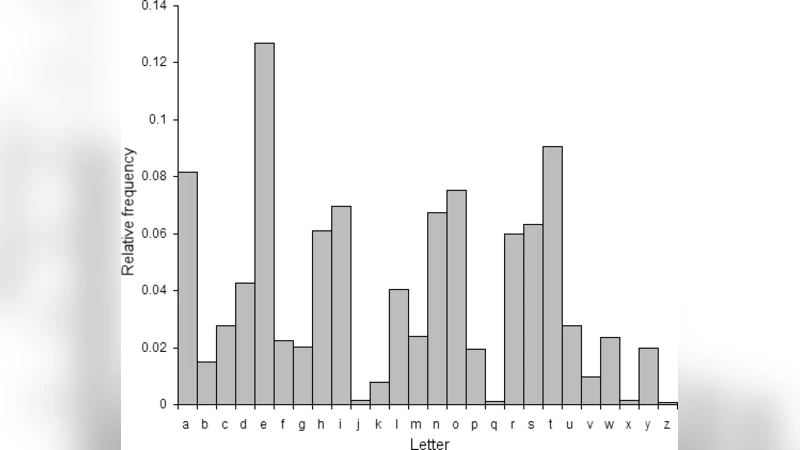
A New Technique for Text Data Compression
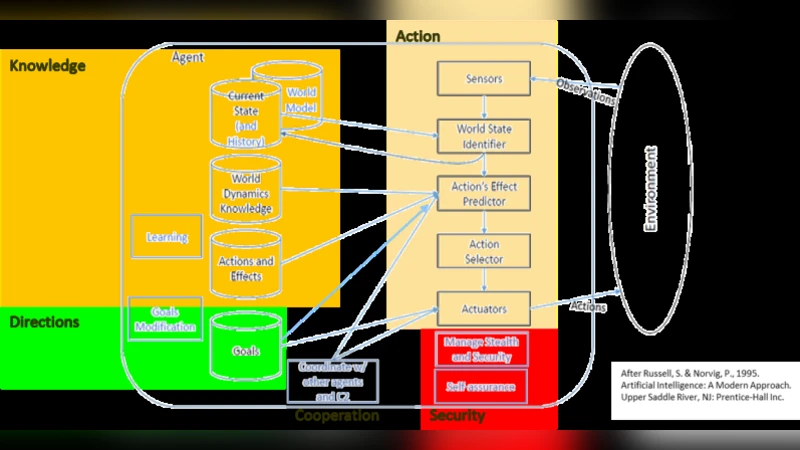
Towards an Active, Autonomous and Intelligent Cyber Defense of Military Systems: the NATO AICA Reference Architecture
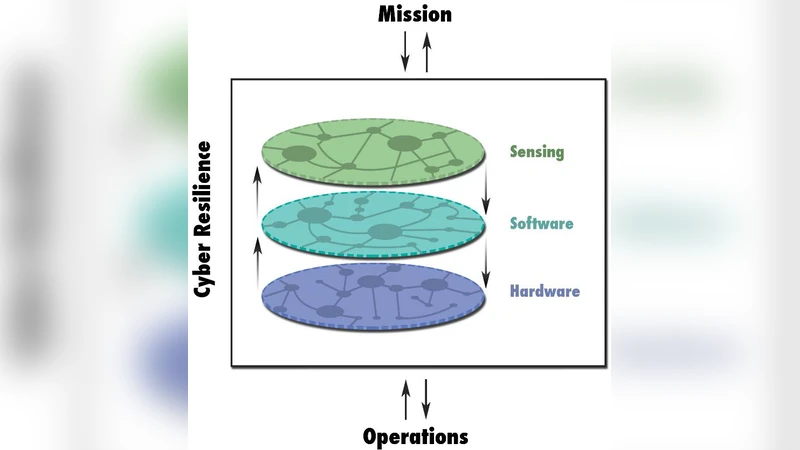
Fundamental Concepts of Cyber Resilience: Introduction and Overview
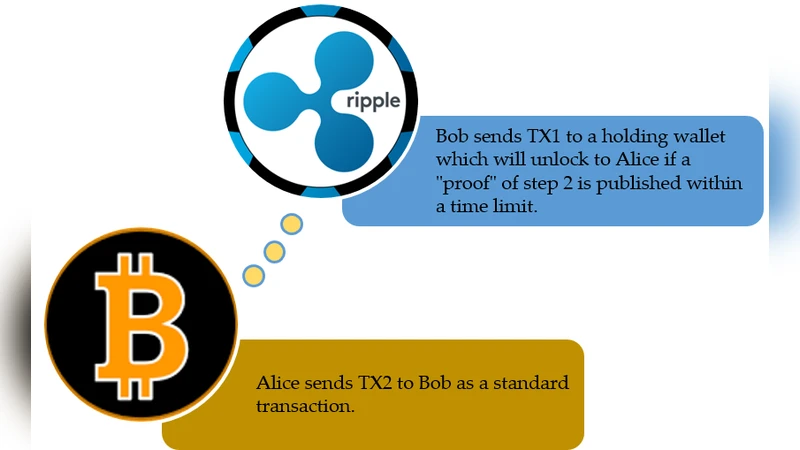
Atomic Cross-chain Swaps: Development, Trajectory and Potential of Non-monetary Digital Token Swap Facilities

Enhanced IoV Security Network by Using Blockchain Governance Game
Role of Trust in OAuth 2.0 and OpenID Connect
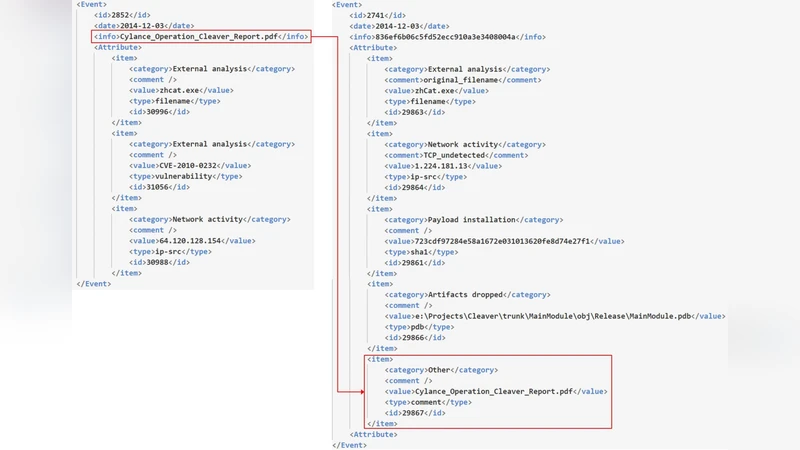
Automated Dataset Generation System for Collaborative Research of Cyber Threat Analysis

On improving security of GPT cryptosystems
Secure Extensibility for System State Extraction via Plugin Sandboxing
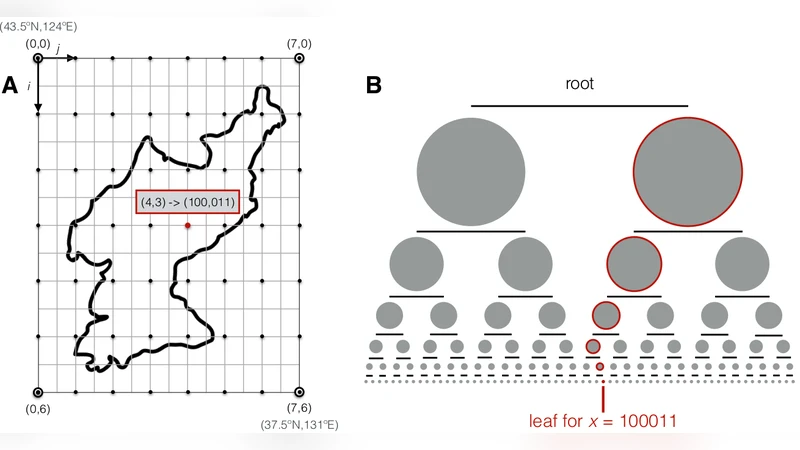
A Cryptographic Escrow for Treaty Declarations and Step-by-Step Verification

Mean-Set Attack: Cryptanalysis of Sibert et al. Authentication Protocol
