Cs-Cr


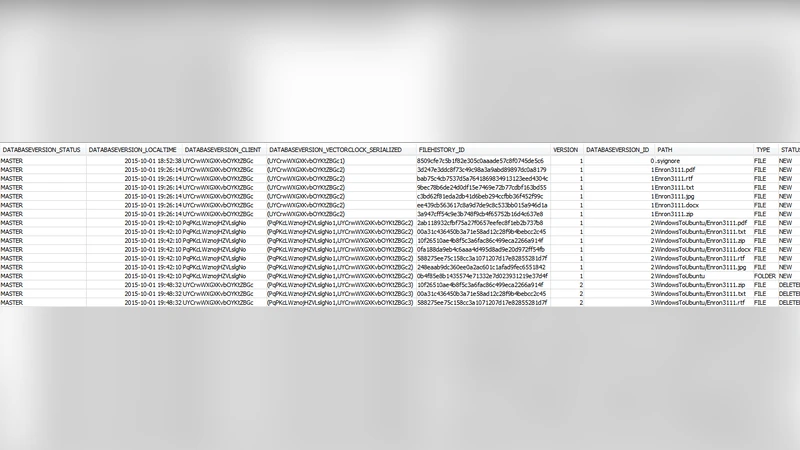
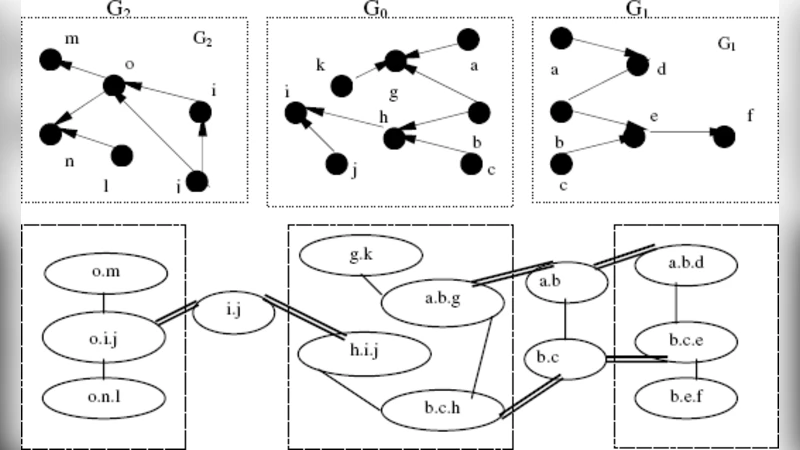
A Method for Ontology-based Architecture Reconstruction of Computing Platforms
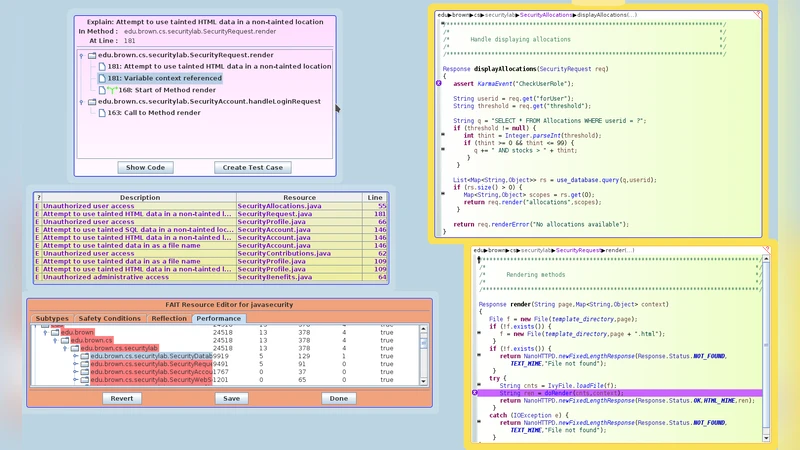
Continuous Flow Analysis to Detect Security Problems
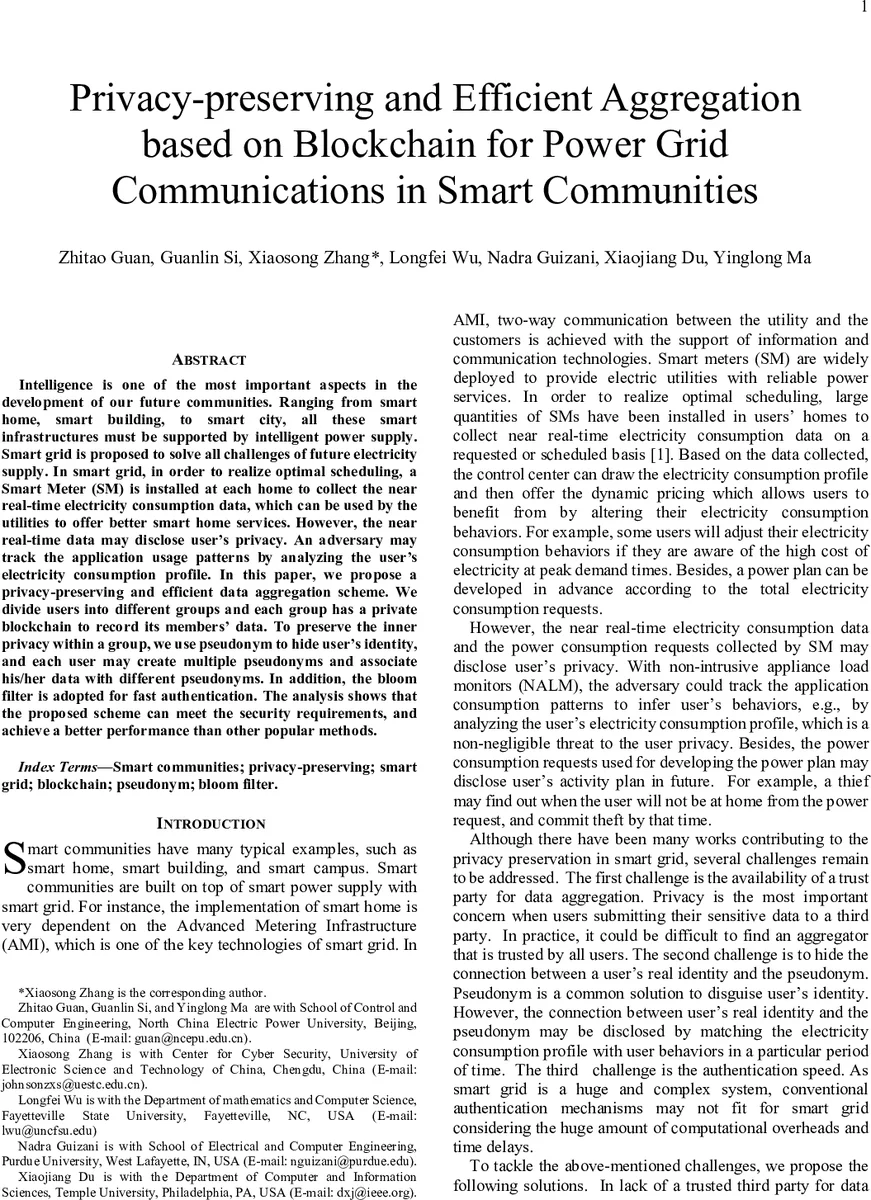
Privacy-preserving and Efficient Aggregation based on Blockchain for Power Grid Communications in Smart Communities

Virtualization Technologies and Cloud Security: advantages, issues, and perspectives
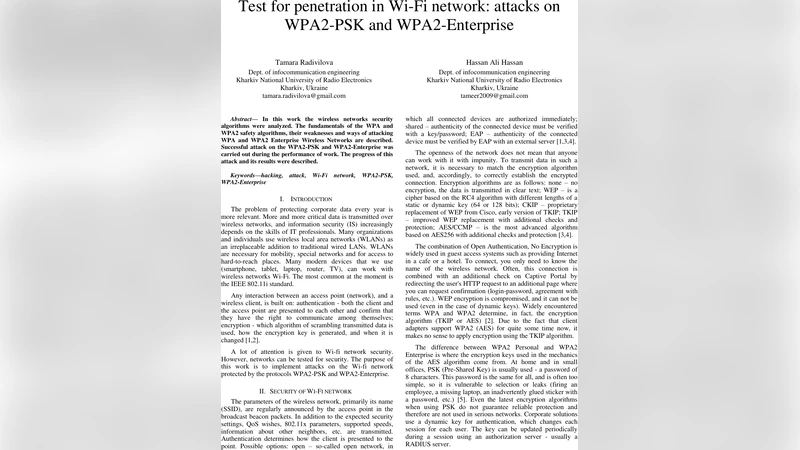
Test for penetration in Wi-Fi network: attacks on WPA2-PSK and WPA2-Enterprise

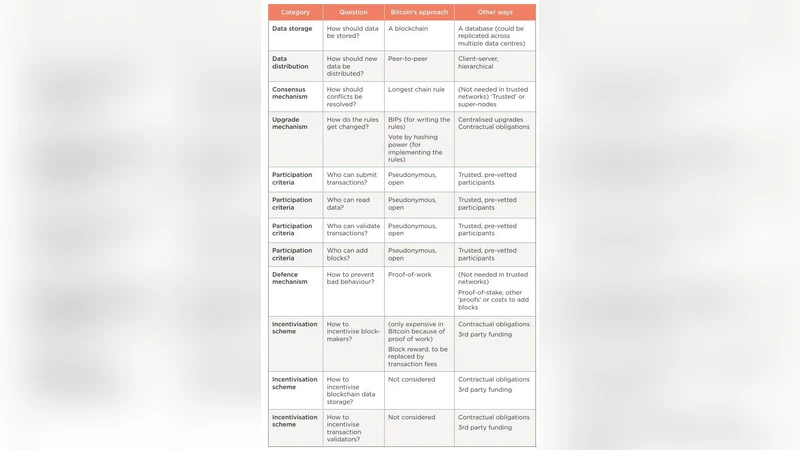
On the Origins and Variations of Blockchain Technologies

NLHB : A Non-Linear Hopper Blum Protocol
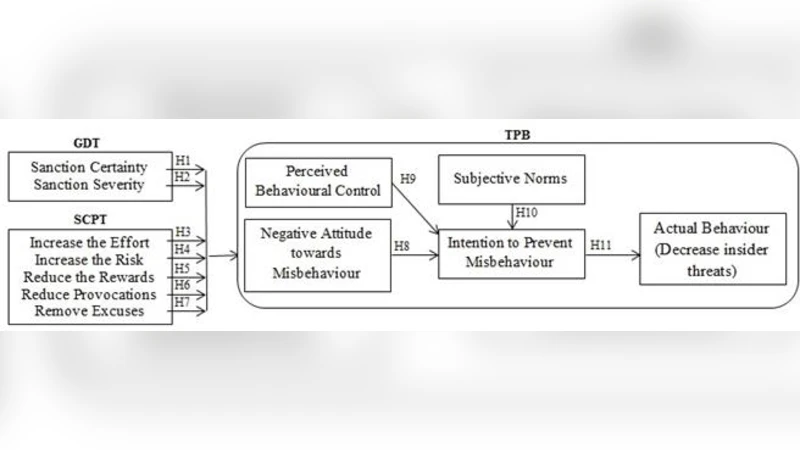
Deterrence and Prevention-based Model to Mitigate Information Security Insider Threats in Organisations
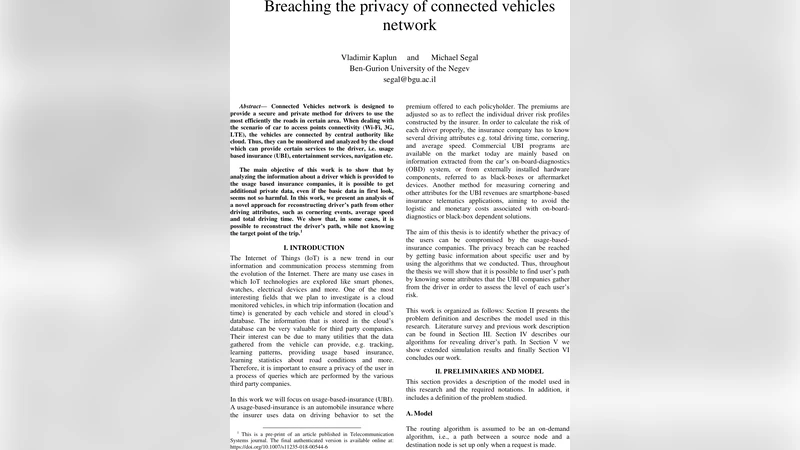
Breaching the privacy of connected vehicles network
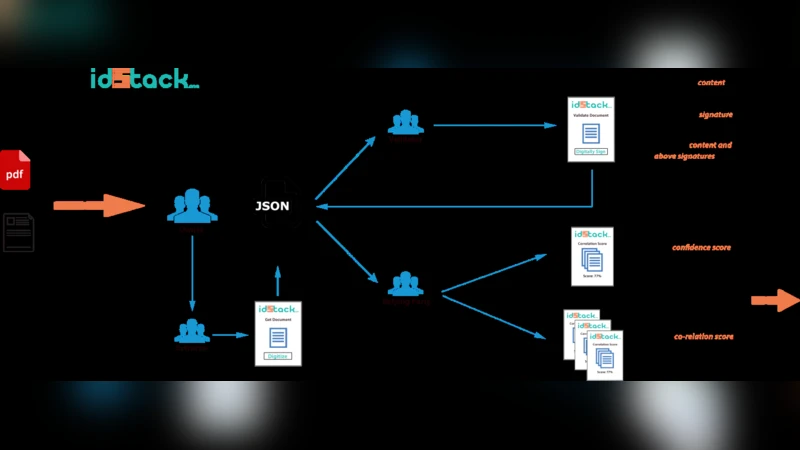
IDStack -- The Common Protocol for Document Verification built on Digital Signatures

New Attack Strategy for the Shrinking Generator
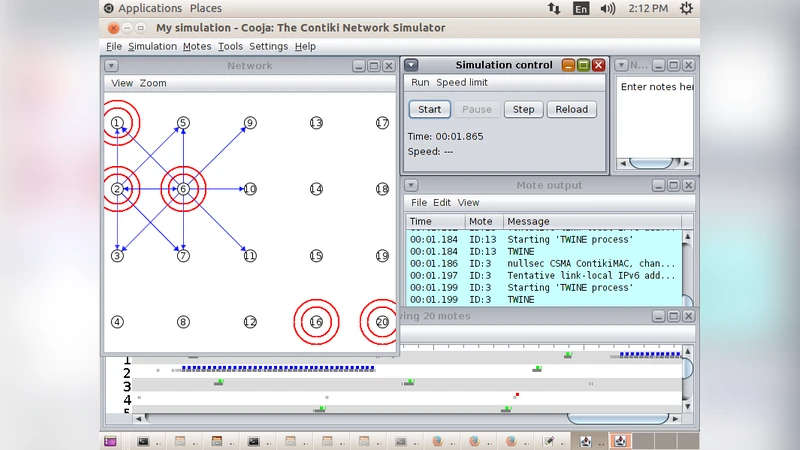
Performance Analysis of Symmetric Key Ciphers in Linear and Grid Based Sensor Networks

Architectural Tactics for Big Data Cybersecurity Analytic Systems: A Review
Transparent Voting Platform Based on Permissioned Blockchain
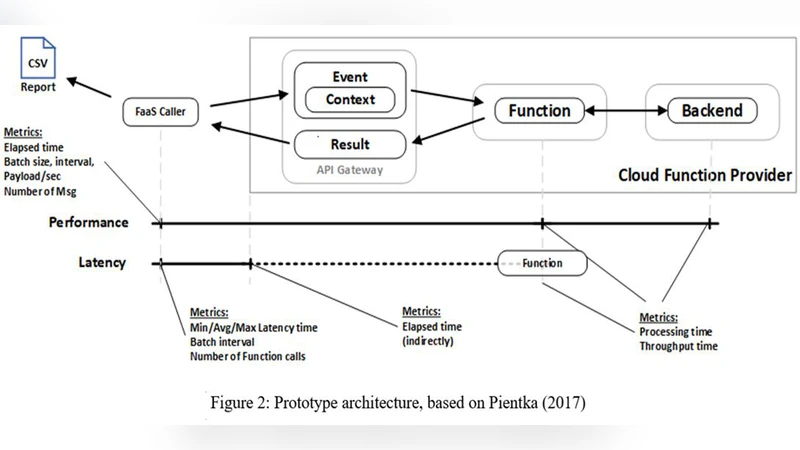
Towards a Security-Aware Benchmarking Framework for Function-as-a-Service

Divide et Impera: MemoryRanger Runs Drivers in Isolated Kernel Spaces
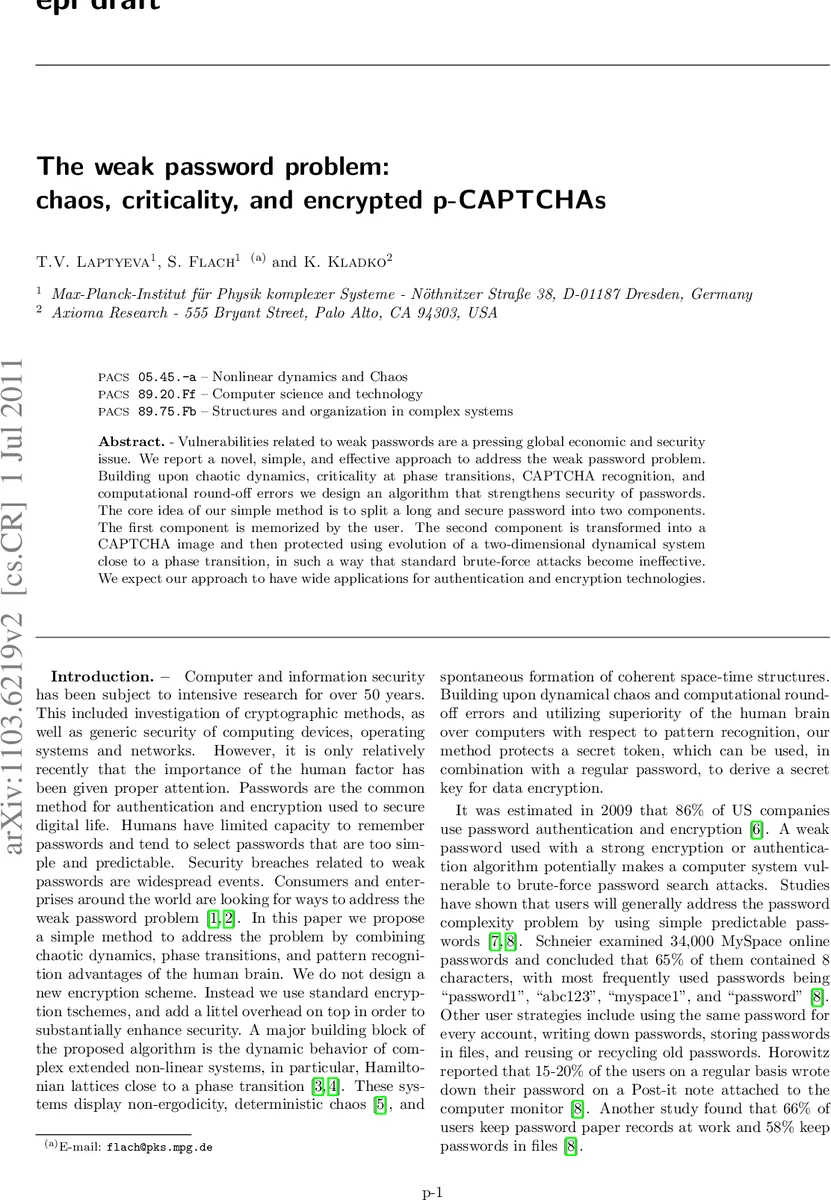
The weak password problem: chaos, criticality, and encrypted p-CAPTCHAs

RFID Key Establishment Against Active Adversaries
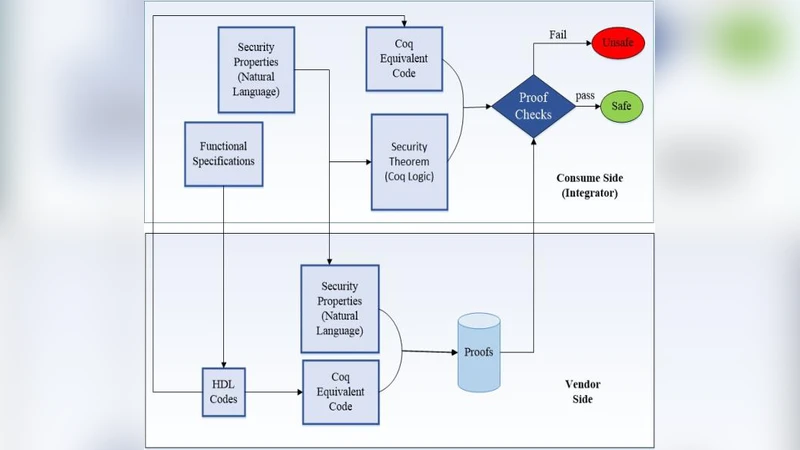
Validation of Hardware Security and Trust: A Survey
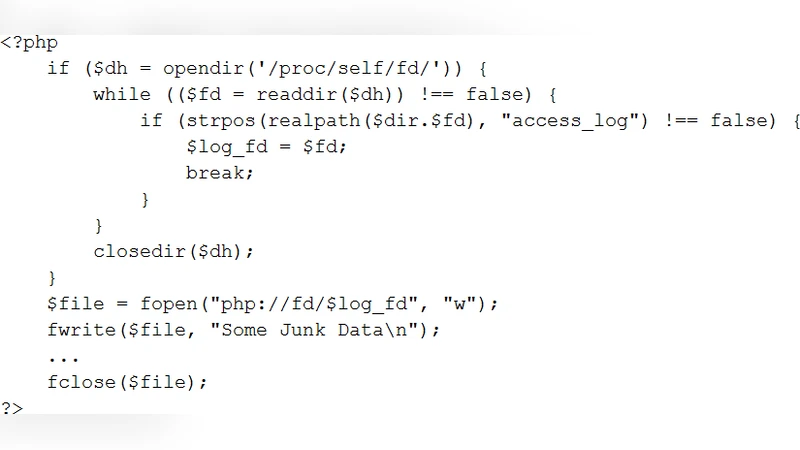
Two Novel Server-Side Attacks against Log File in Shared Web Hosting Servers
A Robust and Fault-Tolerant Distributed Intrusion Detection System
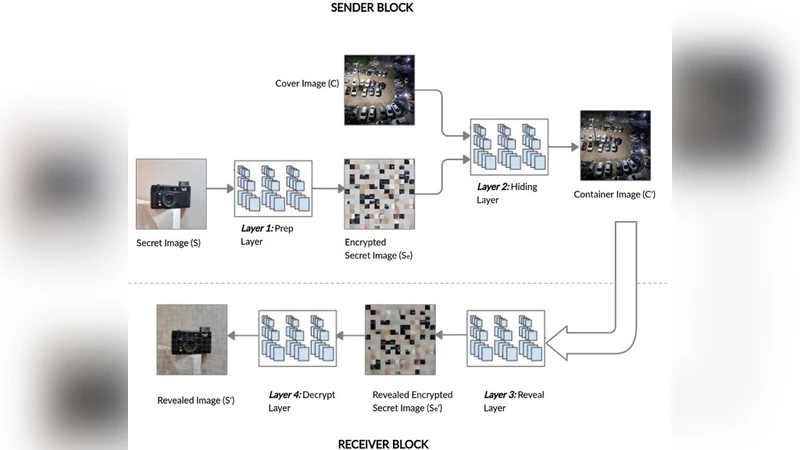
Hiding Data in Images Using Cryptography and Deep Neural Network