Cs-Cr
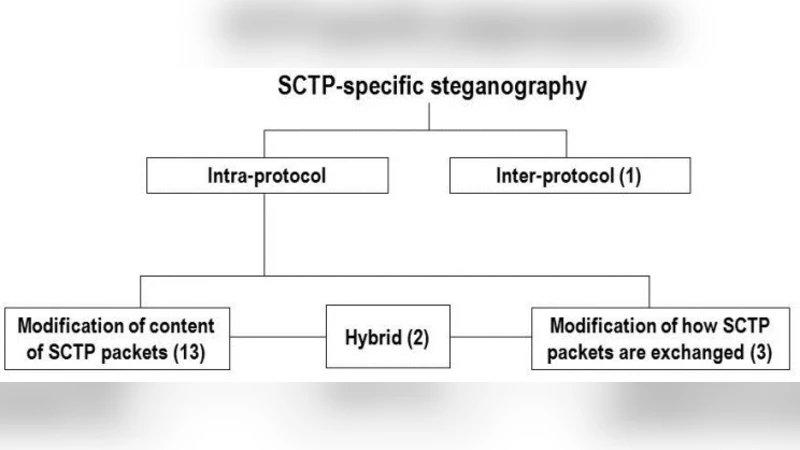
Hiding Information in a Stream Control Transmission Protocol
Automatic Web Security Unit Testing: XSS Vulnerability Detection

A Smart Approach for GPT Cryptosystem Based on Rank Codes

Distributed Private Data Analysis: On Simultaneously Solving How and What
Clustering based Privacy Preserving of Big Data using Fuzzification and Anonymization Operation
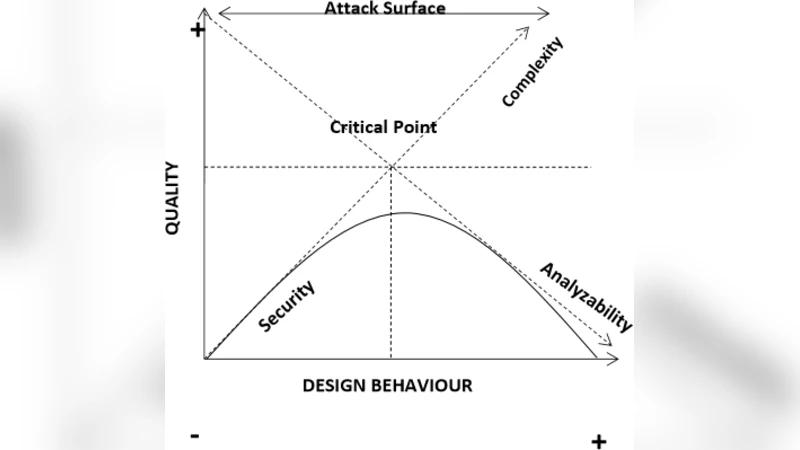
On the Relationship between Software Complexity and Security

Managing Delegation in Access Control Models
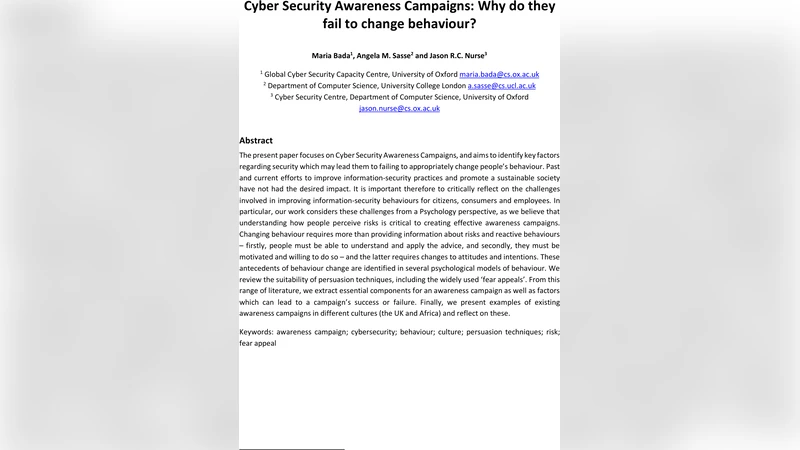
Cyber Security Awareness Campaigns: Why do they fail to change behaviour?
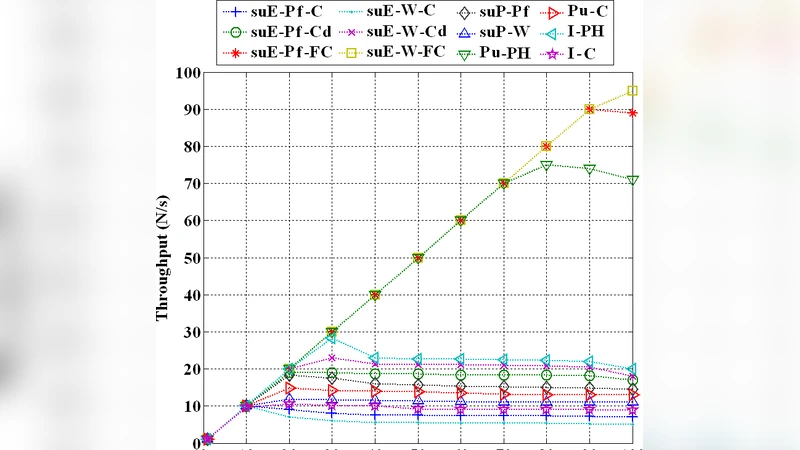
Performance Evaluation of Shared Hosting Security Methods
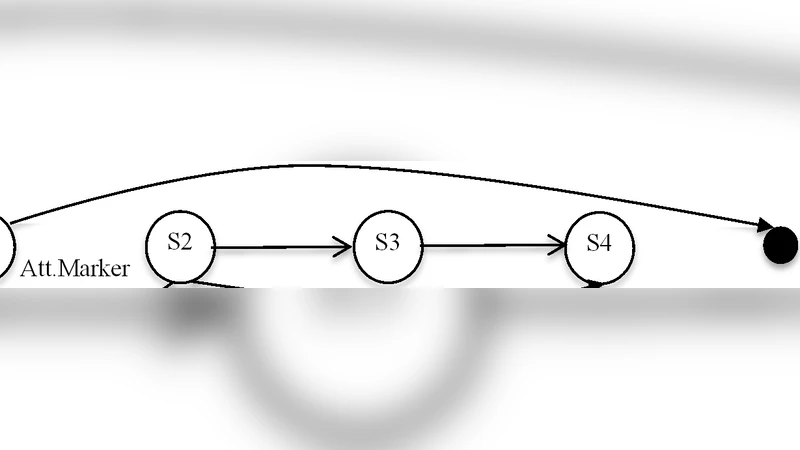
Secure Information Flow by Model Checking Pushdown System

Detecting cyber threats through social network analysis: short survey

A closer look at Intrusion Detection System for web applications
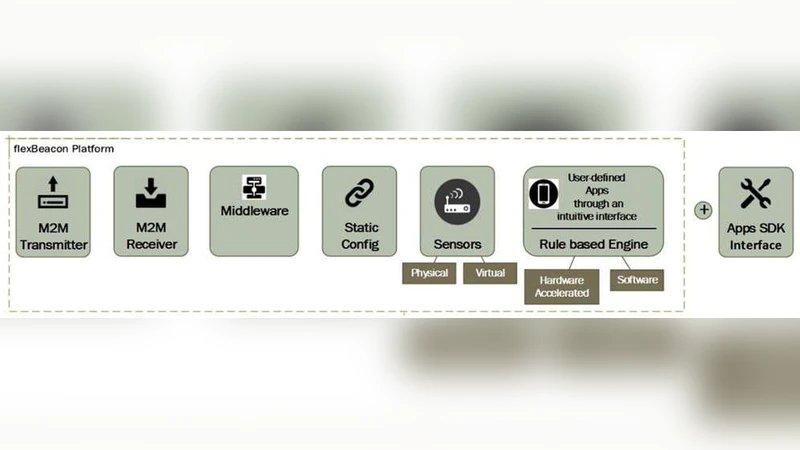
Softwarization of Internet of Things Infrastructure for Secure and Smart Healthcare
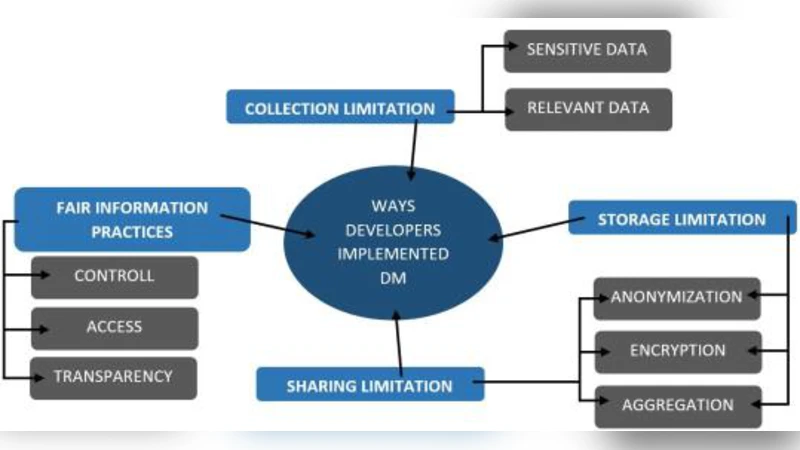
Understanding Software Developers Approach towards Implementing Data Minimization
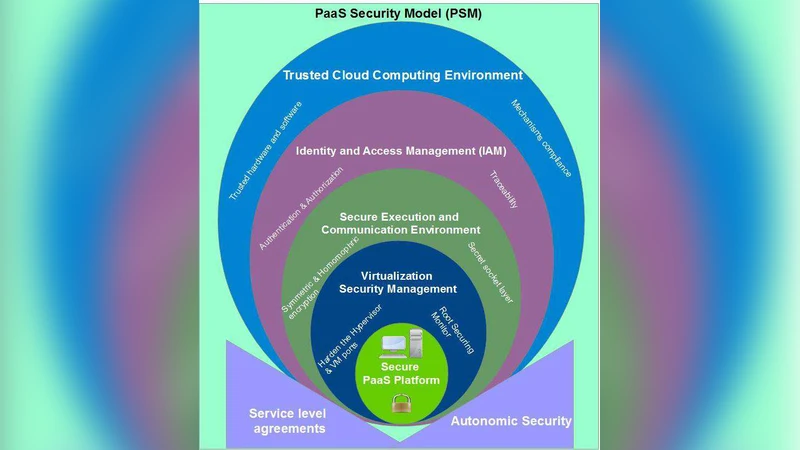
MPSM: Multi-prospective PaaS Security Model
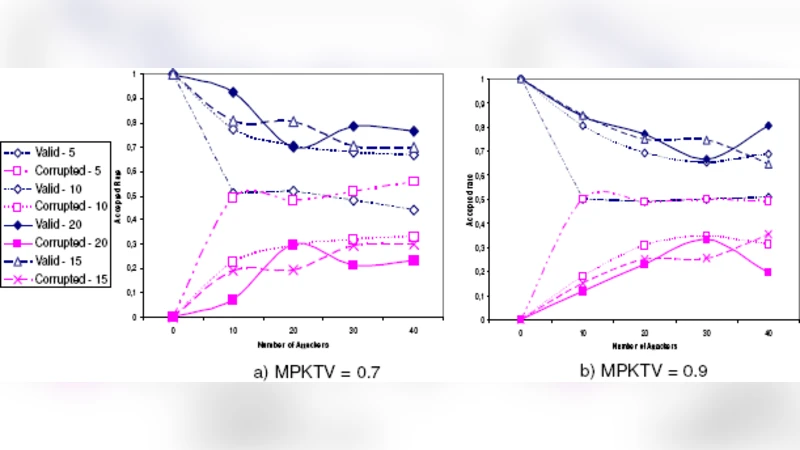
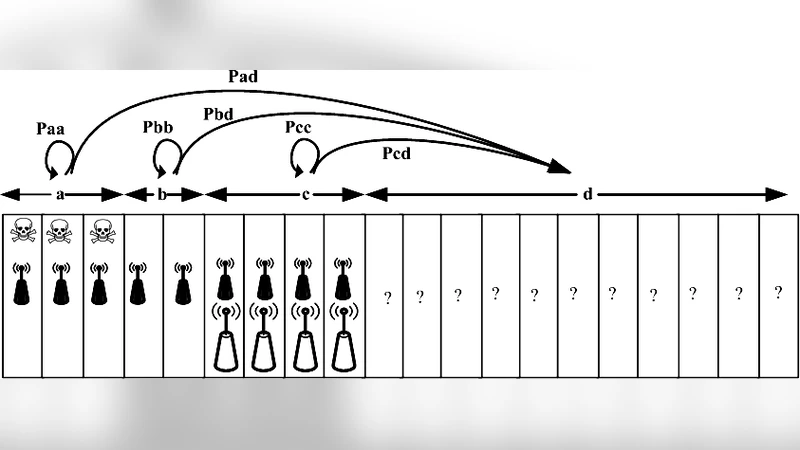
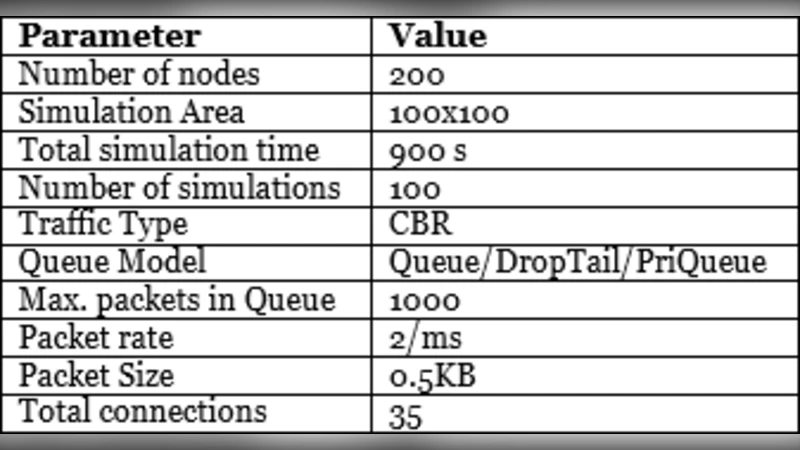
A Robust and Efficient Node Authentication Protocol for Mobile Ad Hoc Networks
Investigating Cybersecurity Issues In Active Traffic Management Systems
Game-theory-based analysis on interactions among secondary and malicious users in coordinated jamming attack in cognitive radio systems
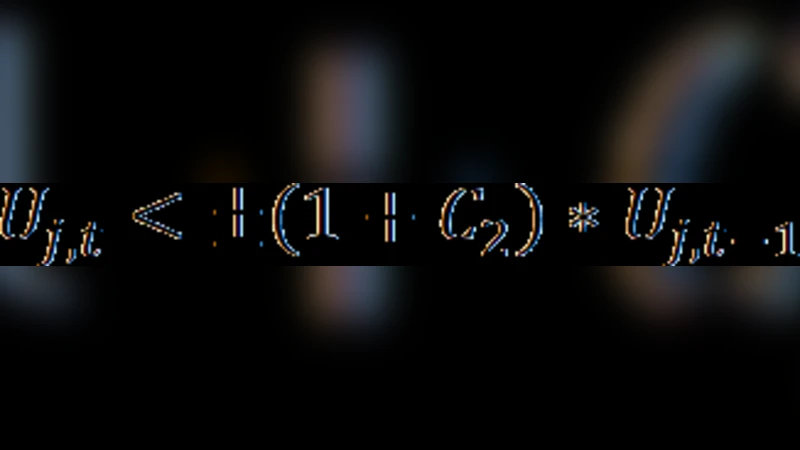
Security Rating Metrics for Distributed Wireless Systems
RESCUE: Interdependent Challenges of Reliability, Security and Quality in Nanoelectronic Systems
Exploring Information Centrality for Intrusion Detection in Large Networks
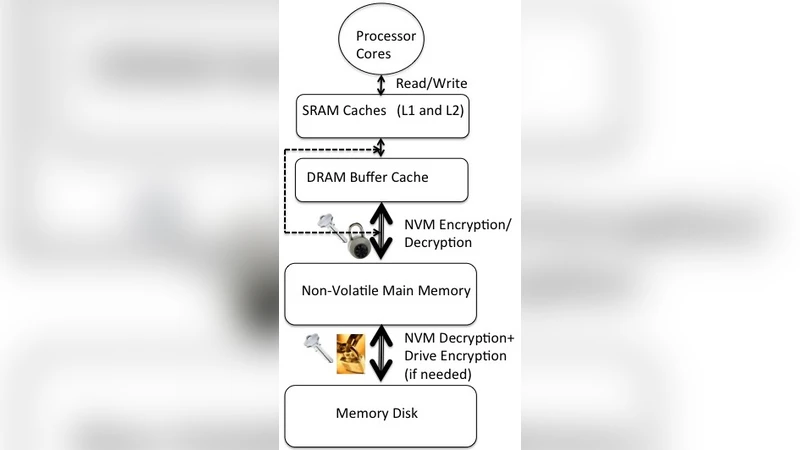
Architecting Non-Volatile Main Memory to Guard Against Persistence-based Attacks