Cs-Cr

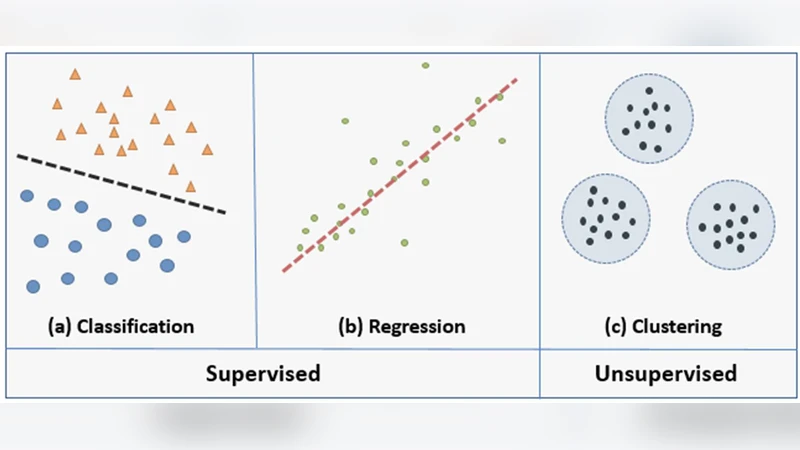
Privacy Preserving Machine Learning: Threats and Solutions

Improving Privacy and Trust in Federated Identity Using SAML with Hash Based Encryption Algorithm
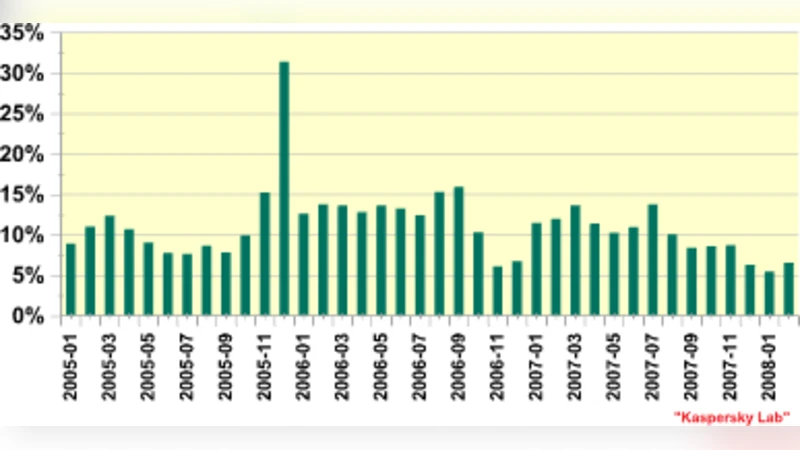
Software Vulnerabilities, Banking Threats, Botnets and Malware Self-Protection Technologies

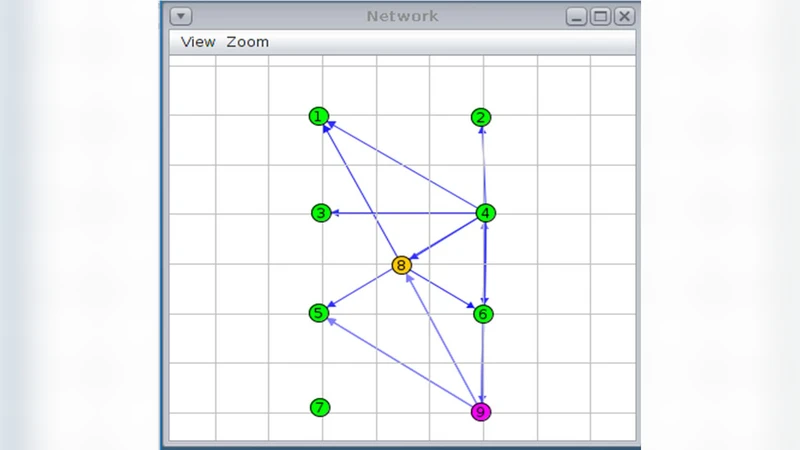
Simulation of Computer Network Attacks
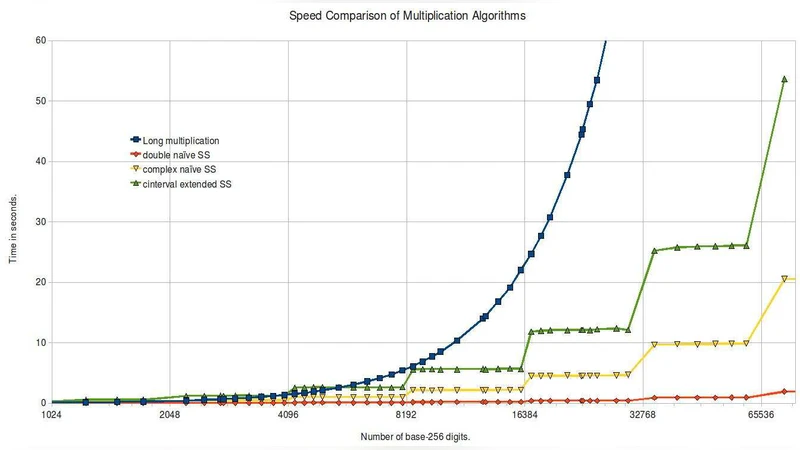
A Rigorous Extension of the Sch"onhage-Strassen Integer Multiplication Algorithm Using Complex Interval Arithmetic
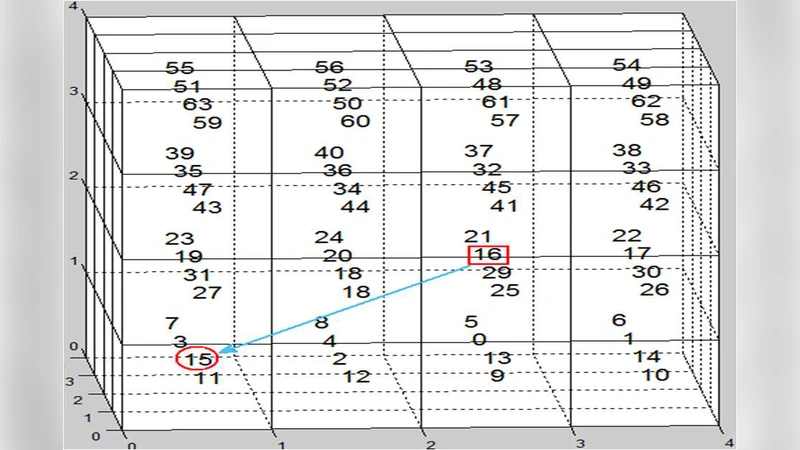
A novel method of speech information hiding based on 3D-Magic Matrix

Designing a Bit-Based Model to Accelerate Query Processing Over Encrypted Databases in Cloud
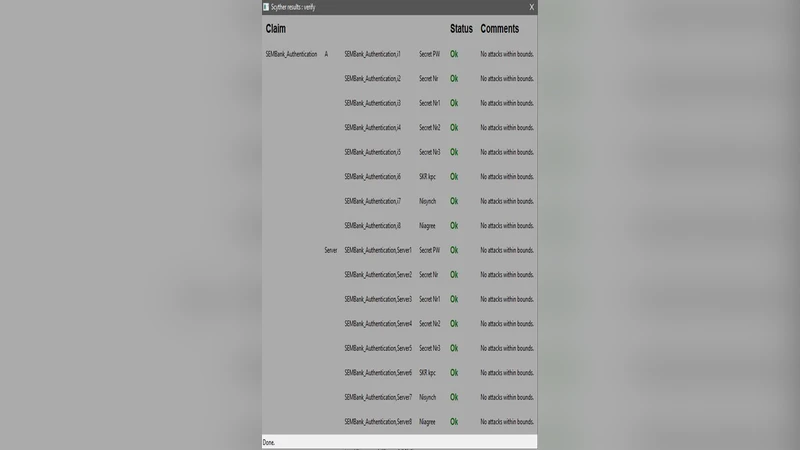
S-Mbank: Secure Mobile Banking Authentication Scheme Using Signcryption, Pair Based Text Authentication, and Contactless Smartcard
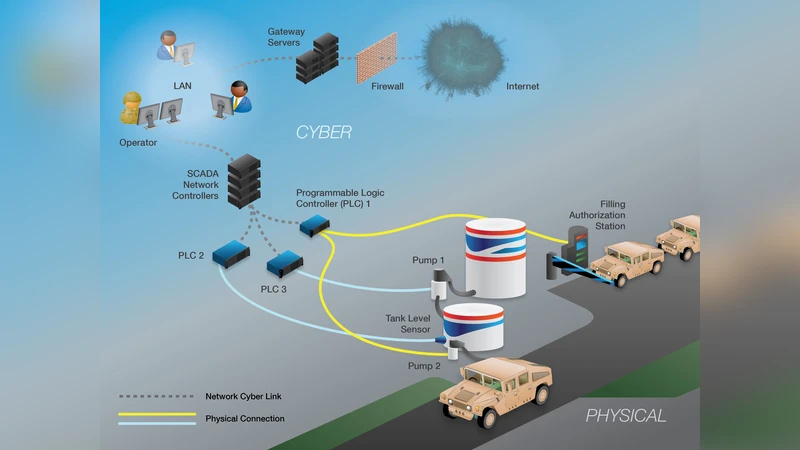
Game-Theoretic Model and Experimental Investigation of Cyber Wargaming
Synchronization in Quantum Key Distribution Systems

Post-Quantum Cryptography: Riemann Primitives and Chrysalis
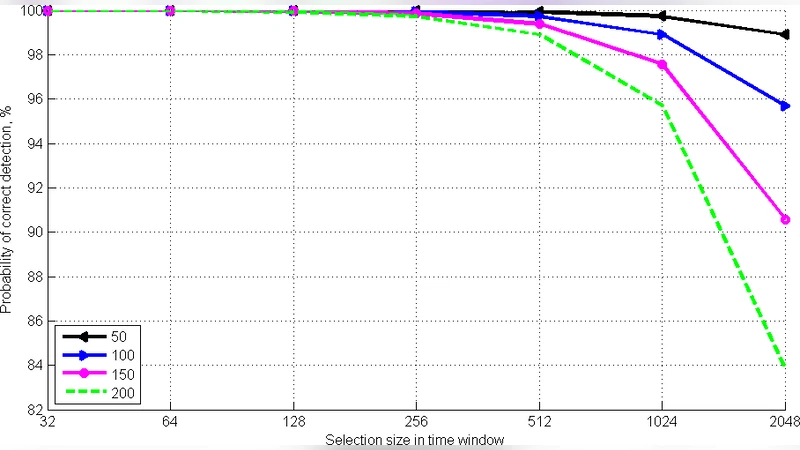
Timing Channel in IaaS: How to Identify and Investigate
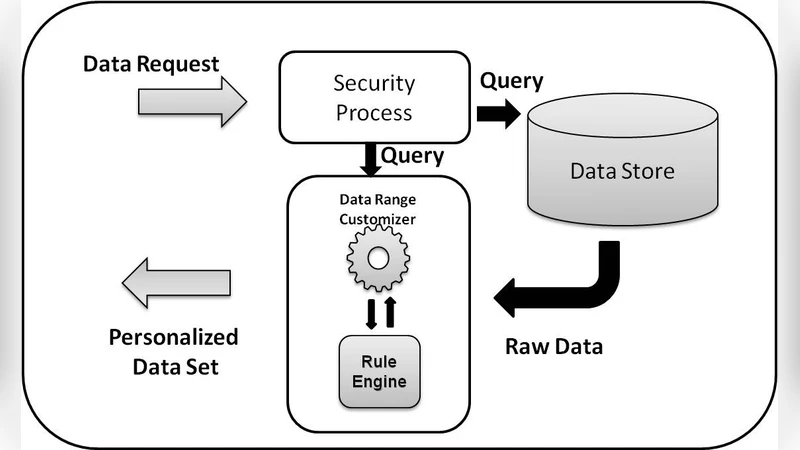
Personalized Data Set for Analysis

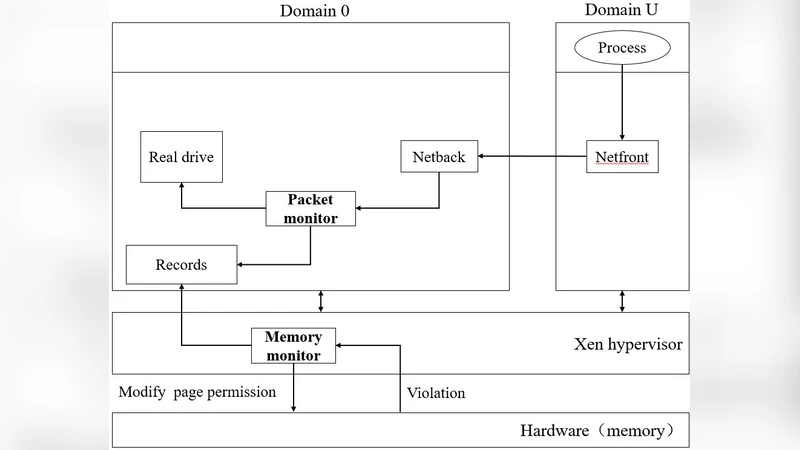
Hypervisor-Based Active Data Protection for Integrity and Confidentiality of Dynamically Allocated Memory in Windows Kernel
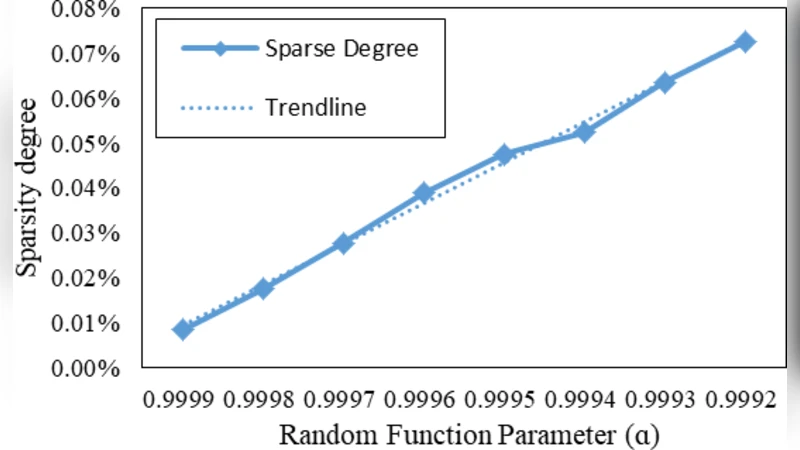
Roundtable Gossip Algorithm: A Novel Sparse Trust Mining Method for Large-scale Recommendation Systems

A complete formalized knowledge representation model for advanced digital forensics timeline analysis

Am I Responsible for End-Users Security? A Programmers Perspective
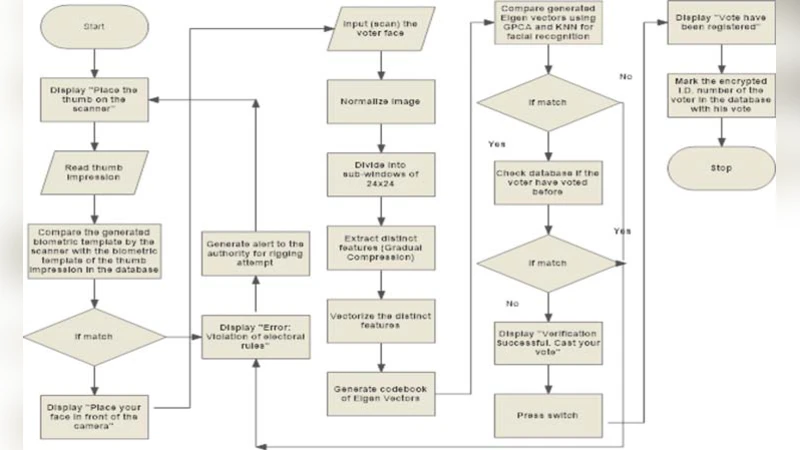
A Novel Hybrid Biometric Electronic Voting System: Integrating Finger Print and Face Recognition

Automatically Generate Steganographic Text Based on Markov Model and Huffman Coding

Towards joint decoding of binary Tardos fingerprinting codes

PQC: Extended Triple Decomposition Problem (XTDP) Applied To GL(d, Fp)-An Evolved Framework For Canonical Non-Commutative Cryptography

Measuring the Impact of Spectre and Meltdown