Cs-Cr
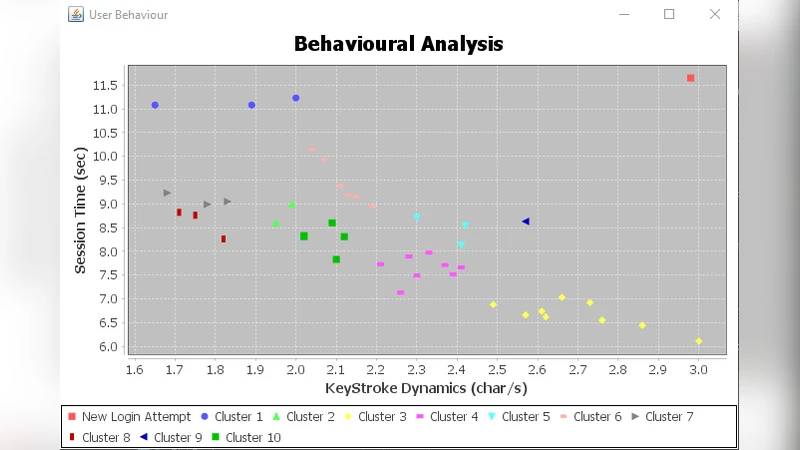
Behavioural Analytics: Beyond Risk-based MFA

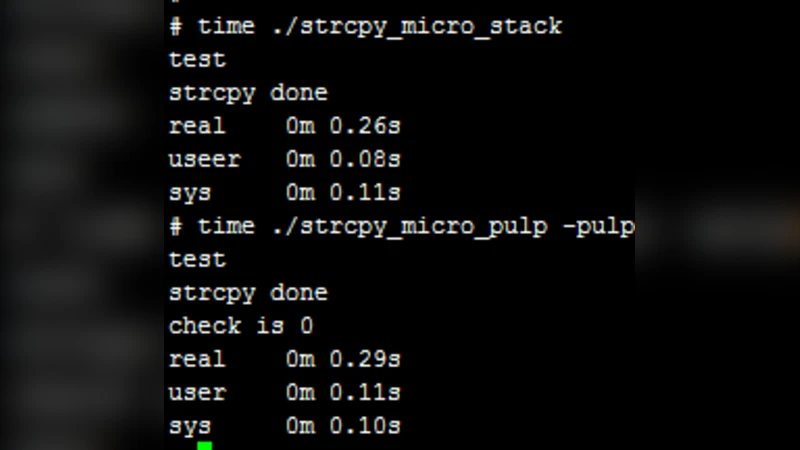
Code Reverse Engineering problem for Identification Codes
Traceability Decentralization in Supply Chain Management Using Blockchain Technologies
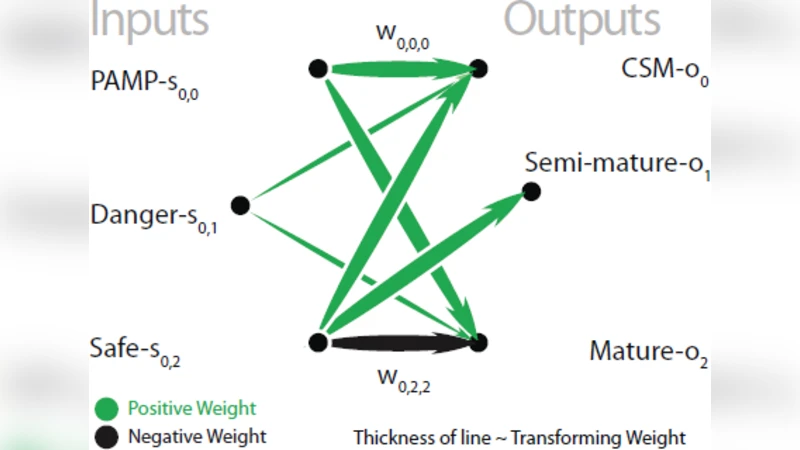
The DCA:SOMe Comparison A comparative study between two biologically-inspired algorithms
Decoding square-free Goppa codes over $F_p$
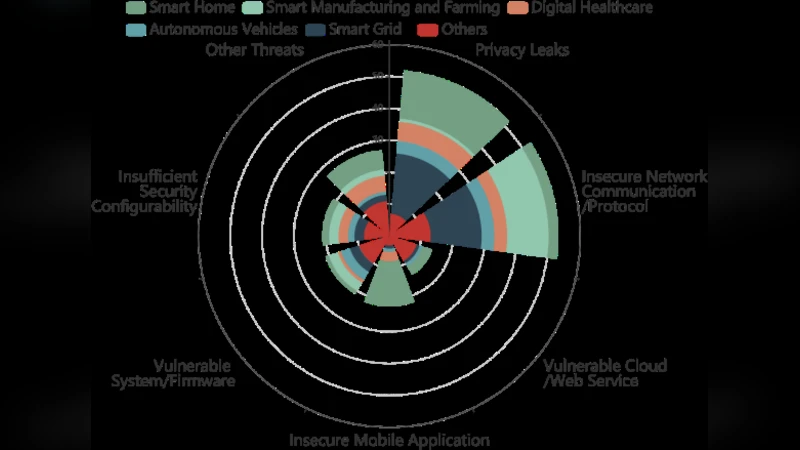
The Effect of IoT New Features on Security and Privacy: New Threats, Existing Solutions, and Challenges Yet to Be Solved

Encryption of Binary and Non-Binary Data Using Chained Hadamard Transforms

Anomaly Generation using Generative Adversarial Networks in Host Based Intrusion Detection
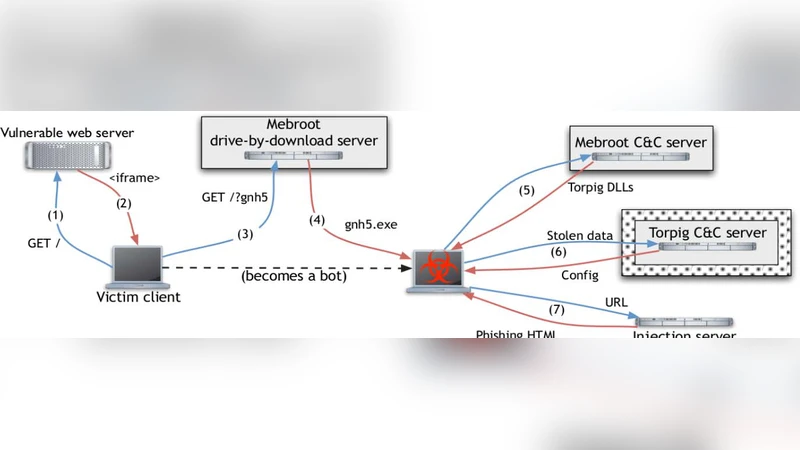
Mitigating Botnet Attack Using Encapsulated Detection Mechanism (EDM)
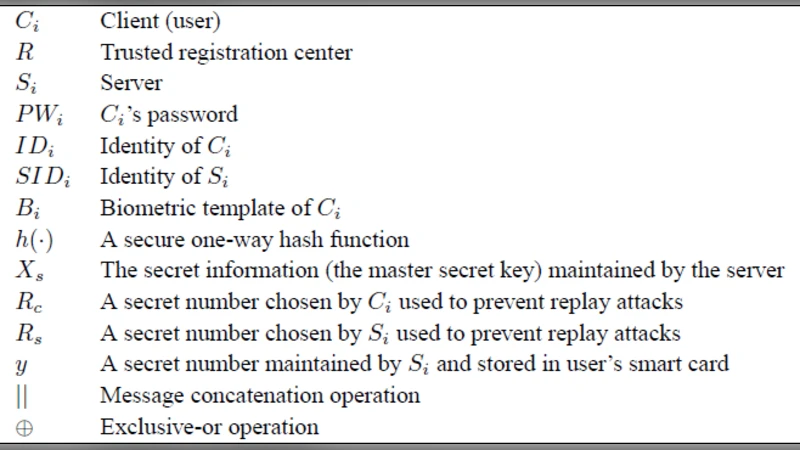
Cryptanalysis And Further Improvement Of A Biometric-Based Remote User Authentication Scheme Using Smart Cards
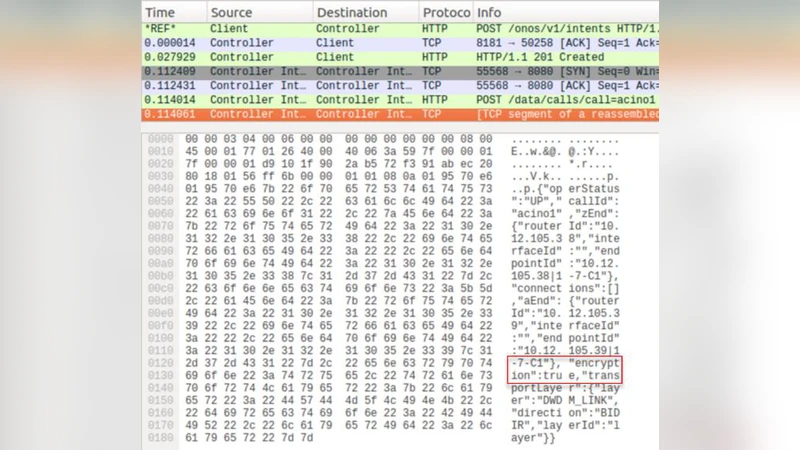
First Demonstration of an Automatic Multilayer Intent-Based Secure Service Creation by an Open Source SDN Orchestrator
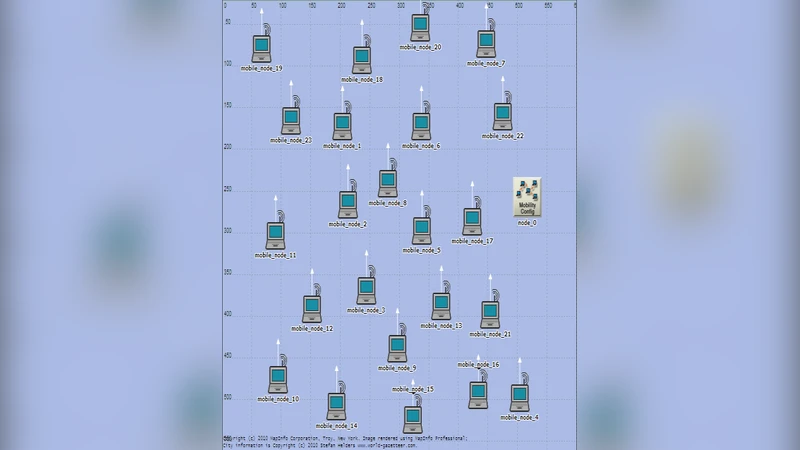
Performance Analysis of AODV under Black Hole Attack through Use of OPNET Simulator

A Conjoint Application of Data Mining Techniques for Analysis of Global Terrorist Attacks -- Prevention and Prediction for Combating Terrorism
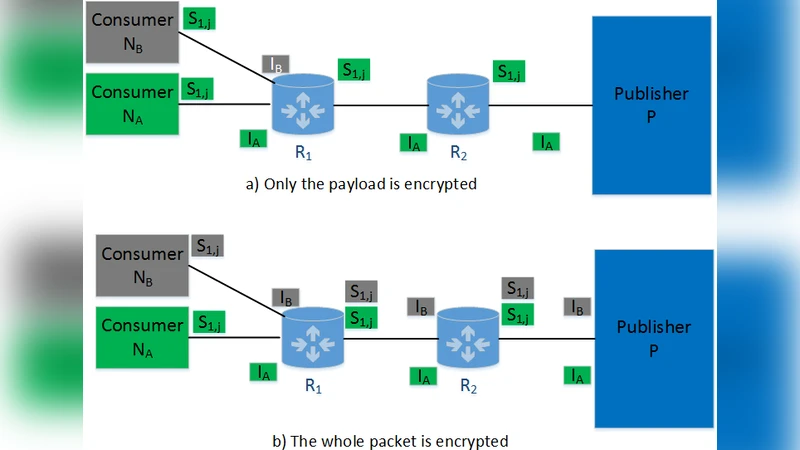
Effective Caching for the Secure Content Distribution in Information-Centric Networking
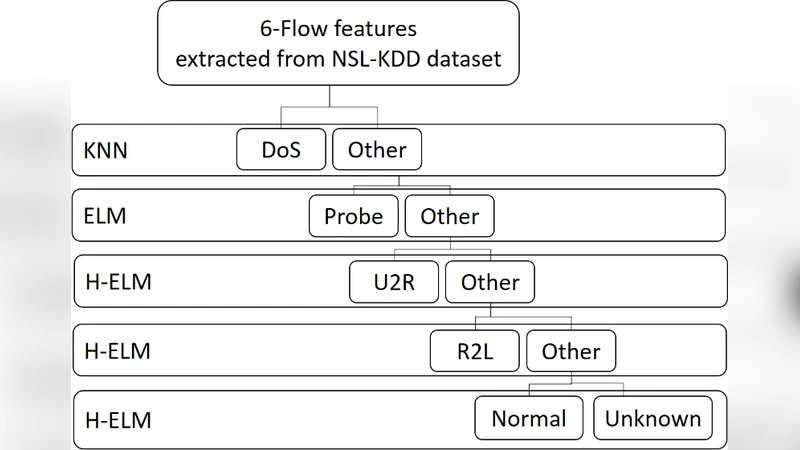
An Efficient Flow-based Multi-level Hybrid Intrusion Detection System for Software-Defined Networks
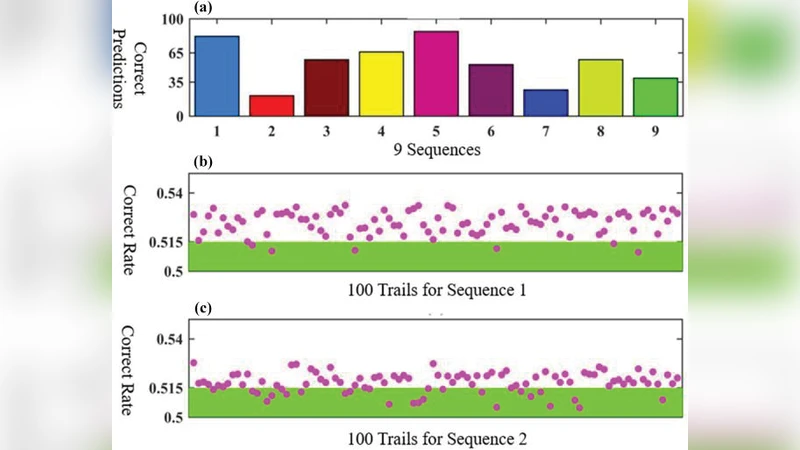
Learning from Pseudo-Randomness With an Artificial Neural Network - Does God Play Pseudo-Dice?
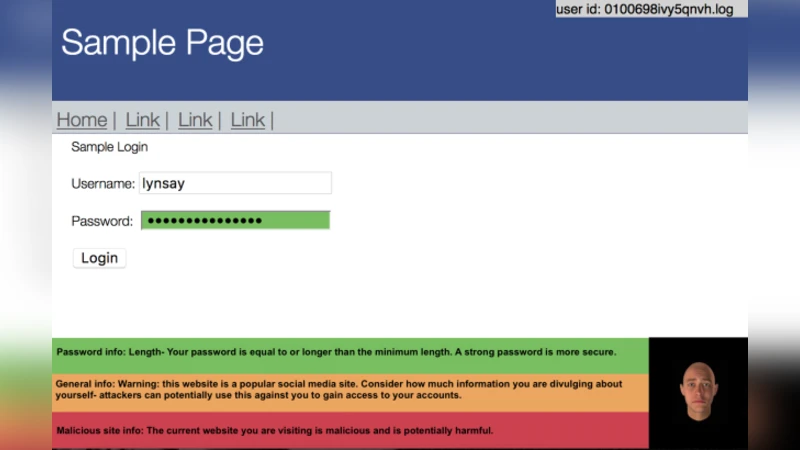
Security Awareness and Affective Feedback: Categorical Behaviour vs. Reported Behaviour
Data-Oblivious External-Memory Algorithms for the Compaction, Selection, and Sorting of Outsourced Data

Blockchain Technology Overview

Secret Sharing and Proactive Renewal of Shares in Hierarchical Groups

A New Family of Practical Non-Malleable Diffie-Hellman Protocols
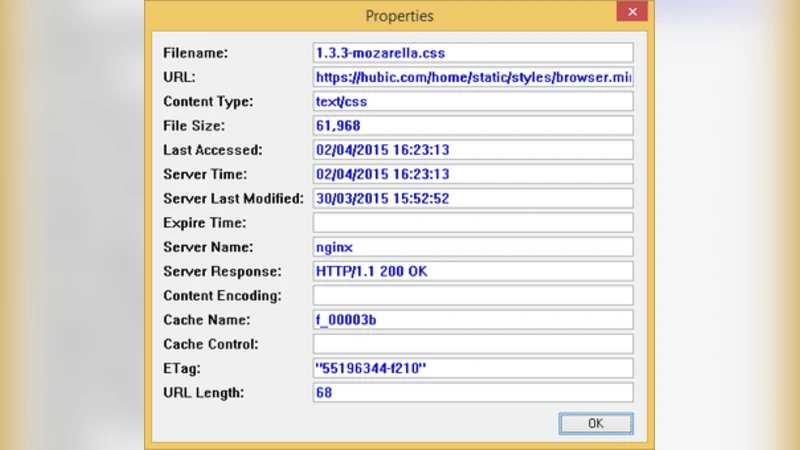
Cloud Storage Forensic: hubiC as a Case-Study