Cs-Cr
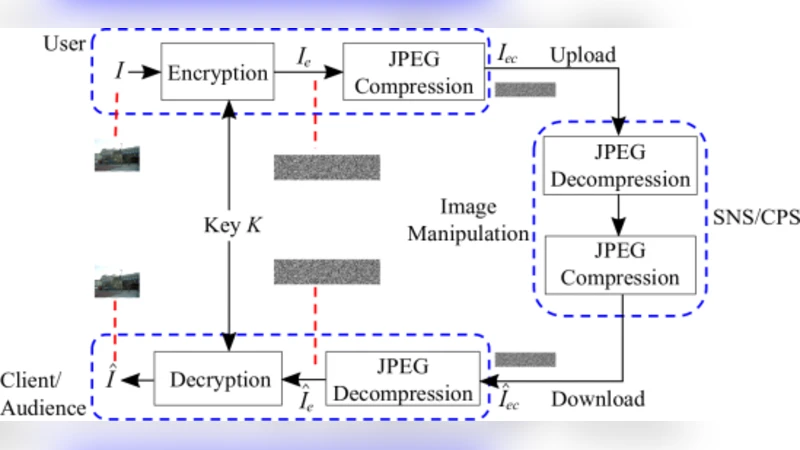

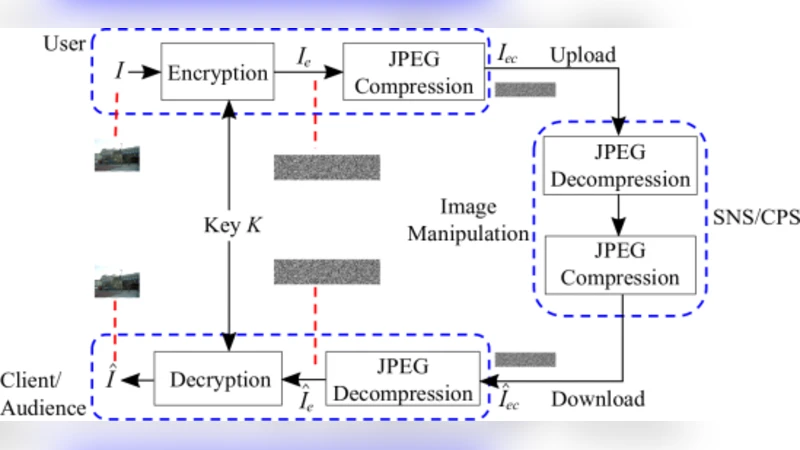
Video Encryption: A Survey
Profile-Based Ad Hoc Social Networking Using Wi-Fi Direct on the Top of Android
Contribution of Herv{e} Suaudeau for the mission of the French Senate Law Commission on electronic voting on 25 January 2018
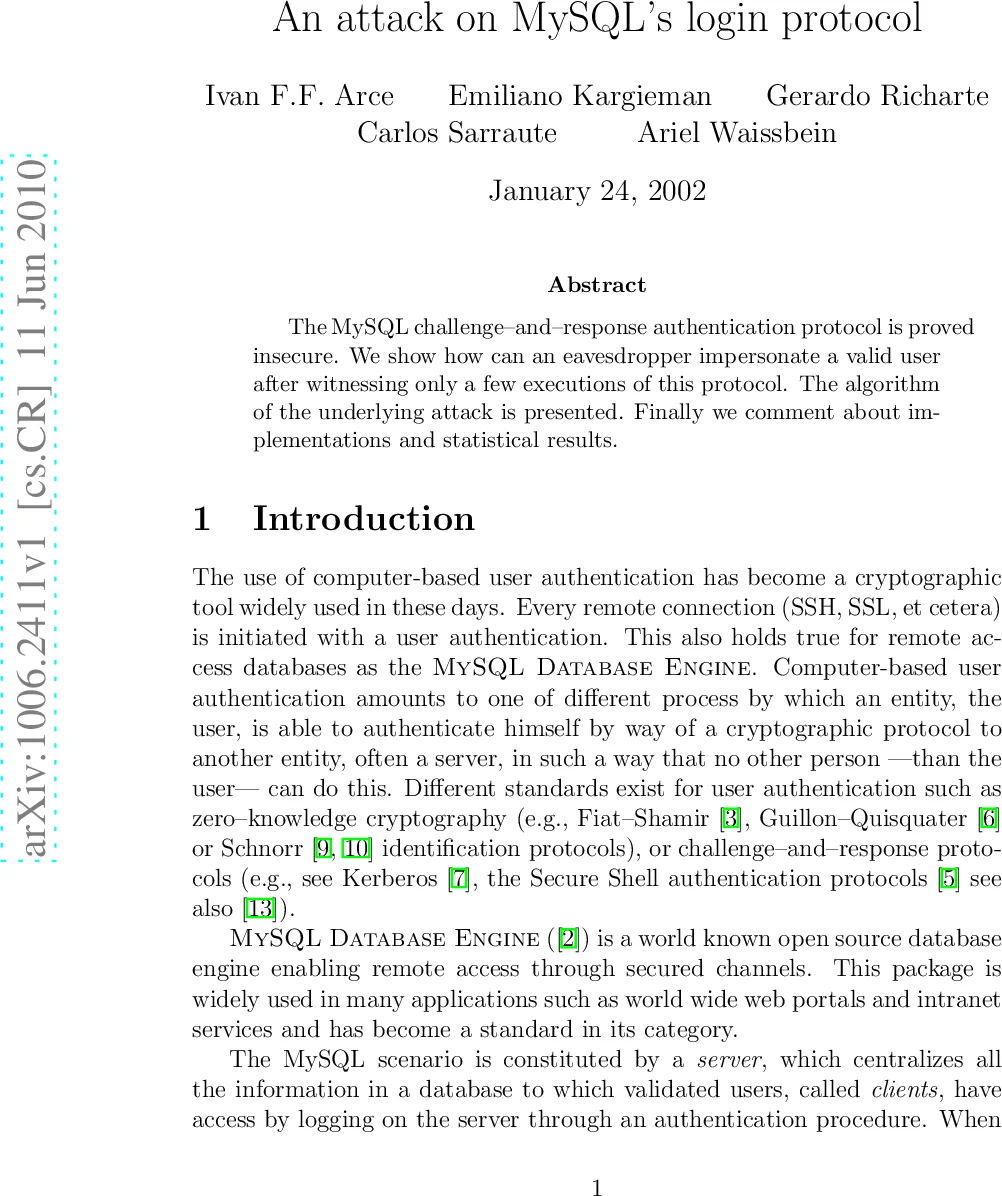
An attack on MySQLs login protocol

Towards Security as a Service to Protect the Critical Resources of Mobile Computing Devices
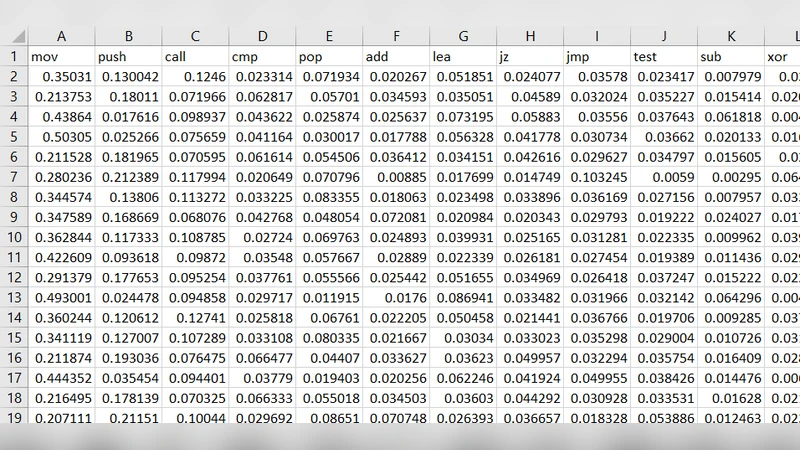
Leveraging Support Vector Machine for Opcode Density Based Detection of Crypto-Ransomware
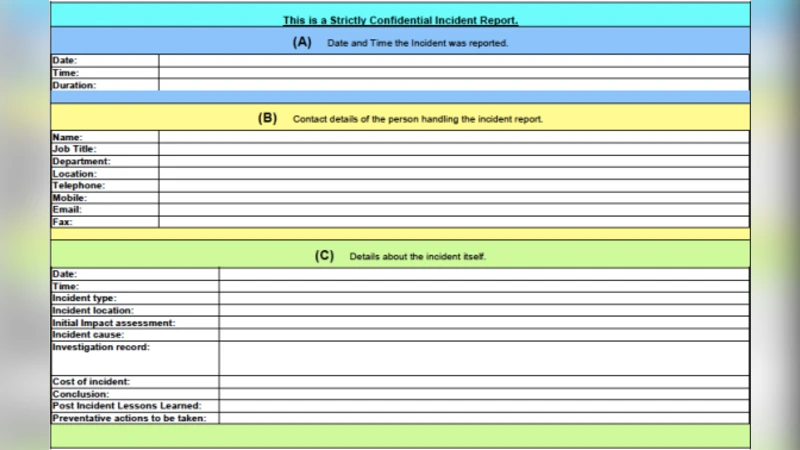
How Good is Your Data? Investigating the Quality of Data Generated During Security Incident Response Investigations
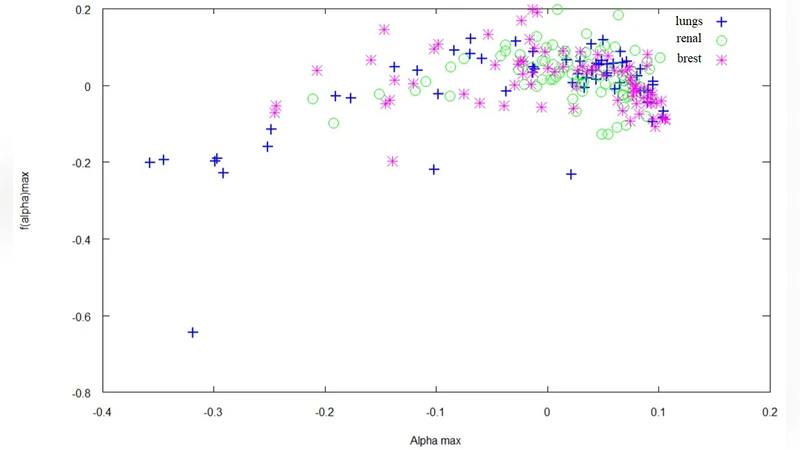
Neural Network based classification of bone metastasis by primary cacinoma
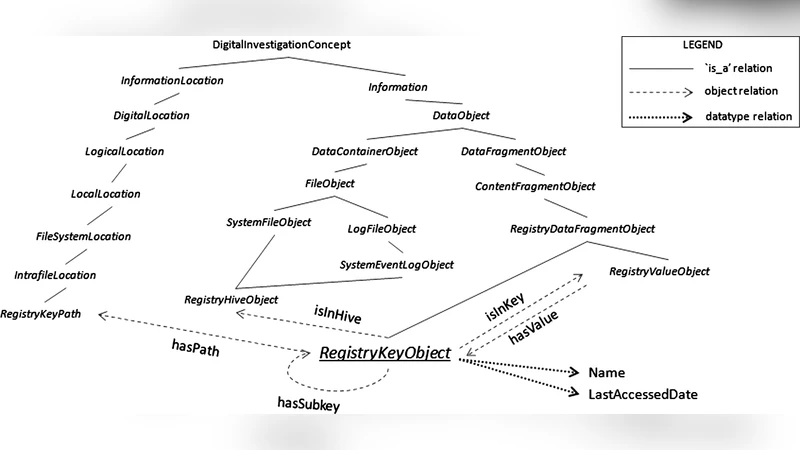
DIALOG: A framework for modeling, analysis and reuse of digital forensic knowledge
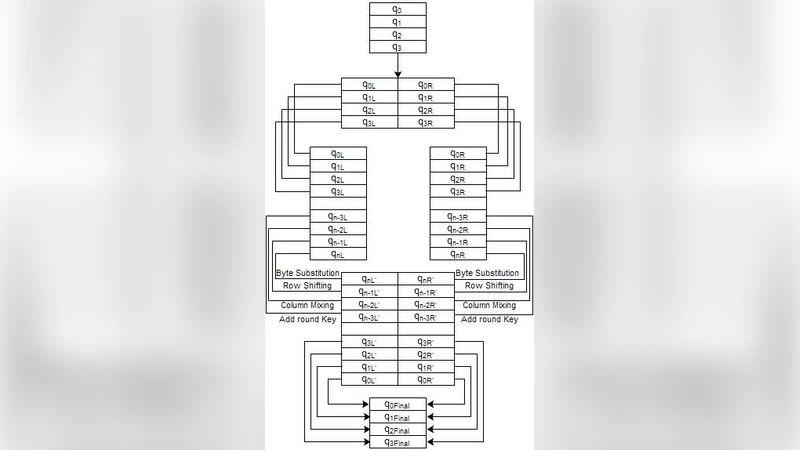
A Parallel Encryption Algorithm for Block Ciphers Based on Reversible Programmable Cellular Automata

Automated Symbolic Analysis of ARBAC-Policies (Extended Version)
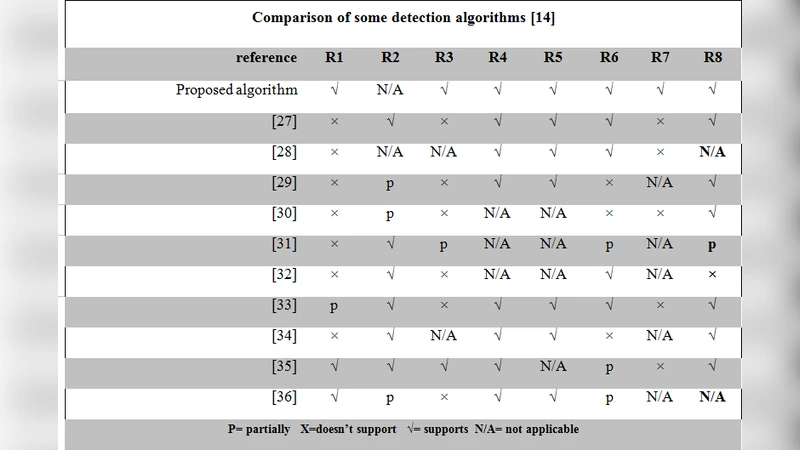
A Novel Framework for DDoS Detectionin Huge Scale Networks, Thanksto QoS Features

Security protocols for distributed wireless sensor networks

A Method for Ontology-based Architecture Reconstruction of Computing Platforms
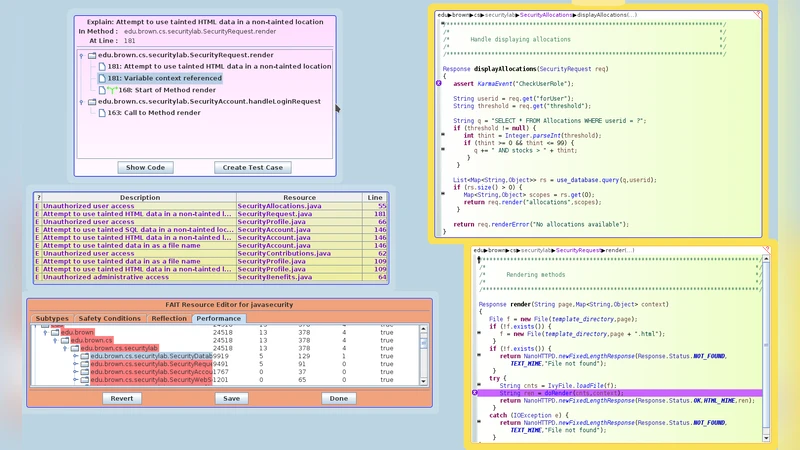
Continuous Flow Analysis to Detect Security Problems
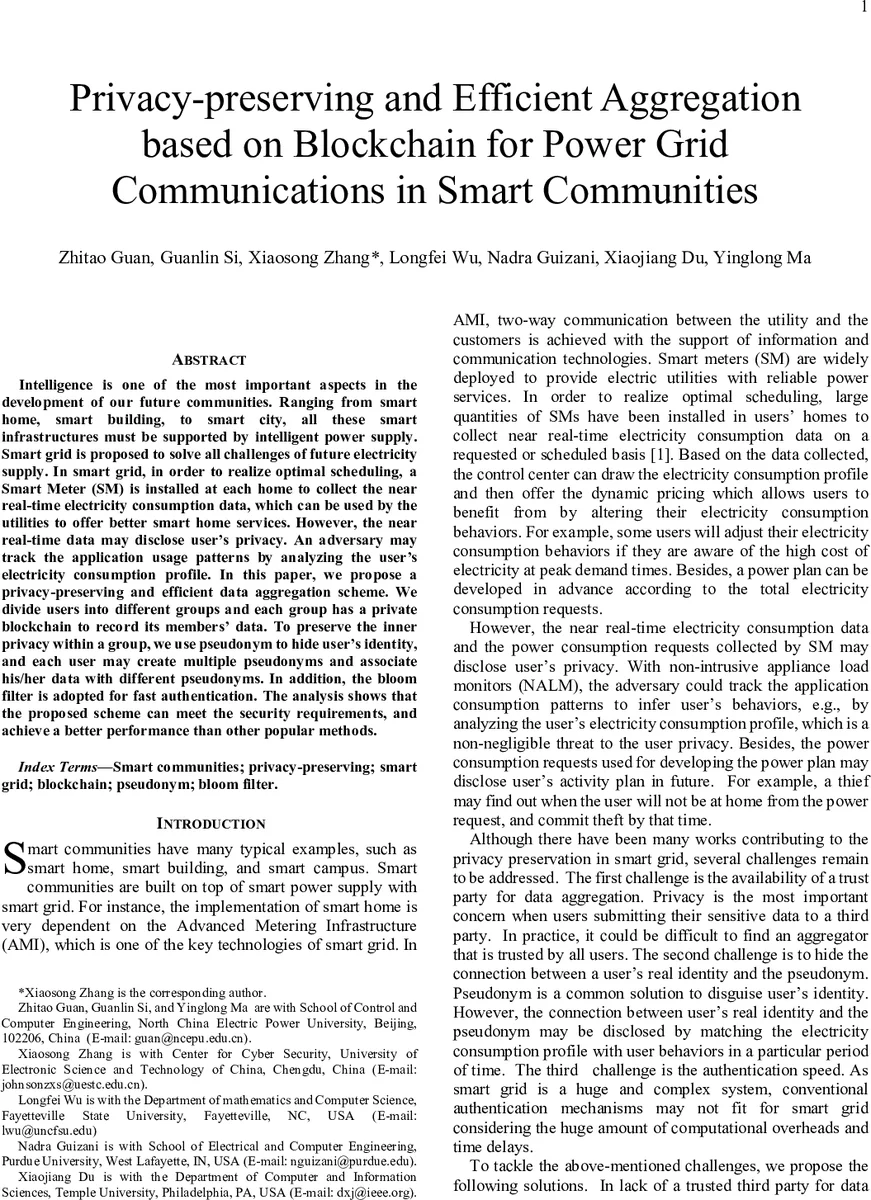
Privacy-preserving and Efficient Aggregation based on Blockchain for Power Grid Communications in Smart Communities

Virtualization Technologies and Cloud Security: advantages, issues, and perspectives
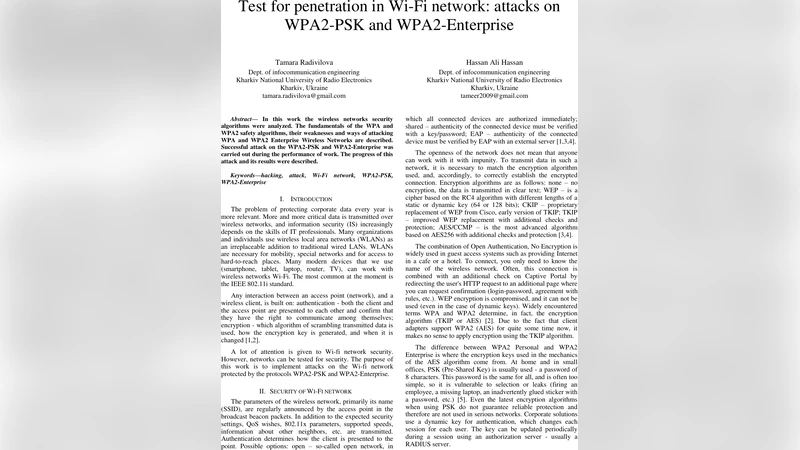
Test for penetration in Wi-Fi network: attacks on WPA2-PSK and WPA2-Enterprise

On the Origins and Variations of Blockchain Technologies

NLHB : A Non-Linear Hopper Blum Protocol
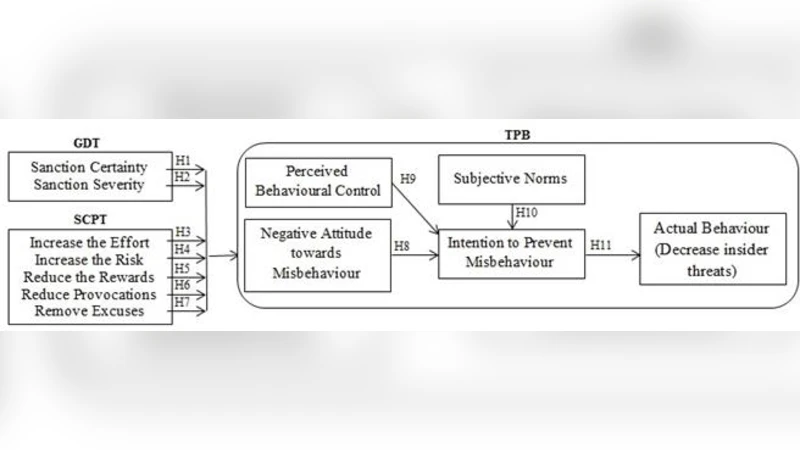
Deterrence and Prevention-based Model to Mitigate Information Security Insider Threats in Organisations
Breaching the privacy of connected vehicles network