Cs-Cr

Open Data, Grey Data, and Stewardship: Universities at the Privacy Frontier
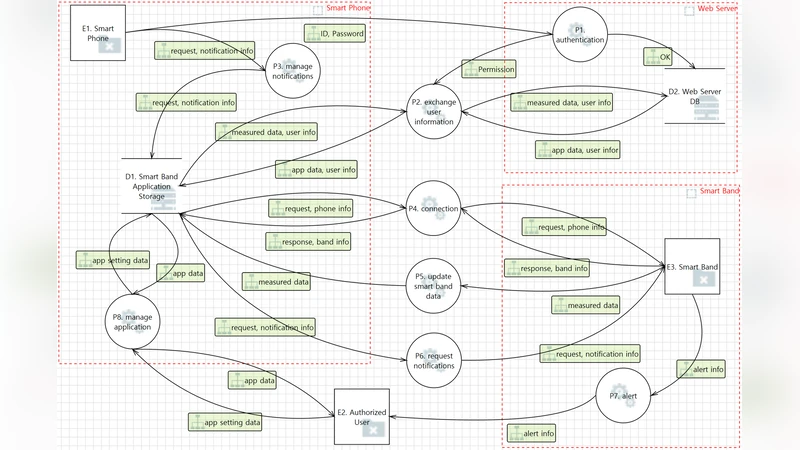
Trustworthy Smart Band: Security Requirement Analysis with Threat Modeling
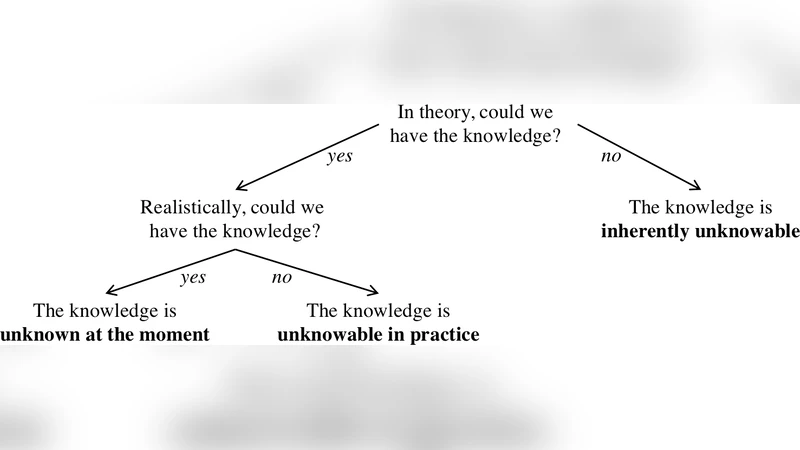
Prediction in Cyber Security: Complications and Consolations
Strategic Alliance for Blockchain Governance Game

Outrepasser les limites des techniques classiques de Prise dEmpreintes grace aux Reseaux de Neurones
RF-PUF: IoT Security Enhancement through Authentication of Wireless Nodes using In-situ Machine Learning

Device-independent quantum key distribution
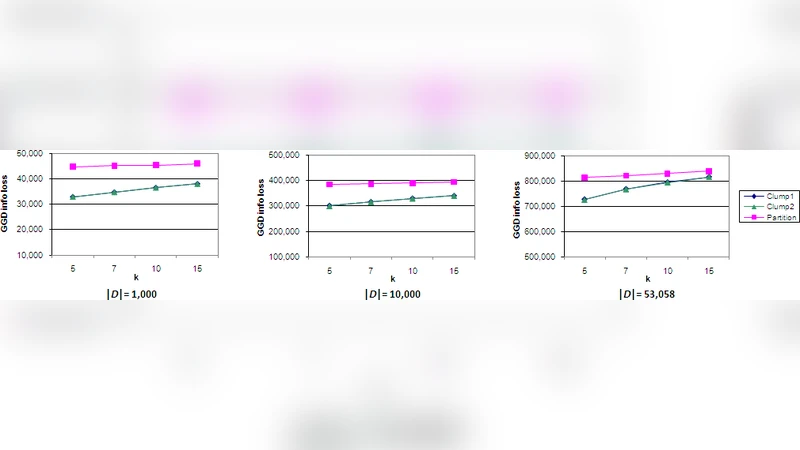
An Effective Clustering Approach to Web Query Log Anonymization

Quality of Source Location Protection in Globally Attacked Sensor Networks
Secured histories: computing group statistics on encrypted data while preserving individual privacy

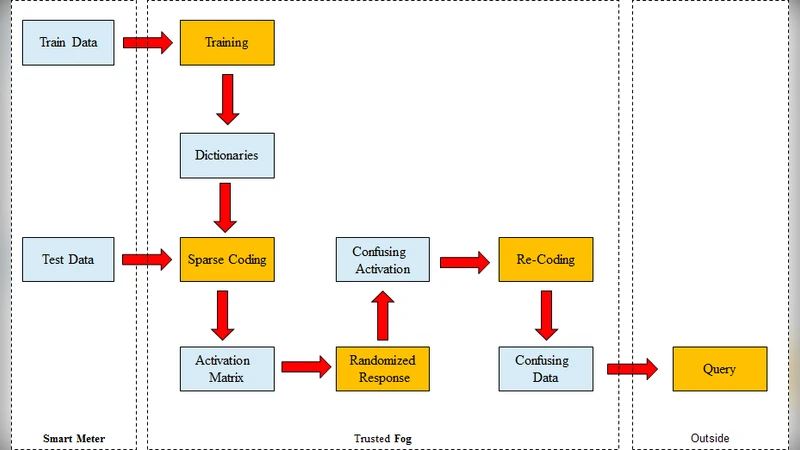
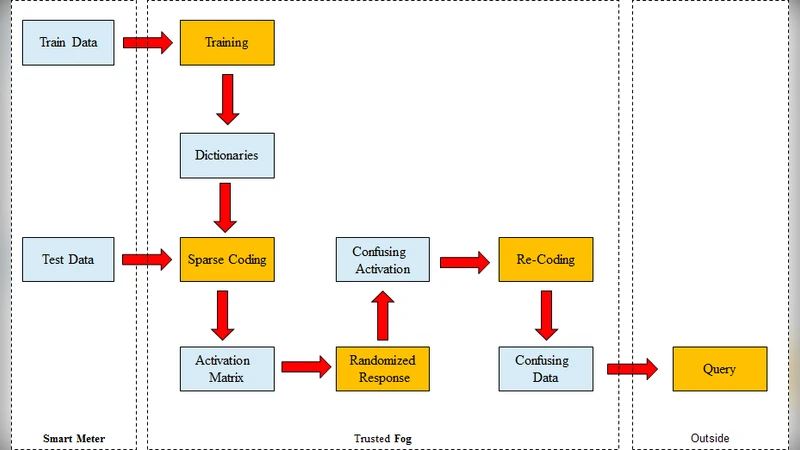
Plug-in privacy for Smart Metering billing

Survey of Consensus Protocols

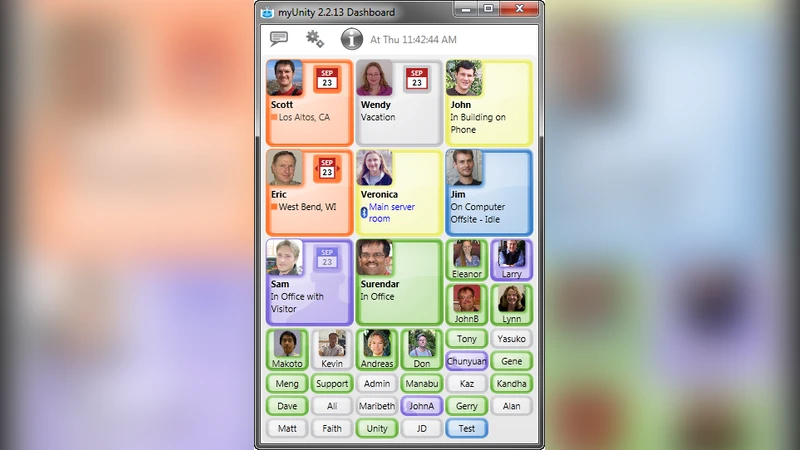
Sorry: Ambient Tactical Deception Via Malware-Based Social Engineering
Malicious Web Domain Identification using Online Credibility and Performance Data by Considering the Class Imbalance Issue
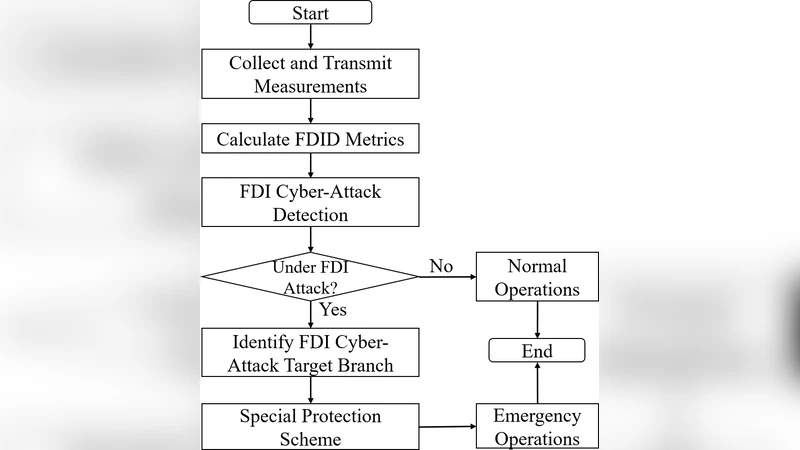
Enhancing Power System Cyber-Security with Systematic Two-Stage Detection Strategy

Blockchain based Proxy Re-Encryption Scheme for Secure IoT Data Sharing
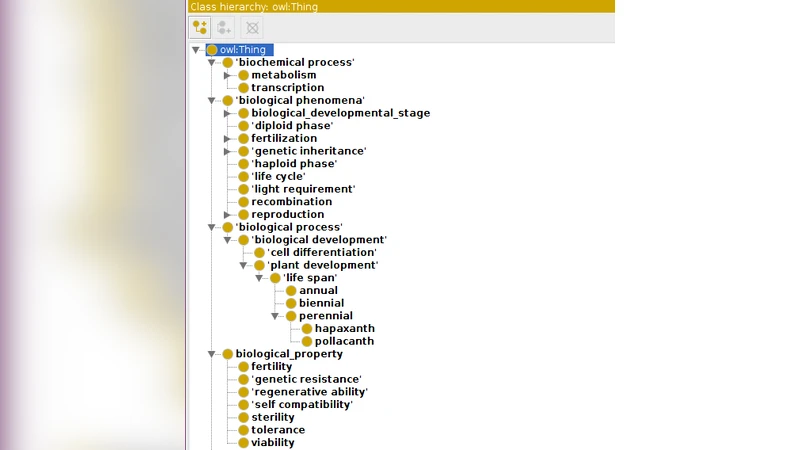
Leveraging protection and efficiency of query answering in heterogenous RDF data using blockchain
An Anomaly-based Botnet Detection Approach for Identifying Stealthy Botnets

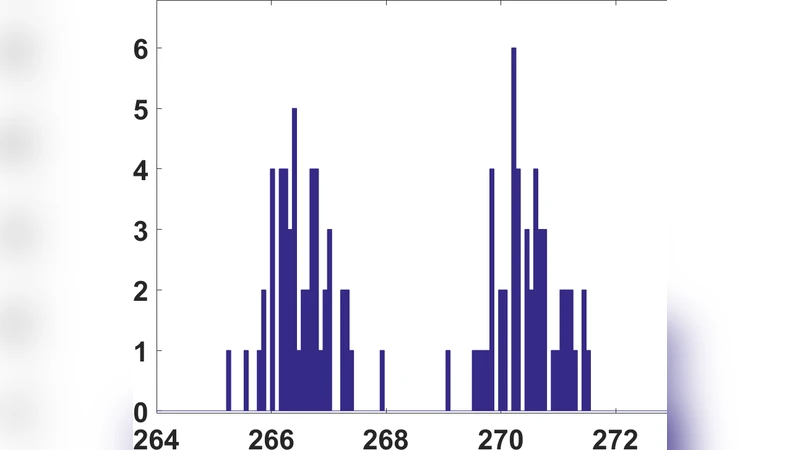
Time Series Analysis of Electricity Price and Demand to Find Cyber-attacks using Stationary Analysis
New generation of mobile phone viruses and corresponding countermeasures

Aperiodic logarithmic signatures
A Study on Recent Approaches in Handling DDoS Attacks