Cs-Cr

Non Abelian Bent Functions
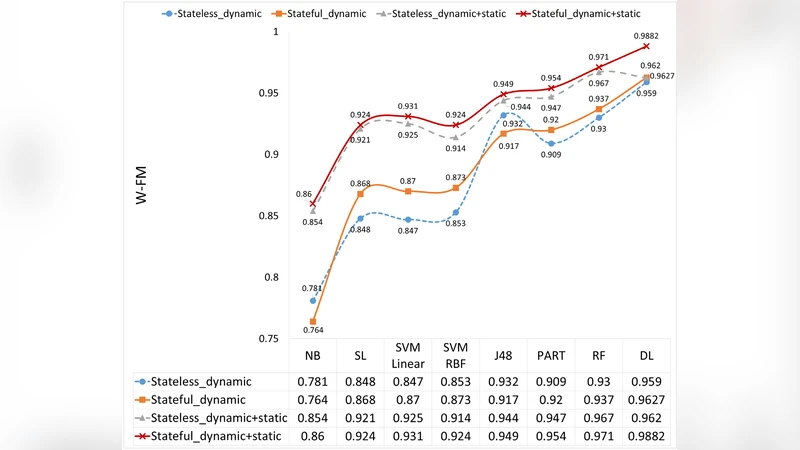
An Intrusion Detection Architecture for Clustered Wireless Ad Hoc Networks
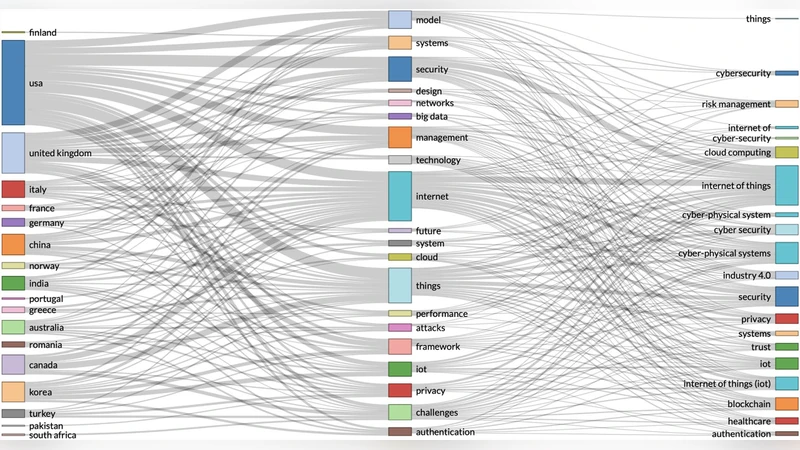
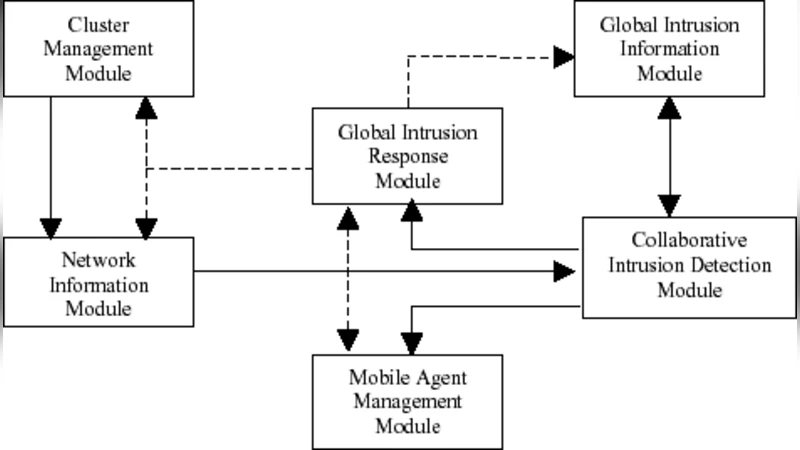
Dynamic real-time risk analytics of uncontrollable states in complex internet of things systems, cyber risk at the edge
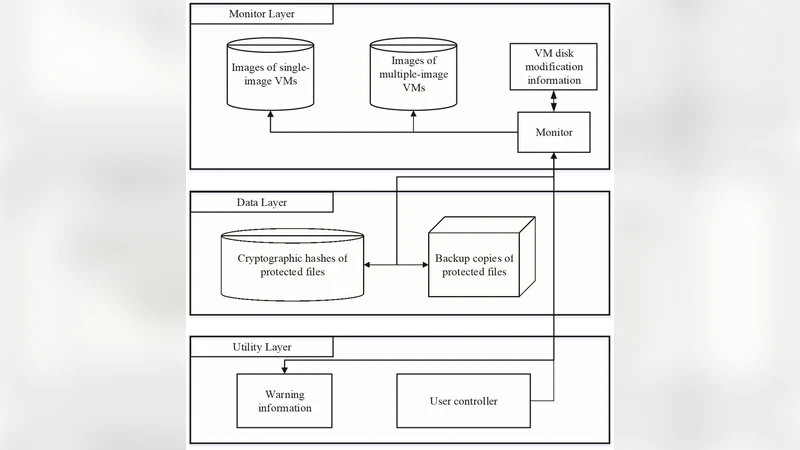
A high-performance virtual machine filesystem monitor in cloud-assisted cognitive IoT
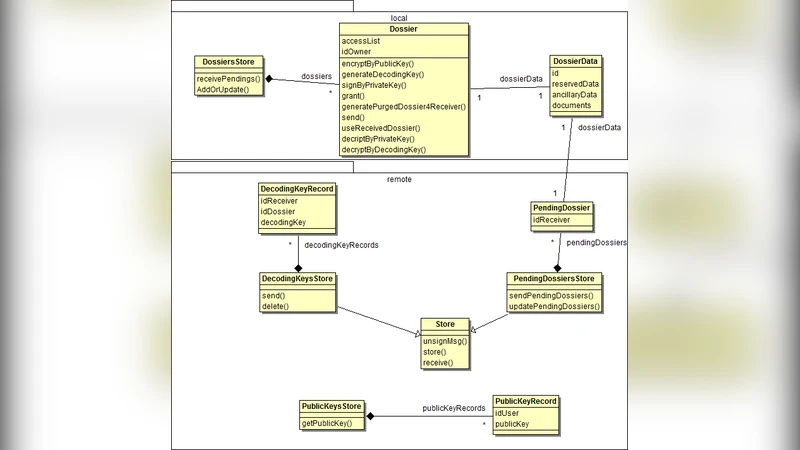
Handling Confidential Data on the Untrusted Cloud: An Agent-based Approach
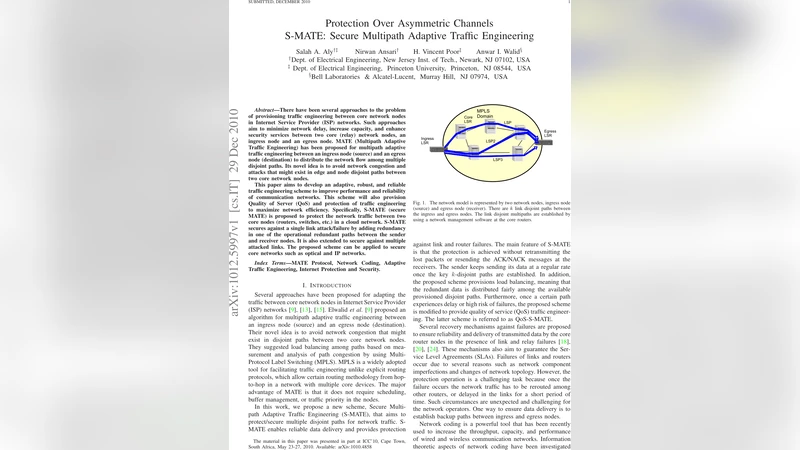
Protection Over Asymmetric Channels, S-MATE: Secure Multipath Adaptive Traffic Engineering

Abstract Certification of Global Non-Interference in Rewriting Logic

Primary User Emulation Attacks: A Detection Technique Based on Kalman Filter
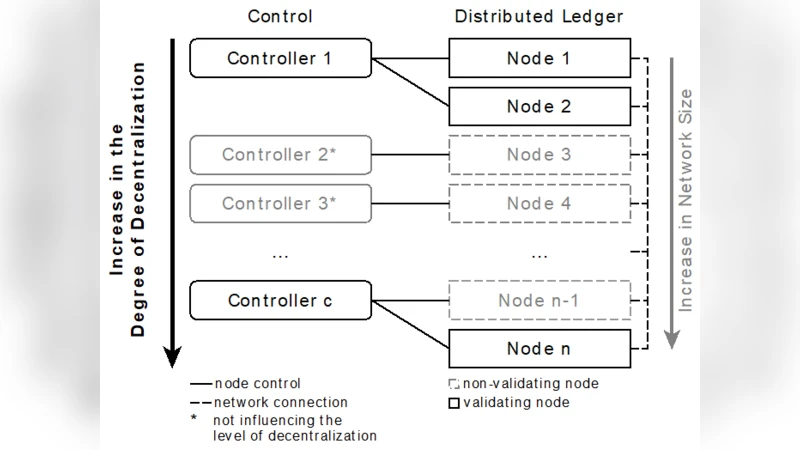
Mind the Gap: Trade-Offs between Distributed Ledger Technology Characteristics

A Bleeding Digital Heart: Identifying Residual Data Generation from Smartphone Applications Interacting with Medical Devices

Towards Models for Availability and Security Evaluation of Cloud Computing with Moving Target Defense

User Acceptance of Usable Blockchain-Based Research Data Sharing System: An Extended TAM Based Study

MFA is a Waste of Time! Understanding Negative Connotation Towards MFA Applications via User Generated Content

Compliance of POLYAS with the Common Criteria Protection Profile

Ubuntu One Investigation: Detecting Evidences on Client Machines

Physical Access Control Management System Based on Permissioned Blockchain

BARS: a Blockchain-based Anonymous Reputation System for Trust Management in VANETs

Analysis of the User Acceptance for Implementing ISO/IEC 27001:2005 in Turkish Public Organizations

EPA-RIMM: A Framework for Dynamic SMM-based Runtime Integrity Measurement

Truxen: A Trusted Computing Enhanced Blockchain

Measuring the Correlation of Personal Identity Documents in Structured Format

A Blockchain-Based Architecture for Traffic Signal Control Systems
